AFIO
Weekly Intelligence Notes #11-10 dated
23 March 2010
REMOVAL
INSTRUCTIONS: We
do not wish to add clutter to inboxes. To discontinue receiving
the WINs, click here: |
CONTENTS
Section I -
INTELLIGENCE HIGHLIGHTS
Section
II - CONTEXT & PRECEDENCE
Section
III - COMMENTARY
Section
IV -
BOOKS, RESEARCH REQUESTS AND COMING
EVENTS
Books
Research Requests
Coming Events
Current
Calendar New and/or Next Two Months ONLY
- Thursday,
25 March 2010, 6 p.m. - New York, NY - AFIO Metro NY
Chapter hosts
U.S. Secret Agent who specialized in Explosives and Codes
- Wednesday, 31 March 2010, 8 p.m. - Coral
Gables, FL - AFIO Miami Chapter hosts Keith
Thomson in special reading
"Once a Spy" and presentation on Microdrones -- or did you
think it was
just an insect on your ceiling?.
- 1 April 2010 - Tysons Corner, VA - AFIO National
Luncheon featuring Seymour Hersh and Marc
Thiessen. Details here.
- Wednesday, 7 April 2010, 6 p.m. - Las Vegas, NV - AFIO Las Vegas Chapter Meeting features Matthew Zucker, Las Vegas Metropolitan Police Department. Topic: “Mexican Drug Cartels.”
- Tuesday, 13 April 2010, 5 p.m. - Hampton Roads,
VA - The AFIO Norm Forde Hampton Roads Chapter - to hear
Carl Finstrom
on Stella Polaris
- Tuesday, 13 April 2010, 1130 hrs - Tampa, FL - The AFIO Suncoast Chapter will hold its Spring meeting and luncheon on "Current Challenges to America's Historical Strengths in the Intelligence Community" featuring Walter Andrusyszyn.
- Wednesday,
14 April 2010, 11:30 a.m. - Scottsdale, AZ - AFIO Arizona Luncheon on
"Current Perspective on Pakistan-Afghanistan-India Issues"
- 15 April 2010, 12:30
p.m. - Las Angeles, CA - The AFIO L.A. luncheon hosts Marthe Cohn -
"Behind Enemy Lines: A French Spy Inside Nazi
Germany"
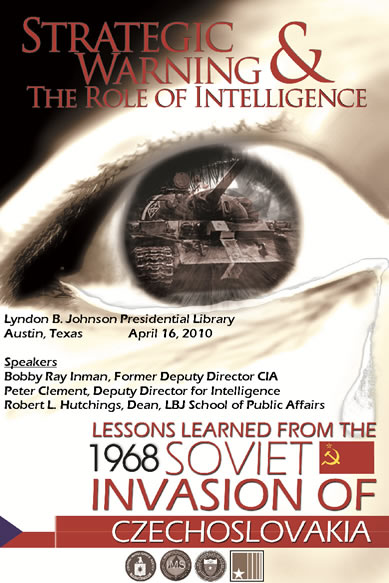
- Friday, 16 April 2010 - Austin, TX - CIA - LBJ
Library Conference on STRATEGIC WARNING and The ROLE OF INTELLIGENCE -
Lessons Learned from the 1968 Soviet Invasion of Czechoslovakia.
- 23 - 25
April 2010 - S. Portland, ME - The New England Chapter of the Naval
Cryptologic Veterans Association (NCVA-NE) holds a spring Mini-Reunion
at the Marriott at Sable Oaks
- 28 April 2010, 6:30 p.m. - Coral Gables, FL -
The AFIO Miami Chapter hosts dinner with Clandestine Service Officer.
- 28
April 2010, 6:00 p.m. - Washington, DC - The Goethe Institute will host
a presentation and discussion of the film "The Lives of Others" about
the surveillance society of East Germany during the Cold War.
- 30
April 2010, 9 a.m. - 6 p.m. - Washington, DC - "The Stasi and its
Foreign Intelligence Service" - Workshop by CWIHP and
GHI
- Saturday, 1 May 2010, 1000 - 1430 - Salem, MA - The AFIO New England Chapter hear Ed Barr on "The State of HUMINT in CENTROM Area of Operations."
- 20 May 2010, 11:30 am - Colorado Springs, CO - AFIO Rocky Mountain Chapter at the Air Force Academy, Falcon Club features Mark Pfoff of the El Paso Sheriff Office, "Computer Forensics and all things Digital."
Events at the International Spy Museum in
March, April and May with full details
- Monday, 5 April 2010; 6:30 pm - Washington, DC - "An
Evening with Nigel West: Secrets from the Cambridge Spies"
at the
International Spy Museum
- Wednesday, 14 April 2010; 6:30 pm - Washington, DC -
"Striking Remotely: Predator Drones" at the International
Spy Museum
- Thursday, 15 April 2010; noon - 1 pm - Washington, DC -
"Broker, Trader, Lawyer, Spy" at the International Spy
Museum
- Wednesday, 5 May 2010; 6:30 pm - Washington, DC -
"Abduction, Black Site Prisons, and the CIA: Extraordinary
Rendition
Today" at the International Spy Museum
- Thursday, 6 May 2010; 12 noon – 1 pm - Washington, DC -
"On the Front Lines of Cyber War with Richard A. Clarke"
at the
International Spy Museum
- Monday, 10 May 2010; 6:30 pm - Washington, DC - "Our Man
in Havana" at the International Spy Museum
- Thursday, 13 May 2010; 10 am - 2:30 pm - Washington, DC -
"Codebreaking in World War II: The Inside Story" at the
International
Spy Museum
- Thursday, 20 May 2010; 6 pm - Washington, DC -
"Goldfinger" at the International Spy Museum
OTHER EVENTS in 2010 requiring advanced reservations NOW.....
11-13 July 2010 - Dungarvan, Ireland - 2010 Analytic Best Practices Conference by Mercyhurst College Institute of Intelligence Education. Event to be at Dungarvan Town Hall Theatre. Further details.....
PLAN NOW
so you do not miss SPYCRUISE� on 13 - 20 November 2010 - Ft. Lauderdale,
FL - SPYCRUISE� to Grand Turks, Turks & Caicos;
San Juan, PR; St. Thomas, USVI; and Half Moon Cay, Bahamas - with
National Security Speakers Discussing "Current & Future Threats:
Policies, Problems and Prescriptions." Full Details....
|
AFIO
SPRING
LUNCHEON
THURSDAY,
1 April 2010
1 p.m. speaker: Seymour M.
Hersh, Controversial, Pulitzer prize-winning
investigative
journalist/author who writes on intelligence issues,
author of
Chain of Command: The Road from 9/11 to Abu
Ghraib
and
11 a.m. speaker: Marc A.
Thiessen,
Equally Controversial Washington Post reporter,
Writer/Commentator, Former Bush White House
& Pentagon Chief Speechwriter, author of the
acclaimed, newly
released
Courting Disaster: How the CIA Kept America Safe and
How Barack Obama Is Inviting the Next Attack
Crowne Plaza Hotel, Tysons Corner, VA
Check-in for badge pickup at 10:30 a.m.
Marc Thiessen address is at 11 a.m.
Lunch at Noon
Seymour Hersh address at 1 p.m.
Event closes at 2 p.m.
Register securely here.
Registration limited |
|

|
CIA
Invites AFIO Members to the CIA - LBJ Library Conference on
STRATEGIC WARNING and
The ROLE OF INTELLIGENCE
Lessons Learned from the 1968 Soviet Invasion of
Czechoslovakia
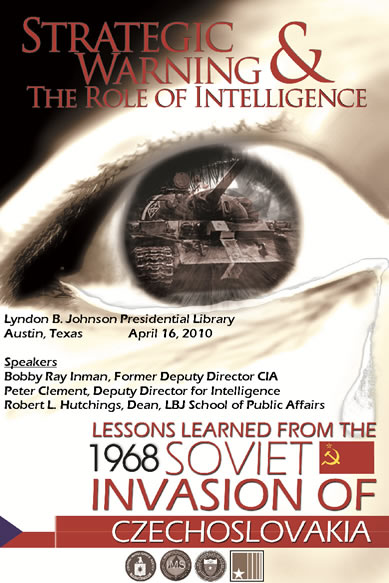
[Click on image above for full details
and registration from www.afio.com]
WIN CREDITS FOR THIS
ISSUE: The WIN editors thank the following special
contributors to
this issue: pjk, cjlc, th, and fwr.
They have contributed one or more
stories used in this issue.
For Additional Events two+ months or more....
view our online Calendar of Events |
Section
I - INTELLIGENCE
HIGHLIGHTS
New Network for British Intelligence Agencies. The Secret Intelligence Service (SIS) and GCHQ - the government's eavesdropping center - are working on a new network to collaborate with other agencies.
Following the failure of phase two of the SCOPE program, which would have delivered Top Secret intelligence to law enforcement, government departments and agencies, it was feared the intelligence agencies were not able to communicate well enough.
But according to the Intelligence and Security Committee's latest report, the SIS and GCHQ have started on an initiative to fix that. Called Collaboration in the Intelligence Community (CLiC), it is intended to be a "low-risk, inexpensive approach".
The report said CLiC will provide incremental changes to existing systems and will address the intelligence community's most urgent IT collaboration needs.
Former chief of SIS, Sir John Scarlett, told the committee: "CLiC is designed to shore up... some of the capability that SCOPE 2 would have given us... We are doing really quite well on this more modest CLiC programme, which is not being run out of the Cabinet Office, it is being run out of SIS and GCHQ... and it will be of community-wide value when it is delivered."
The first three areas CLiC will address are a link to HMRC so it can receive Top Secret intelligence and communicate securely via email; a secure
messaging system called STRAP3A, which the report predicted will let GCHQ, SIS, MI5, the Ministry of Defence, the Foreign Office (FCO), the Cabinet Office and the Home Office exchange Top Secret information by April; and an extension of a programme to share intelligence with the Serious Organised Crime Agency.
Details on expenditure and the contractor being worked with have been classified, although funding for CLiC came from GCHQ and SIS primarily, with the FCO and HMRC contributing too.
"CLiC appears to be progressing well so far. We are optimistic that it will deliver some of the IT solutions that the (far more costly) SCOPE Phase 2 programme was unable to. It is regrettable that this same practical and incremental approach was not adopted in the planning of the SCOPE programme," the ISC said.
The report also revealed that SCOPE technology is being slowly rolled out to overseas posts, with 40 posts already expected to be running the technology. Funding constraints have meant the FCO is unlikely to roll out any more for now, the report added.
Regarding the original failure of SCOPE 2, the committee said it is still investigating and said it would reveal its findings in its next report.
[PublicServiceUK/16March2010]
U.S. Army Worried About Wikileaks in Secret Report. A leaked U.S. Army intelligence report, classified as secret, says the Wikileaks Web site poses a significant "operational security and information security" threat to military operations.
Classified U.S. military information appearing on Wikileaks could "influence operations against the U.S. Army by a variety of domestic and foreign actors," says the report, prepared in 2008 by the Army Counterintelligence Center and apparently disclosed in its entirety on Monday.
The embarrassing twist: It was Wikileaks that published the 32-page document, but not before editor Julian Assange prepended a critique saying some details in the Army report were inaccurate and its recommendations flawed.
One section of the original document says "criminal prosecution" of anyone leaking sensitive information could "deter others considering similar actions from using the Wikileaks.org Web site." Another speculates that Wikileaks - which boasts that it is "uncensorable" - is "knowingly encouraging criminal activities," including violation of national security laws regarding sedition and espionage.
Lt. Col Lee Packnett, a spokesman for the U.S. Army on intelligence topics, said he was not familiar with the Wikileaks disclosure and would not immediately be able to comment. The National Ground Intelligence Center, which provides the Army with information about enemy weapons system and was mentioned in the report, did not immediately respond to a query from CNET.
Under the federal Espionage Act, it is a crime to disclose "information relating to the national defense which information the possessor has reason to believe could be used to the injury of the United States" (18 USC 793(e)). Another section says even indirect disclosures of national defense information to foreign citizens can be punished, in certain cases, by death (18 USC 794(a)).
Some First Amendment scholars have argued that those portions of the federal code cannot survive legal scrutiny - otherwise, as a few conservative commentators have claimed, The New York Times' disclosure of Bush-era warrantless wiretapping would have been a crime. In a since-abandoned prosecution of two former pro-Israel lobbyists charged with disclosing classified U.S. defense information, however, a federal judge had ruled that the balance struck by the Espionage Act "is constitutionally permissible."
Wikileaks has disclosed classified U.S. Defense Department information before. A 2004 report about Fallujah also marked secret was highlighted repeatedly as an example of damaging disclosure in the document released Monday.
The document no longer appears to exist on Wikileaks' Web site. A previous location now returns the error message: "The resource you are looking for has been removed, had its name changed, or is temporarily unavailable." (Wikileaks' Assange did not immediately reply when asked for an explanation.)
Wikileaks previously disclosed thousands of pages of pager logs from September 11, 2001, and won a case in federal court in San Francisco, after a Swiss bank attempted to pull the plug on the entire Web site. It shut down briefly last month because of lack of funds.
"While we will not comment on whether this is, in fact, an official document, we do consider the deliberate release of what Wikileaks believes to be a classified document is irresponsible and, if valid, could put U.S. military personnel at risk," Rear Adm. Gregory J. Smith, a spokesman for American military command in Baghdad, told The New York Times after Wikileaks posted a classified 2005 document about rules of engagement in that country.
[McCullagh/CNET/16March2010]
Family Starts Scholarship to Spur Government Careers. Heirs to a supermarket fortune will launch a multimillion-dollar scholarship foundation that is designed to encourage graduate students to pursue government careers in national security, foreign policy and international development.
The Robertson Foundation for Government plans to eventually provide full financial support to hundreds of graduate students in those fields who agree to at least three years of service with a federal agency within five years of graduation.
"We are very serious about the mission of getting these people to work for the government," said Bill Robertson, the foundation's director.
His mother, Marie Robertson, donated $35 million worth of stock in the A&P supermarket company in 1961 to Princeton University's Woodrow Wilson School of Public and International Affairs. But her heirs sued Princeton in 2002, arguing that the university diverted her original donation from its stated purpose of preparing college students for public service.
The suit was settled last year after a prolonged battle closely watched by universities, nonprofit groups and donors increasingly eager to keep close tabs on their contributions. Terms of the settlement require Princeton to pay approximately $60 million in payments and interest to the foundation by 2018.
The foundation plans to name four or five partner universities in coming weeks and then select its first eight fellows by the start of the 2010-11 academic year, Robertson said. Partner universities must agree to pay some student costs, and none of the schools will be members of the Ivy League, he said.
Although most scholarship recipients may consider careers with the State Department or the U.S. Foreign Service, Robertson hopes they will also consider jobs with the U.S. Agency for International Development, congressional committees, intelligence agencies and international development programs.
The foundation's board of directors includes former Virginia governor and senator Charles S. Robb, former national security adviser Brent Scowcroft and Paul Light, a government scholar who is now a professor at New York University. The group plans to establish a public service award program and work with federal agencies on retention efforts.
"We would like to attempt to make federal jobs more enticing to graduate students and also make these jobs more interesting," Robertson said. "One of the things students find after a few years is that they don't find [public service] as interesting or rewarding."
Few other endowments have provided such generous or specific support to students pursuing government careers, said Max Stier, president of the Partnership for Public Service.
"It's certainly not unique, but it's important, and there aren't enough of them," Stier said. His group was founded in 2001 by businessman Samuel J. Heyman, who established public service fellowship programs at Harvard and Yale universities.
Interested applicants can obtain more information at www.rffg.org. [WashingtonPost/15March2010]
Obama Fights against Congressional Oversight of Spy Agencies. President Barack Obama is threatening to veto legislation that funds intelligence agencies unless Congress backs off on several fronts to expand oversight of the intelligence community.
For starters, lawmakers want to give the Government Accountability Office, which investigates most but not all federal offices, the authority to probe intelligence agencies. Currently, only the inspectors general of each intelligence shop can investigate these operations.
Second, many people on Capitol Hill have talked about the need to reopen the FBI investigation of the anthrax attacks of 2001. Some lawmakers and scientists question the bureau's pursuit of government scientist Bruce Ivins, who killed himself upon learning of the FBI's plans to indict him for the attacks. The White House strongly objects to any attempt to revisit the Ivins matter.
Finally, Obama opposes a move by Congress to do away with the so-called Gang of Eight system, under which the White House notifies only the speaker and minority leader of the House, the majority and minority leaders of the Senate, and the chairmen and ranking minority members of the Senate and House intelligence committees on sensitive spy operations. Lawmakers instead want to give each intelligence committee the power to write their own rules for how the White House must inform lawmakers about secret work.
[Brinkerhoff/AllGov.com/17March2010]
UK Delays New Guidelines for Spies, Soldiers. New British guidelines on handling terrorism suspects held overseas have been delayed over a dispute about how to deal with potentially life-saving information from detainees who may be at risk of torture by allies.
Prime Minister Gordon Brown promised a year ago that new rules would be drawn up, and the government was expected to make them public for the first time this month. But officials have acknowledged the document won't appear before the country's national election, due within three months.
Brown ordered the rules to be rewritten following accusations that British officials were complicit in the torture of terror suspects held overseas by other nations, including the United States. Police are investigating two cases related to the actions of intelligence officers from the MI5 and MI6 spy agencies.
Two government officials, who demanded anonymity to discuss the issue, said Britain's government and Parliament's intelligence oversight committee disagree over a section of the new rules dealing with how ministers should handle material gleaned from suspects who may be at risk of mistreatment.
A report by the committee on detainee handling will be published alongside the new guidelines. Opposition lawmakers and human rights groups have accused the government of purposely delaying publication of controversial material until after the election, expected in May.
Conservative Party legislator William Hague said Brown is "suspected in some quarters of wishing to suppress difficult issues" and accused the government of "mounting incompetence" over national security issues.
In a new report on human rights, Britain's Foreign Office hinted at the likely tone of the new rules. It acknowledged the U.K. can't "afford the luxury of only dealing with those" who share Britain's standards or laws.
The report claimed "there are times when we cannot reduce the risk to zero" that detainees held by other nations are being mistreated.
"Why does it take more than a year to change a torture policy that should be perfectly simple - we never do it, we are not complicit in it, and when we learn that someone has been tortured we do as the law requires and report it," said Clive Stafford Smith, director of human rights group Reprieve.
Foreign Secretary David Miliband told the House of Commons that drafting the new rules had been more complex than first imagined. "The most important thing is to get this guidance right," he told lawmakers.
Lawmaker Kim Howells, chairman of the Intelligence and Security Committee, said it was now was "a matter for the prime minister" to decide when the rules are finalized and made public.
Howells on Thursday issued an annual report by his oversight committee, warning that Britain's intelligence agencies are preparing for cuts to their budgets for the first time since the Sept. 11, 2001, attacks on the United States.
MI5 director Jonathan Evans told the panel that his agency is readying for "a more austere financial climate." It has already scaled back plans to increase its staff numbers to 4,100, setting a new target of 3,800.
The committee said MI5 - which Evans said is dealing with "a couple of hundreds cases" of international terrorism - has issued a program called "Living Within Our Means," aimed at reducing its spending.
Britain is grappling with a net debt of 857.7 billion pounds ($1.3 billion), equal to 60.3 percent of gross domestic product. A key issue in the looming national election is over how fast, and how deep, cuts to public spending should be.
Domestic spy agency MI5, overseas intelligence service MI6 and the eavesdropping and intercept organization GCHQ have a combined annual budget of about 2.35 billion pounds, and receive several billion pounds more for spending on equipment upgrades and other additional costs.
MI6 chief John Sawers defended his agency's budget to the committee, saying MI6 work "saves a great deal of investment and resource here in Britain ... investigating terrorist plots and strengthening our border security."
Agency chiefs give testimony to the committee - whose members are selected by the prime minister - behind closed doors. However, some portions of their comments are quoted in the committee's reports.
[AP/16March2010]
'External' Spies Turn Focus on Home Front. Domestic New Zealand security threats will be more closely examined by a reformed government intelligence bureau.
The External Assessments Bureau announced on its website that it has been renamed the National Assessments Bureau. The Green Party says this is a "huge change", creating a "domestic spy agency" that should have been subject to Parliament's scrutiny.
The name change marks a change of emphasis for the bureau, with more work being done on intelligence within New Zealand. The staff and budget have not increased from the existing 30 people and $3.5 million.
The change follows a review of the Government's three security services by former foreign affairs secretary Simon Murdoch. Besides the new bureau, the Government also relies on the Security Intelligence Service (SIS) and the Government Communications Security Bureau for intelligence.
The National Assessments Bureau is a unit of the Department of the Prime Minister and Cabinet, and will now provide more advice on threats from within as well as from overseas.
Prime Minister John Key said the change reflected the need for intelligence agencies to make sure people were safe ahead of the Rugby World Cup next year.
Green Party foreign affairs spokesman Keith Locke said a lack of consultation over the change treated Parliament and the public with contempt. "It is a bit sad where the only growth area in the public service is in the spy agencies, who are quite unaccountable to the general public."
A beefed-up domestic security effort by the new bureau could create confusion and crossover with the work being done by police and the SIS, he said.
[Hartevelt/Stuff/17March2010]
Sale of Historic Espionage Gear Draws Ottawa's Attention. The Department of Canadian Heritage has opened a dossier on a private collection of aeronautical and espionage gear that an Oshawa, Ont., woman put up for sale last month for $1-million. Deirdre Stuart raised local ire last month - and fears that the collection would end up in the hands of a foreign collector - when she advertised her late father's assemblage, which includes gadgets from the Camp X spy school. For 30 years the artifacts have been available for public viewing at the family's private museum. Heritage officials contacted Ms. Stuart this week to tell her some military artifacts could be subject to export restrictions under the Cultural Property Export and Import Act. "It's personal property - people don't get that," Ms. Stuart said in an interview with the Post. She said potential buyers have shown "a lot of interest."
[Kelowna/20March2010]
West German Spy Agency Employed About 200 Former
Nazi Criminals. The German spy service has admitted that it employed about 200 former Nazi criminals for at least 15 years after the end of the Second World War.
Some had been involved in massacres in Poland and Russia, others were Gestapo torturers; all found a berth in the West German intelligence service. The cases have been brought to light because the Federal German Intelligence Service (BND) is compiling a history of its espionage activities since 1956 - and so polishing up its image, in the manner of MI6.
There was never any attempt to hide the fact that the BND employed Nazis - it was set up in a hurry, with US help, to create spying networks against the Soviet Union - but it has always been vague about its war records.
Now the Frankfurter Allgemeine Zeitung newspaper has been given access to files from the 1960s that detail how the BND tried, belatedly, to weed out suspected war criminals. Potted biographies of the agents, with lightly disguised names, have been published at www.faz.net/bnd.
"It has always been clear that the BND had a dark past," said Hansjoerg Geiger, who headed the BND between 1996 and 1998. "But I would never have reckoned with such a high proportion." He urged the BND to continue digging: "Only transparency about the past will clearly establish that the present-day BND has nothing in common with the service in its early years."
According to the newspaper the BND was thrown into confusion by the discovery of two Soviet moles, Heinz Felfe and Johannes Clemens, in 1961. Felfe had previously been a member of the SS while Clemens had been nicknamed "The Tiger of Como" for his savage treatment of Italian dissidents during the war.
The head of the BND, Reinhard Gehlen - himself a former intelligence officer in the Wehrmacht - decided that a criminal war record could make his agents a security risk, giving Moscow blackmail material. The old Nazis had served their purpose, providing agent networks and inside knowledge of the Soviet Union and Eastern Europe. Now they had to be screened.
Gehlen, one of the legendary Cold War spymasters, assigned a 32-year-old mole-hunter, Hans-Henning Crome, to the task. In 1963 Mr. Crome, now a pensioner living close to his former offices in Pullach, on the fringes of Munich, set up a team called Unit 85, which established itself in the attic of Gehlen's villa on the BND compound. Co-operating with Nazi-hunters in Ludwigsburg they started to work through the records of the agency's 2,450 employees.
Many had made only rudimentary attempts to cover their tracks. A certain Kurt W, formerly of the Gestapo in Koblenz, for example, had claimed to be a passport control officer in Sajmiste, near Belgrade. In fact, Sajmiste was the site of a concentration camp in which thousands of Jews were detained and murdered. Kurt W. - a promising officer in the BND - was thought to have been involved in the killings.
Georg W had been a young officer in the Gestapo, joined an Einsatzkommando - in essence a killing squad - that murdered the Polish intelligentsia after the German invasion. His unit killed 1,700 Poles, including women and children, in a single day in a wood outside Palmiry. By the end of the war, he was hunting down Jews and communists in hiding in Kassel. Then he joined the BND and rose through the ranks.
He had plenty of opportunities to bump into old comrades in the canteen - Helmut S, for example, whose SS unit was deemed responsible for the slaughter of 24,000 people, most of them Jews, in the Soviet Union.
Gehlen recorded his contacts and reports from the war and stored the microfilms in water-tight barrels in various sites in the Austrian Alps; he later traded them for his freedom. One of his nuggets of information was that several members of the American Office of Strategic Services - the precursor to the CIA - had been secret members of the US Communist Party.
But the BND was a spy service without a real tradition and even after the sacking of the Nazis and Gehlen's retirement in 1968, it was plagued by moles.
[TimesOnline/20March2010]
Release of Guant�namo Detainees Thoroughly Investigated, Senate Told. All U.S. intelligence agencies agreed unanimously on which war-on-terror captives now held at Guant�namo can be let go and which alleged terrorists must be held - with or without trial, President Barack Obama's national intelligence director and attorney general told the Senate on Thursday.
The letter itself gave no breakdown to Congress. But the Obama administration leaked in late January that "roughly 110'' of nearly 200 long-held foreign prisoners were cleared for transfer - either to further imprisonment in other countries or outright release.
Thursday's letter says that Central Intelligence Agency analysts were a part of the analysis process, as well as representatives of the FBI and Defense Intelligence Agency, or DIA. It was signed by Retired Adm. Dennis Blair, the director of National Intelligence and Attorney General Eric Holder.
In the end, it said, each decision was by agreement of six "senior-level officials'' authorized to attend a weekly case review meeting from the Homeland Security, Justice, State and Defense departments, as well as from Blair and the Joint Chiefs of Staff.
The six who voted unanimously in each case, the letter said, relied upon the work of more than 100 Guant�namo Review Task Force staff members who included FBI and CIA analysts as well as "senior military officers, military prosecutors and national security lawyers.''
The men addressed the letter to Senators Dianne Feinstein, Carl Levin, John McCain and Christopher Bond, senior members of the Intelligence and Armed Services Committee, and said it was in response to a question by Levin on whether the CIA and DIA "concurred in the decisions to approve the transfer of certain detainees to countries outside the United States.''
Congress has been increasingly interested in the processes by which Guant�namo detainees are released in light of periodic reports that some men who were sent to their homelands during the Bush administration have reemerged as active members of either al Qaeda or the Taliban.
The Obama administration has argued that its review processes are more thorough and systematic.
[Rosenberg/MiamiHerald/19March2010]
UK Has 5,700 "Secret Agents." It is the first time that the number of foreign intelligence gathering officers employed by MI6, also known as the Secret Intelligence Service, has been published.
The figure was disclosed in the annual report of the parliamentary Intelligence and Security Committee.
The ISC had previously disclosed the number of domestic security service officers who work for MI5, known as "spooks" - now around 3,500 - but had never done so for spies.
MI6 has launched a new recruitment drive aimed, in part, at former City bankers, with experience of foreign countries and language skills.
According to the ISC's report, there are now 2,252 MI6 officers and it aims to increase that to 2,527 this year.
The report also revealed there were 5,296 staff employed at the GCHQ monitoring station in Cheltenham, Gloucestershire, where they intercept telephone, email and internet communications. The report said the combined budget for MI5, MI6 and GCHQ was now �2.2bn.
According to the report, MI6 devotes 37 per cent of its effort to fighting international terrorism, with an increased focus on al-Qaeda in the Arabian Peninsular, based in Yemen, following its role in the failed Christmas Day bombing over Detroit.
Much of the rest of its focus is on Russia, Iran and an unnamed third country, redacted from the report - probably China.
MI5 currently has around 3,500 officers with an aim to increase that to 4,100 by next year.
They have recruited at junior levels in order to boost the number of frontline staff involved directly in counter-terrorism work, coordinating investigations, running agents and conducting surveillance operations against targets.
The Security Service now has an "Ethical Counselor" to provide staff with an avenue to raise ethical concerns about the service's work with someone who is outside their management line.
MI5 has attributed the success of its recruitment campaigns to a focus on raising awareness of the Security Service as an "employer of choice," with radio commercials and a media advertising campaign aimed at London commuters, along with on-line testing at the early stages of recruitment.
But it has also had to improve its screening mechanisms so that candidates with serious vetting concerns can be identified and rejected at an early stage.
MI5 are dealing with a "couple of hundred cases of one sort or another" relating to terrorism, Jonathan Evans, the director general of MI5, told the committee. He has previously said the service has around 2,000 individuals under surveillance.
Three quarters of the service's work is devoted to fighting terrorism, while the service now has to devote 18 per cent of its resources to Northern Ireland because of the increased threat from dissident groups, and 4 per cent to dealing with the threats from Russia and China.
GCHQ does not break down where it concentrates its effort but it is mainly ploughed into fighting terrorism over the internet and intercepting communications in Afghanistan, with other work on counter espionage and the threat of electronic attack by foreign powers, along with work on countering nuclear proliferation in the Middle East and North Africa.
A separate report released last week by the ISC, which oversees the work of the security and intelligence services, revealed MI6 had been struggling with recruitment recently.
The problems were exacerbated by plans to increase deployments overseas by around 40 per cent, strengthening existing "stations" and creating new ones.
Sir John Scarlett, then Chief of MI6, told the committee that the problems were caused by difficult conditions in overseas postings and by operational officers "at their peak" who had been sent out to foreign postings and needed more time off as a result.
He said it was also taking time to train new staff and allow them to accumulate sufficient experience. [Gardham/Telegraph/19March2010]
Sacked Australian Spy Chief Reopens His Case. Some 34 years after the event and at the age of 93, the last surviving founder of the Australian intelligence community, W.T. (Bill) Robertson, has reopened one of its great controversies - his sacking by Gough Whitlam when the then prime minister was in the middle of his own, terminal, dismissal crisis.
Mr. Robertson, dismissed in October 1975 as director of the Australian Secret Intelligence Service, has placed in the National Archives of Australia a statement disputing the reasons Mr. Whitlam gave for sacking him.
For a spy chief to lodge a personal statement in the archives in this fashion is unprecedented.
While not saying so explicitly, it strongly implies that Mr. Whitlam, now also 93, has lied about the circumstances of Mr. Robertson's dismissal.
Mr. Whitlam's office, asked for comment, said: "Mr. Whitlam declines to respond."
This dispute raises a significant contemporary issue - the continuing and absurd shroud of secrecy that surrounds ASIS and its history.
The documents relating to such events as Mr. Robertson's sacking, and ASIS activities as a proxy of the CIA are still heavily censored, well beyond the needs of national security and the 30-year rule that ring-fences other government documents.
Indeed, Mr. Robertson's statement in the archives has clearly been censored to the point where his note is sometimes almost incomprehensible.
His career and reputation were rather covertly restored by Malcolm Fraser and justice Robert Hope, the royal commissioner who investigated the intelligence community in the middle 1970s. But Mr. Robertson has been agitating for permission to publish his side of the story before he dies.
It was on October 21, 1975, that an enraged Mr. Whitlam sacked the spy chief.
Mr. Robertson recounts that, after a quiet start, the meeting was interrupted and Mr. Whitlam spoke to someone who had knocked at the door.
"Whatever had been said to him... had made Whitlam completely lose his temper. Red in the face, he shouted at me: "You are finished. That's the end of you and I will probably dispose of your service, too'."
Less than three weeks later, Mr. Whitlam was sacked by then governor-general John Kerr.
[TheAustralian/20March2020]
New Document Provides Framework for Interagency Data
Sharing. A recently released publication is designed to help facilitate information sharing across civilian and military organizations in the U.S. Government. Produced as a joint effort by the National Institute of Standards and Technology (NIST), the Defense Department and the U.S. intelligence community, the document creates a common information security framework for the federal government and the contractors who support it.
NIST Special Publication 800-37, Revision 1, Guide for Applying the Risk Management Framework to Federal Information Systems: A Security Life Cycle Approach (NIST SP 800-37), emphasizes building information security capabilities into information systems through state-of-the-practice management, operational and technical security controls. The publication structures the certification and accreditation process into a six-step risk management framework (RMF).
The revised RMF promotes near-real-time risk management and ongoing information system authorization by implementing continuous monitoring processes; using automated support tools as decision-making aids; integrating information security more closely into the enterprise architecture and systems development life cycle; equally emphasizing the selection, implementation, assessment and monitoring of security controls and the authorization of information systems; establishing responsibility and accountability for security controls deployed in organizations' information systems; and using a risk executive function to link risk management processes at the information system level to those at the organization level.
A major goal of NIST SP 800-37 is to permit the defense and intelligence communities to share information more easily. According to Roger L. Caslow, chief of the Risk and Information Assurance Program Division, Office of the Associate Director of National Intelligence and Chief Information Officer (ADNI/CIO, IC CIO), NIST SP 800-37 and the revised RMF support a balanced risk management approach for federal cybersecurity. The RMF allows security to be built into information systems' life cycles, supporting adaptability to varying environments across the community. He explains that the document provides an approach to manage risks for both traditional and complex systems, a procedure that was not formalized previously.
Other benefits include incorporating information assurance (IA) into intelligence community enterprise architecture to promote the delivery of IA services as enterprise services. Caslow indicates that the increased efficiencies from leveraging and reusing previous work allows more resources to be directed at risks as opposed to compliance issues. "The most obvious impacts will be seen in how this brings the national security community closer to legislative compliance requirements, assists our inspector general audits, and aligns with the rest of the federal government to support reciprocity," he says.
For Defense Department users, the new framework is very similar to the department's current certification and accreditation system, says Dominic A. Cussatt, a senior policy adviser in the Cyber Information Assurance Policy and Strategy Directorate, Office of the Deputy Assistant Secretary of Defense for Cyber Information and Identity Assurance. However, he adds that NIST SP 800-37 provides greater detail, operational scenarios, and addresses several external environments such as partnerships, outsourcing, and supply chain considerations that may prove useful to the department. "For the first time, there will be a common agreed-upon approach for information security risk management across the federal government that will provide a strong basis for reciprocal acceptance of security authorization decisions and facilitated information sharing. We will also share a common lexicon of risk management roles and responsibilities so that we are all speaking the same language and working from the same context," he says.
[Kenyon/Signal/20March2010]
Official Defends Alleged Off-The-Books Spy Program. A Defense Department official under investigation for allegedly running an off-the-books spy operation with private contractors in Afghanistan and Pakistan said the program was authorized by military commanders and saved lives.
Michael D. Furlong said that his now-suspended program prevented the assassination of two Afghani leaders, and that the private, unarmed teams he used to gather intelligence didn't go around "kicking in doors" and killing people.
Furlong's program was first brought to light this week by The New York Times, and Pentagon officials said the story raised serious allegations that warranted review. The Times reported that some of the intelligence was used to track down and attack militants.
Furlong denied those allegations.
"I take stuff in open source and throw it in the intelligence pipeline," Furlong told the Express-News. "I don't take this information and go directly to a kill."
Furlong is retired from the Army and is now stationed at Lackland Air Force Base, where he said he is a principal strategist for U.S. Strategic Command. He said he has been locked out of his office and no longer has access to documents or e-mails.
Pentagon spokesman Bryan Whitman said the department is still gathering facts and will take action if improprieties are found.
A U.S. official, who spoke on condition of anonymity to discuss the case, told The Associated Press this week that Furlong directed a defense contract to gather information about the region that could be shared with military units. After military officials suspected he was using Defense Department money for an off-the-books spy operation, defense officials shut down that part of the contract, the official said.
Furlong said military supervisors approved the program, and a legal opinion was sought that deemed the operation lawful.
Furlong said contractors collected information that was openly available, such as banter at markets or bazaars that might contain information about potential attacks on U.S. interests.
"This is not about anything but providing the best force protection we can provide all of those 20-somethings in foxholes," Furlong told the newspaper. "It's about saving lives."
Part of the original $22 million contract that Furlong was directing remains intact, the official told the AP, because it provides the funding for nine workers involved in information-gathering, translation and similar work. Those workers are employed by International Media Ventures with offices in Florida, Texas and elsewhere.
[AP/20March2010]
Section
II -
CONTEXT & PRECEDENCE
Russian Secrets for Sale, No Questions Asked. At Moscow's Savyolovsky Market, anyone can buy discs filled with information hacked or leaked from government databases. Reporters or hit men, it really doesn't matter.
They are selling secrets along the shining corridors of the Savyolovsky Market: Unlisted numbers. Tax returns. Customs declarations. Wanted lists. Police reports. Car registrations. Business permits.
Wrenched from the bowels of government by the forces of runaway capitalism and corruption, the hush-hush databases have made their way to this market in central Moscow where the windows of tiny shops glitter with cell phones, pirated DVDs and porn.
Compressed on discs, frozen in Cyrillic letters, is a trove of petty squabbles and personal tragedies that make up the fabric of this vast and often lawless land.
In a country where you have no right to know, but really you can know anything, anybody can anonymously buy discs burned with private information such as rape victimization, financial holdings and the suspicion of CIA involvement. Asking price (it's negotiable): $40 to $60.
Nobody asks whether the buyer is looking for a competitive edge, an address to plan a hit, research for a newspaper article. The sale of these databases is illegal, sure, but nobody seems to care. A few beat cops browse lazily among the stalls, studying cell phones.
"Krysha," a vendor with matted dreadlocks and bloodshot eyes says slyly, stretching a flat hand over his head. "Roof" - the word Russians use to denote protection.
The roof is the person who has enough connections, and enough muscle, to shelter underlings from the authorities. When Russians talk about operating in Moscow - opening a business, or even working as a journalist - they will, almost inevitably, say the same thing: What you need is a roof.
"It's cool, right?" the vendor prods, jabbing a cigarette at the wall displays advertising available databases. "It's cool."
A reporter settles on two discs: one purporting to contain all police reports in Russia throughout 2009, the other an amalgamation of cell phone numbers, addresses and professions. Both are packed with data technically off-limits to the public.
"They get leaked, or else somebody hacks into official databases," says another vendor, a swarthy young man who gives his name only as Alexander. "It's not legal."
The buyers might be concerned that a used car they're looking to buy was stolen, or maybe they're trying to track a license plate or find long-lost relatives or friends. Or, Alexander adds ominously, they are "people conducting their own investigations."
A browse through the database of phone directories turns up full names, addresses and telephone contacts for employees of the FSB, the secretive intelligence service that is a successor to the KGB.
Other bits of information come to light: A Russian colleague discovers that his name and his father's were found among the papers of a woman who was slain.
Anybody interested in calling on the 49-year-old longtime FSB agent whose job is described as "creation of favorable psychological climate in the collective... organization of video control and control of access" need only fish his address from the database. For the less formal, a telephone number and e-mail address are also provided.
If sympathies run in the other direction, you might phone the woman whose name was found in the notebook of a suspected CIA agent.
The police records offer a window on a compulsively secretive world. Crimes committed by police officers on a single September day included rape, hooliganism, embezzlement, bribe-taking and false testimony. "Suicide of an arrested person" also appeared in this category.
And on that same day in Novosibirsk, a traffic police captain hanged himself in his shed. "The motives are being established," the report says helpfully.
A few keystrokes dredge up the names, addresses and telephone numbers of crime victims. There's the 20-year-old woman who was dragged into a yard and raped from 1 a.m. to 5 a.m. on an August night by four unknown young men.
And, too, the director of a fruit company who was robbed of the $52,000 he was carrying in a briefcase.
A summary of street demonstrations carried out across Moscow on an April day included an account of 15 citizens who gathered on Arabat Street. They carried a dummy dressed in a blue tracksuit that was emblazoned with the name of the Chechen president, Ramzan Kadyrov.
The purpose of the demonstration, the anonymous police loggers dutifully typed up, was "to establish support for Ramzan Kadyrov." Did they really believe the demonstration was a gesture of solidarity for the feared leader? Were they snickering as they typed?
With straight faces, they logged the slogans, which appear to have been dripping with sarcasm: "Kadyry, decide everything!" (an allusion to Stalin's famous "Cadres decide everything.") "Academician Kadyrov will resurrect Russian science!" "Putin today, Kadyrov tomorrow!"
"No violations of public order resulted," the report concluded dryly.
Meanwhile, across the city, a lone veteran picketed the Defense Ministry. And near a monument to the Orthodox St. Kiril, eight young men passed out a neo-Nazi newspaper and chanted, "Russia is a Russian land."
Here, too, the faceless recorders kept their sense of humor. The neo-Nazis, they noted, were trying to "attract public attention to the social, political and ecological situation in the Russian Federation."
[Stack/LATimes/17March2010]
Stalking the CIA. Last week, Bill Gertz of the Washington Times broke news of a fight between the Central Intelligence Agency and the Department of Justice. The CIA wants Justice to investigate aggressively whether any laws were broken by attorneys working for the John Adams Project, a joint initiative of the ACLU and the National Association of Criminal Defense Lawyers. The lawyers reportedly provided photographs of CIA interrogators to defense attorneys, who then showed them to al Qaeda terrorists held at Guant�namo Bay.
Why would lawyers do that? Gertz says it was done "in an attempt to have the terrorism suspects identify the interrogators in order to call them as witnesses in future trials." The John Adams Project's lawyers wanted to use court proceedings intended to try mass-murdering terrorists for another purpose: to put the Bush administration and the CIA on trial.
Although CIA officials say the pictures compromised the agency's ongoing operations and could potentially lead to reprisals against the interrogators, Attorney General Eric Holder's department apparently does not think the photos are all that important. During discussions with the CIA, the department's lawyers have reportedly downplayed the seriousness of the offense. And the CIA is not happy about it.
"Given the events of the past year there is concern in the agency over whether or not someone has their back," a former senior intelligence official explained to us. "A failure to aggressively follow up these allegations will only worsen that concern."
Gertz attributes the Justice Department's reticence to particular lawyers within the department who are "sympathetic to the John Adams Project." One Justice Department lawyer who is clearly sympathetic is Jennifer Daskal, who previously worked for Human Rights Watch and was appointed by Holder to the Justice Department's Detainee Policy Task Force last year. Prior to joining the government, Daskal was an outspoken critic of the CIA and the interrogation techniques authorized by the Bush administration.
President Bush "will go down in history as the torture president," Daskal told the Associated Press in March 2008. "The Bush administration continues to insist that CIA and other nonmilitary interrogators are not bound by the military rules and has reportedly given CIA interrogators the green light to use a range of so-called 'enhanced' interrogation techniques, including prolonged sleep deprivation, painful stress positions, and exposure to extreme cold," Daskal added.
Daskal's anti-CIA activism was not limited to making hyperbolic statements to the press. Daskal and Human Rights Watch played a significant role in uncovering the CIA's secret detention facilities in Eastern Europe and Afghanistan, where top terrorists were detained and interrogated.
On November 2, 2005, Dana Priest of the Washington Post reported that the "CIA has been hiding and interrogating some of its most important al Qaeda captives at a Soviet-era compound in Eastern Europe." The Post, citing the government's security concerns, did not name the countries where the facilities were located. But just a few days later, on November 6, 2005, Human Rights Watch revealed the countries in a posting on its website. The organization said it had "collected information that CIA airplanes traveling from Afghanistan in 2003 and 2004 made direct flights to remote airfields in Poland and Romania." The organization encouraged European officials to investigate further, and the Europeans did just that.
In May 2006, the European parliament sent a delegation to Washington to discuss the CIA's secret detention and interrogation program with various interested parties. The delegation met with Human Rights Watch on May 10. Here is how a document produced by the European parliament describes the meeting:
"The delegation met with John SIFTON (Counterterrorism Researcher) and Jennifer DASKAL (US Advocacy Director) who provided the delegation with circumstantial evidence linking Poland and Romania to secret CIA prisons, including flight records, statements by Polish and Romanian government officials, as well as precise details of specific planes used by the CIA. Both recognized that they do not have formal evidence of these allegations, but stressed the indications of these facts were actually very strong. Their information was that there had been detainees in CIA custody well before the Guant�namo Bay detention center had been established."
Although the Europeans listed Daskal's colleague, John Sifton, as a "counterterrorism researcher," he was really researching the CIA - not the terrorists. In The Guant�namo Lawyers, a collection of short, sentimental memoirs written by dozens of lawyers, who sanitized their clients' histories and glorified their work on behalf of war on terror detainees, Sifton offered an intriguing account of how Human Rights Watch assisted in uncovering details of the CIA's operations.
"Throughout the years after 2001, journalists, human rights investigators, and lawyers managed to obtain a surprising amount of information about U.S. detention and interrogation operations," Sifton wrote. He elaborated:
"Amnesty International, Human Rights Watch, and the [New York] Times found and interviewed former CIA detainees. FOIA litigation by the Associated Press, the ACLU, and the Center for Constitutional Rights produced information about former CIA detainees at Guant�namo - lower-level prisoners who had been kept short-term in CIA detention. Every piece of the story seemed to come from a different source...
"Lawyers and human rights groups worked together, sharing "intelligence" to uncover what intelligence agencies were doing with detainees. When I was working at Human Rights Watch, I managed to piece together a good deal of information about the CIA's detention facilities in Afghanistan by collecting accounts from former CIA detainees at Guant�namo, mostly from notes provided by habeas attorneys. I called and met with numerous Guant�namo attorneys to inquire whether their clients had been in CIA custody. In several instances, attorneys I reached were not aware that their clients had been in CIA custody until I explained that their clients' own accounts matched those of other CIA detainees. In one notable example, I spoke with one of the editors of this book, Mark Denbeaux, after I came to suspect his client had been in a secret site in Afghanistan - the detainee had described one of his earlier places of detention in ways that closely matched other detainees' descriptions of a CIA site in Afghanistan. The next time Mark went to Guant�namo, he confirmed this previously secret fact with the detainee."
Human Rights Watch published Sifton's investigation of the CIA's detention facilities in Afghanistan in a February 2007 report entitled "Ghost Prisoner." The report draws on graphic descriptions offered by former detainees. That same report was "reviewed and edited" by Jennifer Daskal.
What's particularly striking about Sifton's description is the role played by the Gitmo habeas attorneys. These lawyers were supposed to be helping their clients file habeas petitions with federal courts. Instead, they went far beyond that legal representation, working to expose the CIA's activities during a time of war. This involved violations of a 2004 protective order that prohibits detainee attorneys from discussing military operations, arrests, intelligence, or current events with their clients. Nor were they allowed to discuss information about other detainees who are not their own clients.
The cabal described by Sifton worked to uncover not only the location of the CIA's secret sites, but also the identities of the CIA personnel charged with transporting (via special flights), detaining, and interrogating terrorists. In The Guant�namo Lawyers, Sifton explained how CIA personnel were identified:
"CIA aviation operations were handled by corporate front companies, some of which were hidden by oddly thin veneers. Pilots' aliases could be cracked by searching FAA records for real persons with characteristics matching those of the aliases. CIA officers passing through Europe also broke their aliases, for instance, by calling their homes from hotels. Police records from Italy and France, revealing these calls, could later be used to confirm officers' identities."
It also proved possible for investigators to confirm that personnel were CIA: Public-records searches for CIA officers would typically reveal a set of overseas State Department or U.S. military base postings and post office-box addresses in Northern Virginia.
Some of the Gitmo lawyers have no problem with exposing the CIA's secret detention facilities or stalking CIA operatives and then showing their pictures to top al Qaeda terrorists. It is all part of the investigation and potential prosecution of the CIA, which Jennifer Daskal has long advocated.
"It would be contrary to the principles of the criminal justice system for the attorney general to say he believes a very serious crime has been committed and then to do nothing about it," Daskal told the New York Times in January 2009. She was referring to comments made by Holder during his confirmation hearings, in which he compared CIA interrogation techniques to atrocities committed by the Japanese in World War II and by the Khmer Rouge. "Waterboarding is torture," Holder flatly stated. "We prosecuted our own soldiers for using it in Vietnam." The clear implication was that the CIA's interrogators could be prosecuted as well.
While Holder has been willing to denigrate CIA interrogators, he is apparently not eager to investigate the people who stalked and photographed CIA interrogators and then exposed them and their families to admitted al Qaeda killers. Instead, Holder has hired lawyers like Daskal, who opposed the CIA's role in countering the terrorist threat and worked to expose the agency's detention and interrogation operations.
[Burlingame/Joscelyn/WeeklyStandard/22March2010]
U-2 Spy Plane Evades the Day of Retirement. The U-2 spy plane, the high-flying aircraft that was often at the heart of cold war suspense, is enjoying an encore.
Four years ago, the Pentagon was ready to start retiring the plane, which took its first test flight in 1955. But Congress blocked that, saying the plane was still useful.
And so it is. Because of updates in the use of its powerful sensors, it has become the most sought-after spy craft in a very different war in Afghanistan.
As it shifts from hunting for nuclear missiles to detecting roadside bombs, it is outshining even the unmanned drones in gathering a rich array of intelligence used to fight the Taliban.
All this is a remarkable change from the U-2's early days as a player in United States-Soviet espionage. Built to find Soviet missiles, it became famous when Francis Gary Powers was shot down in one while streaking across the Soviet Union in 1960, and again when another U-2 took the photographs that set off the Cuban missile crisis in 1962. Newer versions of the plane have gathered intelligence in every war since then and still monitor countries like North Korea.
Now the U-2 and its pilots, once isolated in their spacesuits at 70,000 feet, are in direct radio contact with the troops in Afghanistan. And instead of following a rote path, they are now shifted frequently in midflight to scout roads for convoys and aid soldiers in firefights.
In some ways, the U-2, which flew its first mission in 1956, is like an updated version of an Etch A Sketch in an era of high-tech computer games.
"It's like after all the years it's flown, the U-2 is in its prime again," said Lt. Col. Jason M. Brown, who commands an intelligence squadron that plans the missions and analyzes much of the data. "It can do things that nothing else can do."
One of those things, improbably enough, is that even from 13 miles up its sensors can detect small disturbances in the dirt, providing a new way to find makeshift mines that kill many soldiers.
In the weeks leading up to the recent offensive in Marja, military officials said, several of the 32 remaining U-2s found nearly 150 possible mines in roads and helicopter landing areas, enabling the Marines to blow them up before approaching the town.
Marine officers say they relied on photographs from the U-2's old film cameras, which take panoramic images at such a high resolution they can see insurgent footpaths, while the U-2's newer digital cameras beamed back frequent updates on 25 spots where the Marines thought they could be vulnerable.
In addition, the U-2's altitude, once a defense against antiaircraft missiles, enables it to scoop up signals from insurgent phone conversations that mountains would otherwise block.
As a result, Colonel Brown said, the U-2 is often able to collect information that suggests where to send the Predator and Reaper drones, which take video and also fire missiles. He said the most reliable intelligence comes when the U-2s and the drones are all concentrated over the same area, as is increasingly the case.
The U-2, a black jet with long, narrow wings to help it slip through the thin air, cuts an impressive figure as it rises rapidly into the sky. It flies at twice the height of a commercial jet, affording pilots views of such things as the earth's curvature.
But the plane, nicknamed the Dragon Lady, is difficult to fly, and missions are grueling and dangerous. The U-2s used in Afghanistan and Iraq commute each day from a base near the Persian Gulf, and the trip can last nine to 12 hours. Pilots eat meals squeezed through tubes and wear spacesuits because their blood would literally boil if they had to eject unprotected at such a high altitude.
As the number of flights increases, some of the plane's 60 pilots have suffered from the same disorienting illness, known as the bends, that afflicts deep-sea divers who ascend too quickly.
Relaxing recently in their clubhouse at Beale Air Force Base near Sacramento, Calif., the U-2's home base, several pilots said the most common problems are sharp joint pain or a temporary fogginess.
But in 2006, a U-2 pilot almost crashed after drifting in and out of consciousness during a flight over Afghanistan. The pilot, Kevin Henry, now a retired Air Force lieutenant colonel, said in an interview that he felt as if he were drunk, and he suffered some brain damage. At one point, he said, he came within five feet of smashing into the ground before miraculously finding a runway. As a safety measure, U-2 pilots start breathing pure oxygen an hour before takeoff to reduce the nitrogen in their bodies and cut the risk of decompression sickness. Mr. Henry, who now instructs pilots on safety, thinks problems with his helmet seal kept him from breathing enough pure oxygen before his flight.
Lt. Col. Kelly N. West, the chief of aerospace medicine at Beale, said one other pilot had also been disqualified from flying the U-2. Since 2002, six pilots have transferred out on their own after suffering decompression illnesses.
Still, most of the pilots remain undeterred, and the Air Force is taking more precautions. Holding an oxygen mask to his nose, one pilot, Maj. Eric M. Shontz, hopped on an elliptical machine for 10 minutes before a practice flight at Beale to help dispel the nitrogen faster. Several assistants then made sure he stayed connected to an oxygen machine as they sealed his spacesuit and drove him to the plane.
Major Shontz and other U-2 pilots say the planes gradually became more integrated in the operations in Iraq and Afghanistan. But since the flights over Afghanistan began to surge in early 2009, the U-2s have become a much more fluid part of the daily battle plan.
Major Shontz said he was on the radio late last year with an officer as a rocket-propelled grenade exploded. "You could hear his voice talking faster and faster, and he's telling me that he needs air support," Major Shontz recalled. He said that a minute after he relayed the message, an A-10 gunship was sent to help.
Brig. Gen. H.D. Polumbo Jr., a top policy official with the Air Force, said recent decisions to give intelligence analysts more flexibility in figuring out how to use the U-2 each day had added to its revival.
Over beers at the clubhouse, decorated with scrolls honoring the heroes of their small fraternity, other U-2 pilots say they know their aircraft's reprieve will last only so long.
And the U-2's replacement sits right across the base - the Global Hawk, a remote-controlled drone that flies almost as high as the U-2 and typically stays aloft for 24 hours or more. The first few Global Hawks have been taking intelligence photos in Iraq and Afghanistan.
But a larger model that could also intercept communications has been delayed, and the Air Force is studying how to add sensors that can detect roadside bombs to other planes. So officials say it will most likely be 2013 at the earliest before the U-2 is phased into retirement.
"We've needed to be nimble to stay relevant," said Doug P. McMahon, a major who has flown the U-2 for three years. "But eventually it's bound to end."
[Whittaker/NYTimes/22March2010]
Section
III - COMMENTARY
Worst Science Article of the Week: The CIA Dosed a French Town With LSD!, by Smriti
Rao. The CIA's experiments with mind-control and hallucinogenic drugs are well documented. It's hard to forget about programs like Operation Midnight Climax, in which the agency studied the effects of LSD by dosing unsuspecting clients at brothels. But did the agency go so far as to send an entire French village on an acid trip that killed a few people and institutionalized a bunch more? According to The Telegraph, the CIA did just that in 1951.
For years, people familiar with "the incident of the cursed bread" (or le pain maudit) have subscribed to the theory that villagers in Saint-Pont-Esprit in Southern France suffered massive delusions because they all ate bread contaminated by ergot, a hallucinogenic fungus. After eating bread from a local baker, the villagers reported such delusions as the conviction that they were missing body parts or had animals in their stomachs.
Now, The Telegraph reports that the incident was not "ergotism" caused by the fungus, as previously believed, but was actually a bad trip caused by the CIA, which had spiked the village bread with LSD, or maybe just sprayed LSD into the air. Quite a story, huh? Too bad it doesn't hold up under scrutiny.
The always credulous Telegraph reports that the discovery was made by investigative journalist H. P. Albarelli Jr., who published a book on the CIA's research. Albarelli claimed the outbreak was the result of a covert experiment carried out by the CIA and the U.S. army's top secret Special Operations Division (SOD) at the height of the cold war.
The Telegraph reports:
"Mr. Albarelli came across CIA documents while investigating the suspicious suicide of Frank Olson, a biochemist working for the SOD who fell from a 13th floor window two years after the Cursed Bread incident. One note transcribes a conversation between a CIA agent and a Sandoz official who mentions the "secret of Pont-Saint-Esprit" and explains that it was not "at all" caused by mould but by diethylamide, the D in LSD."
The Telegraph's article immediately drew sharp responses from other journalists, who dismissed the report as bunkum. David Steven of The Global Dashboard points out that Albarelli's theories were rejected out of hand by Steven Kaplan, a history professor at Cornell University and a noted bread expert who has written a book on the incident.
Terming the report "incoherent and harebrained," Kaplan told France 24:
"I have numerous objections to this paltry evidence against the CIA. First of all, it's clinically incoherent: LSD takes effects in just a few hours, whereas the inhabitants showed symptoms only after 36 hours or more. Furthermore, LSD does not cause the digestive ailments or the vegetative effects described by the townspeople."
It is absurd, this idea of transmitting a very toxic drug by putting it in bread. As for pulverizing it [for ingestion through the air], that technology was not even possible at that time. Most compellingly, why would they choose the town of Pont-Saint-Esprit to conduct these tests? It was half-destroyed by the US Army during fighting with the Germans in the Second World War. It makes no sense."
The report also came under fire for not getting its science right. Derek Lowe, a chemist who has worked in several major pharmaceutical companies, points to the reporter's assertion that the hallucinations were caused by diethylamide, the D in LSD, as incorrect.
He writes:
"Laughter may now commence. For the non-chemists in the audience, diethylamide isn't a separate compound; it's the name of a chemical group. And LSD isn't some sort of three-component mixture; it's the diethylamide derivative of the parent compound, lysergic acid. (I'd like to hear this guy explain to me what the "S" stands for).
In short, neither the author of this new book, nor the people at the Telegraph, nor the supposed scientific "source" of this quote, knows anything about chemistry. This is like saying that the secret of TNT is a compound called "Tri". Nonsense."
[DiscoverMagazine/15March2010]
When the CIA's Intelligence-Gathering Isn't Enough, by David Ignatius. The headline read like something you might see in the conspiracy-minded Pakistani press: "Contractors Tied to Effort to Track and Kill Militants." But the story appeared in Monday's New York Times, and it highlighted some big problems that have developed in the murky area between military and intelligence activities.
The starting point for understanding this covert intrigue is that the U.S. military has long been unhappy about the quality of CIA intelligence in Afghanistan. The frustration surfaced publicly in January in a report by the top military intelligence officer in Kabul, Maj. Gen. Michael T. Flynn, that began: "Eight years into the war in Afghanistan, the U.S. intelligence community is only marginally relevant to the overall strategy."
It's a complicated tale, but it has some simple lessons: Under the heading of "information operations" or "force protection," the military has launched intelligence activities that, were they conducted by the CIA, might require a presidential finding and notification of Congress. And by using contractors who operate "outside the wire" in Afghanistan and Pakistan, the military has gotten information that is sometimes better than what the CIA is offering.
A reconstruction of what happened, based on conversations with a half-dozen military and intelligence sources, raises two crucial issues: What new military procedures are needed to bring "information operations" and related activities under better control? And how can the CIA improve its own collection efforts so that private contractors aren't brought in to fill the gaps?
The outsourced intelligence operation described by the Times began in 2008 with a push from the Pentagon's Strategic Command, which oversees information operations. A Stratcom civilian named Michael D. Furlong began funding former journalists to provide "ground truth," with a planned budget of $22 million.
Another private intelligence effort was launched in November 2008, when a Boston firm called American International Security Corp. (AISC) was hired by the New York Times to free its reporter David Rohde, who had been kidnapped by the Taliban that month. The firm turned to Duane "Dewey" Clarridge, a former CIA officer who launched the agency's counterterrorism center in 1986 and was an important figure in the Iran-contra affair. He set about building a network of informants who could help free Rohde.
Rohde escaped in June 2009, but Clarridge's network continued to function. It currently has about 10 operatives who act as case officers, drawn from the United States, Britain, South Africa and other countries. These officers, in turn, run about 20 "principal agents" who are in contact with roughly 40 sources in Afghanistan and Pakistan.
Clarridge had been in contact with U.S. Special Operations Command (SOCOM) in Tampa since March 2009 to share information and to make sure that his private network wouldn't clash with U.S. operatives. He is said to have briefed both Adm. Eric Olson, the head of SOCOM, and Lt. Gen. David Fridovich, the director of its center for special operations.
Clarridge's contacts with the military deepened last July after he provided detailed intelligence about an Army soldier, Pfc. Bowe Bergdahl, who had been captured by the Taliban in eastern Afghanistan.
The two outsourced operations linked up in mid-2009, after Furlong met one of Clarridge's operatives in Dubai. In October, the military awarded a contract for several million dollars to Clarridge and AISC through a series of subcontractors.
The CIA, meanwhile, was flummoxed by Clarridge's freelancing. The new chief of station in Kabul protested last summer, and lawyers drew up new rules. Clarridge's mission was described as "force protection," a normal military activity in a war zone. His unclassified reports were fed into the J-3 operations center in Kabul, and then often classified and disseminated though intelligence channels.
Clarridge's reports carried the rubric "Force Protection Atmospherics." His sources were described as "cooperators" and his effort was termed "commercially gathered" data, rather than intelligence collection.
But these semantics didn't resolve the tension between military activities, which fall under Title 10 of the U.S. Code, and CIA covert action, which is authorized under Title 50. This gray area has led Adm. Dennis Blair, the director of national intelligence, to argue privately that the country may need what could be described as a new "Title 60," that blends the two in a coherent framework with proper controls.
The case of the clandestine contractors should prompt a serious debate about creating such a Title 60, and about the military's rules for information operations. Meanwhile, Clarridge's private network continues to provide fresh intelligence. His latest report from Paktia province was disseminated on Monday, the same day the New York Times article appeared.
[Ignatius/WashingtonPost/18March2010]
Section
IV -
BOOKS, RESEARCH REQUESTS AND COMING EVENTS
Books
Nest of Spies, by Fabrice de Pierrebourg and Michel
Juneau-Katsuya, Reviewed by Rebecca Walberg. Canada has become one of the most attractive countries in the world for spies, argues Nest of Spies, and to date little has been done about it. Because of our prosperity, advanced technology, close alliances with major powers and multicultural cities, we're not only a ripe target for spying, but also a fairly safe haven for foreign agents. Flabby law enforcement and an unwillingness to prosecute have only worsened the situation. While the United States, Great Britain and France have tried hundreds of cases involving spying since the 1990s, Canada has not prosecuted a single one.
During the Cold War, Pierrebourg and Juneau-Katsuya suggest, Canada was of great strategic importance because of its geography, directly between much of the Soviet Union and the U.S. - and therefore of interest to foreign intelligence agencies. After the Berlin Wall fell, many Canadians, along with their government, assumed the days of espionage were over and consequently allocated fewer resources to gathering intelligence in other countries and to protecting Canadian intelligence. As a result, many states widely considered security threats - among them China, Iran and Tunisia - have taken advantage of our lax security, but so have ostensible allies, including the U.S., South Korea, France, Israel and Japan.
While spies summon up Jason Bourne-style images of car chases and assassinations, the reality is both more mundane and harder to detect. Economic espionage, in which business intelligence, technology and research are stolen for the benefit of other countries, is the single largest category, with the Canadian economy losing an estimated $1-billion a month as a result.
Industrial spying between France and the U.S. and the resulting political tensions have led to the expulsion of diplomats suspected of involvement. Here, though, the Canadian Security Intelligence Service is prohibited from pursuing espionage carried out by corporations, which further lowers the risk to foreign spies.
Another category of espionage is what Pierrebourg and Juneau-Katsuya call "foreign interference." Immigrants make up a growing proportion of the Canadian population, and many left behind countries in which freedom of speech, human rights and democratic accountability are, to put it mildly, not highly prized. When new Canadians criticize their countries of origin, rally activists to their cause and lobby their representatives to press for reforms, they frequently become targets for reprisals, ranging from social pressure and coercion all the way to assassination.
More byzantine yet is the role played by foreign intelligence agencies in bringing conflicts from other parts of the world to Canadian soil. Nest of Spies discusses the Air India bombing of 1986 extensively, and points out that there are still many holes in our understanding of how this atrocity, until Sept. 11 the bloodiest terrorist act in history, came about.
One factor, the authors suggest, is the track record of interference on the part of Indian agents with Sikh communities within Canada. This hampered RCMP and CSIS intelligence gathering, and dissuaded moderate Sikhs from involving themselves with government investigations, ultimately helping to provide cover for the Sikh extremists behind the bombing.
Pierrebourg and Juneau-Katsuya offer many ideas for private citizens and companies seeking to improve their security. Collectively, we need to commit resources and enforce existing laws to fight espionage, as well as change our mindset to recognize both our vulnerability to it and the high price it exacts.
Nest of Spies often wanders off into chatty and gossipy territory. "It is impossible to know when [a source] is telling the truth," the authors concede about a man claiming to be a former Mossad employee, in the midst of 14 pages dedicated to his exploits and adventures. While entertaining reading, this and similar passages have the feel of celebrity tell-alls meant to titillate. The authors should have stuck to the more journalistic and analytic sections dedicated to technical, and measurable, aspects of espionage. Despite the many contentious claims the authors make, they provide relatively few footnotes and there is no index.
The structure of the book is problematic, with major themes organized neither chronologically nor by country. Perhaps as a result, some passages are repetitive. The colloquial tone is also questionable: The frequent broadsides against unnamed bureaucrats could have been deleted, for example, without weakening any of the author's arguments or criticisms.
These flaws aside, though, de Pierrebourg and Juneau-Katsuya present a strong argument that Canada's security institutions don't pay enough attention to espionage, particularly when it comes to technology and business. [Rebecca Walberg is a Winnipeg writer and policy analyst.]
[Walberg/NationalPost/13March2010]
The KGB's Poison Factory: From Lenin to
Litvinenko, by Boris Volodarsky, Reviewed by Joshua Foust. It can be difficult to stand out in the somewhat crowded field of Russian scare-books. Whether arguing for the resumption of a "new cold war" or whatever conspiracy happens to be topical, recent years have seen an avalanche of books arguing that Russia is not the somewhat broken creature it is often portrayed in the West.
Boris Volodarsky, however, has a leg up. A former Captain in the GRU, he has first-hand access to many of the files, personalities, and programs one would need to discuss Russia's international espionage activities. It is just this encyclopedic understanding that he brings to The KGB's Poison Factory. Though often confusing because of the sheer volumes of names, pseudonyms, shadow programs, and overlapping personalities he puts into play, Volodarsky very clearly argues that the posture of Russian intelligence is essentially the same as has been throughout the 20th century.
Volodarsky argues that Russian intelligence holds as much venom for its individual detractors as for its international opponents, And it is venom that he seems primarily concerned with. Assassinations obviously can take many forms - the U.S. prefers flying robots these days. But Volodarsky argues that Russia has a special affection for poison.
And what a poison it is: The particular hallmark of Russian poisons, besides their creativity, seems to be their relatively long kill time. A victim will languish for weeks, even months, in sheer agony before either barely surviving or dying. Volodarsky describes this tradition while tracing Soviet and Russian poisoneers (for lack of a better term) through early uses of merely unusual plant extracts to the industrial development of unique compounds. The resulting potions are engineered specifically to mimic other problems, usually some form of gastritis, so that by the time doctors eventually realize what's happened, it's too late to fix.
The inspiration for Volodarsky's history is the death of Alexander Litvinenko, the KGB defector slowly poisoned with Polonium-210 in 2006. While it can be difficult to parse the complicated history that Volodarsky writes - this is a book by and for insiders - the picture that emerges is damning of Russia going back decades. This might be where the book would fit in the pantheon of anti-Russia books: Volodarsky argues that the post-USSR poisoning activities of Russian intelligence demonstrate a strong continuity between Soviet and Russian activities.
In fact, if we were to read this in the context of similar books of the Russian government's capriciousness - those by Anna Politkovskaya, for instance - it would be easy to think that it is more dangerous to oppose Moscow today than it was, say, in the 1970s, even though there was much more concern over it back then. Since Vladimir Putin left the Kremlin, Volodarsky writes, the Sluzhba Vneshney Razvedki, or SVR, Russia's foreign intelligence service, no longer has to report to the President - they only have to inform him, the prime minister. Given Putin's almost legendary intolerance for dissent, and the environment he's created, in which unofficial murders aren't exactly approved but aren't exactly punished, it is a pretty terrifying realm that Volodarsky explores.
Unfortunately, that exploration is a real bear to sift through. While the book is engaging as a work of espionage, I found it difficult to keep track of the tangle of personalities and operations. That is in part because Volodarsky's footnotes aren't exactly immaculate. Mixed with clinical discussions of operations are Volodarsky's ideas about what constitutes good or poor tradecraft. While it's certainly fun to see how central Vienna is to Russian-European espionage, my eyes glazed over during long expositions of place and timing. That's not to fault Volodarsky's writing. But for those who aren't borderline obsessives with the mechanics of tradecraft, the endless detail can become exhausting. It is a little too inside baseball for a layman to pick up and comprehend, and Volodarsky doesn't provide enough documentation for a layman to follow the breadcrumbs and learn more (though he does, to his credit, highlight other books for more information on individual kills.).
The KGB's Poison Factory is still fascinating to read. As long as you can slog through. Whether you're looking for a concise history of Russian intelligence assassinations, or even a taste of how bewildering the intelligence hall of mirrors can be, it is a pretty severe indictment of how the former Soviet capital operates.
[Foust/Registan/12March2010]
Research Requests
Looking to Speak to Children of CIA Parents.
Dear AFIO Members,
My name is Ian Shapira and I'm an enterprise reporter for the Washington Post. I am looking to speak with families who had a parent in the CIA from the 1970s to the present day for a potential book project. I am hoping to speak with children of CIA officers who can talk about the bonds they formed with their parents after learning about their time in the agency, or what they wish they knew but never found out. I am also looking to speak with families who have relatives currently in the CIA and am happy to speak privately or off the record.
At the Post, I am a features reporter in our Metro section and typically write about young adults, those now in their 20s in the so-called Millennial generation. I have been a staff writer at the Post for 10 years and was a lead reporter on a team that won the Pulitzer Prize for coverage of the Virginia Tech shootings in 2007. Recently, I wrote a front-page story about children, now in their 40s or 50s, whose parents were in the CIA and what they remembered about their mom or dad.
Feel free to reach me at 202-569-9442 or via email: shapirai@washpost.com. And just to repeat: I am happy to honor any requests to speak off the record.
Best regards,
Ian Shapira, The Washington Post -
1150 15th Street N.W. | Washington, D.C. 20017 -
Office: +1 202-334-7572 | Mobile: + 1 202-569-9442
E mail: shapirai@washpost.com - http://blog.washingtonpost.com/story-lab/
Intelligence Analysts: The US Department of Labor’s Occupational Information Network (O*NET) is seeking assistance from expert intelligence analysts, with at least 7 years experience, to complete a series of occupational questionnaires for a national database. This database is a service to employers, human resource professionals, job counselors and labor market analysts across the country, providing information about the skills, abilities, activities and work context for about 900 occupations nationwide. Analysts will be asked to complete several O*NET questionnaires to provide information on their field of expertise. These take about 90 minutes to complete. Interested applicants should contact Traci E. Davis, Business Liaison O*NET Operations Center, RTI International at 877-233-7348, Ext. 109 or by email tdavis@onet.rti.org. Further information about this initiative can be found at www.doleta.gov/programs/onet
Coming
Events
EVENTS
IN COMING
TWO MONTHS....
MANY Spy Museum Events in March, April and May
with full details are listed on the AFIO Website at www.afio.com. The
titles for some of these are as follows:
- Monday, 5 April 2010; 6:30 pm - Washington, DC - "An Evening with
Nigel West: Secrets from the Cambridge Spies" at the International
Spy
Museum
- Wednesday, 14 April 2010; 6:30 pm - Washington, DC - "Striking
Remotely: Predator Drones" at the International Spy Museum
- Thursday, 15 April 2010; noon - 1 pm - Washington, DC - "Broker,
Trader, Lawyer, Spy" at the International Spy Museum
- Wednesday, 5 May 2010; 6:30 pm - Washington, DC - "Abduction,
Black Site Prisons, and the CIA: Extraordinary Rendition Today" at
the
International Spy Museum
- Thursday, 6 May 2010; 12 noon – 1 pm - Washington, DC - "On the
Front Lines of Cyber War with Richard A. Clarke" at the
International
Spy Museum
- Monday, 10 May 2010; 6:30 pm - Washington, DC - "Our Man in
Havana" at the International Spy Museum
- Thursday, 13 May 2010; 10 am - 2:30 pm - Washington, DC -
"Codebreaking in World War II: The Inside Story" at the
International
Spy Museum
- Thursday, 20 May 2010; 6 pm - Washington, DC - "Goldfinger" at the
International Spy Museum
Thursday, 25 March 2010, 6 p.m. - New York,
NY - AFIO Metro NY Chapter hosts U.S. Secret Agent who specialized in
Explosives and Codes. The AFIO New York Metro Chapter
Thursday evening meeting will feature Dr. John Behling,
one of the last
surviving members of the forerunner agency of CIA [the Office of
Strategic Services], who will tell of his training in explosives and
codes, his being dropped behind enemy lines, his work with the
Resistance, and the post-war years in the Occupied Zones. Of special
interest is his eyewitness account of his visit to the Mauthausen
Extermination Camp, and his subsequent search for escaping Nazis,
hidden assets and war criminals.
Many of these experiences will be in a yet-to-be-published memoir on
his distinguished wartime service. He also spent many years
working for the U.S. Department of State.
This is a first-hand account with remarkable -- and chilling --
details that no film or printed work can convey in the same manner.
Do
not miss it.
Location: University Club, 9th Floor. $40 pp; $20 students/military
No reservations required.
For further information contact Jerry Goodwin, Chapter President, at
347-334-1503 or afiometro@yahoo.com
Wednesday, 31 March 2010, 8 p.m. - Coral
Gables, FL - AFIO Miami Chapter hosts Keith Thomson in special reading
"Once A Spy" and a special presentation on Microdrones -- or did you
think it was an ordinary insect on your ceiling? Thomson
will read from his spy novel: Once A Spy, at Books & Books in
Coral
Gables. The Microdrones [professional unmanned aerial vehicles] have offered to debut their
2.5LB drones beforehand for AFIO members, as well. Microdrones have
been
used to extraordinary success by police in the UK (FAA regulations are
thwarting their use in the U.S.; meanwhile radio-controlled
helicopters
and airplanes up to 55LBs have essentially no restraints). Clearly an
event not to miss. For further information contact chapter President
Tom
Spencer at trsmiami@aol.com
THURSDAY,
1 April 2010 - Tysons Corner, VA - National AFIO Luncheon featuring
Seymour Hersh and Marc Thiessen.
Full details are here.
Wednesday, 7 April 2010, 6 p.m. - Las Vegas, NV - AFIO Las Vegas Chapter Meeting features Matthew Zucker, Las Vegas Metropolitan Police Department. Topic: “Mexican Drug Cartels.” Employed with the Las Vegas Metropolitan Police Department (LVMPD) for 12 years, Officer Matthew Zucker is currently serving as a TAC Officer assigned to the Detention Services Training Division. While assigned to the LVMPD Detention Services Division Intelligence Section, Officer Zucker worked issues involving Hispanic Gangs, Black Gangs, White Gangs, Prison Gangs, and Outlaw Motorcycle Gangs. He compiled a certified training class entitled “Introduction to Surenos” which has been taught to approximately 10,000 police and corrections officers nationwide. He has been a featured speaker at three consecutive LMPD Gang Conferences, the Virginia Gang Conference, American Jails Conference, Southern Nevada Gang Symposium, the National Latino Peace Officers Conference, Bureau of Alcohol, Tobacco, Firearms and Explosives (BATF) Hispanic Agent Association Conference, Federal Law Enforcement Analysis Training, and the LVMPD Sheriff’s Recruitment Council.
Location: Nellis Air Force Base Officers' Club. Guest names must be submitted to me by 4:00 p.m., Monday, March 29th. Join us at 5 p.m. in the "Check Six" bar area for liaison and beverages.
If you plan to attend, RSVP with names by 4 pm, Monday, March 29th. Entrance to the Base for your guest(s) cannot be guaranteed if I don't have their names
(unless they already have military ID to enter the base). (The deadline to submit names of guests is by 4:00 p.m March 29, 2010)
All guests must use the MAIN GATE located at the intersection on Craig Road and Las Vegas Blvd. 5871 Fitzgerald Blvd.
Bring your spouse and/or guest(s) to dinner as well as our meeting, but remember to submit your guest(s) names to me be the stated deadline above.
You may email at BentleyM@nv.doe.gov or call me anytime at 702-295-1024 if you have any questions. We look forward to seeing you!
Tuesday, 13 April 2010, 5 p.m. - Hampton
Roads, VA - The AFIO Norm Forde Hampton Roads Chapter - to hear Carl
Finstrom on Stella Polaris. AFIO member Carl
Finstrom will
present, "Stella Polaris: The Exfiltration of Finnish COMINT
Material"-
The evacuation of the Finnish Intelligence Service from Finland to
Sweden in Sep 1944.
Finstrom is an AFIO Member and Past President, Christopher Wren
Association.
Stella Polaris was the code name for a secret plan developed by the
Finnish Intelligence Service for their evacuation to Sweden in the
final
phase of World War Two. The plan was coordinated with the Swedish
counterpart intelligence organizations in June 1944 after the Soviets
resumed a massive offensive. By the end of June there was a real
danger
of a Soviet breakthrough and Soviet occupation of Finland. The Finns
sought to relocate their intelligence assets to neutral Sweden so that
they could continue the fight working with a significant Finnish
stay-behind force. Finns stored weapons and ammunition at hundreds of
locations to support a stay-behind force of at least 50,000 resistance
personnel. The Stella Polaris story is of great interest to
cryptologic
historians. The story of the evacuation of the Finnish Military
Intelligence Branch from Finland to Sweden after the signing of the
ceasefire with the USSR in Sept 1944 is perhaps the most extraordinary
event in the history of communications intelligence
Free and open to the public. Light refreshments will be served.
RSVP: Melissa Saunders at mwsaunders@cox.net
Location: Main meeting room at Tabb Library, York County. Directions:
From Norfolk take I-64 West. Merge onto US-17 North via Exit 258B
toward Yorktown. Follow US-17 North approximately 2.2 miles to Victory
Blvd/VA-171 East. Turn right onto Victory Blvd/VA-171 East. Turn right
at the next traffic light onto Hampton Hwy/VA-134 South. Turn right at
the next traffic light onto Long Green Blvd. Tabb Library is on the
immediate right. It is across the street from the Victory YMCA.
From Williamsburg take I-64 East. Merge onto Victory Blvd/VA-171 East
via Exit 256B. Follow Victory Blvd/VA-171 East approximately 2 miles.
Turn right onto Hampton Hwy/VA-134 South. Turn right at the next
traffic
light onto Long Green Blvd. Tabb Library is on the immediate right.
It
is across the street from the Victory YMCA.
Tuesday, 13 April 2010, 1130 hrs - Tampa, FL - The AFIO Suncoast Chapter will hold its Spring meeting and luncheon on "Current Challenges to America's Historical Strengths in the Intelligence Community" featuring Walter Andrusyszyn. Check-in registration will commence at 1130 hours, opening ceremonies and lunch& Business Meeting at noon, followed by our speaker, Walter Andrusyszyn who will be discussing the consequences of global/U.S. debt; Middle East; Russia and Eastern Europe; NATO/EU; China and the proliferation of nuclear weapons with a favor of the White House and State Department. A full Luncheon with normal salad, rolls, dressing of choice, coffee and tea, and desert, will be served for the usual $15, all inclusive. We will have the wine and soda bar open at 1100 for those that wish to come early for our social time. We recommend you not miss this luncheon and presentation.
Reply ASAP, with your name and any guests accompanying you, to: Bill Brown at billbrown1@tampabay.rr.com
Your check payable to 'Suncoast Chapter, AFIO' (or cash) should be presented at time of check-in for the luncheon. Should you not have 'bumper stickers' or ID card for access to MacDill AFB, please so state in your response. Be sure to include your license number, name on drivers license and state of issue for yourself and for any guests you are bringing on base. And don't forget, all of you needing special roster gate access should proceed to the Bayshore Gate entrance to MacDill AFB (need directions, let us know). The main gate will send you to the visitor‘s center and they will not be able to help you get past security, unless you are just asking for directions to the Bayshore Gate.
We look forward to your response -- hopefully also seeing you at the O'Club at the April 13th luncheon.
Walter Andrusyszyn has been an Adjunct Professor of International Business at the College of Business Administration of the University of South Florida, where he began teaching in spring 2007. From January to May 2009 he was temporarily assigned as Deputy Permanent Representative to the U.S. Mission to NATO. He joined the Plastipak Packaging Company in January 2004 following a career in the U.S. Government. He retired from public service at the end of 2003, after serving at the White House as the Director for Northern and Eastern European Affairs in the National Security Council (he became Director in November 2001). Having entered the Foreign Service in 1980, he served in Stockholm (1980-82) and in East Berlin (1982-84) before returning to Washington to be the Desk Officer for Grenada and the Windward and Leeward Islands of the Caribbean (1985-1987). In 1987-1988 he was Special Assistant to Assistant Secretary Rozanne Ridgway in the Bureau of European and Canadian Affairs. He then served in Bonn as the Bonn Group Representative, responsible for Berlin and Four Power rights during Germany's reunification. In 1990, he headed the Political-Military unit at the American Embassy in Bonn.
Andrusyszyn became the Desk Officer for Latvia, Lithuania, and Estonia in 1992. In 1994, he returned to Bonn to head the unit reporting on domestic political events in Germany. In October 1995, he was assigned to the American Embassy in Sarajevo where he served during the Dayton Peace Talks and for the first months of IFOR deployment. For his efforts to gain the release of an imprisoned American journalist held by Bosnian Serb authorities, Mr. Andrusyszyn received the Secretary's Award for Heroism. In April 1996, he was assigned to Stockholm as Political Counselor. In August 1997 he was appointed Charge d’Affaires at the American Embassy in Tallinn, Estonia and in July 1999, be became director of the Office of European Security and Political Affairs, responsible for NATO and the OSCE. In September 2001 he was named the Director of the Task Force on Terrorism in response to the September 11 attacks.
Born in Blackburn, England in 1951, Mr. Andrusyszyn emigrated to the U.S. in 1957 and was raised in New York City. A graduate of New York University (1973), he attended the Fletcher School of Law and Diplomacy (1973-1975). He continued his studies in Germany and also worked as a local employee for the Sri Lanka Embassy in Bonn (1977-78).
Wednesday, 14
April 2010, 11:30 a.m. - Scottsdale, AZ - AFIO Arizona Luncheon on
"Current Perspective on Pakistan-Afghanistan-India Issues." Where: McCORMICK RANCH GOLF COURSE,7505 McCormick Parkway, Scottsdale
AZ 85258 ~ Phone 480.948.0260
Speaker: Prof Phil Jones, Director, Global
Security/Intelligence Studies, Embrey-Riddle Aeronautical, Prescott,
Arizona Campus, on “Current Perspective on Pakistan-Afghanistan,
Pakistan-India Issues.” Phil Jones is a former national intelligence
analyst and an international security expert with extensive field
experience in political and security risk studies. He has also served as
security manager for an international corporation and management
services for corporate clients.
He has done extensive field work for World Bank clients in
international development projects and is an expert on South Asia.
Professor Jones will focus on timely Pakistan-Afghanistan,
Pakistan-India issues.
RESERVATIONS: WE WILL NEED FOR EVERY MEETING an RSVP
no later than 72 hours ahead of time; in the past, not reserving or
cancelling without prior notice (72 hours prior to the meeting) created
much grief for those of us organizing the meeting and dealing with the
personnel!
WE ARE charged for the no-shows and please remember, we are a small
organization with a humble coffer!
We would therefore APPRECIATE that you all respond to this email to
confirm your presence (or not). Our meeting fees will be
as follows: $20.00 for members, $22 for non-member guests.
Email Simone simone@4smartphone.net or simone@afioaz.org or call and
leave a message on 602.570.6016
15 April 2010, 12:30 p.m. -
Las Angeles, CA - The AFIO L.A. luncheon hosts Marthe Cohn - "Behind
Enemy Lines: A French Spy Inside Nazi Germany."
Marthe Cohn was a member of the French First
Army intelligence service during World War II and made many covert trips
inside Nazi Germany. During her presentation, she will recount her
missions as a French Jewish spy and how she disguised herself as a young
nurse to find information about German troop movements and alert Allied
commanders. Her book, Behind Enemy Lines, an outstanding memoir, is the
story of an ordinary human being who, under extraordinary
circumstances, became the hero her country needed her to be. Nine years
ago she was awarded the Medaille Militaire, a relatively rare medal
awarded for outstanding military service and given, in the past, to the
likes of Winston Churchill.
She has appeared at the International Spy Museum in Washington, D.C.
and on CSPAN2.
Lunch will be served at 12:30 PM at the LMU campus for a cost of $20.
Please RSVP via email AFIO_LA@Yahoo.com by no later than April 9, 2010 if you would like to attend the meeting.
If directions are needed please forward an email request.
Friday,
16 April 2010 - Austin, TX - CIA Invites AFIO Members to the CIA - LBJ
Library Conference on STRATEGIC WARNING and The ROLE OF INTELLIGENCE -
Lessons Learned from the 1968 Soviet Invasion of Czechoslovakia.
Full details at top right column of this issue of the Weekly Notes.
23 - 25
April 2010 - S. Portland, ME - The New England Chapter of the Naval
Cryptologic Veterans Association (NCVA-NE) holds a spring Mini-Reunion
at the Marriott at Sable Oaks. For additional event
information, call (518) 664-8032 or visit website.
28 April 2010, 6:30 p.m. - Coral Gables,
FL - The AFIO Miami Chapter hosts dinner with CIA Clandestine Services
Officer. Save the date for a special dinner meeting with a
member of the Clandestine Service, CIA. We will be discussing the
mission and how we can help. This will be an opportunity to invite
trusted members of the business community. Details to follow. Inquiries
to trsmiami@aol.com
28 April 2010, 6:00 p.m. - Washington, DC - The
Goethe Institute will host a presentation and discussion of the film
"The Lives of Others" about the surveillance society of East Germany
during the Cold War.
If interested in attending this free cinema presentation and
discussion, send your RSVP to: rsvp@washington.goethe.org or by phone to: 202/289-1200 extension 170. Please note that the film discussion is scheduled to begin AFTER the film. The entire film will be shown, followed by discussion. To accept: rsvp@washington.goethe.org
30
April 2010, 9 a.m. - 6 p.m. - Washington, DC - "The Stasi and its
Foreign Intelligence Service" - Free Workshop by CWIHP and
GHI.
The German Historical Institute and The Cold War International
History Project of the Woodrow Wilson International Center for Scholars
hosts one day workshop on the STASI. This CWIHP-GHI workshop will be
held at the Woodrow Wilson Center, One
Wilson Plaza/1300 Pennsylvania Avenue N.W. in Washington. There will
be four panels with leading
American, German, British and Canadian historians working on the Stasi
and HVA: Panel 1: The Stasi and East German Society; Panel 2: The
Stasi
and the East German State and the SED (communist party); Panel 3: The
HVA and KGB; and Panel 4: The HVA and the West, which will deal mainly
with East German espionage in West Germany.
PROGRAM:
Friday, April 30 (Woodrow Wilson Center) The Stasi and East German
Society, with Uwe Spiekermann, GHI; Jens
Gieseke, Zentrum f�r Zeithistorische Forschung, Potsdam, and Gary
Bruce, Waterloo University, Canada. David Bathrick gives commentary.
The Stasi, the SED, and the GDR State - a panel with Christian
Ostermann, Woodrow Wilson Ctr, Walter S��,
Birthler Agency, Berlin, and Jefferson Adams, Sarah
Lawrence College.
Keynote Address: “The Stasi Legacy in Germany’s History” by Professor Konrad Jarausch, University of North Carolina
The HVA and KGB panel with Mircea Munteanu, Woodrow
Wilson Ctr, Benjamin Fischer, formerly CIA History
Staff, Washington, DC and Paul Maddrell, Aberystwyth
University. Comment by Oleg Kalugin, KGB (ret)
The HVA and the West panel with R. Gerald Livingston,
GHI, Georg Herbstritt, Birthler Agency, Berlin and Kristie
Macrakis, Georgia Institute of Technology
Dirk Doerrenberg, formerly Bundesamt f�r
Verfassungsschutz.
A luncheon keynote address on the Legacy of the Stasi in German
History will be delivered by Professor Konrad Jarausch of the University of North Carolina's History Department.
AFIO members are invited to participate in the discussion
following panelists' presentation. but asked to register with
the Wilson Center in advance, identifying themselves as AFIO members. No fee for participation is required. REGISTER by e-mail at the following address: coldwar@wilsoncenter.org.
Contact persons at the
Wilson Center: Mircea. Munteanu, CWIHP Deputy Director (Mircea.Munteanu@wilsoncenter.org)
or Tel: 202/69-4267, or Timothy McDonnell (Timothy.McDonnell@wilsoncenter.org).
A full program outline can be
provided by the Wilson Center contact persons.
Saturday, 1 May 2010, 1000 - 1430 - Salem, MA - The AFIO New England Chapter hear Ed Barr on "The State of HUMINT in CENTROM Area of Operations." Edward J. Barr, Esq. is a colonel in the U.S. Marine Corps Reserve and has served as an advisor to the United Nations and as a liaison to foreign governments. As a senior intelligence officer, Ed has worked with all major intelligence agencies, including the Central Intelligence Agency (CIA), the Defense Intelligence Agency (DIA), the Federal Bureau of Investigation (FBI), and the National Security Agency (NSA). He helped create an executive-level masters degree program at the Department of Defense's Joint Military Intelligence College (JMIC) and served as the program's first Marine Corps faculty member. He has served in countries throughout Southeast Asia and the Middle East to include Afghanistan, Iraq, and Djibouti. Ed has just ended an active duty period where he served as US Central Command’s senior counterintelligence and HUMINT officer, responsible for intelligence operations in 27 countries.
The May 1st chapter meeting will be held at the Salem Waterfront Hotel located in Salem MA. The hotel web site is here: http://www.salemwaterfronthotel.com/. For directions to the hotel look here: http://www.salemwaterfronthotel.com/location.html
Information about Salem MA and local hotels can be found here: http://salem.org/
Our schedule is as follows: Registration & gathering, 1000 - 1130, membership meeting
1130 – 1200. Luncheon at 1200 followed by our speaker, with adjournment at 2:30PM.
Note, as this meeting is a one-day event we have not made any hotel arrangements.
For additional information contact us at afionechapter@gmail.com
Advance reservations are $25.00, $30.00 at the door - per person.
Luncheon reservations must be made by 23 April 2010.
Mail your check and the reservation form to:
Mr. Arthur Hulnick, 216 Summit Avenue # E102, Brookline, MA 02446, 617-739-7074 or hlnk@aol.com
20 May 2010, 11:30 am - Colorado Springs, CO - AFIO Rocky Mountain Chapter at the Air Force Academy, Falcon Club features Mark Pfoff of the El Paso Sheriff Office, "Computer Forensics and all things Digital." RSVP to Tom Van Wormer at robsmom@pcisys.net
JULY EVENT in IRELAND, REQUIRING PLANNING NOW....
11-13 July 2010 - Dungarvan, Ireland - 2010 Analytic Best Practices Conference by Mercyhurst College Institute of Intelligence Education. Event to be at
Dungarvan Town Hall Theatre. Mercyhurst College's Institute for Intelligence Education hosts this special event which focuses on intelligence issues from a global perspective.
The conference will converse and discuss analytic best practices using panels of leading practitioners in the fields of medicine, law, finance, technology, journalism and the sub-disciplines of national security, law enforcement, and business.
This year the event will explore the nature of analysis and its application in various disciplines, building bridges between analytic practitioners and scholars within those disciplines, and exploring best practices in teaching analytic methodologies.
Intended takeaways for attendees include a deeper and broader appreciation of the value of different analytic methods borrowed as “best practices” from other disciplines, as well as instruction.
Speakers will include The Hon. Tom Ridge, Dennis Dirkmaat, Liam Fahey, Catherine Lotrionte, William McGill, Justine Marut Schober, Mark Williams, Anthony Campbell, Justyna Krajewski, Don McDowell, Chris Pallaris, Randy Pherson, Jim Poole, Barry Zulauf.
For additional information or questions, please contact:
Mr. Robert Heibel, Executive Director,
Institute of Intelligence Education at Mercyhurst College at 1 (814) 824-2117 or rheibel@mercyhurst.edu
Mrs. Michelle Henderson, Mercyhurst College, 1 (814) 824-2131 at mhenderson@mercyhurst.edu
Mrs. Heather Tate, Instructional Systems Designer, Mercyhurst College, 1 (814) 824-3121 or at htate@mercyhurst.edu
REGISTRATION: Opens March 1, 2010. FEE: $195 attendee; $75 spouse/guest.
FULL DETAILS and REGISTRATION:
https://www.regonline.com/dungarvan_conference_2010
PLAN NOW FOR THIS UPCOMING
SPYCRUISE�....
13 - 20
November 2010 - Ft. Lauderdale, FL - SPYCRUISE to Grand Turks, Turks
& Caicos; San Juan, PR; St. Thomas, USVI; and Half Moon Cay, Bahamas
- with National Security Speakers Discussing "Current & Future
Threats: Policies, Problems and Prescriptions."
This National Security Educational
Lecture/Seminar co-sponsored by the Centre for Counterintelligence and
Security Studies (CICENTRE) and Henley-Putnam University, being held
aboard Holland America's M.S. Eurodam features some top
intelligence experts, as follows:
Porter Goss, Former Director, CIA
Gen. Michael Hayden, Former Director of CIA and NSA
Peter Brookes, Heritage Foundation Fellow, Former CIA
Operations Officer
Michael Braun, DEA Operations Chief, Retired,
Managing Partner, Spectre Group Intl
Dr. Michael Corcoran, President, Henley-Putnam
University
Major General Paul E. Vallely, U.S. Army Retired
Clare Lopez, Retired CIA Operations Officer, Ci
Centre Professor; VP, Intelligence Summit
SPACE IS LIMITED - Reserve your stateroom now for this EIGHT DAY
cruise/conference.
RESERVATIONS: www.DFunTravel.com or call 1-888-670-0008.
Fees are remarkably reasonable for an eight day cruise: $1,199 inside
cabin; $1269 Ocean View Cabin; $1449 Verandahs; $1979 Suites. Price
includes program, taxes, port charges and gratuities.
Colorful brochure here.
For
Additional Events
two+ months or greater....view our online Calendar of
Events
-----------------------------------------------------------------------
Disclaimers
and Removal Instructions
Weekly
Intelligence Notes (WINs) are commentaries on Intelligence and related
national security matters, based on open media sources, selected,
interpreted, edited and produced for non-profit educational uses by
members
and WIN subscribers.
REMOVAL
INSTRUCTIONS: We
do not wish to add clutter to inboxes. To discontinue receiving the
WINs:
a)
IF YOU ARE A MEMBER -- click here: UNSUBSCRIBE and supply your full name and email
address
where you receive the WINs. Click SEND, you will be removed from
list.
If this link doesn't open a blank email, create one on your own and
send to afio@afio.com with the
words: REMOVE FROM WINs as the subject, and provide your full
name and
email address where you are currently receiving them.
b)
IF YOU ARE NOT A MEMBER, and you received this message, someone
forwarded this newsletter to you [contrary to AFIO policies]. Forward
to afio@afio.com the
entire WIN
or message you received and we will remove the sender from our
membership
and distribution lists. The problem will be solved for both of us.
CONTENTS
of this WIN [HTML version recipients - Click title to jump to story or
section, Click Article Title to return to Contents. This feature does
not
work for Plaintext Edition or for some AOL recipients]. If you wish to
change to HTML format, let us know at afio@afio.com. The HTML feature also does not work
for
those who access their e-mail using web mail...however NON-HTML
recipients
may view the latest edition each week in HTML at this link: https://www.afio.com/pages/currentwin.htm
-----------------------------------------------------------------------
WINs
are protected by copyright laws and intellectual property laws, and
may
not be reproduced or re-sent without specific permission from the
Producer. Opinions expressed in the WINs are solely those of the
editor(s)
or author(s) listed with each article. AFIO Members Support the AFIO
Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for
back issues of the WINs, information about AFIO, conference agenda
and
registrations materials, and membership applications and much more!
(c)
2010, AFIO, 6723 Whittier Ave Suite 200, McLean, VA
22101. Voice: (703) 790-0320; Fax: (703) 991-1278; Email: afio@afio.com
Click here to return to top.