01 - 07 March 2023 — (Issue 10)
is sponsored by

Readers who encounter problems with the email version of this newsletter can
view the latest web edition here
| Visit us on |
CONTENTS
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
- Putin tells FSB to raise its game against Western spy agencies - Euractiv, 28 Feb 23
- Secret Service, ICE carried out illegal stingray surveillance, government watchdog says - The Record, 02 Mar 23
- DHS Tests Show Facial Recognition Tech has Varied Results, But Gaining Ground - NextGov, 26 Feb 23
- MI5 to face criticism over ‘significant missed opportunities’ to stop Manchester terror attack - The Telegraph, 02 Mar 23
- ‘Havana syndrome’ not caused by energy weapon or foreign adversary, intelligence review finds - Washington Post, 01 Mar 23
- Security Clearance Application Headed for an Upgrade - Clearance Jobs, 01 Mar 23
- US Launches Aggressive National Cybersecurity Strategy - Global Security, 02 Mar 23
- How Russia's security service framed an Estonian prisoner as a secret agent - Yahoo News, 02 Mar 23
- Turkish spy agency MIT agents shadowed foreign aid and rescue teams in quake zone - Nordic Monitor, 27 Feb 23
- Senior PKK/KCK terrorist 'neutralized' by Turkish intelligence in N. Iraq - AA, 03 Mar 23
- Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
- Assessing Top Global Security Threats with Expert Frederick Kagan — Former Acting CIA Director Mike Morell, Intelligence Matters
- "Ukraine and Intelligence: One Year On" - with Shane Harris — Andrew Hammond, PhD. SpyCast
- The German-French relationship is still the beating heart of the European Union and it needs to stay healthy. — Former Acting CIA Dep. Dir. for Ops and Arkin Group President Jack Devine, In Other News
- Economic Rift with China, Imminent Breakthrough in Yemen?, “White Power Rangers,” Assad Uses Earthquake, Middle East “Biden Doctrine” — Former FBI Special Agent and Soufan Group CEO Ali Soufan, Intel Brief
- Blinken at the G20, War in Ukraine at One Year, Taliban hunts US collaborators, and more... — WTOP National Security Correspondent JJ Green - Inside the SCIF, Target USA, The Hunt
- China Shaking Up Spy Agencies? - Jeff Stein and Colleagues in SpyTalk (Substack)
Section III - MEMBER CONTRIBUTIONS
- Article: China’s Trial Balloon - The American Spectator, 06 Feb 23
- Report: Why the Afghan Security Forces Collapsed - Special Inspector General for Afghanistan Reconstruction, February 2023
- Poem: A Smuggler's Song - Rudyard Kippling, Puck of Pook's Hill (1906)
- Article: US Cyber Command developing own intelligence hub - C4ISRnet, 01 Mar 23
- Article: In Neural Networks, Unbreakable Locks Can Hide Invisible Doorsv- Quanta Magazine, 02 Mar 23
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
- Analysis: Skies, Spies, and Scientific Surveys – The Legal Aspects of Chinese Unmanned Balloon Flight Over American Territory - European Journal of International Law, 06 Mar 23
- Audio: Matt Olsen on Foreign Intelligence Surveillance Act Section 702 (86 mins) - Lawfare, 01 Mar 23
- OpEd: Chinese Espionage - The Unfortunate Reason Behind its Great Success - or it must be shut down - Japan Forward, 02 Mar 23
- Analysis: How the Chinese spy agency MSS disrupts the world - First Post, 02 Mar 23
- Report: National Threat Assessment 2023 - Norwegian Police and Intelligence Services, March 2023
- OpEd: We Have a New National Cybersecurity Strategy. Now What? - Cipher Brief, 03 Mar 23
- Video: Counter Intelligence Today (75 mins) - GMU Hayden Center for Intelligence Policy, 03 Mar 23
- Paper: The uses and utility of intelligence - The case of the British Government during the War of the Spanish Succession - Journal of Intelligence History, Released March 2023 (Originally published 17 Nov 21)
- Article: The Spy Whisperer - Psychiatry and Intrigue with Dr. Kenneth Deklev - SpyScape, 01 Mar 23
- Analysis: The great power pivot and the intelligence community - FCW, 27 Feb 23
- Video: House Permanent Select Committee on Intelligence Hosts Think Tank Leaders to Discuss Intelligence Issues (134 minutes) - HPSCI, 28 Feb 23
- Infographic and Report: How the Russian Invasion of Ukraine Impacts Science and Academia - Visual Capitalist, 24 Feb 23
- Intelligence in History - A Collection of Recent Content
- True Intelligence Matters in Film: Bonhoeffer - Agent of Grace - Director Eric Till (2000)
- Walking Tours: The Spies of Embassy Row and Spies of Georgetown - Washington, DC. (Sundays, Dates/Times Vary)
Section V - Books, Research Requests, Academic Opportunities, Jobs, Obituaries
Books — Forthcoming, New Releases, Overlooked
- The Dirty Tricks Department: Stanley Lovell, the OSS, and the Masterminds of World War II Secret Warfare by John Lisle
- We Were Never There: Volume 2: CIA U-2 Asia and Worldwide Operations 1957-1974 by Kevin Wright
- Disrupting Time: Industrial combat, espionage, and the downfall of a great American company by Aaron Stark
Research Requests and Academic Opportunities
- Call For Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
- Call For Sources: Intelligence Officers Who Lived in Spain in the 1970s
- Academic Opportunity: Critical Thinking for Intelligence Analysis Course (21 Apr 23, 0800-1700 (ET) - The Intelligence and Security Academy - Virtual
- Academic Opportunity: The International Security and Intelligence Programme (9 July - 5 August 2023) - Magdalene College, Cambridge
- Call For Papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
- Search For Stories: of encounters with China's civilian and military intelligence apparatus.
- Search For Information: on CIA gallantry award recipients Bob A. Plan and Arthur J. Porn.
- Search For Information: on CIA operation against Iran in late 1990s and bomb found during President Clinton visit to Philippines in 1996
- Search For Information: on the adverse effects of diversity, equity, and inclusion on intelligence
- Call For Papers: Israel Affairs - "The Struggle in the Israeli Security Zone in South Lebanon, 1985-2000" (30 Mar 23 deadline)
- Call For Articles: AFIO Journal, The Intelligencer
- Faculty Opening - Adjunct Faculty, Intelligence Analysis - Krieger School of Arts and Sciences, Johns Hopkins University, Online
- Retired Federal Government Employees Wanted - National Security Agency, Fort Meade, MD
- Assistant Professor - Intelligence Studies (Global Security and Intelligence Studies), Embry-Riddle Aeronautical University - Prescott, Arizona
- Teaching Associate - Intelligence and National Security Studies, Coastal Carolina University, Conway, South Carolina
- Colonel Bill Roche, Decorated Defense Attache, CIA Consultant
- Dennis Moran, Career CIA Officer
- John Brady, Career CIA Case Officer
- Bernard D'Ambrosio, Career CIA Operations Officer
- Frank Knott, Career Foreign Service Officer
- 16 Mar 23 (Thursday), 1130 (MST) - In Person - Colorado Springs David Humpert discussing "1983 The Year of Maximum Danger" - Rocky Mountain CO Chapter
- 13 Apr 23 (Thursday), 1130 (PST) - In Person - San Francisco - CAPT Richard E. Hanson on CIA Operations in Viet Nam - Andre LeGallo Chapter
- 21 Apr 23 (Friday), 1030 (ET) - In Person - Tysons, VA - Hold the Date for AFIO Spring Luncheon on Artificial Intelligence and other matters - AFIO National Event
Events from Advertisers, Corporate Sponsors, Others
- 08 Mar 23, 1200 (ET) – The Double Life of Katharine Clark – International Spy Museum Program - Virtual
- 13 Mar 23, 1700 - 1800 (ET) Publishing with Intelligence - Institute of World Politics – Virtual
- 14 Mar 23, 0900 - 0945 (ET) Coffee and Conversation with DIA China Mission Group Chief Doug Wade - INSA – Virtual
- 15 Mar 23, 1200 (ET) – Intro to MASINT with Peter Humphrey – International Spy Museum Program - Virtual
- 18 Mar 23, 1400-1600 (ET) – Book Signing Event with Jonna Mendez – International Spy Museum - In Person – Washington, DC
- 19 - 28 Mar 23 - Gary Powers' 10-Day Cold War Espionage Tour - In-person, Washington DC to Europe and back
- 24 Mar 23, 1200 (ET) – Sidney Reilly: Master Spy with Benny Morris – International Spy Museum Program - Virtual
- 27 Mar 23, 1630 (ET) – Discussion on The Fourth Man with Prof. John J. Quattrocki, Institute of World Politics - In-Person - Washington, DC
- 27 Mar 23, 1830 (ET) – Red London with Alma Katsu – International Spy Museum Program - Virtual
- 28 Mar 23, 1400-1500 (ET) – SPY with Me: Memory Loss Program – International Spy Museum Program - Virtual
- 29 Mar 23, 0900-1700 (ET) – How Wars End: A Conference Presented by the Pardee Center for the Study of the Longer-Range Future – Boston University - In Person
- 30 Mar 23, 1400-1500 (ET) – SPY with Me: Memory Loss Program – International Spy Museum Program - Virtual
- 13-14 Jul 23 2023 Intelligence and Security Summit – AFCEA/INSA - In Person - National Harbor, MD
See the AFIO Calendar of Events for scheduling further in the future.
NGA Tearline Project Wins Inaugural OSINT Unit of the Year Award

Left to right – Chris Rasmussen, NGA Tearline, Program Manager; Vice Admiral Frank Whitworth, NGA Director; Barbara Alexander, OSINT Foundation President; and Eliot Jardines, OSINT Foundation Director of Operations
Left to right – Chris Rasmussen, NGA Tearline, Program Manager; Vice Admiral Frank Whitworth, NGA Director; Barbara Alexander, OSINT Foundation President; and Eliot Jardines, OSINT Foundation Director of Operations
The OSINT Foundation announces that the inaugural Turbiville OSINT Unit of the Year Award goes to NGA's Tearline Project. Named after U.S. Army Foreign Military Studies Office Director Dr. Graham Hall Turbiville, Jr. (a widely respected 40-year defense intelligence community veteran and steadfast OSINT advocate), the award recognizes the IC unit that has demonstrated exceptional impact to national security and has materially contributed to the OSINT discipline.
Tearline's public-facing website, which highlights high-quality OSINT-enabled GEOINT products of national security interest, advances U.S. national security by better informing decision makers and the general public while educating prospective IC professionals on OSINT and GEOINT exploitation and analytical tradecraft. Tearline advances the NGA mission by delivering world-class GEOINT that provides a decisive advantage to its consumers and helps train the future NGA workforce.
Tearline Program Manager Chris Rasmussen: “What makes Tearline successful is that it's mutually beneficial for both NGA and our collaborators. We’re helping bridge the gap between intelligence and the public through the transparent creation of quality OSINT.”
OSINT Foundation President Barbara Alexander: “Tearline represents the future of the OSINT discipline: innovative and forward-looking use of technology coupled with meticulous tradecraft that taps into the growing community of practitioners outside of the U.S. Intelligence Community to provide meaningful, operationally-relevant products to answer intelligence questions. The Foundation’s commitment to the development of the next generation of open-source intelligence practitioners makes Tearline an especially meaningful inaugural recipient, and one that would clearly have delighted Dr. Turbiville."
LATEST FROM AFIO
Released exclusively to members 7 March 2023...
The Rise of The Abwehr
Nigel West, Historian and Former MP, on
"Hitler's Nest of Vipers: The Rise of The Abwehr"
Interview of Thursday, 19 January 2023 of Nigel West, Intelligence Historian, Author, former MP, and AFIO Honorary Board member. Interviewer - Host: James Hughes, AFIO President, a former CIA Operations Officer.
TOPIC: Nigel West and Jim Hughes discuss Nigel's recent book, "Hitler's Nest of Vipers: The Rise of The Abwehr." Topics include: German Intelligence Service and military districts; wehrmacht; Sicherheitsdienst; Abwehr defectors; Maj Richard Wurmann; MI5 post-war analysis of interrogated prisoners; Penetration of French Resistance; compromise of Allied Networks; Soviet System compromises; Rote Kapelle (Red Orchestra) started by Abwehrstelle Belgium, a field office of Abwehr; Portugal and Spanish links to Abwehr; KOs - hybrids with three branches; Impact on GRU and Communist networks; Death of British agents in Holland; the truth about the effectiveness of the Double-Cross System; the double agent who escaped capture.
The interview runs 22 minutes and includes several Q&As.
Purchase a copy of "Hitler's Nest of Vipers"here.
Access the Nigel West interview here or click above image
The AFIO Now video series in 2023 is sponsored by Northwest Financial Advisors.

"AFIO Now" Video Interviews and Podcasts in 2023 are sponsored by
Northwest Financial Advisors
Click here to watch interviews in the AFIO Now series released in 2023.
View interviews from 2020 to 2022 here.
Watch public-release interviews on our YouTube channel or listen to them in podcast form at the links below.
Log into the member-only area for member-only features.
Latest podcast episode: Nigel West, Historian and Former MP, on "Spies Who Changed History: Greatest Spies and Agents of the 20th Century" Interview held Sunday, 15 January 2023. Interviewer - Host: James Hughes, AFIO President, a former CIA Operations Officer.
Are you too busy to watch an entire AFIO Now episode on YouTube? Would you rather listen in your car or while accomplishing other tasks? You can download or stream episodes on any of the 8 podcasting platforms that host AFIO Now. Search for 'AFIO Podcast' for a selection of the interviews above (public released ones) on:
Podbean; iTunes; Google; Spotify; Amazon Music; Amazon TuneIn + Alexa; iHeartRadio; Pandora
Social media users, and those who wish to explore, can find or be notified about new
announcements and other material on AFIO's Twitter feed, LinkedIn
page, and YouTube channel. Access them here: LinkedIn, Twitter, and YouTube.
![]()
![]()
![]()
FROM THE AFIO STORE
 Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Superior quality and shrink resistant; features a detailed embroidered AFIO seal. The shirt color is royal blue.
The sale price is $25 and includes shipping.
Available in men's sizes only: small, medium, large, extra-large, XXL, and XXXL.
Due to limited quantities, please contact the AFIO National Office for availability of size and to provide payment information.
You may telephone the office at 703-790-0320 or email annettej@afio.com
Access CIA's Inhouse Gift Shop
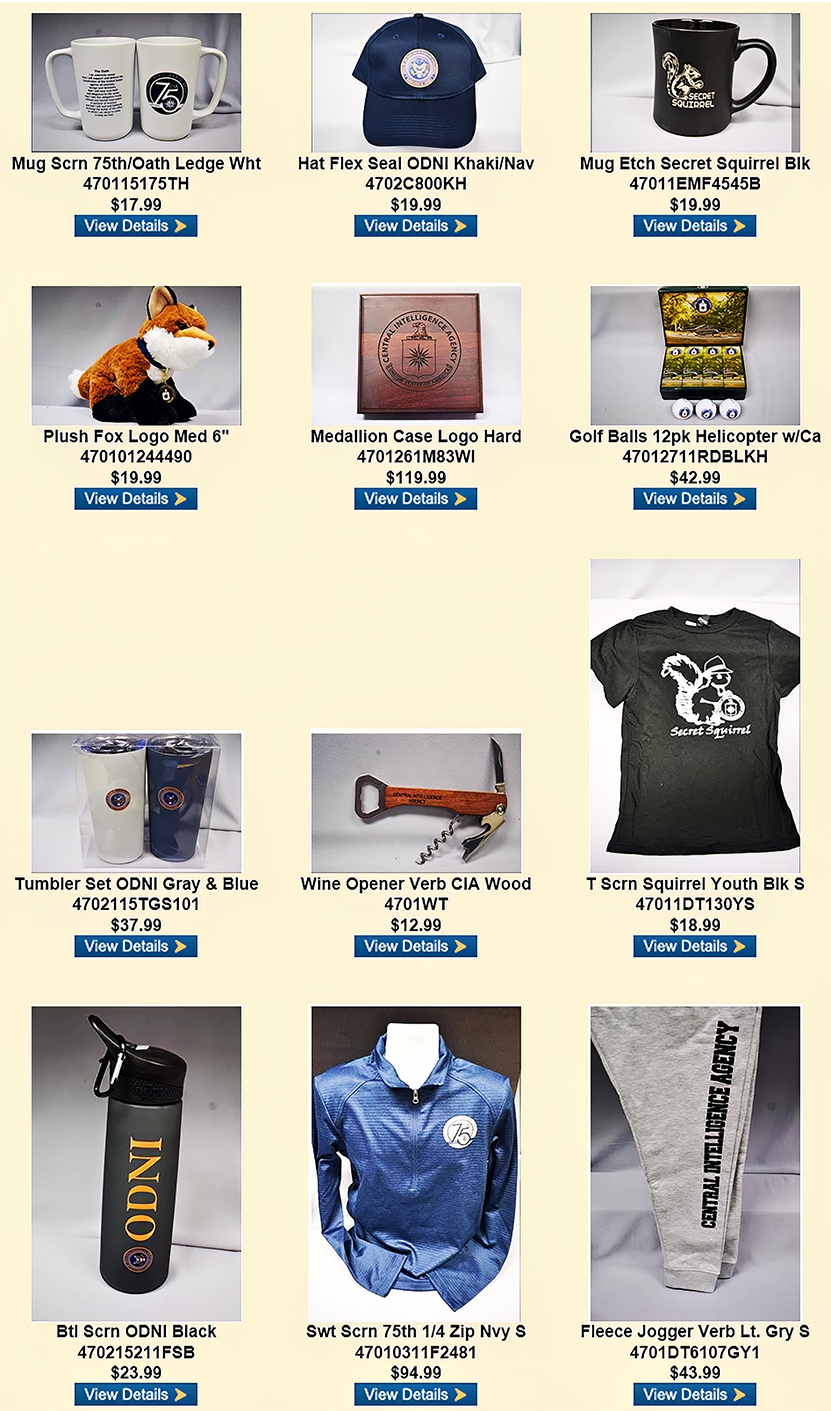
One special benefit of AFIO membership is access to CIA's EAA Store.
After completing the required, quick pre-approval process for all AFIO members, described here, you can purchase directly from the EAA online store their unusual logo'd gift items for self or colleagues. EAA on 10 February 2023 released the photo above, which features some of their newest CIA items and other gift suggestions.
NEWLY PUBLISHED
| Be informed on career opportunities in the U.S. Intelligence Community |
  |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. This is the all new fifth edition. |
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |
ACKNOWLEDGEMENTS
The WIN editors thank the following contributors of content for this issue:
JK, JH, EJ, EB, PO, FR
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
JK, JH, EJ, EB, PO, FR
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
DISCLAIMER
Our editors include a wide range of articles and commentary in the Weekly Intelligence Notes to
inform and educate our readers. The views expressed in the articles are purely those of the authors and do not reflect support or endorsement from AFIO. WIN notices about non-AFIO events do not constitute endorsement or recommendation by AFIO.
AFIO does not vet or endorse research inquiries, career announcements, or job offers. We publish reasonable-sounding inquiries and career offerings as a service to our members. We encourage readers to exercise caution and good judgment when responding and to independently verify the source before supplying resumes, career data, or personal information.
TECHNICAL DIFFICULTIES
Readers who encounter problems with links or viewing this newsletter as an email can access
the latest web edition here.
the latest web edition here.
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
Putin tells FSB to raise its game against Western spy agencies - Euractiv, 28 Feb 23
Russian President Vladimir Putin told the FSB domestic security service on Tuesday (28 February) to step up its activity to counter what he said was increasing espionage and sabotage against Russia by Ukraine and the West. In a speech to officials, Putin said the FSB had to stop “sabotage groups” entering Russia from Ukraine, step up protection of infrastructure, and prevent Western security services reviving what he called terrorist or extremist cells inside Russia. “Western intelligence services have traditionally always been active in Russia, and now they have thrown additional personnel, technical and other resources at us. We need to respond accordingly,” Putin said. He instructed the FSB to prevent illegal weapons flows into Russia, and to strengthen security in four regions of Ukraine that Moscow has partially seized and claimed as its own – a move most countries at the United Nations have condemned as illegal. (Full article here.)
Secret Service, ICE carried out illegal stingray surveillance, government watchdog says - The Record, 02 Mar 23
U.S. federal agencies failed to secure required court orders to conduct phone tracking surveillance, according to a recently redacted memorandum from a government watchdog. The report, written by the Office of the Inspector General (OIG) and dated February 23, provided details of an audit of the use of cell-site simulators (CSS) — a law enforcement tool that mimics cellular towers to trick nearby devices into connecting with them. These instruments, which are also known as stingrays or IMSI-catchers, allow law enforcement to track the location of a suspect or identify targeted devices. The auditors found that in 2020 and 2021, Immigration and Customs Enforcement’s Homeland Security Investigations division and the Secret Service had in some cases violated the law by not following regulations around the use of CSS. (Full article here.)
DHS Tests Show Facial Recognition Tech has Varied Results, But Gaining Ground - NextGov, 26 Feb 23
The research and development arm of the Department of Homeland Security published results of its 2022 biometric tech rally, meant to test identity systems in use cases of small groups of people in populated places like airports, on Thursday. Overall, the tests show that group processing can work, DHS officials told media during a press briefing on Thursday, although some, but not all, systems did show some performance differences based on demographics, also known as demographic differentials. The DHS Science and Technology Directorate has been holding tech rallies since 2018, meant to engage industry with challenge problems and test products against set metrics. Future tests will look at the performance of remote identity validation tech like document validation and liveness tech, which is meant to ensure that a live person is presenting themselves to be identified, as opposed to a spoof. For the 2022 rally, the testers tested 40 combinations of acquisition systems that capture images and matching algorithms against 575 volunteers over 11 days in the agency’s test facility in Maryland. Specifically, DHS officials were looking at effectiveness, efficiency, privacy, user satisfaction and equitability. (Full article here.)
MI5 to face criticism over ‘significant missed opportunities’ to stop Manchester terror attack - The Telegraph, 02 Mar 23
MI5 is expected to face pressure to explain the missed opportunities to stop Manchester bomber Salman Abedi after the publication of a final report into the atrocity on Thursday. The judge-led investigation into the attack is expected to criticise MI5’s failure to stop Abedi before he killed 22 people outside an Ariana Grande concert in May 2017. Richard Scorer, a lawyer at Slater and Gordon who represents 12 of the victims’ families, told The Telegraph that it appeared “significant opportunities” were missed to stop Abedi. He said that the failures needed to be examined “forensically and unsparingly”, adding: “Only by doing this can we hope to learn the lessons of the Arena bombing and ensure that attacks are prevented in the future.” It came as a man left paralysed by the attack said he wanted the truth and not “excuses” from MI5. (Full article here.)
‘Havana syndrome’ not caused by energy weapon or foreign adversary, intelligence review finds - Washington Post, 01 Mar 23
The mysterious ailment known as “Havana syndrome” did not result from the actions of a foreign adversary, according to an intelligence report that shatters a long-disputed theory that hundreds of U.S. personnel were targeted and sickened by a clandestine enemy wielding energy waves as a weapon. The new intelligence assessment caps a years-long effort by the CIA and several other U.S. intelligence agencies to explain why career diplomats, intelligence officers and others serving in U.S. missions around the world experienced what they described as strange and painful acoustic sensations. The effects of this mysterious trauma shortened careers, racked up large medical bills and in some cases caused severe physical and emotional suffering. Many of the afflicted personnel say they were the victims of a deliberate attack — possibly at the hands of Russia or another adversarial government — a claim that the report contradicts in nearly every respect, according to two intelligence officials who are familiar with the assessment and described it to The Washington Post. (Full article here.) (Note: May require a one time free registration or sit behind a pay wall.)
Related: Statement by CIA Director William J. Burns on the IC Assessment on AHIs - CIA Website, 01 Mar 235
Security Clearance Application Headed for an Upgrade - Clearance Jobs, 01 Mar 23
The Office of Personnel Management recently released a draft version of a new Personnel Vetting Questionnaire, the replacement for the SF-86, SF-85, and SF-85P. In a period of public comment, the Intelligence and National Security Alliance (INSA) offered its feedback on the upgrade to everyone’s favorite security clearance application. Larry Hanauer, Vice President of Policy at INSA, sat down with ClearanceJobs to discuss the form, why it’s an improvement on the current process, and some of the small steps the government can take it to be even better. (Full article here.)
US Launches Aggressive National Cybersecurity Strategy - Global Security, 02 Mar 23
The Biden administration is pushing for more comprehensive federal regulations to keep the online realm safer against hackers, including by shifting cybersecurity responsibilities away from consumers to industry and treating ransomware attacks as national security threats. The plan is part of the National Cyber Strategy that the administration released Thursday, outlining long-range goals for how individuals, government and businesses can safely operate in the digital world. This includes placing the burden on the computer and software industry to develop "secure by design" products that are purposefully designed, built and tested to significantly reduce the number of exploitable flaws before they're introduced into the market. The strategy "fundamentally reimagines America's cyber social contract" and will "rebalance the responsibility for managing cyber risk onto those who are most able to bear it," Acting National Cyber Director Kemba Walden said Wednesday in a press briefing to preview the strategy. (Full article here.)
How Russia's security service framed an Estonian prisoner as a secret agent - Yahoo News, 02 Mar 23
“I am a foreign agent of the special services of the Estonian Kapo,” the man, whose face has been blurred and whose voice has been rendered into bass, states on camera. “For a long time, I carried out tasks assigned to me by representatives of the Estonian Kapo, both on the territory of Estonia and in a number of other European countries, as well as on the territory of the Russian Federation in relation to civilians and including members of criminal groups.” To hear Russia’s Federal Security Service, or FSB, tell it, the unnamed 36-year-old Estonian national was captured in the arctic Russian city of Murmansk in late June 2022. A spokesperson for the FSB in Murmansk stated that the suspect was going to “collect information about the employees of the FSB with access to state secrets and individuals who provide them with confidential information.” (Full article here.)
Turkish spy agency MIT agents shadowed foreign aid and rescue teams in quake zone - Nordic Monitor, 27 Feb Jan 23
Turkish intelligence agency MIT shadowed foreign aid workers who were deployed to contribute to rescue and relief efforts in the aftermath of devastating earthquakes in southern Turkey on Feb. 6, MIT’s propaganda point man has publicly admitted. Ali Burak Darıcılı, a former intelligence officer who has been working as a publicist for the agency, said on February 22 that MIT vetted all aid workers sent to Turkey, ran background checks and took a closer look in particular at members of an Israeli delegation that was dispatched to Turkey. The surveillance, which at times amounted to harassment and risked the safety of foreign workers, shows the paranoia in the leadership of the government of Turkish President Recep Tayyip Erdoğan, apparently more concerned about backlash from frustrated voters than the lives of tens of thousands of people who perished under the rubble. (Full article here.)
Senior PKK/KCK terrorist 'neutralized' by Turkish intelligence in N. Iraq - AA, 03 Mar 23
A senior PKK/KCK terrorist was “neutralized” by Turkish intelligence in northern Iraq, according to security sources on Friday. Saad Ali Bedel, codenamed Ceko Pir, who was determined to have participated in actions against Turkish bases, was the ringleader of the terrorist activities against the Turkish intelligence agency in the Sinjar region, according to the sources. The agency, which assigned a special team to monitor Bedel's activities in Sinjar, determined that the terrorist was living with the Ezidi people, a religious minority group. Turkish forces took action after learning that Bedel was planning a new action against the Turkish army’s Basika base area in Mosul, Iraq, the sources added. (Full article here.)
Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
- Moldova kicks out two foreigners over plan for ‘violent’ uprising, spy agency says - Politico, 28 Feb 23
- Fears as alleged Russian spy, 39, caught in Australia worked in Ireland’s Dail office - The Sun, 26 Feb 23
- Poland: Spanish journalist Pablo González in custody for one year on charges of spying for Russia and no trial in sight - International Federation of Journalists, 28 Feb 23
- Israel issues rare indictment against Hezbollah agent for espionage, terrorism - World Israeli News, 02 Mar 23
- Armenia arrests former POW on suspicion of espionage - Armen Press, 07 Mar 23
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
The Latest National Security Topic Interview by Former Acting D/CIA Mike Morell
 Intelligence Matters: A CBS News national security podcast hosted by former CIA Acting Director and CBS News national security contributor Michael Morell.
Intelligence Matters: A CBS News national security podcast hosted by former CIA Acting Director and CBS News national security contributor Michael Morell.
28 Feb | Assessing Top Global Security Threats with Expert Frederick Kagan
In this episode of Intelligence Matters, host Michael Morell speaks with State Department Counselor Derek Chollet about the state of the war in Ukraine as it enters its second year. Morell and Chollet discuss the implications of a deepening relationship between Russia and Iran as well as Russia and China, which the U.S. recently warned against providing material aid to Moscow. Chollet also provides new insights into the newly tense relationship between Washington and Beijing, following the shootdown of a Chinese surveillance balloon. He outlines the Biden administration's approach to managing Iran's nuclear ambitions after the earlier collapse of nuclear talks.
Past episodes:
21 Feb | Marking One Year of War in Ukraine: State Department Counselor Derek Chollet
14 Feb | Chinese Spy Balloon Fallout: Military Expert John Culver
07 Feb| Inside Global Diplomacy: RT. Honourable Baroness Catherine Ashton
More about Intelligence Matters by Michael Morell here.
The Latest from International Spy Museum Historian Andrew Hammond, PhD.
 Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
28 Feb | "Ukraine and Intelligence: One Year On" - with Shane Harris Shane Harris joins Andrew to discuss the role of intelligence in the Ukraine conflict one year after it began. Shane reports on intelligence for the Washington Post and is the author of two books.
Past episodes:
21 Feb | "The Espionage News Cycle" - A Conversation with SPY's Aliza Bran
14 Feb | From the Vault: "The Birth of American Propaganda" - A Conversation with John Hamilton
07 Feb | How Artificial Intelligence is Changing the Spy Game
The Latest Insights from Former CIA Acting Deputy Director for Operations Jack Devine.
 In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
03 Mar | The German-French relationship is still the beating heart of the European Union and it needs to stay healthy. In late January, 60 years after France and West Germany signed the Treaty at the Élysée, French and German heads of state again met in Paris to reconfirm their bilateral friendship. It’s more critical than ever that French President Macron and German Chancellor Scholz overlook their rocky start and present a united front against Russian aggression. The French-German relationship generally propels the EU, but since Brexit in 2020, this relationship has become even more important. When Germany and France are in alignment, the entire EU profits. But when they diverge, it threatens to grind the EU to a halt. Right now, there’s too much at stake for the EU to be anything less than fully functional. (Full version available to AFIO members in the coming days here.)
10 Feb | Keeping Russia at bay one year into the war will require unrelenting political and physical will.
Daily Analysis of Security Issues and Geopolitical Trends
 Intel Brief The Soufan Center’s flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
Intel Brief The Soufan Center’s flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
07 Mar | The Complexities of an Economic Rift with China
Press reports and U.S. and China official statements and high-level meetings are dominated by discussion of growing tensions between the United States and China. Reflecting the growing bipartisan criticism of China, a clear majority of the House of Representatives in the 118th Congress have formed a new House Select Committee on the Strategic Competition Between the United States and the Chinese Communist Party to examine the range of disputes and differences between the two powers and review policy options. On February 28, the new Committee held its first hearing; the discussion unfolded broadly across a range of strategic, political, and economic issues including the possibility that China will seek to reunite Taiwan to the mainland by force; U.S.-China trade; allegations that China might acquire and misuse personal data from the use of the Tik Tok social media application; and China’s deplorable human rights record, including the repression of its Muslim community in Xinjiang. Other issues raised across the U.S. political spectrum include China’s lack of transparency into the origins of COVID-19; President Xi Jinping’s increasing consolidation of authority; China’s espionage against the United States; the potential for China to materially support Russia’s war against Ukraine; and China’s acquisition and alleged misuse of U.S. intellectual property. (Full brief here.)
06 Mar | Is a Breakthrough in Yemen Imminent?
03 Mar | Meet the “White Power Rangers”: The Far-Right Violent Extremist Group Gaining Traction in Russia
02 Mar | Assad Uses Earthquake to Advance Normalization
01 Mar | A “Biden Doctrine” for the Middle East
Analysis of Global Security Events with WTOP National Security Correspondent JJ Green
 Inside the SCIF - 02 Mar - Blinken at the G20 discussing Ukraine War, Paul Whelan, START Treaty; Notes on Domestic Terrorism; more...
Inside the SCIF - 02 Mar - Blinken at the G20 discussing Ukraine War, Paul Whelan, START Treaty; Notes on Domestic Terrorism; more...
 Target USA Podcast - 01 Mar - The War in Ukraine; One Year On
Target USA Podcast - 01 Mar - The War in Ukraine; One Year On
The Hunt Broadcast - 01 Mar - Taliban hunting down US collaborators
The Latest Insights from Jeff Stein and Colleagues in SpyTalk (Substack)
01 Mar | China Shaking Up Spy Agencies? - Matt Brazil
The non-communist Chinese press was abuzz last week with rumors that the Chinese Communist Party (CCP) plans to reorganize its IC (intelligence community) by merging the Ministry of State Security and the Ministry of Public Security together into a new organ of state security, directly under the Central Committee. Citing Ming Pao (Hong Kong), China Times, a Taiwan news outlet, says here that the supposed new super-security organ, to be established under the CCP Central Committee, would be called the "Central Internal Affairs Commission" [中央内务委员会, Zhongyang Neiwu Weiyuanhui]. This rumor is also being written up in the usual Falun Gong-affiliated sources as well as Radio Free Asia’s new site. Supposedly, this reorganization will be announced during the "two sessions" (the NPC and the CPPCC) next month. I have yet to find the original Ming Pao report: I don't see it on their website and wonder if it was taken down after publication, or if it was never there in the first place. (Full article here.)
27 Feb | Afghan Treachery and Kabul's Collapse - Jeff Stein
21 Feb | A Final Word on Balloongate - Matt Brazil
18 Feb | Return to the Wilderness of Mirrors - Jeff Stein
To support SpyTalk, subscribe here.
Section III - MEMBER CONTRIBUTIONS
OpEd: China’s Trial Balloon - The American Spectator, 06 Feb 23
As the Chinese spy balloon crisis deflates, a key question remains: Why did the PRC do it? The answer might be as simple as this: Because they could. Maybe no one in Beijing believed that the Red Zeppelin would be allowed to overfly the entire United States. But then again, maybe they did. The Chinese intelligence community no doubt has a substantial personality profile on President Joe Biden, based on his self-admitted long association with President Xi Jinping. And Biden’s response to this crisis was true to form — risk averse, lacking in decisive leadership, yet claiming everything went according to plan. If any president was going to let this mess happen and still brag afterward, it would be Biden. (Full article here.)
Report: Why the Afghan Security Forces Collapsed - Special Inspector General for Afghanistan Reconstruction, February 2023
Findings: The decision by two U.S. presidents to withdraw U.S. military forces from Afghanistan fundamentally altered every subsequent decision by U.S. government agencies, the Ghani administration, and the Taliban. Actions taken by each ultimately accelerated the collapse of the ANDSF in August 2021. But the stage had been set for that collapse long before—by the failure of the U.S. and Afghan governments to create an independent and self-sustainable ANDSF, despite 20 years and $90 billion of international support. Due to the ANDSF’s dependency on U.S. military forces, the decision to withdraw all U.S. military personnel and dramatically reduce U.S. support to the ANDSF destroyed the morale of Afghan soldiers and police. The ANDSF had long relied on the U.S. military’s presence to protect against large-scale ANDSF losses, and Afghan troops saw the United States as a means of holding their government accountable for paying their salaries. The U.S.-Taliban agreement signed under the Trump administration in 2020 made it clear that this was no longer the case, resulting in a sense of abandonment within the ANDSF and the Afghan population. The agreement set in motion a series of events crucial to understanding the ANDSF’s collapse. (Full article here.)
Poem: A Smuggler's Song - Rudyard Kippling, Puck of Pook's Hill (1906)
Clandestine activity, a letter for a spy, bribes, look outs...all fixed in verse and later turned into musical pieces and more. "If you wake at midnight, and hear a horse’s feet, Don’t go drawing back the blind, or looking in the street, Them that ask no questions isn’t told a lie. Watch the wall, my darling, while the Gentlemen go by! Five and twenty ponies, Trotting through the dark, Brandy for the Parson, ’Baccy for the Clerk, Laces for a lady, letters for a spy, And watch the wall, my darling, while the Gentlemen go by!" (Full poem and some commentary here.)
Article: US Cyber Command developing own intelligence hub - C4ISRnet, 01 Mar 23
U.S. Cyber Command, tasked with defending Department of Defense IT networks and coordinating cyberspace operations, is developing its own intelligence hub, after years of relying on other information-gathering sources. The endeavor, still in its infancy, is meant to buttress data collection and augment CYBERCOM’s understanding of foreign capabilities in the ever-expanding cyber realm. “We know everything about a T-72 tank, all the way to every nut and bolt in there, for the Army,” Col. Candice Frost, the leader of the Joint Intelligence Operations Center at CYBERCOM, said at a Feb. 28 event hosted by Billington Cybersecurity in Virginia. “But we don’t have that for networks, with respect to an all-source capability.” “Congress asked us: Do we need a center that is focused on all-source intelligence to support Cyber Command, in the cyber domain?” Frost said. “And the answer was a resounding yes.” (More information and order here.)
Article: In Neural Networks, Unbreakable Locks Can Hide Invisible Doors - Quanta Magazine, 02 Mar 23
Machine learning is having a moment. Yet even while image generators like DALL·E 2 and language models like ChatGPT grab headlines, experts still don’t understand why they work so well. That makes it hard to understand how they might be manipulated. Consider, for instance, the software vulnerability known as a backdoor — an unobtrusive bit of code that can enable users with a secret key to obtain information or abilities they shouldn’t have access to. A company charged with developing a machine learning system for a client could insert a backdoor and then sell the secret activation key to the highest bidder. To better understand such vulnerabilities, researchers have developed various tricks to hide their own sample backdoors in machine learning models. But the approach has been largely trial and error, lacking formal mathematical analysis of how well those backdoors are hidden. (Full article here.) (Note: May require a one time free registration or sit behind a pay wall.)
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
Analysis: Skies, Spies, and Scientific Surveys – The Legal Aspects of Chinese Unmanned Balloon Flight Over American Territory - European Journal of International Law, 06 Mar 23
Earlier this month, the US shot down an aerial object which had been seen traversing through parts of Alaska, Idaho, and Missouri. The Biden Administration claims that the object was an unmanned high-altitude surveillance balloon deployed by the PRC as ‘part of a larger Chinese surveillance-balloon program’. The PRC’s Ministry of Foreign Affairs has denied these allegations and purports that the unmanned balloon was ‘a civilian airship used for research, mainly meteorological, purposes’. In this article, I shall answer a series of questions related to the legality of conducting flights over the territory of a foreign state for meteorological and surveillance purposes, respectively, under the 1944 Convention on International Civil Aviation (“Chicago Convention”). (Read full report here.)
Audio: Matt Olsen on Foreign Intelligence Surveillance Act Section 702 (86 mins) - Lawfare, 01 Mar 23
Matthew Olsen, the Assistant Attorney General of the National Security Division at the U.S. Department of Justice, gave yesterday a major address at the Brookings Institution. He talked about FISA Section 702, the section of the Foreign Intelligence Surveillance Act that allows U.S. intelligence authorities to collect against targets reasonably believed to be overseas when their signals pass through the United States. The provision comes up for reauthorization this year, and Olsen argues that it is imperative that Congress act to reauthorize it. This audio from the Brookings event includes an introduction from Camille Busette, the Interim Vice President for Governance Studies at the Brookings Institution; remarks from Olsen; a Q and A between Olsen and Lawfare editor-in-chief Benjamin Wittes; and questions from the live audience. (Listen here.)
OpEd: Chinese Espionage - The Unfortunate Reason Behind its Great Success - or it must be shut down - Japan Forward, 02 Mar 23
Spy balloons are one small part of an enormous, "whole of society" decades-long Chinese espionage campaign against the United States. And unfortunately, it has been successful. As with most intelligence operations, it's a mix of technical and human platforms that aim to obtain (by any means) other countries' secrets. However, the People's Republic of China (PRC) operates on a completely different scale. It's not just the Ministry of State Security (MSS) deploying officers to recruit spies. China's 2017 National Intelligence Law explicitly requires all Chinese companies and citizens to assist: "An organization or citizen shall support, assist in and cooperate in national intelligence work in accordance with the law and keep confidential the national intelligence work that it or he knows. The state shall protect the individual organization that has supported, assisted in, or cooperated in national intelligence work." (Full report here.)
Analysis: How the Chinese spy agency MSS disrupts the world - First Post, 02 Mar 23
China’s premier spy agency Ministry for State Security (MSS) has been on the forefront of setting up and running a ruthless global espionage and counter-espionage network. MSS was set up in 1983 to bring together multiple agencies which were already functional so that Chinese spy networks could work more cohesively as well as ruthlessly. Officially the proposal to set up this agency was brought by Zhao Ziyang at the first session of the sixth National People’s Congress (NPC) on June 20, 1983. The NPC can be broadly termed as the Parliament of China. Ziyang proposed the establishment of a state security ministry “to protect the security of the state and strengthen China’s counterespionage work.” The NPC approved it and voted to appoint Ling Yun as the first minister. The inaugural meeting of the MSS was held on 1 July, 1983 to announce the formal establishment of the. The opening speech was delivered by chairman Chen Pixian of the ‘Central Political-Legal Commission’ one of the key bodies of CCP. He categorically said, “Doing state security work well will effectively promote socialist modernisation and the cause of realising the unification of the motherland opposing hegemonism, and defending world peace.” The Chinese intent was clear: MSS would be its ace espionage and counter-intelligence agency. (Full report here.)
Report: National Threat Assessment 2023 - Norwegian Police and Intelligence Services, March 2023
In the National Threat Assessment (NTV), the Norwegian Police Security Service (PST), The Norwegian Intelligence Service (NIS), and The Norwegian National Security Authority (NSM) present an unclassified review of the threats facing Norwegian society this year. The assessment focuses on the intel- diligence threat, devoting special attention to Russian and Chinese intelligence activities, as well as to the threat of terrorism and threats facing Norwegian dignitaries. The NTV has been compiled during a time impacted by Russia’s war of aggression against Ukraine, as well as by the shoot- ing incident in Norway on 25 June 2022, which PST considers an Islamic extremist terrorist attack. The war has profoundly altered relations between Russia and Western countries, including Norway. This impacts the threat posed by Russian intelligence services in Norway. However, the intelligence threat posed by other countries will continue to be characterised by continuity, and no major changes are expected during the current year. (Full report here.)
OpEd: We Have a New National Cybersecurity Strategy. Now What? - Cipher Brief, 03 Mar 23
The new National Cybersecurity Strategy is clear and concise, laying out the case for a more robust and engaged approach to defending our national critical infrastructure from a growing list of threats in cyberspace. Implementing it is the next big challenge. The document articulates priorities and affirms for our allies and adversaries alike, that we will defend our interests and values in cyberspace. The key to long-term improvements in national cyber resilience, however, is not just the articulation of policy. It will be in the implementation and resourcing of the guidance laid out in the strategy. The new strategy is consistent with, and expands on, the work of the Cyberspace Solarium Commission (on which we both served), and it is informed by three additional years of attacks on our nation’s security, prosperity and democracy by nation-state and criminal actors. This administration cut its cyber teeth on responses to Russia’s years-long, sophisticated cyber espionage campaign against the U.S. government through U.S. software company SolarWinds and China’s vast espionage effort exploiting Microsoft vulnerabilities to target the private sector. Then, came criminal ransomware attacks against U.S. critical infrastructure and the discovery of a dangerous vulnerability at the heart of the software in millions of devices around the world. (Full article here.)
Video: Counter Intelligence Today (75 mins) - GMU Hayden Center for Intelligence Policy, 03 Mar 23
This week, Lawfare Publisher David Priess wore his hat as a Senior Fellow at George Mason University's Michael V. Hayden Center for Intelligence, Policy, and International Security to host a rare live conversation on counterintelligence with leading practitioners. His guests were Mirriam-Grace MacIntyre, Executive Director of the National Counterintelligence and Security Center (NCSC), and Alan Kohler, Assistant Director of the Counterintelligence Division at the FBI. They discussed the organization known as the NCSC, the role it plays across the U.S. Government and beyond, and how the FBI's long-running counterintelligence efforts play into it. They talked a lot about the People's Republic of China and its extensive intelligence efforts against the U.S., as well as about counterintelligence and science, outreach to the public on these issues, how Congress fits in, and more. (Watch here.)
Paper: The uses and utility of intelligence - The case of the British Government during the War of the Spanish Succession - Journal of Intelligence History, Released March 2023 (Originally published 17 Nov 21)
It is usually taken for granted that intelligence organisations provide information for decision-making and that the knowledge produced in the process is therefore deeply utilitarian. Drawing on organisational sociology, this article draws on a case study of English intelligence efforts during the War of the Spanish Succession (1701–1714) to reflect critically on the assumed direct relationship between intelligence-gathering and political decision-making. In eighteenth-century England, intelligence frequently fulfilled other, often more symbolic functions, for example when access to intelligence was employed to legitimise individual actors. In this sense, intelligence was doubtlessly useful, albeit in other ways than generally postulated by intelligence theory. These observations strongly suggest a ‘missing dimension’ in the history of intelligence in other periods as well as intelligence theory more generally. (Full report here.)
Article: The Spy Whisperer - Psychiatry and Intrigue with Dr. Kenneth Deklev - SpyScape, 01 Mar 23
The Cold War was over by the time US State Department Psychiatrist Kenneth Dekleva arrived in Russia in the early 2000s. The KGB was disbanded but Moscow was still a hardship post. US Embassy staff were watched 24/7 with audio and video surveillance at home and minders on the streets. Occasionally, Russia’s secret police would even break into their apartments. In one instance, a Moscow diplomat had a family member who was being treated in the US for a serious illness. He arrived home to find a Post-it Note: “How’s your wife?” The intimidation was designed to pressure the Americans to leave - ‘get off the X', in espionage parlance - and the Russians were world-class experts at it. Dr. Dekleva recalled counseling embassy staff about coping strategies and even found the surveillance exasperating himself at times. “Yes, like everyone. It’s annoying,” Dekleva admits, but he deflected it with humor. (Full report here.)
Analysis: The great power pivot and the intelligence community - FCW, 27 Feb 23
After more than two decades of focus on international counterterrorism strategy and operations, the U.S. intelligence community is pivoting toward the intensifying Great Power competition with China and Russia – but this time, the potential battlefield has extended beyond air, sea and land to both space and cyberspace. Private defense contractors played a pivotal role in the development and production of military technology throughout the Cold War arms race, working alongside the Department of Defense and various military research and development organizations to invent world-changing weaponry. Col. Michael Medgyessy, chief information officer and chief data officer for the Air Force Intelligence Community, said at intelligence conference last December that "the requirement to shift from an insurgency fight to a peer competition" has driven the community into "changing – or needing to change – our industrial age processes into a digital age." (Full report here.)
Video: House Permanent Select Committee on Intelligence Hosts Think Tank Leaders to Discuss Intelligence Issues (134 minutes) - HPSCI, 28 Feb 23
Watch as teh House Permanent Select Committee on Intelligence hosts a broad ranging discussion with the leaders of numerous leaders of think tanks that have long partnered with the U.S. Intelligence Community. (Watch here.)
Infographic and Report: How the Russian Invasion of Ukraine Impacts Science and Academia - Visual Capitalist, 24 Feb 23
On February 24, 2022, Russia invaded the eastern territories of Ukraine, claiming ownership of the Donetsk and Luhansk regions. This began one of the largest military conflicts in modern European history. After a year of casualties, structural devastation, and innumerable headlines, the conflict drags on. Many report the impacts to the economy, social demographics, and international relationships, but how do science and academia fair in the throes of war? Within the actions and responses of the conflict, we take a look at how six key scenarios globally shape science. (Access visual tool and full report here.)
Intelligence in History - A Collection of Recent Content
- Article - Early Anti-Eavesdropping / Wiretapping Invention - Spy Busters, 06 Mar 23
- Article - Josephine Baker: Actress Turned Spy - Grey Dynamics, 05 Mar 23
- Video - USS Halibut, Cold War Spy Sub (52 minutes) - Sub Brief, 02 Mar 23
- Article - Smear, frame, mislead: The British army in Ireland - Declassified UK, 01 Mar 23
- Article - Behind Enemy Lines: CIA POWs in China - Foreign Affairs, 28 Feb 23
- Article - Richard Sorge - Journalist and Spy (Substack), 27 Feb 23
- Paper - Knowing the ‘hereditary enemy’: Austrian-Habsburg intelligence on the Ottoman Empire in the late sixteenth century - Journal of Intelligence History, Released March 2023 (Originally published 01 Mar 22)
- Paper - The secret service of Renaissance Venice: intelligence organisation in the sixteenth century - Journal of Intelligence History, Released March 2023 (Originally published 13 Nov 22)
- Paper - Case studies in early modern European intelligence - Journal of Intelligence History, Released March 2023 (Originally published 18 Nov 22)
True Intelligence Matters in Film - Bonhoeffer - Agent of Grace - Eric Till (2000)
 What is a moral person to do in a time of savage immorality? That question tormented Dietrich Bonhoeffer, a German clergyman of great distinction who actively opposed Hitler and the Nazis. His convictions cost him his life. The Nazis hanged him on April 9, 1945, less than a month before the end of the war. Bonhoeffer's last years, his participation in the German resistance and his moral struggle are dramatized in this film. More than just a biographical portrait, Bonhoeffer: Agent of Grace sheds light on the little-known efforts of the German resistance, including how Bonhoeffer was issued false documents by officers within the Abwer (military intelligence) as part of a cover story of being an intelligence agent for the nation and the similar use of false documents from with the German intelligence community to facilitate the flight of some Jews. It brings to a wide audience the heroic rebellion of Bonhoeffer, a highly regarded Lutheran minister who could have kept his peace and saved his life on several occasions but instead paid the ultimate price for his beliefs.
What is a moral person to do in a time of savage immorality? That question tormented Dietrich Bonhoeffer, a German clergyman of great distinction who actively opposed Hitler and the Nazis. His convictions cost him his life. The Nazis hanged him on April 9, 1945, less than a month before the end of the war. Bonhoeffer's last years, his participation in the German resistance and his moral struggle are dramatized in this film. More than just a biographical portrait, Bonhoeffer: Agent of Grace sheds light on the little-known efforts of the German resistance, including how Bonhoeffer was issued false documents by officers within the Abwer (military intelligence) as part of a cover story of being an intelligence agent for the nation and the similar use of false documents from with the German intelligence community to facilitate the flight of some Jews. It brings to a wide audience the heroic rebellion of Bonhoeffer, a highly regarded Lutheran minister who could have kept his peace and saved his life on several occasions but instead paid the ultimate price for his beliefs.
More on this based-on-true-events production here.
Walking Tours - Washington, DC - Sundays (Dates/Times Vary)
Former intelligence officers guide visitors on two morning and afternoon espionage-themed walking tours: "Spies of Embassy Row" and "Spies of Georgetown." For more information and booking, click here or contact rosanna@spyher.co
Section V - Books, Research Requests, Jobs, Obituaries
Books — Forthcoming, Newly Released, Overlooked
 The Dirty Tricks Department: Stanley Lovell, the OSS, and the Masterminds of World War II Secret Warfare
The Dirty Tricks Department: Stanley Lovell, the OSS, and the Masterminds of World War II Secret Warfare
by John Lisle
(St. Martin's Press, 07 Mar 23)
In the summer of 1942, Stanley Lovell, a renowned industrial chemist, received a mysterious order to report to an unfamiliar building in Washington, D.C. When he arrived, he was led to a barren room where he waited to meet the man who had summoned him. After a disconcerting amount of time, William “Wild Bill” Donovan, the head of the OSS, walked in the door. “You know your Sherlock Holmes, of course,” Donovan said as an introduction. “Professor Moriarty is the man I want for my staff…I think you’re it.” Following this life-changing encounter, Lovell became the head of a secret group of scientists who developed dirty tricks for the OSS, the precursor to the CIA. Their inventions included bat bombs, suicide pills, fighting knives, silent pistols, and camouflaged explosives. Moreover, they forged documents for undercover agents, plotted the assassination of foreign leaders, and performed truth drug experiments on unsuspecting subjects. Based on extensive archival research and personal interviews, The Dirty Tricks Department tells the story of these scheming scientists, explores the moral dilemmas that they faced, and reveals their dark legacy of directly inspiring the most infamous program in CIA history: MKULTRA.
Order book here.
 We Were Never There: Volume 2: CIA U-2 Asia and Worldwide Operations 1957-1974
We Were Never There: Volume 2: CIA U-2 Asia and Worldwide Operations 1957-1974
by Kevin Wright
(Helion and Company, 01 Feb 22)
Devised by Kelly Johnson and operated by the CIA from 1956-74, the U-2 is the world’s most famous ‘spyplane.’ It flew at unprecedented altitudes and carried the most sophisticated sensors available, all in the greatest secrecy. The second volume of We Were Never There concentrates on the period of operational missions mainly across Asia from 1957-74. The book utilizes a large number of declassified documents to explore some of the remaining secrets of these missions. The book starts by looking at some of the missions conducted by the CIA’s Detachment ‘C’ U-2s against key targets in the Soviet Far East up to Mayday 1960. It moves on to explore in detail the overflights of the Peoples Republic of China by Nationalist Chinese pilots in conjunction with the CIA. In particular, the study of Project TACKLE looks at efforts to gain intelligence on the PRC’s expansive nuclear program from the early 1960s. This is supplemented with details of Taiwanese/CIA operations against North Korea and its Yongbon nuclear reactor. It presents target images and reveals detailed routes for many of these overflights that have not been publicly seen before. While the USAF took the lead in operations against Cuba, the book explores the earlier CIA missions against Cuba during the Bay of Pigs landings and the missile crisis. Another chapter explores the efforts to equip the U-2 for operations from US Navy aircraft carriers. Detachment G, based at Edwards AFB, had a worldwide contingency role, able to quickly deploy anywhere in the world. It undertook missions targets in Tibet, the PRC, Vietnam, Cambodia, Laos, British Guiana, Venezuela and elsewhere. A section of the book examines the development of the U-2R, a major update of the original aircraft, making it larger and much more capable. Its handling characteristics and comparisons with the U-2C are explored with the help of interviews with two former USAF U-2 pilots who flew both models of the aircraft. The final chapter looks at the return of the U-2 to Europe, in particular the UK, for training missions from the late 1960s. It covers details on operations over the middle east monitoring ceasefire arrangements between Israel and its neighbors in 1970 and 1973. It ends with the phasing out of Agency U-2 operations, the closure of projects TACKLE and JACKSON and an evaluation of the U-2’s contribution to aerial intelligence collection.
Order book here.
 Disrupting Time: Industrial combat, espionage, and the downfall of a great American company
Disrupting Time: Industrial combat, espionage, and the downfall of a great American company
by Aaron Stark
(02 Mar 23 (Audiobook), 09 Dec 22 (Hardback))
In the fall of 1876, two Swiss spies came to America and conducted some of the most covert and consequential industrial espionage in history, changing the course of the global watch industry forever. Had the events of 1876 never happened, we would likely know little of Swiss watches today. Disrupting Time is a true historical narrative of business strategy, espionage, and consequences. Set during the Centennial Exhibition in 1876, a great world’s fair in Philadelphia, it details the story of Jacques David and Theo Gribi. Having attended the Centennial Exhibition and witnessed the powerful Waltham Watch Company’s frighteningly novel assembly line exhibit, they knew it spelled the end of their Swiss industry. Rather than be deterred, Gribi and David were commissioned by the Society of Jura Industries, a Swiss trade association, to acquire the secrets of America’s technology sector – the American watch industry. They captured their intelligence in a 130-page report that would remain mostly secret until 1992. Disrupting Time details the never-before-told story of David and Gribi’s secrets and mission, showing how they used disguises, agent recruitments, and other classic espionage methods to steal the secrets of America’s technology sector of the era. Disrupting Time details a fascinating tale of cutthroat competition, industrial espionage, societal development, and a great world’s fair using the archival reports and letters of the spies, the Waltham Watch Company, and records from the 1876 Centennial Exhibition. It specifically examines the years 1857 to 1900. This period catalyzed modern, industrial watch production and solidified the Swiss’ role as the world’s best watchmakers, a reputation which has endured through many subsequent chapters of their history. The competition in this era was so intense it was even referred to as “combat of industry” by contemporary observers. It is a chronicle of strategy, competition, espionage, decisions, and consequences that shaped the global watch market at the turn of the twentieth century. It is the account of a remarkable turn of events driven by cunning spies, visionary leaders, and strategic choices that put the Swiss and American watch industries on entirely different trajectories. The themes of this book are explored through the eyes of Waltham, the Swiss watchmakers, and their main characters: Royal Robbins, Ambrose Webster, Jacques David, Theophilus Gribi, and Edouard Favre-Perret. This is the story of industrial combat, an industry ‘broken apart’ and ‘thrown into disorder,’ and how a cottage industry of Swiss watchmakers organized to defeat an American industrial power. About the Author: Aaron Stark is the author of the book Disrupting Time: Industrial combat, espionage, and the downfall of a great American company. He is also the co-author of the Harvard Business School strategy case study "Stealing Time: America's disruption of the Swiss watch industry" (available through Harvard Business Publishing). Before entering business, he was an assistant professor of economics at West Point, with a specialization in finance. He holds an MBA from Harvard Business School with a focus on finance and business strategy, and a BS in Economics from West Point. He is a veteran of the US Army with two combat tours in Afghanistan, serving as an Apache helicopter pilot.
Order book here.
Research Requests and Academic Opportunities
Call for Sources: Intelligence Officers Who Lived in Spain in the 1970s
Spanish journalist Francisco Jiménez is preparing a documentary about the intelligence services in Spain in the 70s. He is looking for intelligence officers who worked in Spain in those years. If you are willing to assist Franciso, he can be reached at fjimenez@globomedia.es.
The Washington Post is developing a multipart audio documentary series (i.e. podcast) chronicling the Grenadian revolution and the US intervention in 1983. They’ve interviewed nearly 100 people so far, ranging from the heads of state, former Grenadian officials, current and former US officials, veterans, and intelligence officers. They're looking for people who served at the time and may be knowledgeable about intelligence activities in Grenada and the southern Caribbean between 1979 and Operation Urgent Fury. They would also be interested in speaking with anyone who knew Leonard Barrett during the same period. If anyone is interested in participating, please reach out to Washington Post reporter Ted Muldoon via email at ted.muldoon@washpost.com or on Signal at 651-497-5449.
Academic Opportunity: Critical Thinking for Intelligence Analysis Course - 21 Apr 23, 0800-1700 (ET) - Virtual
This course will help Intelligence Analysts improve their critical thinking skills. It begins by reviewing the basic characteristics of quality intelligence analysis (and the challenges to producing it) and the methodology for building an analytic argument. The course continues with a discussion of the mental traits and habits that inhibit critical thinking and objectivity. Finally, the course discusses several types of structured techniques designed to inject critical thinking and analytic rigor into intelligence production. $600 fee. (More information and registration here.)
Academic Opportunity: The International Security and Intelligence Programme - 9 July to 5 August 2023 - Magdalene College, Cambridge
Chaired by Sir Richard Dearlove the former Chief of the British Secret Intelligence Service, the Cambridge Security Initiative (CSi) launched the ISI Programme in 2016. The purpose of this unique programme is to provide an opportunity for participants to meet and work with leading academics and practitioners from the intelligence and security communities in the historic setting of one of the world’s foremost universities. The Programme is run in partnership with the Department of War Studies at Kings College, London. (More information and registration here.)
Call for papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
History shows that without planning for post-war reconstruction, apparent victory in war can lead to long-term defeat. On the other hand, wise post-war planning can lead to friendly, peaceful, and profitable relations between victor and vanquished. For political, socio-economic and security-related planning, intelligence plays a crucial role in estimating capabilities, securing infrastructure, locating persons of interest, and rebuilding. In honor of the 75th anniversary of the European Recovery Program (Marshall Plan) after the Second World War, the editors are particularly interested in papers dealing with intelligence concerning post-war reconstruction initiatives and planning connected to historical and recent conflicts. Both case studies and theoretical and methodological approaches are welcome. The studies may include, but do not have to be focused on, the following questions and issues:
- The role of diplomatic and military intelligence during the conflict as preparation for post-war reconstruction, from the conceptual to the practical.
- What intelligence needs to be collected to secure and boost reconstruction?
- What contacts, networks, and infrastructure are necessary for intelligence to be effective?
- Who has been or should be approached and/or recruited for reconstruction efforts based on intelligence?
- When has intelligent post-war planning (or its opposite) been historically evident?
- How should intelligence interact with formerly warring parties and international organizations to empower practical reconstruction efforts?
- What intelligence collection challenges have services encountered in working for post-war peace?
- How did intelligence factor in the European Recovery Program?
- What was George C. Marshall’s position on the role of intelligence in general or concrete examples related to “his” plan?
01 Nov 23 deadline. More information and submission instructions here.
Search for stories: Matt Brazil, an AFIO member in the San Francisco Chapter and co-author of Chinese Communist Espionage, An Intelligence Primer (Naval Inst. Press, 2019) is writing a second work on Beijing's worldwide espionage and influence offensive. As part of that effort, he seeks interesting stories of encounters with China's civilian and military intelligence apparatus. If you are interested in telling your story or you know someone who would be, Matt can be reached via matthew.brazil@gmail.com or his website www.mattbrazil.net.
Search for information: Author and AFIO member Toby Harnden is researching recipients of CIA gallantry awards (DCI's OPA is assisting). Harnden is eager to speak to anyone with memories of, information about, or pointers toward Bob A. Plan and Arthur J. Porn. Plan was born in Croatia in 1920 and served with the OSS in Yugoslavia 1944-45. He became a CIA contractor, working as a career agent and translator, and was based in Greece in the 1950s and Mexico in the 1960s. He was parented by EUR Division when he came out of retirement to enter Tehran in 1980. Porn, born in 1930, was a WH case officer from 1958 who was based in Argentina, Honduras and Bolivia in the 1960s and 1970s. He was honored for an act of bravery in Bolivia in 1970. Please contact tobyharnden@gmail.com or 202-213-3775.
Search for information: Searching for information on a CIA "intelligence operation" carried out during the Clinton administration in 1997 or 1999 aimed at Iran and/or its MOIS in response to Iran's involvement in the 1996 Khobar Towers bombings. Clinton's counterterrorism chief Richard Clarke made a brief reference to this operation on p. 129 of his book Against All Enemies; George Tenet made a possible reference to this operation on p. 124 of his book At the Center of the Storm; and Bruce Riedel posted a reference to it here in his article "The Iran Primer: The Clinton Administration." He called it "Operation Sapphire" - not to be confused with Operation Sapphire aimed at Kazakhstan. Also, searching for information on a bomb found on a bridge in Manila, Philippines around November 23, 1996 when President Clinton was in the city. Contact: dpluchinsky@rocketmail.com.
Search for information: Dr John Gentry of Georgetown University seeks information on what ways, to what extent, at what agencies, and with what implications/consequences are DEI (diversity, equity, inclusion) policies damaging the IC and DOD. Request examples and assessments that link senior-level policies, and middle managers' interpretations of them, to specific organizational and personal actions and then to actual consequences in sufficient volume and detail to be able to make a coherent argument. Anonymity assured. Contact: jag411@georgetown.edu.
Call For Papers: The Struggle in the Israeli Security Zone in South Lebanon, 1985-2000, Israel Affairs
In June 1985, the Israel Defense Forces (IDF) de jure completed its withdrawal from Lebanon to the Israeli borders. De facto, Israel left in its hands a strip of land, about 15 kilometers from its border, in which its ally, the South Lebanon Army (SLA), operated. This strip of land came to be known as the Israeli Security Zone. The idea was that the SLA would be almost independent, while the IDF would intervene only when necessary in the battle against Palestinian and Shiite groups and supervise the SLA. Soon, however, the IDF became more involved, building military posts within the Security Zone, reinforcing itself, and encountering new challenges. In May 2000, Israel pulled its forces back to its borders and the SLA collapsed, along with the Security Zone. The 15 years of fighting in the Security Zone were rarely mentioned within Israeli society, let alone in the academic sphere. Only in recent years has the Israeli public become aware of this period after many soldiers who served in the Security Zone began sharing their memories through books and social media. The campaign to raise awareness of the period successfully ended when in March 2021, Israel officially recognized this period as one of warfare. This special issue aims to interdisciplinarily bridge the gap in the academic discourse regarding the war in the Security Zone. The editors are interested in articles dealing with various topics concerning the 1985-2000 war in the Security Zone. 30 March 2023 deadline. For more information, including submission instructions and suggested topics, click here.
Call For Articles: AFIO Journal, The Intelligencer
For the past four years, AFIO has included in The Intelligencer a series of articles on “when intelligence made a difference.” Written by scholars, intelligence practitioners, students, and others, they cover events from ancient times to the modern world and in many countries. AFIO is soliciting articles for future issues. Most articles run between 2,000 and 3,000 words, although some are longer or shorter. If you have an idea for an article that fits the theme, email senior editor Peter Oleson at peter.oleson@afio.com.
Jobs
Faculty Opening - Adjunct Faculty, Intelligence Analysis - Krieger School of Arts and Sciences, Advanced Academic Programs, Johns Hopkins University, Online
The Advanced Academic Programs (AAP) division seeks non-tenure track adjunct faculty to teach several courses within the MS in Intelligence Analysis program. The course(s) will be taught fully online beginning in Summer 2023 and beyond. Candidates with online course development and teaching experience and those with experience teaching and engaging students from diverse backgrounds are of particular interest. Full details and online application instructions can be found here.
Retired Federal Government Employees Wanted - National Security Agency - Fort Meade, Maryland
The National Security Agency (NSA) may occasionally need skilled civilian retirees to augment the existing work force on high priority projects or programs. In order to fill these temporary positions quickly, we need to know who may be interested and available to return to work with us on a short notice basis as well as their skills. Retirees provide expertise and corporate knowledge to temporarily support mission requirements, manpower shortfalls, and/or mentor the next generation of Agency employees. Salary Range: $86,335 - $170,800.
Additional information and application here.
Assistant/Associate Professor of Intelligence Studies (Global Security and Intelligence Studies) - Embry-Riddle Aeronautical University - Prescott, Arizona
Embry-Riddle Aeronautical University's Prescott, Arizona campus is accepting applications for a tenure-track assistant or associate-level professor of intelligence studies to teach intelligence courses to students in the Global Security and Intelligence program. The successful candidate will teach students about the intelligence community, strategic intelligence, the intelligence cycle and intelligence analysis, writing, and briefing. Prior experience working in the intelligence community is strongly preferred. We are interested in candidates with teaching acumen in intelligence analysis and writing using structured analytical techniques.
Additional information and application here.
Teaching Associate - Intelligence and National Security Studies - Coastal Carolina University, South Carolina
The Department of Intelligence and Security Studies ( ISS ) at Coastal Carolina University is accepting applications for a pool of Teaching Associates (part-time adjunct faculty) to teach introductory and undergraduate elective course offerings for the program beginning in August 2022. While the ad is open to any specialization within the field of study, courses in the areas of homeland security, law enforcement intelligence, counter-narcotics, and cybersecurity are of particular interest. Course offerings can be in a face-to-face or synchronous online modality. To be considered, candidates must have a masters or doctoral degree in a relevant subject area. Prior professional experience in the profession, as well as prior teaching experience are preferred.
Additional information and application here.
Obituaries
![]() Colonel Bill Roche — Decorated Defense Attache, CIA Consultant
Colonel Bill Roche — Decorated Defense Attache, CIA Consultant
Colonel William (Bill) Lawrence Roche (USAF Retired), 98, passed in Colorado Springs, Colorado, on Wednesday, February 22, 2023. Bill was born in Lexington, KY, attended Lexington Latin High School, and was one of eight students to graduate in 1940. At the first opportunity after graduation, he enlisted in the Army Air Corps and became a B-17 Flying Fortress waist gunner. During WWII he was stationed at Deopham Green, England flying missions with the 452nd Bomb Group, 8th Air Force. On two occasions he was shot down, once crash landing in France, and then behind Russian lines in Poland where he was interred by the Russians and eventually repatriated to his unit three months later. After the war, Bill returned to Lexington, KY, and attended the University of Kentucky. Subsequently he was commissioned as a Second Lieutenant, serving in the US Air Force for the next 33 years as linguist and Intelligence Officer. Upon graduating from language school as a Russian linguist, Bill was assigned to the new US Air Force Academy and helped establish the Foreign Language Department where he taught students from the class of 1959, the first graduating class.
At the height of the Cold War, between tours teaching at the Academy, Bill was assigned to multiple sensitive diplomatic positions as an attaché at the US Embassies in Moscow, Prague, and Belgrade. He was stationed in Berlin, Germany where he was assigned to the elite US Military Liaison Mission in Postdam, East Germany. During his long and distinguished US Air Force career, he earned the US Legion of Merit along with numerous other awards, medals, and decorations. Upon his retirement, at the request of the CIA, Bill continued to work as a consultant. In 2008 Bill was inducted into the Defense Intelligence Agency (DIA) Attaché Hall of Fame and in 2013 Bill was awarded the French Legion of Honor for his service to the French during WWII.
Colorado funeral services will be held March 15, 2023, at St. Peter’s Catholic Church in Monument, Colorado with viewing at 9:30am and Mass starting at 10am with reception afterward. Services will be livestreamed. (https://www.petertherock.org) Bill will be buried at Arlington National Cemetery on a date TBD.
![]() Dennis Moran — Career CIA Officer
Dennis Moran — Career CIA Officer
Dennis Joseph Moran passed away at the age of 70 surrounded by his loved ones after a short battle with cancer on the evening of Wednesday, February 15, 2023 in Elizabeth City, North Carolina. Born in Dallas, Texas, Dennis graduated from Essex Catholic High School in New Jersey before completing a degree in photo science from the Rochester Institute of Technology. A true patriot, Dennis enjoyed a long and fulfilling career with the Central Intelligence Agency, where he traveled the world while faithfully serving his country for more than 41 years.
![]() John Brady — Career CIA Case Officer
John Brady — Career CIA Case Officer
John L. Brady, 82, passed away at Brandywine Assisted living in Rehoboth Beach, Delaware on February 28, 2023 from Alzheimers and Parkinson’s. Born in Mankato, Minnesota, John joined his parent when they were assigned to the Agency for International Development in Kirkuk, Iraq. The Brady family was evacuated to Rome, Italy during the 1958 coup in Iraq. There he finished his high school years at The Notre Dame Academy. At that point, John realized that the life for him was to be overseas. He studied foreign affairs at the Foreign Service School at Georgetown University. Following Georgetown, John entered the Officer Candidate program in the Navy. After his tour in the Navy, he worked for two years at the Defense Intelligence Agency. In 1967, John joined the CIA. His first assignment was in Jeddah, Saudi Arabia. After that, he studied Arabic in Beirut, Lebanon. John spent 35 years as a case officer working mainly in the Middle East as Chief of Station in Ankara, Khartoum, Damascus and Yemen. He also, served in Mumbai, India and Bonn, Germany. John retired from the CIA in 2011. After retirement, John worked in a contract capacity.
![]() Bernard D'Ambrosio — Career CIA Operations Officer
Bernard D'Ambrosio — Career CIA Operations Officer
Bernard F. D'Ambrosio, 91, passed away in his sleep on February 22, 2023 at his independent living facility in Greenspring of Springfield, VA. Bernard was born in Cambridge, Massachusetts, attended Somerville High School, and enlisted in the USMC, serving in the 1st MARDIV during the Korean War from 1952-54. Upon returning from Korea, Bernard graduated from USC in Southern California, then earned a Master's degree from Tuft's University at the Fletcher School of Law and Diplomacy in 1959. Fully enjoying his contributions as an Operations Officer during his 28 year career in the Central Intelligence Agency (CIA) from 1959 to 1987, he served in Burma (Myanmar) twice, Laos, Vietnam, Thailand, Indonesia, and Honolulu, Hawaii where he retired.
![]() Frank Knott — Career Foreign Service Officer
Frank Knott — Career Foreign Service Officer
Frank Matthew Knott passed on Friday, March 3rd, 2023. Born in Washington, DC, he attended Washington-Lee High School before moving with his family to Japan for his senior year. The assignment was part of his father’s work in the foreign service, and Frank decided to remain with his family in Japan following his graduation, and work for a year at the US government offices before starting university. It was that assignment that solidified his interest in the practical and operational side of government service and foreign relations. Following a bachelor’s degree from the University of Massachusetts and a master’s degree from Pennsylvania State University, he spent 46 years working in foreign service endeavors before retiring. His continued passion for foreign relations and government service was evident in many of the family conversations. Though firm in his convictions, he was a lifelong learner and enjoyed a spirited discussion.
Section VI - Events
16 Mar 23 (Thursday), 1130 (MST) - In Person - Colorado Springs - The AFIO Rocky Mountain Chapter hosts Dave Humpert, discussing "1983 The Year of Maximum Danger." ABSTRACT: "During my first years in Washington, I think many of us in the administration took it for granted that the Russians, like ourselves, considered it unthinkable that the United States would launch a first strike against them. But the more experience I had with the Soviet leaders and other heads of state who knew them, the more I began to realize that many Soviet officials feared us not only as adversaries but as potential aggressors who might hurl nuclear weapons at them in a first strike." President Ronald Reagan - "The American intelligence misconception was not to fully realize the nature of Soviet fears and the implication of those fears….Understanding other people's misconceptions is a long-standing problem in intelligence analysis."
BIO: During his varied career as a USAF Soviet/Russian military and political specialist, Dave relied on his knowledge of Russian political and military history and its culture with two degrees in Russian Area Studies. His Russian language ability was invaluable as an interpreter, translator, and source-language analyst in a variety of challenging assignments for the USAF and the operational intelligence community. In 2002, Dave retired from the USAF and began a career in DIA as the Senior Analyst for Political-Military Strategic (Russia) issues with the J2 Directorate, NORAD/USNORTHCOM. He performed additional intelligence duties for CIA, NSA and Department of State until his final retirement in 2016. This is an in-person event. For event location and other information, contact Steve Pease at steve13507@gmail.com.
13 Apr 23 (Thursday), 1130 (PST) - In Person - San Francisco - The AFIO Andre LeGallo Chapter hosts Richard E. Hanson on CIA Operations in Viet Nam. No-host cocktail. Location: Basque Cultural Center, 599 Railroad Avenue, South San Francisco, CA. Please contact Mariko Kawaguchi, Board Secretary at afiosf@aol.com for questions. Students: please e-mail your school ID to get sponsored. Register here.
21 April 2023(Friday), 1030 (EST) - In-Person Tysons, VA - HOLD THE DATE for AFIO National Spring Luncheon. Presentations by LTG Michael Groen (USMC – ret), former Commander of the Joint Artificial Intelligence Center, discussing AI, at 11:00 a.m. and by afternoon speaker TBA. Check-in and badge pickup for Registered Attendees begins at 10:30 a.m.
NO registrations or walk-ins at hotel.
Lunch is served from noon-1:00 p.m.
The second speaker TBA is scheduled for 1:00 p.m.
The event ends at 2:00 p.m.
Registration closes at 5:00 p.m. on Monday, 17 April.
Register here
Luncheon prices are $55 for Members; $70 for nonmember guests and all Subscribers.
Though we do not provide special overnight room rates, if you wish to make room reservations at the hotel, do so here.
Cancellation Schedule: AFIO must commit to the hotel facilities and therefore, regrets it must charge a cancellation fee. 100% refund until close of registration. No refunds or cancellations after close of registration. You will receive a donation receipt for fees forfeited. A donor statement will be sent showing that you made a "gift to AFIO" in such instances. Gifts to AFIO are tax-deductible.
All attendees must be members of AFIO or accompanied by a member of AFIO. If you would like to learn more about becoming a member, please visit www.afio.com. If you have any questions regarding membership, please contact our office at 703-790-0320 or email us at afio@afio.com.
Questions regarding event to events@afio.com
See the AFIO Calendar of Events for scheduling further in the future.
Events from Advertisers, Corporate Sponsors, Others
She was the first female accredited correspondent during World War II. After secret meetings with its author, she smuggled The New Class, an anti-Communist manifesto out of Yugoslavia, where it went on to sell more than three million copies and be translated into more than 60 languages. Isn't it time you knew her story? Katharine Clark was the first female military accredited correspondent during World War II. Staying on as a foreign correspondent behind the Iron Curtain after the War, she risked her life to expose the truth about the realities of Communism to the world. Join author Katharine Gregorio to discover a trailblazer and an intense and too little-known Cold War story. Gregorio dug into the real life of her great aunt to write The Double Life of Katharine Clark: The Untold Story of the Fearless Journalist Who Risked Her Life for Truth and Justice. Support for this program has been provided by a generous grant from the Pritzker Military Foundation, on behalf of the Pritzker Military Museum & Library. Explore or Register here: www.spymuseum.org.
13 Mar 23, 1700 - 1800 (ET) – Publishing with Intelligence - Institute of World Politics – Virtual
This information-filled seminar will discuss getting your article or manuscript to be published by an academic journal or obtaining a contract for a book. The forum will provide a book proposal template used by some major book publishers and how proposed articles make it through a double-blind review process for an academic publication. A question and answer period will dominate the forum, and attendees are encouraged to bring any proposed manuscripts they seek to publish. About the Speaker: Dr. Jan Goldman is Professor of Intelligence and Security Studies at The Citadel. His research areas focus on ethics and intelligence operations, secrecy, intelligence analysis, psychological operations, intelligence in civil society, and intelligence education. He has over 25 years experience working in the U.S. intelligence community. He taught for many years at the National Intelligence University (formally known as the National Defense Intelligence College) and the FBI Academy at Quantico, Virginia. He is the organizer for several international academic and professional intelligence conferences held at Johns Hopkins University, Georgetown University, and Oxford University. He is currently the editor-in-chief of the highly respected International Journal of Intelligence and Counterintelligence; the founding editor for professional textbooks – Security Professionals Intelligence Education Series (S.P.I.E.S. at Rowman and Littlefield Publishers); a member of several academic, research and publishing advisory boards; co-founder of the non-profit International Intelligence Ethics Association; and the founding editor of the International Journal of Intelligence Ethics. He is the author or editor of numerous publications to include, as a co-author, Intelligence and Information Policy for National Security: Key Terms and Concepts (Rowman and Littlefield, 2017). His two-volume The Central Intelligence Agency: An Encyclopedia of Covert Operations, Intelligence Gathering, and Spies (ABC-CLIO, 2016) honored as Editors’ Top Community College Resources award and the Best Reference Title award of 2016; and War on Terror Encyclopedia: From the Rise of Al Qaeda to 9/11 and Beyond (ABC-CLIO, 2015). Dr. Goldman is an internationally recognized expert on ethics and intelligence, and the only intelligence analyst to be awarded “current and warning intelligence expert” at the Defense Intelligence Agency. Free registration here.
Join intelligence community colleagues online for a Coffee and Conversation with Doug Wade, Chief, China Mission Group, Defense Intelligence Agency (DIA). In this 45-minute discussion with Larry Hanauer, INSA Vice President for Policy, Mr. Wade will discuss China's military capabilities, technology innovation, space and cyber strategies, and political/economic influence on countries around the world. He will also discuss the value of open source intelligence in understanding China, prospects for conflict in the Taiwan Straits and elsewhere in the Pacific, and lessons from the Russia-Ukraine war that could be applied to a conflict with China. Free registration here.
Birds do it, bees do it -- even educated slugs do it! But you can't do it…that is smell certain chemicals, feel an earthquake before it hits, or sense changes in the atmosphere. That's why spy agencies have invented super sensors to collect invisible intelligence -- chemical traces, nuclear particles, vibrations, and wave-lengths – that can be used to identify and track targets. Join us for an introduction to the too little-known field of Measurement and Signature Intelligence (MASINT) from Peter Humphrey. Humphrey is an all-source analyst: a researcher and writer with some 50 publications in the fields of intelligence, international affairs, and geophysics. Explore or Register here: www.spymuseum.org.
From the spymaster and inspiration for the movie Argo, discover the "real-life spy thriller" of the brilliant but under-supported CIA operatives who developed breakthrough spy tactics that helped turn the tide of the Cold War. Antonio Mendez and his future wife Jonna were CIA operatives working to spy on Moscow in the late 1970s, at one of the most dangerous moments in the Cold War. Soviets kept files on all foreigners, studied their patterns, and tapped their phones. Intelligence work was effectively impossible. The Soviet threat loomed larger than ever. The Moscow Rules tells the story of the intelligence breakthroughs that turned the odds in America's favor. Jonna Mendez is a former Chief of Disguise with over twenty-five years of experience as a CIA officer working in Moscow and other sensitive areas. Explore or Register here: www.spymuseum.org.
19 - 28 Mar 23 - Washington DC to Europe and back - Gary Powers' 10-Day Cold War Espionage Tour
Join author and historian Gary Powers Jr. on this unforgettable 10-day tour of Cold War and Espionage related sites throughout Germany and the Czech Republic
Day 1: Departure from the USA; Day 2: Arrival Berlin; Day 3: Berlin - Potsdam - Berlin; Day 4: Berlin; Day 5: Berlin – Leipzig – Dresden; Day 6: Dresden – Prague – Pilsen; Day 7: Pilsen – Míšov – Pilsen; Day 8: Pilsen – Rozvadov – Nuremberg – Stuttgart; Day 9: Stuttgart – Sinsheim – Speyer – Frankfurt; Day 10: Departure for the USA.
Included Visits: Berlin Wall Memorial • Checkpoint Charlie Museum • German Spy Museum • Military History Museum Gatow • Glienicke Bridge • Hohenschönhausen Memorial • Berlin Stasi Museum • Allied Museum on Clay Allee • Museum in Der Runde Ecke • Leipzig Forum of Contemporary History Museum • Dresden's Military History Museum • Bautzner Strasse Dresden Memorial • KGB Museum • Prague Museum of Communism • Vitkov Hill Nuclear Bunker • Pilsner Urquell Brewery • Atom Museum • Iron Curtain Museum • Nuremberg Trials Memorial • Stuttgart Cold War Bunker • Sinsheim Technik Museum • Speyer Museum of Technology.
Tour Name: Gary Powers' Cold War Espionage Tour - view tour; Group Name: Garypowers.Com Tours; Departure City: Washington, DC; Tour Departure Date: March 19, 2023; Tour Return Date: 28 Mar 23.
Tour Price: $3,950.00 (deduct $950 for land only tour) per person, assumes 2-person registration.
For full description of the activities and accommodations on each of those dates and locations, explore full information about the tour here or Call 1.800.323.4466.
To enroll now for this 2023 once in a lifetime tour, do so here.
ALSO See: "Enemy Territory: The Story of American CIA U-2 Pilot Francis Gary Powers" - A Graphic Novel by Francis Gary Powers Jr. and Walter Pfenninger.
Join International Spy Museum Historian and Curator Dr. Andrew Hammond in conversation with historian Benny Morris, author of Sidney Reilly: Master Spy, about one of the most colorful and best-known spies of the twentieth century. Emerging from humble beginnings in southern Russia, Reilly was an inventive, multilingual businessman and conman who became a virtuoso of espionage. He spent World War I in the United States, brokering major arms deals for tsarist Russia, and then joined the ranks of MI6, Britain's foreign intelligence service. He tried to overthrow the Bolshevik regime in Moscow before eventually being lured back to Russia and executed. The Spy Museum is proud to exhibit the only object in existence that illustrates the connection between Reilly and R.H. Bruce Lockhart, co-conspirator of the plot. Join the historians as they sift through the reality and the myth of Reilly's life to paint a fascinating portrait of one of the most intriguing figures from the golden age of spies. Program is free of charge but requires advanced registration. Explore or Register here: www.spymuseum.org.
Prof. John J. Quattrocki, Former Vice President, CACI's National Intelligence Solutions Group; Former Senior Executive on the National Security Staff, will be discussing "The Fourth Man" controversy raised by retired CIA Case Officer, Bob Baer, who published a book of the same title which has reignited an Intelligence Community bar fight as the IC approaches its 40-year anniversary. Join the discussion at IWP, as they discuss the case that has been at the core of IWP's curriculum on the Statecraft of Counterintelligence for more than 18 years. Location: The Institute of World Politics, 1521 16th St. NW, Washington D.C. 20036, in the Marlatt Mansion, Commodore Barry Room. Register here. No cost to attend but registration required.
Alma Katsu is the award-winning author of seven novels; Red London, her latest is a follow-up to the successful Red Widow where she unveiled Lyndsey Duncan, a CIA intelligence officer nicknamed "the human lie detector." Katsu knows what she is writing about. She had a thirty-five-year career as a senior intelligence analyst for several US agencies, including the CIA and NSA, where she advised policymakers and military commanders on issues of national security. Her newest book is a nuanced, race-against-the-clock story that invokes today's headlines. International Spy Museum Director of Adult Education Amanda Ohlke and Katsu will discuss how Lyndsey reflects the reality of women working in intelligence and how the thriller's plot reflects both current affairs and famous notes from the past—like well-placed moles at the CIA. Explore or Register here: www.spymuseum.org.
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. To register, please email Shana Oltmans at soltmans@spymuseum.org. Free but space is limited. Register below. Explore or Register here: www.spymuseum.org.
Wednesday, 29 Mar 23, 0900-1700 (ET) – Boston, MA – How Wars End: A Conference Presented by the Pardee Center for the Study of the Longer-Range Future – Boston University - In Person
The event will feature five expert panels:How wars end from a historical perspective (Moderator: Prof. Erik Goldstein), How intelligence supports diplomats in ending wars (Moderator: Prof. Joseph Wippl), How the Afghanistan War ended (Moderator: Prof. John Woodward), How the Iraq War ended (Moderator: Prof. Shamiran Mako), How current crises will end (Moderator: Ambassador Mark Storella). The full list of panelists will be announced in the coming weeks. This conference is convened by Prof. John Woodward, Prof. Cathal J. Nolan, and Prof. Erik Goldstein in their capacity as Pardee Center Faculty Research Fellows. This event is free and open to the public. Register here.
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. To register, please email Shana Oltmans at soltmans@spymuseum.org. Free but space is limited. Register below. Explore or Register here: www.spymuseum.org
"The Nation's Premier Intel and National Security Event" - Save the date for the 10th Annual AFCEA/INSA Intelligence and National Security Summit! The powerful, two-day program, at the Gaylord National Resort, will feature five blockbuster plenaries, six engaging breakout sessions, and a jam-packed exhibit hall full of the latest IC technology innovations. Top leaders will discuss State of the Community, Military Intelligence Priorities, Strategic Intelligence, and Cybersecurity Challenges. Breakout sessions with senior leaders, technology experts, and thought leaders will examine some of the most pressing issues facing the community. Plus, powerful networking opportunities designed to foster partnerships and relationship building. Stay tuned! Registration to open in early March. Check for updates here.
Gifts for Friends, Colleagues, Self
 Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Show your support for AFIO with our new Black Short-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $50 each including shipping.
Sizes for (M) men, only; Small, Medium, Large, XL, XXL, and XXXL. $50 per shirt.
You may pay by check or credit card. Complete your order online here or mail an order along with payment to: AFIO, 7600 Leesburg Pike, Ste 470 East, Falls Church, VA 22043-2004. Phone orders at 703-790-0320. Questions? Contact Annette at: annettej@afio.com.

PopSocket for cellphones or tablets
Show your support to AFIO while enjoying the convenience offered by our AFIO Logo PopSocket. The PopSocket is most commonly used as a stand and as a grip for your mobile phone or tablet; handy for taking selfies, watching videos, and for texting. The PopSocket looks like a small button or sticker which, when closed, sticks flat to your mobile device. However, its accordion-like design enables it to pop open for use. The benefits of using a PopSocket make it a must-have accessory for your mobile phone or tablet. It also aids in keeping your phone from slipping off your hand during use, falling, or breaking.
Price: $15. Order this and other store items online here.

Caps - Dark Navy with Navy AFIO Logo
An authentic silhouette with the comfort of an unstructured, adjustable fit. Fabric: 100% cotton. Unstructured. Fabric strap closure with adjustable D-clip. Price: $30. Order this and other store items online here.

Duffel Bags - Royal Blue and Black with Full Color AFIO Logo This duffel has it all when it comes to value, style and organization.
600 denier polyester canvas with polyester double contrast; D-shaped zippered entry for easy access. Front pocket with hook and loop closure. End mesh pocket Easy-access end pockets. Four durable, protective feet and built-in bottom board for added strength. Web handles with padded grip. Detachable, adjustable shoulder strap.
Dimensions: 11"h x 19.75"w x 9.75"d; Approx. 2,118 cubic inches
Price: $50. Order this and other store items online here.
AFIO Mug with color glazed seal.
Made in the U.S.A., dishwasher-safe.
$35 includes shipping.
Sip your morning joe in style or use it to stash pens, cards, paperclips, or candy.
Order this and other store items online here.
JUST PUBLISHED
FOR 2023
| Be informed on career opportunities in the U.S. Intelligence Community | ||
 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. AFIO's popular 47-page booklet reaches thousands of high school, college students, university guidance offices, and distributed in classes teaching intelligence, to help those considering careers in the U.S. Intelligence Community. |
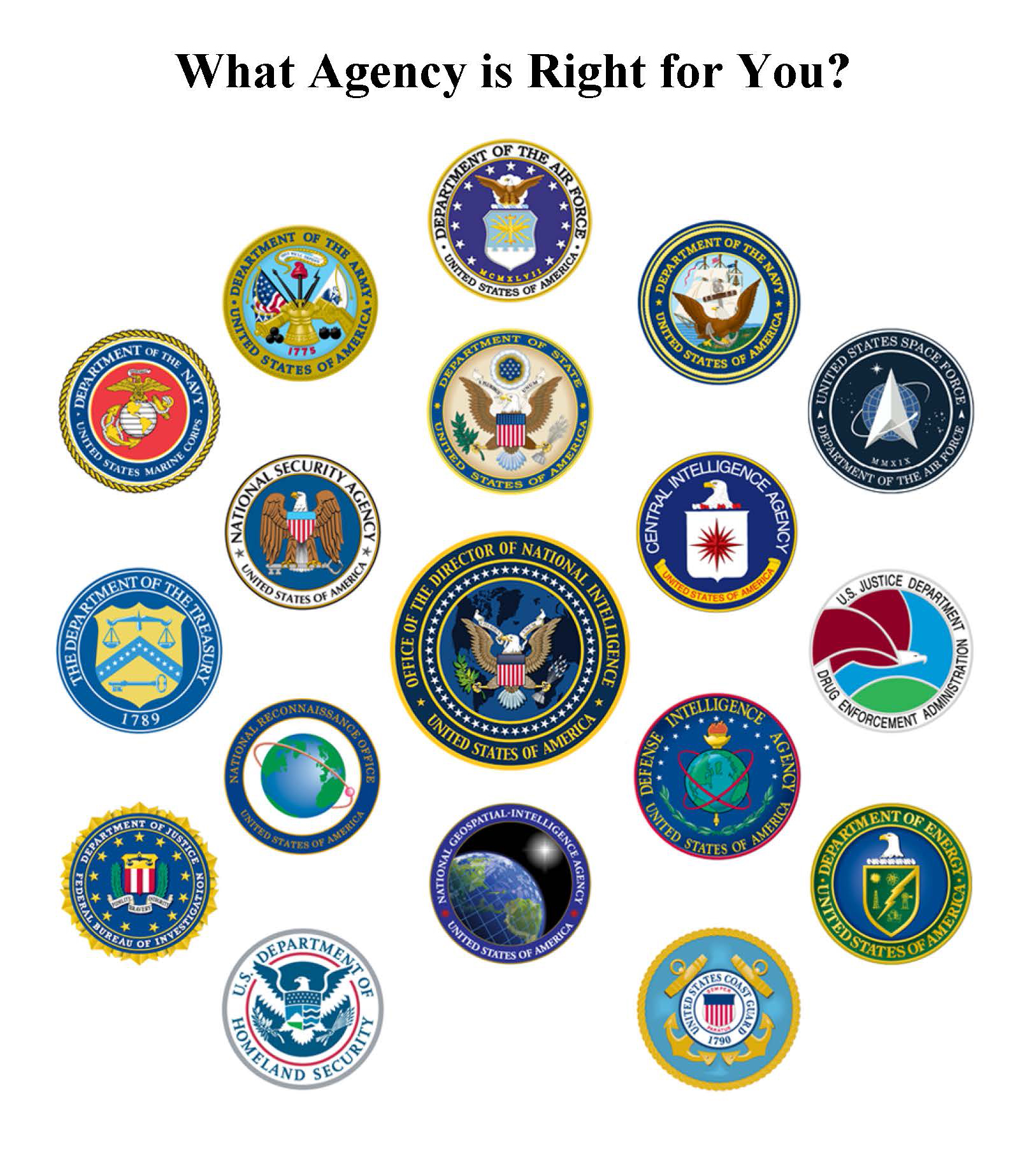 |
| This is the all new fifth edition. The publication is also popular with University Career Guidance Centers, professors and academic departments specializing in national security, and parents assisting children or grandchildren in choosing meaningful, public service careers. This booklet is provided online as a public service from the generosity of AFIO board, volunteer editors/writers, donors, and members. We thank all for their support which makes this educational effort possible. |
||
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |
||
 Guide to the Study of Intelligence...and...When Intelligence Made a Difference
Guide to the Study of Intelligence...and...When Intelligence Made a Difference
"AFIO's Guide to the Study of Intelligence" has sold out in hard-copy.
It is available in digital form in its entirety on the
AFIO website here.
Also available on the website here are the individual articles of AFIO's
history project "When Intelligence Made a Difference" that have been
published to date in The Intelligencer journal.
More articles will be appear in future editions.
Some features of the email version of the WIN do not work for readers who have chosen the Plaintext Edition, some users of AOL, and readers who access their email using web mail. You may request to change from Plaintext to HTML format here afio@afio.com. For the best reading experience, the latest web edition can be found here: https://www.afio.com/pages/currentwin.htm
To unsubscribe from the WIN email list, please click the "UNSUBSCRIBE" link at the bottom of the email. If you did not subscribe to the WIN and are not a member, you received this product from a third party in violation of AFIO policy. Please forward to afio@afio.com the entire message that you received and we will remove the sender from our membership and distribution lists.
(c) 1998 thru 2022
AFIO Members Support the AFIO Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for back issues of the WINs, information about AFIO, conference agenda and registrations materials, and membership applications and much more! .
AFIO | 7600 Leesburg Pike, Suite 470 East, Falls Church, VA 22043-2004 | (703) 790-0320 (phone) | (703) 991-1278 (fax) | afio@afio.com