AFIO
Weekly Intelligence Notes #24-10 dated 29 June 2010
REMOVAL
INSTRUCTIONS: We
do not wish to add clutter to inboxes. To discontinue receiving
the WINs, click here: |
CONTENTS
Section I -
INTELLIGENCE HIGHLIGHTS
Section
II - CONTEXT & PRECEDENCE
Section
III - COMMENTARY
Section
IV - JOBS AND
COMING
EVENTS
Jobs
Coming Events
Current
Calendar New and/or Next Two Months ONLY
- 9, 16, 23 July 2010, 8 and 10 pm - Washington, DC - THE SPY MAGIC SHOW - An incredible exploration into the secrets of spies, shown through stunning sleight-of-hand magic by master magician Michael Gutenplan.
- 10
July 2010, 1000 - 1430 - Salem, MA - The AFIO New England
Chapter meets
to conduct business and hear Douglas Wheeler on "Writing a
History of
Spying" and John Behling, Jr. on "Origins
of Islamic
Extremism."
- Thursday, 15 July 2010, 11:30 am - Colorado
Springs, CO - The Rocky Mountain Chapter hears Tim
Murphy on R&D Platform Usage in Intelligence.
- Wednesday,
21 July 2010, 10 am - 12:45 pm - Annapolis Junction, MD -
"The
Mysterious Rosetta Stone: A Code-Cracking International
Treasure" with
Dr. Joel Freeman, is topic at the National Cryptologic
Museum Foundation
Summer Cryptologic meeting.
- 22
July 2010 – San Francisco, CA – The AFIO Jim Quesada
Chapter hosts John
Yoo, former deputy assistant attorney general in the
Office of Legal
Counsel of the U.S. Department of Justice, where he worked
on national
security and terrorism after the September 11 attacks.
- 24 July 2010 - Abilene, KS - Korea 60: Eisenhower the Peacemaker - Honoring Those who Served in Korea - CIA joint conference at Dwight D. Eisenhower Presidential Library and Museum, Abilene, Kansas
- 28 July 2010, 9 am - 5 pm - Miami, FL - INFRAGARD South Florida and the FBI invite AFIO MEMBERS to their South Florida Conference
- Saturday, 31 July 2010, 10 am - 12 noon - Coral Gables,
FL - AFIO/Miami Police Department Counter-Terrorism
Training
- 17-20 August 2010 - Cleveland, OH - AFIO
National Symposium
on the Great Lakes. Details....
- 29-30 September 2010 - Washington, DC -
Conference on the American Experience in Southeast Asia,
1946-1975
featuring Kissinger, Negroponte & Holbrooke, by the
U.S. Department
of State.
Events at the International Spy Museum in
July & August with full details
- Wednesday, 7 July 2010; 6:30 pm - Washington, DC - "A
New Cold War: Inside Nuclear Iran" at the International
Spy Museum
- Thursday, 15 July 2010; 12 noon – 1 pm - Washington, DC -
"Eyes in the Sky: Eisenhower, the CIA, and Cold War Aerial
Espionage"
at the International Spy Museum
- Thursday, 5 August 2010, noon - Washington, DC -
"Silent Sentry: The Untold Story of the National Security
Agency" - at
the International Spy Museum
- Wednesday, 11 August 2010, 6:30 pm - Washington, DC -
"Uneasy Alliance: The CIA and ISI in Pakistan" - at the
International
Spy Museum
- SpyCruise� Eastern Caribbean setting
sail November 13th, 2010. For information on the upcoming
cruise, visit https://www.afio.com/index.html#spycruise
SpyCruise Stateroom Discount Program
As some of you may know, you may earn a free stateroom if
you acquire 15 other stateroom bookings (double
occupancy). For some
this can prove difficult. Therefore, in order for
each of you to
be able to benefit from this program, we want to offer
everyone a
discount based whatever number of additional staterooms
you are able to
fill. For every additional stateroom you get booked
for
SpyCruise, your stateroom will be discounted by 1/15th of
the cost of
the additional stateroom. In
order for
your stateroom to be completely free, you would need to
acquire 15
additional bookings of the same category or greater than
the one you
book. When your friends, colleagues, family or
neighbors book
their SpyCruise, they will need to tell the agent that
you recruited
them. This way we can track who has earned the
discounts.
Of course, each of those guests may participate in this
program as
well.
- Farewell - A movie based on spy Vladimir Vetrov
- In Select Theaters July 2010 - New York and Los Angeles - July 23, 2010
Cast & Crew: Director: Christian Carion Producers: Christophe Rossignon, Bertrand Faivre, PHILIP BOEFFARD
Cast: WILLEM DAFOE, Guillaume Canet, EMIR KUSTURICA, ALEXANDRA MARIA LARA, Dapkunaite, Dina Korzun, David Soul, Fred Ward
Written by: Eric Raynaud
France 2009 | Run time: 112 min.
Director: Christian Carion | Language: French - English - Russian
- In 1981, Colonel Grigoriev of the KGB (real name - Vladimir Vetrov), disenchanted with what the Communist ideal has become under Brezhnev, decides he is going to change the world…
Discreetly, he makes contact with a French engineer working for Thomson in Moscow and little by little passes on documents to him - mainly concerning the United States - containing information which would constitute the most important Cold War espionage operation known to date.
During a period of two years, French President, François Mitterrand, was to personally vet the documents supplied by this source in Moscow, to whom the French Secret Service gave the codename « Farewell ».
Then master of the White House, Ronald Reagan, set aside his reluctance to work with a French Socialist to put this unhoped-for information from the very heart of the KGB to use. Farewell would in fact decapitate the network which enabled the KGB to gain in-depth knowledge of scientific, industrial and military research in the West.
Once the USSR had been deprived of these precious sources of information, Ronald Reagan's announcement of the new « Star Wars » military programme sounded the death bell of the Soviet Union. The Berlin Wall would fall before the end of the 80s…
In his own way, Farewell managed to change the world, by avoiding traditional espionage methods too well known to the KGB and by not asking for any financial compensation whatsoever – much too capitalist for his taste. He simply followed his destiny, so that a new world might dawn for all his fellow Russians, but especially for his son.
A trailer of the film can be viewed at this link:
http://trailers.apple.com/trailers/independent/farewell/
- More information about the case and film is available at: http://www.FarewellTheMovie.com
-
|
REGISTER NOW
18 - 20 August 2010

AFIO National GREAT LAKES Intelligence Symposium 2010
"Intelligence and National Security on the Great Lakes and Northern Border"
at the Crowne Plaza Hotel, Cleveland, OH
Co-Hosted with the AFIO Northern Ohio Chapter
Includes presentations by U.S. Coast Guard on Great Lakes/Northern Border security;
National Air/Space Intelligence Center; Air Force Technical Applications Center; Ohio Aerospace Institute, Dinner/Cruise on Nautica Queen on Lake Erie.
Spies-in-Black-Ties Reception and Banquet
Make your reservations here.
Agenda is here.
To reserve rooms at the
Crowne Plaza Hotel in Cleveland, Ohio now at the $89/nite special event
rate, use the following link: http://tinyurl.com/37frwnl
Documents From Two Intelligence Symposia, Now
Online...
Strategic Warning and the Role of Intelligence: Lessons
Learned From The 1968 Soviet Invasion of Czechoslovakia
The Czechoslovak crisis began in January 1968. The Czech
communist leadership embarked on a program of dramatic liberalization
of the political, economic, and social orders. These reforms
triggered increasing Soviet concerns culminating in the invasion of 21
August 1968. This collection of documents pertains to these issues,
the responses and analysis of this event in history. Follow
this link to the documents.
Baptism By Fire: CIA Analysis of the Korean War
This
collection includes more than 1,300 documents consisting of national
estimates, intelligence memo, daily updates, and summaries of foreign
media concerning developments on the Korean Peninsula during 1947 -
1954. The release of this collection, which coincides with the 60th
anniversary of the start of the war, makes available to the public the
largest collection of Agency documents released on this issue. The
release of these documents is in conjunction with the conference, "New
Documents and New Histories: Twenty-First Century Perspectives on the
Korean War," co-hosted by the Harry S. Truman Presidential Library
and the CIA in Independence, Missouri.
Follow this link to the documents.
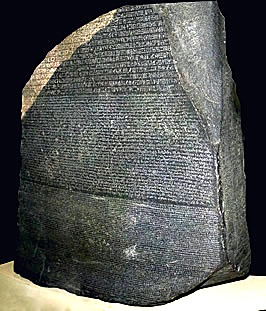
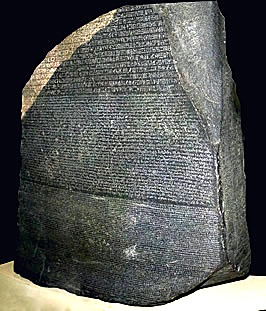
The Mysterious Rosetta Stone: A
Code-Cracking International Treasure
Dr. Joel Freeman speaks at the
National Cryptologic Museum Foundation Summer Cryptologic meeting.
Wednesday, 21 July 2010, 10 am - 12:45
pm - Annapolis Junction, MD
All AFIO members are invited to hear guest speaker, Dr. Joel Freeman, CEO and President of the Freeman
Institute, discuss the history of the Rosetta Stone, focusing on the
historical connection between the Rosetta Stone and the breaking of
codes. Guests will have an opportunity to view the full-sized,
three-dimensional Rosetta Stone replica normally on display in the lobby
of the National Cryptologic Museum. Dr. Freeman is a gifted speaker and
author. As part of the program there will be a brief presentation to
acknowledge the Milt Zaslow Memorial Award for Cryptology that was
presented for the first time at this year's Maryland History Day
Ceremony on 24 April.
Location: the L3 Conference Center in
the National Business Park. Lunch will be served at 11:45 following the
presentation. L3 Conference Center is located at 2720 Technology Dr,
Annapolis Junction, MD 21076 in the Rt. 32 National Business Park.
Cost: the fee is $25 to cover program
& lunch costs.
Confirm your attendance by Wednesday, 14 July, by
calling (301) 688-5436 to pay by credit card or by mailing a
check to NCMF, POB 1682, Ft. Meade, MD 20755. We look forward to seeing
you there.
CALL
FOR
PAPERS
for 2011 NSA Conference
6 - 7 October 2011
- Laurel, MD -
The NSA's Center for Cryptologic History hosts their
Biennial
Cryptologic History Symposium.
2011 theme: "Cryptology in War and Peace: Crisis
Points in History."
Full Details
WIN CREDITS FOR THIS
ISSUE: The WIN editors thank the following special
contributors to
this issue: dh, pjk, fm, cjlc, th, and fwr.
They have contributed one or more
stories used in this issue.
For Additional Events two+ months or more....
view our online Calendar of Events |
Section
I - INTELLIGENCE
HIGHLIGHTS
Russia's FSB To Offer Rewards for Terrorism Information. The Russian Federal Security Service (FSB) will offer monetary rewards to people who pass on information about suspected terrorist activity.
The draft order, signed by FSB director Alexander Bortnikov, says monetary rewards will be offered for any information on suspected terrorist attacks and their organizers. The reward will, however, only be given if the information leads to the capture of a terrorist or the prevention of a terrorist attack.
The order did not define how much the FSB is prepared to pay for such information, but said rewards will be calculated for each case individually, depending on the quality of the information and the results it yields.
Kommersant said that such measures were implemented in 2005 in the search for former Chechen president Aslan Maskhadov. According to some sources, informants were paid up to $10 million, although it is not known who received the reward or what information they gave.
The order is part of a wider FSB policy to increase counter-terrorism measures in Russia.
In April a new bill that allows "preventive measures" against individuals committing extremist actions was submitted to the Russian parliament, fueling fears among opposition parties of a revival of Soviet-era practices.
[Novosti/22June2010]
Intelligence Assessments Paint Bleak Portrait in Afghanistan. After nearly nine years in Afghanistan, U.S. and NATO leaders still do not adequately understand or communicate with the Afghan people, according to classified coalition assessments. That cultural disconnect, along with the West's continued support for a corrupt central government in Kabul, has made it easy for the Taliban to recruit insurgents and prevent NATO from making significant gains, according to classified coalition assessments.
Those assessments paint a grim forecast for Afghanistan. Violence has escalated dramatically since the beginning of the year as insurgents have planted 94 percent more improvised explosive devices than the previous year, to cite one metric of military failure.
"We're getting beat up," said a U.S. military official with direct knowledge of a classified military report titled "The State of the Taliban," which was published late last year and updated in January. "They [the Taliban] know their own people - they are culturally accurate. We know the facts but we are culturally inaccurate. The main message in the reports is that we don't fully understand our enemy and we are not clearly communicating our message to the people."
The report - put together by military intelligence officers who have interviewed high-level Taliban detainees in Afghanistan - recommended that local U.S. commanders mediate cease-fire negotiations with local Taliban commanders.
Taliban commanders are much more effective propagandists than the NATO coalition, the report found. In information-starved Afghanistan, the Taliban has been able to persuade many that the 9/11 attacks were actually a response to the planned invasion of Afghanistan by the United States. And ideas about Islam, including that America does not allow Muslim women to cover themselves and that mosques are not permitted in most American cities, have been easy to sell to potential recruits, the report found.
Afghanistan has grown increasingly deadly for U.S. and coalition forces. Nine NATO soldiers, including five Americans, died in several different incidents in Afghanistan Monday.
Lt. Col. Tadd Sholtis, spokesman for Gen. Stanley McChrystal, NATO's top commander in
Afghanistan, acknowledged the existence of the sober assessments. He told The Examiner that the International Security Assistance Forces are "stepping up engagements with Afghan media at all levels and are facilitating more meetings with credible third parties." The aim is to assure that pro-coalition clerics, teachers and others can address false rumors spread by the Taliban.
Sholtis said negotiations with Taliban commanders are never simple.
"The bulk of insurgents clearly do not see foreign forces as a credible negotiating partner," he said. "It is likely that the insurgents will be more willing to relax their conditions for discussions with the government as the pressure on them from counterinsurgency efforts increases."
U.S. military officials consider current operations to be the last phase of the nation's longest war, leading to a withdrawal planned to begin in about a year. Many military commanders believe that does not allow enough time to turn Pashtun tribal leaders away from the Taliban. And the Afghan army and police forces are years away from providing security for the nation, according to the classified assessments.
Overwhelming corruption in President Hamid Karzai's government and an ingrained tribal system that has survived thousands of years has made Afghanistan its "own monster," said a U.S. military official.
But Sholtis said the Taliban also is rife with corruption, including "nepotism, bribes in the form of 'taxation' and a host of other abuses that are common features of areas that have been controlled by the Taliban."
"The Afghan government doesn't need to be perfect, it just needs to be better than the alternative," Sholtis said.
But some U.S. and Afghan officials said the association of corruption with the Karzai government is an insurmountable obstacle to NATO credibility.
"The U.S. does not hold Karzai responsible for corruption," said an Afghan official in Afghanistan, who asked not to be named. "The U.S. put Karzai in office - he stole the last election and he uses NATO financing, U.S. money to line his coffers."
Military officials involved in civil affairs work highlight other issues in Afghanistan: There are not enough civilian workers to help complete promised construction projects, local governments steal project funding, there are not enough Pashtun interpreters, security concerns inhibit local workers from taking coalition jobs.
"We need to reevaluate who the enemy really is," said a U.S. civil affairs officer in Afghanistan. "We need to leave an Afghanistan where the enemy won't resurge. Based on the evaluations and interviews in the report, we're not sure we're fighting the right war or fighting the war the right way."
[Carter/SFExaminer/22June2010]
Spies Are Everywhere: Germany Accuses Russia of Espionage. Russia and China are the leaders in spying on German technology and pose a threat to the country, said Interior Minister Thomas de Maiziere, presenting an annual report by Germany's internal security agency.
The 300-page report by the Office for the Protection of the Constitution - Germany's domestic intelligence agency - was presented on Monday by its head Heinz Fromm along with Maiziere.
The authors of the report underline that Germany is a country with an economy oriented for the development of technologies and export.
"The situation with dangers [to German economy] is concrete. Such states as Russia and China - via their secret services - actively conduct undercover work in such fields as economy, science and research," the document reads.
According to the data released, Russia and China also "track technical information as well as business strategies."
The most dangerous inquiries, the document states, "are those aimed at mobile communications and computer systems (conducted via internet) of various businesses and state organizations. International financial and economic crisis also has its negative effect upon security structures of private enterprises."
[RT/22June2010]
Spying By Norway On the Increase. Norway is currently engaged in spying in at least eight countries. Lieutenant-General Kjell Grandhagen, recently-appointed head of the intelligence service, says the scope of electronic surveillance is constantly expanding.
The government has increased electronic intelligence service funding by 35 percent in the last five years. 930 million kroner is now spent annually. The number of assignments has increased by more than 400 percent since 2003.
"Developments in the last few years have been characterized by an ever-increasing breadth of tasks for the intelligence service. The number of clients and scope of individual missions have together resulted in an ever-increasing workload for the electronic surveillance service section," Lt-Gen Grandhagen tells Aftenposten.
The intelligence service is currently operating in Afghanistan, Somalia, Chad, Sudan, Egypt, Sudan, Congo, the Middle East, Kosovo, and Bosnia.
These are all countries and regions where Norwegian officers and soldiers are stationed, with one of the military's trademarks being the integration of electronic surveillance when using Special Forces.
Norway hasn't spied as much since the Cold War, and the High North is still the most important area. Grandhagen has said previously that his job is to make sure Norway doesn't get caught unawares, and its interests in the High North are his top priority.
NATO has also used Norwegian high-technological surveillance to monitor the Russians for decades. The Globus-II radar positioned in Vard� is just one example.
"The government's commitment to the High North, traditional threats such as terror, the spread of weapons of mass destruction, as well as Norway's foreign military engagement, means a steady increase in the electronic surveillance section's operations," he says.
Meanwhile, other countries are actively placing their spies on Norwegian soil. The Police Security Service (PST), counted intelligence officers from 19 different countries.
Though some of them are here legally, some have come under false pretences. Many pose as diplomats, businessmen, or journalists, for example, and their aim is to mislead, gather information, influence, recruit, undermine and, at worst, commit sabotage on behalf of foreign states to Norway's cost.
Last year, the PST rated the threat of intelligence against Norway as high. [TheForeigner/22June2010]
Ex-CIA 'Spy for Hizbullah' Fights to Stay in US. A former CIA agent accused of spying for Hizbullah has launched a campaign to regain her United States citizenship, according to her personal blog.
Lebanese Nada Prouty, who immigrated to the US and became an anti-terrorism spy, pleaded guilty in 2007 to citizenship fraud and illegally accessing an FBI computer system and was accused as working for Hizbullah as a double agent.
Federal prosecutors alleged Prouty took advantage of her close relationship with brother-in-law Talal Chahine, who fled to Lebanon in 2005 following a tax evasion lawsuit and is thought to have links with Hizbullah, to provide the party with information on a US probe.
Prosecutors said that Chahine was a Hizbullah supporter and had helped Prouty commit fraud by entering into a "sham marriage" with her first husband, Scott Pelley, in order to obtain US citizenship.
Last week Prouty commenced a series of television interviews, declaring that her admission of guilt was issued under duress and strenuously denying any link with either Hizbullah or Hamas. "It makes me sick that anyone would think I would do anything to harm the United States," Prouty said on CBS's 60 Minutes.
"Everything you can possibly think of I was threatened with, including deportation to Lebanon," she said. "Given all the pressure that was put on me, I had to make a decision about the destruction of my friends and family members or plead guilty and move on."
Prouty, who is credited with assisting in the capture of Saddam Hussein and leading investigations into the USS Cole bombing, claimed that her bank accounts had been frozen but that prosecutor's refusal to deliver a custodial sentence proved her innocence.
In 2008, the CIA sent a letter to prosecutors, indicating that lie-detector tests "did not identify any information that Prouty cooperated or engaged in unauthorized contact with a foreign intelligence service or terrorist organization."
However, after the airing of Prouty's interview, the US Justice Department issued a statement defending its prosecution.
"It appears that Prouty seeks to cast herself as a victim of the US government and the subject of an overzealous prosecution," it said in a statement. "The only victim in this case was the US government, which was repeatedly defrauded by Prouty and risked compromise because of her illegal acts."
[DailyStar/23June2010]
CSIS Chief's Blunder. With a few ill-chosen words, the head of the Canadian Security Intelligence Service (CSIS) has effectively tarred every provincial cabinet minister across the country as a possible foreign spy.
"We're in fact a bit worried in a couple of provinces that we have an indication that there's some political figures who have developed quite an attachment to foreign countries," Richard Fadden said in an interview with CBC that aired Tuesday night. "In at least two provinces, there are ministers of the Crown who we think are under at least the general influence of a foreign government."
Which politicians or which provinces? He wouldn't say. Which foreign governments? Again, he wouldn't say, although he essentially confirmed that China is one of them in response to a question from the interviewer (Peter Mansbridge).
By Wednesday, Fadden was in full retreat. "At this point, CSIS has not deemed the cases to be of sufficient concern to bring them to the attention of provincial authorities," he said in a statement.
In other words, he was blowing smoke, perhaps in order to reinforce his pitch for more funding for CSIS to conduct counter-espionage. In the process, he has undermined his own credibility and cast unwarranted suspicion on provincial politicians. At the very least, he should be severely reprimanded by his political masters in Ottawa.
[TheStar/23June2010]
Death Sentenced Norwegians Ask Congo for Pardon. Two Norwegian ex-soldiers sentenced to death for murder and espionage in the Democratic Republic of Congo have written to President Joseph Kabila to ask for a pardon.
"We have sent a plea for grace citing the extremely difficult conditions of their detention as well as family considerations," Norwegian lawyer Morten Furuholmen said.
Joshua French, 28, who also has British nationality, and Tjostolv Moland, 29, were sentenced to death June 10 by a military court in the northeastern DRC town of Kisangani.
They were found guilty of the May 2009 murder of a Congolese driver of a vehicle they hired in the town, and of spying.
"The request is for a total pardon or, failing that, the commuting of the death penalty" to a prison term that could be served out in Norway, Furuholmen said.
French and Moland did not apologize in their letter for the crimes for which they were convicted, the advocate said.
"They have always said that they are innocent and so it would be illogical for them to apologize," he said.
The Norwegian government, which has always dismissed claims that the men were spies, has said it has received assurances from Congolese authorities that the death penalty would not be carried out.
The court also ordered the men and the Norwegian government to pay a fine of 60 million dollars (73.3 million dollars).
DR Congo has not carried out a death sentence since Kabila came to power in 2001, but has commuted such penalties to life imprisonment.
[AP/24June2010]
Acting Spy Chief Plans Departure. The acting director of national intelligence has resigned, effective at the end of August, U.S. officials said, raising concerns that vacancies in the uppermost ranks of the nation's top spy office could create a security vulnerability if President Barack Obama's nominee for the post isn't confirmed soon.
David Gompert's departure could come before the Senate, scheduled to be in recess during August, has time to confirm Mr. Obama's nominee for the top intelligence post, James Clapper.
If Mr. Gompert leaves before Mr. Clapper is confirmed, chief of staff Lt. Gen. John Kimmons would step in temporarily, but Lt. Gen. Kimmons has announced his plans to retire.
"I would be concerned about the impact on our intelligence community," said Rep. Silvestre Reyes (D., Texas), chairman of the House intelligence committee. "It could be left without a centralized, focused direction at a time when we're initiating large-scale offensives in Afghanistan and, in the wake of several attempted domestic terrorism attacks, undertaking important steps to improve intelligence integration."
Mr. Obama fired his intelligence director, Dennis Blair last month. The White House had hoped that Mr. Blair would stay on until his successor was confirmed, according to officials familiar with the matter. Mr. Blair instead said he would leave the following week on May 28.
As deputy director, Mr. Gompert became acting director. But he also "affirmed he was there as part of the Blair team," and issued his resignation not long after Mr. Blair was fired, a U.S. intelligence official said. "The end of August would be when he would wrap up."
The official said, though, that there wouldn't be a vacancy at the top if Mr. Gompert leaves. Lt. Gen. Kimmons could extend his stay to assume the acting director post, this person said, adding, "someone will be in charge running the place should that gap occur."
The path to Mr. Clapper's confirmation remains uncertain.
The chairman of the Senate intelligence committee, California Democrat Dianne Feinstein, has said she has reservations about Mr. Clapper taking the intelligence-director post because he is a retired general who is now running Pentagon intelligence and she didn't want a military official in the top spy job. She also has said she wouldn't hold a confirmation hearing for Mr. Clapper until Congress passed an intelligence bill that has been held up since last year.
"I look forward to the bill passing in the due course of moving on the Clapper nomination," Ms. Feinstein said, adding that she believed Mr. Clapper could be confirmed before the August recess.
The Senate last week reached a compromise on key issues with the White House that loosened some of the requirements that bolstered congressional oversight of spy agencies, which the White House found objectionable.
House Speaker Nancy Pelosi is seeking provisions in the bill that would require intelligence agencies to inform the entire intelligence committees, rather than just their leaders, of major intelligence programs.
"The speaker has made very clear that she wants to have more notification for members of the intelligence committees, not just the chair and ranking member," said Ms. Pelosi's spokesman Brendan Daly.
She also wants to re-insert a provision that gives the Government Accountability Office the power to review intelligence programs. That provision was dropped in the compromise the Senate made with the White House because the White House objected to it. Unless that impasse is broken soon, or Ms. Feinstein moves ahead with the confirmation without the intelligence bill's passage, congressional officials say Mr. Clapper might not be confirmed until after lawmakers' summer break.
[Gorman/WallStreetJournal/25June2010]
Russian Woman Arrested for Assisting German Spy. A Russian woman accused of assisting a suspected German spy and who has been living in India without legal documents has been arrested.
Oliga Timoshik, in her early 30s, was arrested by Punjab Police from Jaipur and is currently in three days of police remand.
'She is a close aid of a suspected German spy Thomas Kuehn. He was arrested last month from Nangal town as he was living here without visa documents and a passport,' H.S. Hundal, deputy superintendent of police, Nangal in Ropar district said.
'During the interrogation, he told police that his Russian girl-friend had taken away his passport to Nepal. We scrutinized his e-mails and tracked the girl in Jaipur. Her visa had expired and the police have seized her mobile phone and documents,' Hundal added.
According to a source, the Russian woman 'told the police that she is a freelance writer she was sending news stories from India to the newspapers of several other countries. She is also changing her statements at regular intervals.'
She has been allowed to talk to Russian embassy officials, her lawyer and relatives twice a day in the presence of the investigating officer. [SIFY/24June2010]
The Price of Secrecy: Billions. Secrecy, it turns out, isn't cheap. The government and industry spent nearly $10 billion last year to keep government secrets secret, according to the Information Security Oversight Office.
The $9.93 billion total was a modest increase over the $9.85 billion spent in 2008. Not surprisingly, there's been a sharp increase in spending on classifying information since 2001, when the total was $5.48 billion.
Nearly half of the 2009 costs went to securing the computer networks that store classified information. The cost of physically securing sensitive information, managing the data, and paying people to handle it each cost more than $1 billion.
A tiny fraction of that spending, $44.6 million, also went to declassification. But William Bosanko, who directs the oversight office, noted that represented an increase of 4% from 2008.
"Sustaining and increasing investment in declassification is necessary to maintain the classification system and is fundamental to the principles of transparency, participation, and collaboration," Bosanko wrote in a letter to President Barack Obama accompanying his report, which was distributed Friday by Steven Aftergood of the Federation of American Scientists.
The true spending on secrecy is likely much higher than $10 billion, however. The report doesn't include the money that most of the spy agencies, including the Central Intelligence Agency and the National Security Agency, spend on securing their classified data.
The reason: The amount they spend on classifying data is classified. [Gorman/WallStreetJournal/25June2010]
FBI Field Chief Wants 'Transparency.' Shawn Henry has a favorite word that one might not expect from the head of the FBI's Washington field office - "transparency." Just four months into his post as assistant director in charge, Henry says he's already working hard to make the agency more accessible.
He's visited schools, showed up at several of the bureau's Citizens' Academy classes, met with community groups and attended a memorial for fallen local police officers.
But among his larger aims is to partner more with the private sector. The FBI is sharing information with businesses that previously would have been off-limits - even in the midst of criminal investigations - to make sure they're equipped against cyberterrorism and other threats.
"I want to walk up to the line," the 48-year-old Henry said during a recent interview at his office. "I want to give you as much as I can so that you understand what it is that we do."
The inevitable caveat, of course, is what Henry calls maintaining the cloak of secrecy. With the District of Columbia remaining a top target for terrorism and foreign intelligence agencies, and a central site of public corruption, there's a lot he won't reveal.
As a whole, however, the FBI has evolved over the past five years from a "need-to-know" to a "need-to-share" agency, Henry said.
For instance, under his recent tenure overseeing the FBI's cyber division, he said the agency shared information with banks and financial services about a software vulnerability that organized crime groups used to steal millions of dollars. Banks and financial services were then able to prevent attacks.
It would have been kept hidden in the past, he said.
Just this week, his office reached out to a private sector entity, though he can't say about what. But examples include his office talking with retailers, manufacturers, defense contractors and utility companies about threats specific to their industries, he said. That could mean sharing information even during an ongoing investigation - an unusual move for the agency, he said.
Before, FBI officials may have bristled at sharing that information because it could ruin their chances of convicting their suspects later on.
"And what I've said is we have an obligation and a responsibility to share the information so people can protect themselves," Henry said.
The New York native is on familiar turf. He first joined the agency in 1989 at the D.C. field office as a special agent focusing on public corruption and serving on the SWAT team. He also has worked in the Baltimore and Philadelphia field offices, and held several positions at FBI headquarters, including overseeing audits of the agency's operations across the country and heading the cyber division.
Now, Henry directs about 900 agents and 900 professional staff at facilities in Washington and Manassas, Va., for the FBI's second-largest field office after New York.
Situated in the nation's capital, his office has been at the center of countless landmark cases.
In the 1970s, agents investigated bombings by the Weather Underground movement in Washington and the Watergate scandal that led to President Richard Nixon's resignation. The office also handled the case of John Hinckley, who tried to assassinate President Ronald Reagan.
In addition, the office has tackled major espionage cases as well as local crime and corruption issues. For instance, it led the 1990 sting that videotaped former D.C. Mayor Marion Barry smoking crack cocaine, assisted in the D.C. sniper investigation and the case of Harriette Walters, a D.C. tax office manager who pleaded guilty in 2008 to embezzling nearly $50 million.
More recently under Henry, the office has been involved in several high-profile cases, such as five young Muslim men from the D.C. area who were convicted Thursday on terror charges by a Pakistani court. His agents investigating how financial bailout funds are being used also headed a case that resulted in the indictment last week of Lee Bentley Farkas, a mortgage company executive, and others accused of scheming to steal more than half a billion dollars.
In the past few months, his agency opened a cross-border task force office in suburban Maryland with FBI agents from Washington and Baltimore working with local police on gangs, violent neighborhood crews and other crime.
For all of its reach, Henry said the FBI can't do it alone. His transparency approach with community outreach is twofold: gain the public's trust and show people they can play a role in thwarting threats.
"I think sometimes we overprotect and I think that by doing that there's a sense of mistrust," he said.
Nizam Ali, co-owner of the historic diner Ben's Chili Bowl, met Henry at the field office's informational citizen course this spring. To his surprise, Ali said Henry was "extremely warm and friendly."
"I think it's a great message and a great goal of the FBI to be more transparent and I think that really helps with public perception," Ali said. "He'd be a great guy to invite to your home for a cookout," he said of Henry, a burly man with a serious brow who occasionally flashes a smile or quips about his bald head.
Although some might be skeptical about how much transparency an FBI head can offer, Henry said he likes the word. Without breaching delicate protocols or giving away state secrets, he said he finds there's still room for openness.
"I want to be able to pull back the curtain - come on in, here's what we're doing," he said.
[WashingtonPost/26June2010]
Mistrust Marks ISI-CIA Ties. American officials have told Pakistan that there is mistrust between the Central Intelligence Agency (CIA) and the Inter Services Intelligence (ISI).
"John Tierney (the chairman of the House Armed Services Committee of the US Congress) told a Pakistani delegation that there is mistrust between the CIA and ISI," according to a report of the Senate's standing committee on defense about a visit by its members to the US last month.
The 17-page official report, which has been drafted by Iftikharullah Babar, secretary of the Senate committee under the supervision of Senator Javed Ashraf Qazi seems to be a revealing document regarding the thinking of the US establishment towards Pakistan.
This is the first time that the US administration has expressed their views in front of any parliamentarian delegation.
Qazi - who had headed both ISI (1993-95) and Military Intelligence (1990-1991) , while leading the committee delegation in US - held extensive meetings with key members of the US establishment, including one CIA official and Richard Holbrooke the US Special Envoy for Pakistan and Afghanistan.
In a luncheon meeting with Representative John Tierney, the Senator told the delegation that there is mistrust between the CIA and ISI. To this Qazi said this perception was baffling because ISI and CIA are working closely together in this war and there is no such feeling on the ISI side. Qazi warned, "If the mistrust message is conveyed back home it would be taken seriously. CIA should clarify to the Congress if their relationship with ISI is good."
[Dawn/25June2010]
C.I.A. Chief Sees Taliban Power-Sharing as Unlikely. The director of the Central Intelligence Agency, Leon E. Panetta, expressed strong skepticism about the prospects for an Afghanistan deal being pushed by Pakistan between the Afghan government and elements of the Taliban, saying militants do not yet have a reason to negotiate seriously.
"We have seen no evidence that they are truly interested in reconciliation, where they would surrender their arms, where they would denounce Al Qaida, where they would really try to become part of that society," said Mr. Panetta in an interview on ABC's news program "This Week."
Mr. Panetta's comments came amid reports, not yet confirmed by American officials, that Afghan President Hamid Karzai has met personally with Sirajuddin Haqqani, leader of the Haqqani network, a faction of the Afghan Taliban considered to be close to Al Qaeda.
Acknowledging that the American-led counterinsurgency effort is facing unexpected difficulty, Mr. Panetta said that the Taliban and its allies at this point have little motive to contemplate a power-sharing arrangement in Afghanistan.
"We've seen no evidence of that and, very frankly, my view is that with regards to reconciliation, unless they're convinced that the United States is going to win and that they're going to be defeated, I think it's very difficult to proceed with a reconciliation that's going to be meaningful," he said.
Mr. Panetta's comments were the strongest pushback from a top Obama administration official following a report of Pakistan's deal-brokering efforts last week in The New York Times. It came days after a major shake-up in the American military leadership, as President Obama fired his top commander in Afghanistan, Gen. Stanley McChrystal, replacing him with Gen. David H. Petraeus but stating that the American war strategy would not change.
Mr. Panetta acknowledged that the strategy, based in part on the addition of 30,000 more American troops, is off to a troubled start, though he insisted it was making progress.
"It's harder, it's slower, than I think anyone anticipated," he said.
On "Fox News Sunday," the chairwoman of the Senate Intelligence Committee, Dianne Feinstein, Democrat of California, said if General Petraeus objects to the July 2011 date set by President Obama to begin to withdraw American troops, the drawdown should be postponed.
Asked what the president should do if General Petraeus asks for six more months, Ms. Feinstein replied: "I would say give it to him, absolutely." She noted that the president's July 2011 date only sets the beginning of a withdrawal, so General Petraeus "has flexibility, realistically."
On another pressing matter, Mr. Panetta declared publicly what several administration officials have said privately since late last year: that the administration now believes Iran is continuing, at some low level, to work on the design of a nuclear weapon. That contradicts a 2007 National Intelligence Estimate, the consensus view of the American intelligence community.
But he also said he believes it would take Iran two years to convert its current stockpile of nuclear material into deliverable weapons, and he admitted to a disagreement with Israel's intelligence services over whether Iranian leaders have decided to go ahead and produce a weapon.
He said he thought the Israelis were "willing to give us the room to be able to try to change Iran diplomatically and culturally and politically, as opposed to changing them militarily."
Mr. Panetta dodged a question about whether Iran's slow pace in enrichment was partly a result of a covert American program to feed faulty parts to the Iranians and to interfere with their computer systems. That program, begun in the Bush administration, accelerated under President Obama.
"I can't speak to, obviously, intelligence operations, and I won't," he said. "It's enough to say that clearly, they have had problems."
He said the recent sanctions on Iran might "help weaken the regime" but then added: "Will it deter them from their ambitions with regard to nuclear capability? Probably not."
In his remarks on ABC, Mr. Panetta reiterated the narrow goal Mr. Obama set for the Afghan war: "The fundamental purpose, the mission that the president has laid out, is that we have to go after Al Qaeda. We've got to disrupt and dismantle Al Qaida and their militant allies so they never attack this country again."
That goal explains why the administration is skeptical of Pakistan's effort to broker reconciliation between the Afghan government of President Hamid Karzai and the militant Haqqani network, part of the Afghan Taliban coalition that historically has had close ties to Al Qaeda.
But Mr. Karzai and Pakistani leaders believe that with the United States scheduled to begin a withdrawal next year, it makes sense to work aggressively toward a coalition that would involve elements of the Karzai government and the Taliban, both largely from the dominant Pashtun ethnic group. That has led to nervousness on the part of Tajiks and other ethnic minorities, which fear Pashtun domination.
Mr. Panetta admitted that despite the C.I.A.'s aggressive campaign against Al Qaeda and its allies in Pakistan's tribal areas - primarily using missiles fired from drone aircraft - the hunt for Osama bin Laden has made little progress. He said the last precise information on the Qaeda leader's whereabouts came in "the early 2000s."
He said authorities were alarmed by the recent flurry of terrorist plots and attacks aimed at the United States, most recently the failed car-bomb attack on Times Square May 1. He said such plotters have included both people directed by Al Qaeda and its affiliates as well as "self-radicalized" militants such as Major Nidal Hasan, accused of killing 13 people at Fort Hood, Texas, last November.
Together, Mr. Panetta said, "those kinds of threats represent I think the most serious threat to the United States right now."
[Shane/NYTimes/28June2010]
Lebanon Arrests "Suspected Spy at Mobile Phone Network." Lebanon has arrested a technician working for a mobile telephone network who is suspected of spying for Israel.
Lebanon has arrested more than 70 people since launching a major crackdown in April 2009 against suspected Israeli spy networks, including security force members with equipment for monitoring communications.
Israel has not commented on the arrests.
Lebanon and Israel remain technically in a state of war, and convicted spies face life in prison with hard labor or the death penalty if found guilty of contributing to Lebanese loss of life.
[AP/26June2010]
Iran Accuses CIA of Waging Psychological Warfare. Iran accused the US Central Intelligence Agency of waging psychological warfare against it through "fake reports," saying the CIA knows Tehran's nuclear program has no military aims.
Foreign Ministry spokesman Ramin Mehmanparast dismissed CIA director Leon Panetta's comments that Iran could have nuclear weapons ready to use by as early as 2012.
"Such remarks fall within the framework of psychological warfare aimed at creating a negative perception about Iran's peaceful nuclear activities," Mehmanparast told state news agency IRNA.
"The American officials, especially their intelligence apparatus, know that Iran's nuclear program is in no way a military one but is aimed at peaceful purposes," he said.
"Those who bring up such fake reports seek to deflect world public opinion from the main concern... the nuclear arsenals of several countries and a certain regime," he said in apparent reference to Iran's arch-foe Israel.
Speaking on ABC network's "This Week" program, Panetta on Sunday said that Iran has manufactured enough low-enriched uranium for two atomic weapons.
He said Tehran would need a year to enrich it fully to produce a bomb, and that it would take "another year to develop the kind of weapon delivery system in order to make that viable."
"There is a continuing debate right now about whether or not they ought to proceed with a bomb. But they clearly are developing their nuclear capability and that raises concerns," Panetta said.
Western powers led by Washington suspect that Iran is masking a weapons drive under what Tehran says is a civilian atomic program.
On June 9, the United Nations Security Council imposed a fourth set of sanctions on Iran for refusing to halt sensitive uranium enrichment work.
The UN sanctions were followed by unilateral US and EU measures targeting Iran's energy sector and its banking industry.
Iranian officials, including President Mahmoud Ahmadinejad, have dismissed the sanctions and vowed to continue with the country's nuclear program.
Neither the United States nor its top regional ally Israel, the sole if undeclared nuclear-armed power in the Middle East, have ruled out a military strike to scupper Iran's atomic drive.
"Israel is very concerned about what's happening in Iran," Panetta noted.
"We continue to share intelligence (with Israel) as to what exactly is Iran's capacity," he told ABC, adding that Israel feels "more strongly that Iran has already made the decision to proceed with the bomb, but at the same time they know that sanctions will have an impact."
Russian President Dmitry Medvedev has expressed concern over Panetta's remarks.
"This information has to be checked but such information is always worrying and all the more so because the international community does not recognise the Iranian nuclear program as transparent," he told reporters on Sunday in Toronto.
"If this is proved, it would make the situation even more tense," Medvedev said, adding that Russia might have to re-examine its position on the matter.
Russia, which unlike the United States has diplomatic ties with Iran, has in the past been reluctant to impose tough sanctions but backed the latest UN move following Tehran's repeated defiance of orders to halt uranium enrichment.
At the G8 meeting world leaders urged Iran to hold a "transparent dialogue" over its nuclear program.
Later on Monday Ahmadinejad is expected to unveil his conditions for talks.
But in a remark directed at the G8, an angry parliament speaker Ali Larijani said: "You will take the wish to stop Iran's nuclear activities to the grave," Fars news agency reported.
[Deshmukh/AP/28June2010]
Ex-Hacker Who Accused Leak Suspect Is Still Talking. For weeks now, the United States military has been holding an Army intelligence analyst, Bradley Manning, in connection with the release of classified materials to the whistle-blower Web site Wikileaks. He is suspected of being the source of the 2007 video of an Apache helicopter killing 12 civilians in Iraq, including two Reuters journalists. More ominously, he is feared to have leaked 260,000 secret diplomatic cables.
The case broke open when a prominent figure in the hacking world, Adrian Lamo, handed over to the authorities chat logs in which, Mr. Lamo said, Specialist Manning admits to having given the video to Wikileaks.
Those conversations date to late May. Specialist Manning has been under arrest since at least early June and has not uttered a peep publicly. When the Department of Defense announced the arrest, it said that Specialist Manning was in pretrial confinement in Kuwait "for allegedly releasing classified information." Mr. Lamo, on the other hand, has been talking ever since.
There he is on his frequently updated Twitter feed, describing his daily thoughts and activities. In self-published press releases, he explains his actions, or, as one puts it, "Adrian Lamo Clarifies Role in Bradley Manning Wikileaks Arrest."
More comprehensively, Mr. Lamo has had his Web site redirect to Formspring.me, where he answers questions posed by strangers. Typical colloquies: "How does it feel to be the no-1 snitch in US?" Answer: "We're #1! We're #1! We're #1!"
Or "You realize that you have condemned Manning to death, right?" Answer: "Kid'll probably get six months."
Or, more sympathetically, "U have done the right thing." Answer: "I believe this to be true."
It was to be expected that the controversial video, published with the title "Collateral Murder," would sustain an online rumor mill, debating society and newsroom, often all at the same time.
Perhaps more surprising is that this online chatter has continued even as this story has changed from an analysis of a video of killings in Iraq - worthy or not of the label "Collateral Murder" - to the potential prosecution of a soldier on serious charges.
In addition to Mr. Lamo's multipronged online strategy, there is Wikileaks, which used its Twitter feed to comment on reports that Specialist Manning had been arrested. The usual face of Wikileaks, Julian Assange, largely disappeared from public view from early June until recently.
That feed stayed silent on the question on everyone's mind - did he or didn't he? After all, if Wikileaks cleared Specialist Manning, it would be undercutting its central claim: that those who give it information are ensured that they will remain anonymous.
Instead, Wikileaks used Twitter to attack the reporting on the story.
Initially, it accused the reporter who broke the story for Wired News, Kevin Poulsen, of having a "notorious" connection with Mr. Lamo and expressed its anger with him.
It also mentioned that Mr. Poulsen was convicted for hacking, as was Mr. Lamo - in Mr. Lamo's case in 2004 when he pleaded guilty to hacking into the internal computer system of The New York Times. The two have a reporting history that extends more than a decade. And on Wikipedia of all places, there is a photo of Mr. Poulsen, Mr. Lamo and Kevin Mitnick, a well-known ex-hacker, smiling together.
Naturally, Mr. Poulsen used Twitter to respond "Woah. Wikileaks is calling me an informer and manipulator. (They call me a felon, too, but that part's true)." But later his tone turned less jocular: "Sometimes Wikileaks seems more like Nixon than Ellsberg."
In an interview, Mr. Poulsen said he had no relationship with Mr. Lamo other than reporter/subject, and that he had been a hacker but stopped long ago. "When I was hacking, Adrian was barely out of diapers," he said.
Mr. Poulsen said he wondered what Wikileaks would have had him do - keep secret that a soldier was being held on accusations that he had leaked? The arrest is what made the story news, Mr. Poulsen said, adding that "myself and Wired in general are not in the business of printing other journalists' sources." When pressed, he conceded that he considered Wikileaks to be "a journalistic organization."
The Wikileaks accusations against Wired caught the eye of Glenn Greenwald, a former constitutional lawyer who now blogs at Salon. In his blog, Mr. Greenwald analyzed the accusations and, as is his style, showed all his work - including e-mail correspondence with Mr. Poulsen and a telephone interview with Mr. Lamo.
Ultimately, Mr. Greenwald concluded, in his headline, that the case was "strange and consequential." After reading the thousands of words Mr. Greenwald published on the case, what happened - how Mr. Lamo came to know Specialist Manning, among other things - was still not clear.
Mr. Greenwald ended by saying that because of the importance of Wikileaks' function as a check on "powerful factions and imposing transparency," the topic "merits substantial scrutiny, along with genuine skepticism to understand what happened."
And though the online proliferation of comments about the Manning case can be overwhelming, Mr. Greenwald said he preferred this condition to the opposite: "On the whole, it is extremely healthy because it makes things a lot more transparent."
Ever in search of the last word, Mr. Lamo last Monday posted a note on the Wikipedia article about the Manning case, saying it was biased. The note was quickly taken down, and Mr. Lamo dropped the subject.
Representatives of the Army were contacted by e-mail and asked to comment on the arrest of Specialist Manning, but did not reply.
At the same time that the case has been exhaustively examined online, few traditional, that is, offline, outlets have taken up the Manning prosecution as a test of First Amendment principles, a challenge to the free flow of information needed by the public trying to evaluate the conduct of the war in Iraq. "This is an incredible instance of something that happens online, happens via the online transfer of information, and maybe it never got offline," said Lisa Lynch, an assistant professor of journalism at Concordia University in Montreal, who has been studying Wikileaks almost since its creation in 2006. "Maybe it got contained there." [NYTimes/28June2010]
U.S. Arrests 10 For Allegedly Spying for Russia. U.S. authorities said on Monday they have broken up a spy ring that carried out deep-cover work in the United States to recruit political sources and gather information for the Russian government.
Authorities charged 11 individuals with the plot, 10 of whom were arrested on Sunday in Boston, New York, New Jersey and Virginia on charges including conspiracy to act as unlawful agents of the Russian Federation and money laundering.
The group, dubbed the "Illegals," was accused of being tasked by the Russian intelligence agency SVR to enter the United States, assume false identities and become "deep-cover" Americans, according to the U.S. Justice Department.
Their goal was to "become sufficiently 'Americanized' such that they could gather information about the United States for Russia and can successfully recruit sources who are in, or are able to infiltrate, United States policy-making circles," according to criminal complaints filed in U.S. federal court.
However, they were not assigned to collect classified, secret information, a Justice Department official said. Most are believed to be originally from Russia and trained to secretly infiltrate the United States.
News of the bust comes just days after President Barack Obama met with Russian Dmitry Medvedev to continue repairing a relationship between the two nations that has been fractured over diverging foreign policies and business matters.
An attempt to reach a representative at the Russian embassy in Washington was not immediately successful. U.S. law bars individuals from acting on behalf of foreign states without notifying the U.S. government.
Almost like reading straight from a spy novel, the criminal complaints said the individuals in the "Illegals" program received extensive training in coded communications, how to make brush passes and how to evade detection.
One was accused of sending back information about leadership changes at the Central Intelligence Agency.
The arrests are the culmination of a multi-year investigation that used extensive surveillance of communications and wiretaps, including putting listening devices into the homes of the accused individuals.
Those charged include: Christopher Metsos, Richard Murphy, Cynthia Murphy, Donald Heathfield, Tracey Lee Ann Foley, Michael Zottoli, Patricia Mills, Juan Lazaro, Vicky Pelaez, Anna Chapman and Mikhail Semenko. All but Metsos were arrested on Sunday.
The FBI decrypted a coded message in 2009 sent to two of the individuals accused of being part of the ring. The message instructed them to "search and develop ties in policymaking circles in US and send intels" back to Moscow, according to court papers.
The individuals were accused of collecting information ranging from research programs on small yield, high penetration nuclear warheads and the global gold market to trying to obtain background information about people who applied for jobs at the Central Intelligence Agency, according to court papers.
One of the individuals charged, Metsos, who is still at large, was accused of receiving and doling out money to the group, including getting payments during a brush-pass with a Russian government official who was affiliated with the Russian Mission to the United Nations in New York, according to the Justice Department.
Metsos also buried some money in rural New York that was later recovered about two years later by two others in the group who had traveled from Seattle.
Nine of the individuals were accused of conspiracy to commit money laundering related to their activities.
In another instance, one defendant was accused of receiving $80,000 for some of the group from a representative of the Russian government while in an unnamed South American country, according the criminal complaints.
While some of the activities dated back to 2000, one of the complaints said that undercover FBI agents met two of the accused individuals on Saturday, Mikhail Semenko and Anna Chapman. She had apparently been planning to go to Moscow in two weeks, according to one of the criminal complaints.
[Pelofsky/Reuters/28June2010]
Section
II -
CONTEXT & PRECEDENCE
Saddam's Spy Files: Keys To Healing Or More Hurting? Seven years after the fall of Saddam Hussein's regime, Iraq is still trying to win the return of voluminous records and archives compiled for Saddam's Baath Party, many of which are currently being held in the U.S.
Some Iraqis say those millions of documents hold the key to national reconciliation, but others warn that Iraq may not be ready to unlock these secrets of betrayal and brutality.
Riyad al-Rubaiee, a 46-year-old Iraqi, still has a vivid memory from 2003. As the Iraqi government vanished amid the U.S.-led invasion, people scrambled to loot the files of Saddam's secret police from various offices tucked around Baghdad. In one, he came across a man standing amid the chaos, a file in one hand and tears streaming down his face.
"He just kept sobbing, 'Is it possible? Is it possible?' He was holding the file of his brother, a member of the Communist Party who was arrested in 1979. And he'd just learned that the people who had informed on his brother, the people who got him executed, were his own cousin and brother-in-law," Rubaiee says.
Growing up in a tough neighborhood of Sadr City, Rubaiee thought of himself as an Iraqi and a Muslim and a supporter of Saddam Hussein.
But after fighting for his country in the war against Iran in the 1980s, Rubaiee returned home to find Saddam had jailed, tortured and killed many Iraqis at home.
He took part in one anti-Saddam demonstration, and he and his friends would gather at night and talk about what they would like to do to the ruling Baathists if they ever got the chance.
Under the rule of Saddam Hussein, Iraqis were spied on by neighbors, work colleagues, students. Some Iraqis say the nation is not ready to handle the release of records from that era; others say they are the key to national reconciliation.
Then, without warning, the secret police raids began. His friends were arrested and he only just escaped with his uncle. Years later, he realized how the regime had ferreted out his barely formed political views: A prominent Baathist had been using his sisters to glean information from the women and children in the neighborhood.
"They'd go to a wedding and chat with all the women, the same for funerals. You might see them by the front gate all day, watching who goes where and who's talking with whom," Rubaiee says.
Much of the paper trail from Saddam's decades of spying was badly damaged in the post-invasion looting, and millions of documents were spirited away to the U.S., where they remain. A slender, soft-spoken Iraqi named Saad Eskander is trying to change that.
Eskander is the director of the Iraqi National Library and Archives, an aging facility soon to be replaced by a new, modern building being constructed next door. He has a young staff of restorers, trained in the latest conservation techniques from Europe. They are painstakingly freezing, drying and restoring documents. The archives also are being digitized and made available on the Internet.
Eskander's quiet librarian's demeanor hides a fierce belief in the power of information - to imprison a society or free it.
"From a closed society to an open society, that is our slogan," he says. Eskander says not only the Baath Party, but all extremists - from the left and the right - are unhappy about what he calls "the democratization of information."
Eskander says it's crucial to retrieve the spy files as soon as possible because it will take years for Iraq to recover from the effects of a spying operation of staggering perversion and brutality.
"You are spied on by your neighbors, by your work colleagues, by your fellow students at university; every Iraqi was spied on - even those who were part of the regime and had close links to the regime - so the leaders of the regime lived in permanent paranoia," he says.
Perhaps understandably, Eskander says there has never been a dictatorship like Saddam's. But other countries might dispute that. The Oscar-winning 2007 film The Lives Of Others explored the institutionalized spying of the East German Stasi. In one scene, the main character, a famous East German playwright, sits in a research room after the fall of the Berlin Wall, leafing through his own surveillance files.
As he turns the pages, the playwright comes to see himself not as a human being but as a case, code-named "Laszlo," and there is pain but not surprise in his face as he reads how his lover, before she committed suicide, was forced repeatedly to betray him.
Critics say The Lives Of Others is a compelling glimpse into the way a repressive spying apparatus over time eats away at the social fabric holding a community together.
Eskander says this is what happened to Iraq. Yes, he says, it was naive of America to believe its soldiers would be welcomed by Iraqis instantly ready to build a democratic society - and the reasons why are buried in the spy files.
"So the collapse of the regime, it was not a political collapse, it was a social collapse as well. The invasion just opened the gates for all the bad phenomena that took root under Saddam Hussein," Eskander says.
There is considerable debate, both inside and outside of Iraq, about what to do with the spy archives. Many were collected by the Iraq Memory Foundation, a U.S.-funded project dedicated to helping Iraqis come to terms with the atrocities committed under Saddam. The foundation turned the files over to the Hoover Institution at Stanford University to be digitized.
The U.S. government, which under President George W. Bush initially took a keen interest in the Baath Party files, is now adopting a hands-off approach.
"This should be the subject of discussion between Hoover and the Iraqi Memory Foundation and the Iraqi government," says Phillip Frayne, a spokesman for the U.S. Embassy in Baghdad. "In other words, they are in the custody of the Hoover Institution right now, not in the custody of the U.S. government."
But what would it mean for a still-struggling Iraqi society if the secret police files were suddenly revealed? For the Iraq Memory Foundation says those files can be a powerful tool for reconciliation and healing - if they are handled properly.
In a 2005 interview with NPR, Hassan Mneimneh, one of the foundation's directors, said other countries have taken a variety of approaches, some of which it views as extreme, such as South Africa's Truth and Reconciliation Commission.
"This is an extreme model where basically victim and perpetrator face each other. Another extreme model, far closer to Iraq, is the Lebanese model. A traumatic civil war ends, a page is turned as if nothing has actually happened - this is a model almost of denial," Mneimneh told NPR.
"Between these two extremes, we believe Iraqi society is going to try to find its level of comfort and our role is clearly to advocate for one that is more towards openness," he said.
But victims of Saddam's spying regime such as Rubaiee have a very different view. When asked whatever happened to the Baathist who used spy on Rubaiee's neighborhood, he calmly slides a finger across his throat. He says this is not Germany, and Iraq isn't ready to have decades of betrayal revealed all at once.
"For us Iraqis, our tribal nature is still prevailing, our democracy is too new. There would be killing in the streets," he says.
Given the issues of preservation and politics still to be worked through, Iraqis are likely to have quite a bit of time before they know if and when the spy files will return. Then Eskander may find out if the information Saddam used to wound a nation can also help to heal it.
[Kenyon/NPR/23June2010]
Not So Secret: Deal at the Heart of UK-US Intelligence. The terms of a secret agreement that became the core of the special relationship between Britain and the US have been released, more than 60 years after the deal was signed by senior military officials.
A six-page "British-US Communication Intelligence Agreement", known as BRUSA, later UKUSA, tied the two countries into a worldwide network of listening posts run by GCHQ, Britain's biggest spying organization, and its US equivalent, the National Security Agency.
Though its existence has long been known, the agreement, negotiated in London in March 1946, is only now being published, and for the first time officially acknowledged, after freedom of information requests in Britain and the US. Under the agreement, the countries agreed to exchange the knowledge from operations involving intercepting, decoding and translating foreign communications, including the "acquisition of communication documents and equipment". In a passage which ensured that GCHQ's activities remained wrapped in official secrecy, the agreement states: "It will be contrary to this agreement to reveal its existence to any third party whatever."
Documents are available free for a month, at www.nationalarchives.gov.uk/ukusa and include amendments and annexes to the agreement. One, dated 1948, states: "The value of Communication Intelligence in war and peace cannot be over-estimated; conservation of the source is of special importance." It adds: "The time limit for the safeguarding of Communication Intelligence never expires."
The documents emphasize the importance of individuals with access to this information - now know as "sigint", short for signals intelligence - to be indoctrinated about its sensitivity and the need for it to be protected. No one who knew about these intelligence gathering methods "shall be committed to a hazardous undertaking which might subject him to capture by the enemy or third party", one document says.
GCHQ's cover was blown by Time Out in 1976, but it was only officially "avowed" in 1982 when Geoffrey Prime, a former linguist at GCHQ, was jailed for 38 years for passing secrets to the Russians over a 14-year period. He was released in 2001.
Many documents have been weeded out of the GCHQ files to be released today. They include an appendix on the "designation of intercept targets" and another on "collaboration in the field". Also missing is a document titled: "Arrangements for emergency location of Comint (Communication Intelligence) units".
A GCHQ spokesman said last night: "The 1946 UKUSA agreement formed the basis for co-operation between the two countries throughout the cold war and continues to be essential in keeping the UK safe from today's threats."
Ed Hampshire, a senior records specialist at the National Archives, said: "The agreement represented a crucial moment in the development of the 'special relationship' between the two wartime allies and captured the spirit and practice of the signals intelligence co-operation which had evolved on an ad-hoc basis during the second world war."
He added: "As the threat posed by Nazi Germany was replaced by a new one in the east, the agreement formed the basis for intelligence co-operation during the cold war. The two nations linked by common bonds of history, culture and language agreed not to collect intelligence against each other or to tell any 'third party' about the existence of the agreement."
The UKUSA agreement was later extended to include Canada in 1948, and Australia and New Zealand in 1956. According to the intelligence historian, Richard Aldrich, the British tried to use the Commonwealth as an "equalizer", summoning the Canadians and the Australians to a London signals intelligence summit before meeting the Americans, Shortly afterwards, Stewart Menzies, the head of MI6, met an American team led by Joseph Wenger at Bryanston Square in London to work on a bilateral deal. "When negotiations became sticky, Menzies whisked everyone off to White's Club for a bibulous lunch and suitably refreshed they resolved their differences", says Aldrich.
The agreement was signed on 5 March 1946 by Colonel Patrick Marr-Johnson on behalf of the UK's London Signals Intelligence Board and Lieutenant General Hoyt Vandenberg for the US State-Army-Navy Communication Intelligence Board.
The US was reluctant to include Commonwealth countries as equals and on occasions blocked intelligence sharing with them. The 1946 agreement states the exchange of intelligence would not be "prejudicial to national interests".
But, despite occasional rows, the eavesdropping network, sometimes referred to as Echelon, has expanded. Norway joined in 1952, Denmark in 1954, and Germany in 1955. Italy, Turkey, the Philippines and Ireland are also members. Documents released today contain thousands of intercepts from the Soviet Union but stop at 1949, as does the first official history of MI6, to be published in the autumn. Though GCHQ employs about 5,500 staff, significantly more than MI5 or MI6, its budget also remains a secret.
Then sensitivity surrounding GCHQ operations is further reflected in its strong opposition to the product of intercepts being used as evidence in court trials, a ban which critics say would obviate the need for control orders and secret hearings but one which GCHQ argues is needed to protect the capabilities of its technology.
GCHQ, the government's communications headquarters, is based in Cheltenham and grew out of wartime Bletchley Park where mathematicians, scientists and linguists broke the German Enigma codes.
[Guardian/25June2010]
Crime History - Ellsberg Surrenders in Pentagon Papers Leak. On this day, June 28, in 1971, Daniel Ellsberg surrendered to the U.S. government to face charges for leaking the Pentagon Papers.
Two weeks earlier, the New York Times began publishing excerpts of the top secret history of the U.S. involvement in Vietnam that showed that the American people had been deceived about the war.
The White House got an injunction to stop further publication of the papers, but the U.S. Supreme Court quickly ruled in favor of the press.
Ellsberg was charged with espionage, theft and conspiracy. But the charges were dropped during his trial after it was revealed that the Nixon administration had conducted a campaign to discredit Ellsberg, illegally wiretapped his phone and broke into his psychiatrist's office.
[McCabe/TheExaminer/28June2010]
Section
III - COMMENTARY
The Future of Government Secrecy, by Maxwell Abbott. WikiLeaks, the Swedish website that publishes sensitive government and corporate information while preserving the anonymity of its sources, has come under serious criticism in recent days. Last week, authorities arrested Bradley Manning, a former Army intelligence analyst suspected of supplying WikiLeaks with 260,000 secret cables between U.S. diplomats and their contacts around the world. In addition, Mr. Manning is suspected of leaking footage of a U.S. helicopter gunning down a crowd of men in Iraq that included two journalists from Reuters. Most commentators find that WikiLeaks will drastically alter the government's ability to protect classified information. Whether or not that is a good thing is a more divisive question.
The Wall Street Journal finds that the existence of WikiLeaks and other outlets for classified information is something we must "learn to live with" that will make us "less safe." The Weekly Standard objects to WikiLeaks because informing the public necessarily leads to informing "our mortal adversaries." The Weekly Standard contrasted the present situation and the Supreme Court case of New York Times Co. v. United States, in which the court permitted the publication of the infamous Pentagon Papers, a 7,000-page history of America's involvement in Viet Nam. Because the Pentagon Papers were a historical narrative that referred to events at least three years old, the Standard argues that it was appropriate for them to be released. In contrast, the video and diplomatic cables supplied by Mr. Manning should not be released because "intelligence sources and methods are likely to be revealed" and "American soldiers and intelligence agents may die."
The Weekly Standard is, in fact, echoing the same draconian arguments made by the United States during the Pentagon Papers case. In 1971, Michael Hess, chief of the Civil Division of the United States Attorneys Office, argued that "serious injuries are being inflicted on our foreign relations, to the benefit of other nations opposed to our foreign relations, to the benefit of other nations opposed to our form of government." The U.S. Supreme Court rebuffed the government's arguments, stating "security is a broad, vague generality whose contours should not be invoked to abrogate the fundamental law embodied in the First Amendment." Instead, "the press must be left free to publish news, whatever, the source, without censorship, injunctions or prior restraints." In an era where the mainstream media is struggling to find the resources to carry out investigative work, WikiLeaks is filling the critically important role played by the New York Times 40 years ago. In addition, the video depicting the murder of the Reuters journalists is, like the Pentagon Papers at the time of their publication, over three years old. For three years, Reuters has been demanding to know what happened to its journalists. Thanks to WikiLeaks, Reuters now knows the answer and the public is better off for it.
[PRWatch/23June2010]
Does Uncle Sam Really Need 1,100 Data Centers? by Jon Stokes. Earlier this year, the White House announced an initiative to shrink the federal government's overall real estate footprint as a way to shave $3 billion off the federal budget. The initiative covers government-owned facilities of all sorts, including - or, perhaps, especially - Uncle Sam's 1,100 data centers.
The announcement of a Federal Data Center Consolidation Initiative (DCCI) was music to the IT industry's ears, and storage giant NetApp immediately commissioned a study to gauge the program's prospects for success.
What NetApp found, probably to its dismay, is that while most federal IT professionals agree that more data center sharing among agencies is a good idea (76 percent), far fewer believe that it's feasible for their particular agency to share resources with another (49 percent). It's also the case that everyone knows that the other agencies don't want to give up their own data centers, with 86 percent of the survey's correspondents citing government culture as the number one obstacle to consolidation. In spite of the culture factor, 63 percent of those surveyed were confident that consolidation would happen eventually, but most (74 percent) were in agreement that the White House's timetable is unrealistic.
The official number of government data centers owned by the federal government - 1,100 - is surprisingly large. This number is, however, a bit misleading. For most IT professionals, the word "data center" conjures images of a large, dedicated facility with racks upon racks of servers, and special cooling and backup power capabilities. But that's not quite how the government defines the word, according to this FAQ [doc]:
"For the purpose of the Federal Data Center Consolidation Initiative (DCCI) any room that is devoted to data processing servers, i.e., including server closets (typically < 200 sq. ft.) and server rooms (typically < 500 sq.ft.) within a conventional building is considered a Data Center, just like larger floor spaces or entire buildings dedicated to housing servers, storage devices, and network equipment.
Clearly, the DCCI is about more than reducing the number of actual data center facilities that the federal government uses - that number is likely to be small already. Rather, the initiative is about cleaning out the myriad server closets and server rooms that are tucked away throughout the government, and moving that storage and compute functionality off-site to a shared facility.
Probably the best way for the government to do this is to build a new set of dedicated facilities using the latest and greatest best practices, then just shut down the old facilities. If this report on the original DCCI launch is correct, that indeed seems to be part of the plan. The article names northern Virginia as a likely site for a new data center build-out.
While the government is contemplating shared facilities, maybe they could convince the NSA to share some of the $1.8 billion-dollar data center that the taxpayers are building in Utah. This one government data center, which is (as near as I could tell from reading the docs back in July of last year) exclusively for the NSA to use in its snooping operations. Note that the agency's private data center, one of a number that it operates, costs two-thirds of what the DCCI is supposed to save the government over the next few years.
One option that does not appear to be under serious consideration is more extensive use of public clouds, like those operated by Amazon, Google, and Microsoft. Judging by the NetApp survey, the usual concerns about security and privacy apply. This is a shame, because there's a case to be made - and Accenture's Joe Tobolski made it in a part of this interview that I didn't transcribe - that public clouds are likely to be more secure and stable than private ones.
The reason is that lots and lots of users bang on public cloud infrastructure, and the admins see plenty of hostile activity. So for the same reason that open-source code can be less buggy, public clouds have been through the fire and can be relied on. Or so the argument goes.
It's also the case that the public nature of popular cloud platforms is a huge part of their economic value. What I mean is this: when an employee needs to bring up a new server for a small task, she no longer has to submit a request to IT for either hardware or a VM, then wait for that request to go through an approval and possible hardware procurement process; instead she can just spin up a new EC2 instance with a small charge to her company credit card. The latter approach is cheaper, faster, and more productive.
If the government is about to build a new set of private clouds to replace aging data centers and server rooms, it'll be missing out on a big part of the cost and flexibility advantage of cloud computing.
[Stokes/Arstechnica/25June2010]
A Winnable War, by Frederick W. Kagan and Kimberly
Kagan. Success in Afghanistan is possible. The policy that President Obama announced in December and firmly reiterated last week is sound. So is the strategy that General Stanley McChrystal devised last summer and has been implementing this year. There have been setbacks and disappointments during this campaign, and adjustments will likely be necessary. These are inescapable in war. Success is not by any means inevitable. Enemies adapt and spoilers spoil. But both panic and despair are premature. The coalition has made significant military progress against the Taliban, and will make more progress as the last surge forces arrive in August. Although military progress is insufficient by itself to resolve the conflict, it is a vital precondition. As the New York Times editors recently noted, "Until the insurgents are genuinely bloodied, they will keep insisting on a full restoration of their repressive power." General David Petraeus knows how to bloody insurgents - and he also knows how to support and encourage political development and conflict resolution. He takes over the mission with the renewed support of the White House.
Neither the recent setbacks nor the manner of McChrystal's departure should be allowed to obscure the enormous progress he has made in setting conditions for successful campaigns over the next two years. The internal, structural changes he made have revolutionized the ability of the International Security Assistance Force (ISAF) to conduct counterinsurgency operations. He oversaw the establishment of a three-star NATO training command that has accelerated both the expansion and the qualitative improvement of the Afghan National Security Forces in less than a year. He introduced a program of partnering ISAF units and headquarters with Afghan forces that had worked wonders in Iraq - and he improved on it. He oversaw the introduction of a three-star operational headquarters to develop and coordinate countrywide campaign plans. He has managed the massive planning and logistical burden of receiving the influx of surge forces and putting them immediately to use in a country with little infrastructure.
While undertaking these enormous tasks of internal reorganization, he has also taken the fight to the enemy. The controversies about his restrictions on the operations of Special Forces and rules of engagement that limit the use of destructive force in inhabited areas have obscured the fact that both Special Forces and conventional forces have been fighting harder than ever before and disrupting and seriously damaging enemy networks and strongholds. Targeted operations against Taliban networks have increased significantly during McChrystal's tenure, and the Taliban's ability to operate comfortably in Afghanistan has been greatly reduced. ISAF forces have killed, captured, or driven off numerous Taliban shadow governors and military commanders. They have pushed into areas the Taliban had controlled and eliminated safe-havens.
The story of Marjah is particularly illustrative. Before this year, Marjah was a Taliban sanctuary, command-and-control node, and staging area. Taliban fighters based there had been able to support operations against ISAF and coalition forces throughout Helmand Province. Lasting progress in Helmand was simply not possible without clearing Marjah. McChrystal cleared it. The Taliban naturally are trying to regain control of it. ISAF and the ANSF are trying to prevent them.
The attempt to import "governance" rapidly into the area is faltering, which is not surprising considering the haste with which the operation was conducted (driven at least partly by the perceived pressure of the president's July 2011 timeline). The attempt was also ill-conceived. Governance plans for Marjah emphasized extending the influence of the central government to an area that supported insurgents precisely because it saw the central government as threatening and predatory. Although ISAF persuaded President Hamid Karzai to remove the most notorious malign actor in the area from power, Karzai allowed him to remain in the background, stoking fears among the people that he would inevitably return. The incapacity of the Afghan government to deliver either justice or basic services to its people naturally led to disappointment as well, partly because ISAF's own rhetoric had raised expectations to unrealistic levels.
The biggest problem with the Marjah operation, however, is that it was justified and explained on the wrong basis. Marjah is not a vitally important area in principle, even in Helmand. It is important because of its role as a Taliban base camp. It was so thoroughly controlled by the insurgents that the prospects for the rapid reestablishment of governance were always dim. It was fundamentally a military objective rather than a political one, and McChrystal made a mistake by offering Marjah as a test case of ISAF's ability to improve Afghan governance. What matters about Marjah is that the enemy can no longer use it as a sanctuary and headquarters. ISAF's military success there has allowed the coalition to launch subsequent operations in the Upper Helmand River Valley, particularly the more strategically important contested area around Sangin. The Marjah operation has so far succeeded in what it should have been intended to do. The aspects that are faltering should not have been priorities in that location.
Kandahar differs from Marjah in almost all respects. Kandahar City is not now a Taliban stronghold, although the Taliban are present in some force in its western districts and can stage attacks throughout the city. The Taliban had controlled the vital neighboring district of Arghandab until newly arrived American forces began contesting it in September 2009. The insurgents remain very strong in Zhari, Panjwayi, and Maiwand Districts to the west and south of Kandahar City, but they do not control any of those areas as completely as they controlled Marjah.
An even greater difference is that Kandahar City and the surrounding districts are strategically important terrain. It is much too strong to say "as Kandahar goes, so goes Afghanistan" - the coalition could succeed in Kandahar and still lose the war. But it is very hard to imagine winning the war without winning in Kandahar. It is the most populous city in Afghanistan's Pashtun belt, the historical base of the Pashtun dynasties that formed and ruled Afghanistan for most of the last 250 years, and the birthplace of the Taliban itself, as well as the home of the Karzai family. It is also geographically important as the major city at the southwestern tip of the Hindu Kush and the junction of the roads from Herat, Kabul, and Quetta (in Pakistan). For all of these reasons, enduring stability in Kandahar underwritten by acceptable and effective governance is an essential precondition for success in Afghanistan in a way that stability in Marjah simply is not.
The Marjah operation nevertheless offers important lessons about how to approach Kandahar. McChrystal had already rightly abandoned the idea of parachuting government officials into cleared areas around Kandahar before his departure. He was focusing instead on trying to get the government officials already in place to build local support for the operation. That effort, manifested by several jirgas and shuras (gatherings of officials and elders) over the past few months, has been faltering. McChrystal had recognized the problem before his departure, which is one reason he had announced a delay in the planned clearing operations around Kandahar. Petraeus now has the opportunity to revisit this approach to building local support for the operation and correct it.
It is too soon to say which of the various alternative approaches Petraeus will adopt or whether it will succeed. Learning, adapting, and trying different approaches are not the same as failing or losing. On the contrary, these are an essential part of success. American forces in Iraq experimented with a variety of approaches over years throughout the country before hitting on the right set of solutions. Under McChrystal's command, ISAF was moving through similar phases in Afghanistan much more rapidly. Since Petraeus has already shown his ability to explore alternatives until he finds one that works, there is reason to have some confidence that he will do so in Kandahar and in Afghanistan more generally.
Recent news reports have exposed what those who know Kandahar have long understood - that the predominance of Ahmad Wali Karzai, the president's half-brother, alienates a significant portion of the population and is itself a major driver of instability and insurgency. Excellent reporting by Dexter Filkins of the New York Times and others has revealed the degree to which U.S. and ISAF contracting practices have reinforced this predominance and thus contributed to the problem. Does Ahmad Wali's kinship with the president make this problem intractable - thus rendering the entire effort hopeless? Here the example of Iraq may be illuminating.
Between 2003 and 2005 it appeared that the largest problem in Iraq was the Sunni insurgency and the al Qaeda organization with which it interacted symbiotically. In 2006 it became apparent that the problem was larger than that. Shiite militias had been systematically cleansing Baghdad and other mixed areas of their Sunni populations, fueling the insurgency and deepening the hold of al Qaeda, which seemed to offer the Sunni communities under assault their most reliable protection. Individuals within the Iraqi government actively supported the Shiite militias. The deputy health minister allowed them to use ambulances to drive death squads around Baghdad. The Iraqi National Police were badly infiltrated and committed horrendous atrocities at the orders of officials within the government. The minister of finance had brought into the National Police the infamous Wolf Brigade of the Badr Corps that set the standard for sectarian brutality. Prime Minister Nuri al Maliki tolerated this behavior and protected some of those who were engaged in it.
Maliki is still prime minister (for now). The sectarian deputy health minister (who escaped trial by intimidating the judges) has been elected to the new parliament. The Badr Corps finance minister remained in position, as did many others engaged in sectarian activities that were fuelling the insurgencies. But the Shiite death squads have stopped cleansing. The National Police are now welcomed in Sunni districts they once terrorized. Maliki himself led military operations against the strongholds of the most dangerous Shiite militias, in Basra and Sadr City, in 2008. Some of the worst offenders were removed from power, but many were not. What is both remarkable and promising is that even those who remained were persuaded to stop engaging in the activities that were driving Iraq toward unlimited sectarian civil war by the end of 2006. The cessation of malign behaviors can be as important as the removal of malign actors, in Afghanistan as well as in Iraq.
Iraqi sectarian actors did not suddenly see the light and embrace diversity. They changed their behavior in response to a wide array of pressures brought on them and their patrons by the entire American team, from General Petraeus and Ambassador Ryan Crocker down to soldiers in the streets. Petraeus and Crocker in particular adopted a highly nuanced approach to the problem. When they had strong information (not necessarily legal evidence) that particular leaders were behaving badly, they confronted the prime minister with that information as a policy matter rather than a legal one. Lower level commanders did the same thing with their counterparts within the Iraqi Security Forces. In some cases, American units simply partnered with misbehaving Iraqi units so closely that the Iraqis could not engage in malign behavior.
As these efforts were going on, Petraeus and Crocker inserted American forces into contested neighborhoods and effectively took control of the ground. Their presence changed the equation - local people reported on the misbehavior of Iraqi officials; American forces took notice and, when appropriate, took action. By simultaneously taking the fight into the safe-havens and strongholds of the Sunni insurgents and Al Qaeda in Iraq, U.S. forces reduced the capability of those terrorists and began to bring down the violence. As the overall level fell, Shiite militia violence, which had been to some extent concealed by the spectacular attacks of al Qaeda, became more prominent, reinforcing the pressure on malign Shiite actors to take a knee. The fact that American forces then remained in the neighborhoods for a couple of years permitted the emergence of a political process based on new calculations and facilitated the restoration of the most basic confidence among Sunnis that the government was not committed to their annihilation.
The problem in Afghanistan is similar. Power-brokers are not engaged so much in tribal cleansing or death squads, but they do use their own private security companies to enforce order, sometimes at the expense of marginalized groups who fuel the insurgency. Ahmad Wali Karzai is the most prominent example of such a powerbroker, but he is far from unique. A sound ISAF strategy would attempt to remove malign actors where necessary and possible, but also work to shape them and the environment in which they operate in ways that persuade or prevent them from engaging in the malign behavior that is fueling the insurgency and preventing stable governance from taking hold. Improving the way ISAF contracts with local companies - a process that has already begun - is part of the solution, but only part. ISAF will have to refocus its efforts at every level away from a binary choice between removing and empowering the malign actors, and toward the kind of nuanced approach that was successful in Iraq, appropriately modified.
There are never any guarantees in war. But the fact that efforts now will be led by General David Petraeus, with his record of judgment and creativity, is grounds for confidence that we can succeed. [F.Kagan&K.Kagan/WeeklyStandard/28June2010]
Section
IV - JOBS AND COMING
EVENTS
Jobs
Jacobs Technology Inc. - Director for Intelligence and Operations Support.
Title: Director for Intelligence and Operations Support
Company: Jacobs Technology Inc. - Unified and Special Operations Group
Location: Tampa, FL
www.usog.jacobs.com
Minimum Experience: Greater than 15 years experience as an Intelligence Officer/Sr NCO within Army/Joint Special Operations Community or CIA.
Responsible for the management of intelligence and operational services task orders/contracts supporting the Special Operations,
Defense and Federal Agencies throughout CONUS/OCONUS.
Contact: Bob Yuill 813-282-3500x207
Coming
Events
EVENTS
IN COMING
TWO MONTHS....
MANY Spy Museum
Events in August
with full details are listed on the AFIO Website at www.afio.com. The
titles for some of these are as follows:
- Wednesday, 7 July 2010; 6:30 pm - Washington, DC - "A
New Cold War: Inside Nuclear Iran" at the International Spy Museum
- Thursday, 15 July 2010; 12 noon – 1 pm - Washington, DC -
"Eyes in the Sky: Eisenhower, the CIA, and Cold War Aerial
Espionage"
at the International Spy Museum
- Thursday, 5 August 2010, noon - Washington, DC - "Silent Sentry:
The Untold Story of the National Security Agency" - at the
International
Spy Museum
- Wednesday, 11 August 2010, 6:30 pm - Washington, DC - "Uneasy
Alliance: The CIA and ISI in Pakistan" - at the International Spy
Museum
9, 16, 23 July 2010, 8 and 10 pm - Washington, DC - THE SPY MAGIC SHOW - An incredible exploration into the secrets of spies, shown through stunning sleight-of-hand magic by master magician Michael Gutenplan.
Michael Gutenplan, an expert in sleight-of-hand magic is about to expose the secrets of the CIA and you are invited to watch! In an intimate room at the famed Ritz Carlton Hotel in Washington, D.C., Michael will perform world-class magical effects and tell how magicians and the CIA have worked together since its creation in 1947. Using cards, money and mind reading Michael will expose the secrets and skills that have only been rumored to exist. From thought transference and teleportation to lie detection and invisible ink, Michael will transport you to another world where fact and legend go hand- in-hand and spies are around every corner. Grab a drink, have a seat and join us for this once in a lifetime event!
Tickets can be purchased through www.spymagicshow.com or by calling 1-866-811-4111. All tickets are $40.00.
The Spy Magic Show plays Friday, July 9, 16 and 23rd at 8:00 PM and 10:00 in the Roosevelt Room at the Ritz Carlton, located at 1150 22nd Street, N.W., Washington, D.C. 20037
Michael Gutenplan is a professional magician originally from New York and now residing in Los Angeles. He has performed his signature brand of magic around the world including in Great Britain, Spain, Israel, Jordan and across the United States. He was the creator and star of Extraordinary Deceptions, an Off-Broadway magic show that earned Michael rave reviews in the New York Times, Variety and other prestigious publications.
10
July 2010, 1000 - 1430 - Salem, MA - The AFIO New England Chapter
meets
to conduct business and hear Douglas Wheeler on "Writing a History of
Spying" and John Behling, Jr. on "Origins of Islamic Extremism."
Our afternoon speaker will be Chapter Member John Behling Jr . John is a veteran of the OSS. He will speak on "Origins of Islamic
Extremism" The morning speaker is Douglas L. Wheeler,
who will discuss 'Writing a History of Spying-author's dilemma?',
Doug
is Professor Emeritus at the University of New Hampshire where he
taught
African, Iberian & European, World and Intelligence Studies
History
at the University of New Hampshire, 1965-2002 and since then has
taught
there part-time. Schedule: Registration & gathering, 1000 - 1130,
membership meeting 1130 - 1200. Luncheon at 1200 followed by our
speaker, with adjournment at 2:30PM.
Location: the Salem Waterfront Hotel located in Salem MA. The hotel
website is: http://www.salemwaterfronthotel.com/.
For directions to the hotel look here: http://www.salemwaterfronthotel.com/location.html Information about Salem MA and local hotels can be found here: http://salem.org/
Note, as this meeting is a one day event we have not made any hotel
arrangements. For additional information contact us at afionechapter@gmail.com
Advance reservations are $25.00, $30.00 at the door - per person.
Luncheon reservations must be made by 1 July 2010. Mail your check
and
the reservation form to:
Mr. Arthur Hulnick, 216 Summit Avenue # E102, Brookline, MA 02446,
617-739-7074 or hlnk@aol.com
Thursday,
15 July 2010, 11:30 am - Colorado Springs, CO - The Rocky Mountain
Chapter hears Tim Murphy on R&D Platform Usage in Intelligence.
The Chapter presents an expert on Special Ops whose firm is doing an
R&D intelligence platform for the Intelligence community. Retired
Air Force Col. Timothy Murphy, High Altitude Balloon Surveillance, Vice President, Star Tower Division, Global Near Space Services (GNSS), who is also a graduate of the Air Force
Academy. To be held at a new location the AFA Eisenhower Golf Course
Club House. Please RSVP to Tom VanWormer at robsmom@pcisys.net.
Wednesday, 21 July 2010, 10 am - 12:45 pm - Annapolis
Junction, MD - "The Mysterious Rosetta Stone: A Code-Cracking
International Treasure" with Dr. Joel Freeman, is topic at the
National
Cryptologic Museum Foundation Summer Cryptologic meeting.
All AFIO members are invited to hear our guest speaker, Dr.
Joel Freeman, CEO and President of the Freeman Institute,
discuss the history of the Rosetta Stone, focusing on the historical
connection between the Rosetta Stone and the breaking of codes.
Guests
will have an opportunity to view the full-sized, three-dimensional
Rosetta Stone replica normally on display in the lobby of the National
Cryptologic Museum. Dr. Freeman is an gifted speaker and author. As
part
of the program there will be a brief presentation to acknowledge the
Milt Zaslow Memorial Award for Cryptology that was presented for the
first time at this year's Maryland History Day Ceremony on 24 April.
Location: the L3 Conference Center in the National Business Park.
Lunch will be served at 11:45 following the presentation. L3
Conference
Center is located at 2720 Technology Dr, Annapolis Junction, MD 21076
in
the Rt. 32 National Business Park.
Cost: the fee is $25 to cover program & lunch costs.
Confirm your attendance by Wednesday, 14 July, by calling (301)
688-5436
to pay by credit card or by mailing a check to NCMF, POB 1682, Ft.
Meade, MD 20755. We look forward to seeing you there.
22
July 2010 – San Francisco, CA – The AFIO Jim Quesada Chapter hosts
John
Yoo, former deputy assistant attorney general in the Office of Legal
Counsel of the U.S. Department of Justice, where he worked on national
security and terrorism after the September 11 attacks.
John Yoo is currently a professor of law at UC Berkeley. Yoo will
be discussing his new book, Crisis and Command: A History of Executive
Power from George Washington to George W. Bush. RSVP and pre-payment
required. The meeting will be held in San Francisco: 11:30 AM no host
cocktails; noon - luncheon. $25 member rate with advance reservation
and
payment; $35 non-member. E-mail RSVP to Mariko Kawaguchi (please
indicate chicken or fish): afiosf@aol.com and mail check made out to
"AFIO" to: Mariko Kawaguchi, P.O. Box 117578 Burlingame, CA 94011
24 July 2010 - Abilene, KS - Korea 60: Eisenhower the Peacemaker - Honoring Those who Served in Korea - CIA joint conference at Dwight D. Eisenhower Presidential Library and Museum, Abilene, Kansas
The Eisenhower Presidential Library and Museum will host a day of programs on July 24 to honor the service of Americans who have served in the Republic of Korea from 1950 to the present.
The day begins with a presentation by intelligence agency historians and ends with dinner and entertainment. All events are free and open to the public with the exception of the dinner, which costs $20 per person.
The schedule is as follows: Eisenhower, Intelligence, and Korea Visitors Center Auditorium, 10:30 a.m. - noon -Dr. Clayton Laurie, CIA "Baptism by Fire: CIA Analysis of the Korean War" -Dr. David Hatch, NSA historian, "DDE and COMINT: Astute Consumer and Agent of Change" The Korean War was the Agency's first role in an international conflict. The opening of classified material as featured in the "Baptism By Fire" book will contribute significantly to the historic record of the Korean War, making possible new research and great understanding of early Cold War history.
Korean War and Service Veterans Panel Discussion Visitors Center Auditorium, 1 to 2:45 p.m. The panel will feature Dr. Paul Edwards, Director Emeritus, Center for the Study of the Korean War, as moderator. Panel members include veterans who have served in Korea at various times from the 1950s to the 1990s.
Keynote Address | Lt. Gen. Robert Arter, U.S. Army (Ret.) Presentation of Eisenhower Peacemaker Coins Visitors Center Auditorium, 3 to 4:30 p.m.
Keynote speaker retired Lt. Gen. Robert Arter is a veteran of the wars in Korea and Vietnam and former commander of the U.S. Sixth Army. Arter is a Civilian Aide to the Secretary of the Army, and a consultant and bank director. In 2009 he received the Distinguished Civilian Service Award for his work as a Civilian Aide. It is the highest award a civilian can receive from the Army.
The Eisenhower Peacemaker Coin is available to Korean War veterans and all those who have served to keep the peace in Korea since the signing of the armistice on July 27, 1953. (Coin recipients or their representatives MUST be present at the ceremony.) If you or a loved one served in Korea and are able to attend the ceremony, sign up to receive the Eisenhower Peacemaker Coin.
Reception and Dinner 5:30 p.m. Social | Library Lobby 6:00 p.m. Dinner | Library Courtyard Cost is $20 per person and includes the remarks by retired Maj. Gen. Singlaub and entertainment by Ray Marco. RSVPs required by July 16. Please send check, made payable to Eisenhower Foundation, to P.O. Box 339, Abilene, Kan. 67410.
Remarks | Maj. Gen. John K. Singlaub, U.S. Army (Ret.) -
Singlaub is a veteran of WWII, Korea and Vietnam. From July 1976 to June 1977 he served as Chief of Staff, United Nations Command, U.S. Forces Korea. He is recipient of many decorations and awards. His autobiography, Hazardous Duty, was published in 1991.
Entertainment | Ray Marco Mr. Marco is a veteran performer of the stage, television and motion picture screen. His 1956 hit "Abilene" was the unofficial campaign song for President Eisenhower's successful re-election. Mr. Marco is a veteran of the U.S. Air Force Security Service.
This program is in partnership with the Harry S. Truman Library and Museum. Please visit the Truman Library web site at www.trumanlibrary.org for a full schedule of events. The Truman Library programming focuses on the early time period of the war while the Eisenhower Library focuses on the latter time period and years since the signing of the armistice. This program is sponsored by the Eisenhower Foundation and Duckwall-ALCO Stores, Inc. It is dedicated to President Eisenhower's successful conclusion of the conflict on July 27, 1953.
28 July 2010, 9 am - 5 pm - Miami, FL - INFRAGARD South Florida and the FBI invite AFIO MEMBERS to their South Florida Conference
Location: Florida International University, Management Advanced Research Center, Room # 125, 11200 SW 8th St, Miami, FL 33199
Speakers: Eric S. Ackerman, PhD, InfraGard South Florida Chapter President, Stewart L. Appelrouth, CPA, InfraGard Treasurer, SA Nelson J. Barbosa, InfraGard Coordinator/FBI Miami
Sam Fadel, Florida Regional Field Investigator, Corporate Security Department, This presentation will focus on data breach investigations, specifically credit card/account number breaches. Defines the roles of the issuers, law enforcement and forensic experts.
SA Kathleen J. Cymbaluk, Miami FBI Recruiter on FBI Employment Needs. This presentation will discuss current hiring needs of the FBI and requirements on how to qualify and apply.
Stewart Appelrouth and Ed Farath, CPA, Appelrouth/Farah & Co., P.A., This presentation will focus on Financial Fraud, Specifically Ponzi Schemes.
Richard Wickliffe, Team Manager, Special Investigation Unit, State Farm Insurance Companies, Will discuss Fraud, White Collar Financial Issues- and Possible Counterterrorism Implications.
Randall C. Culp, Supervisory Special Agent, FBI, This presentation will discuss Health Care Fraud – Adapting Investigations and Prosecutions to deal with emerging trends.
Gun Running from Broward and Palm Beaches Counties - Mark A. Hastbacka, Supervisory Special Agent, FBI, This presentation will touch on IRA gun running operation in the above counties from a counterterrorism investigation point-of view
RSVP TO Nelson Barbosa at FBI Miami Field Office:Nelson.Barbosa@ic.fbi.gov
Saturday, 31 July 2010, 10 am - 12 noon - Coral Gables,
FL - AFIO/Miami Police Department Counter-Terrorism Training. In cooperation with the City of Miami Police Dept, Office of Emergency
Management & Homeland Security, Officer Marcos T. Perez, AFIO will
be presenting a Counter-Terrorism Training and Program. "Operation
Miami
Shield." There is limited space available for this program.
Please RSVP with checks enclosed before July 21, 2010. There is a $10
charge for AFIO Members. Guests will be charged at $25 per person.
Checks payable to "AFIO" and mailed to Tom Spencer at 999 Ponce de
Leon
Blvd Ste 510, Coral Gables, FL 33134
17 - 20 August 2010 -
Cleveland, OH - AFIO National Symposium on the Great Lakes
- "Intelligence and National Security on the Great Lakes"
Co-Hosted with the AFIO Northern Ohio Chapter at the Crowne Plaza
Hotel, Cleveland, OH. Includes presentations by U.S. Coast Guard on
Great Lakes security; Canadian counterparts to explain double-border
issues;
National Air/Space Intelligence Center; Air Force Technical
Applications Center; Ohio Aerospace Institute.
Cruise on Lake Erie
.
Spies-in-Black-Ties Dinner and Cruise on Lake Erie. Make your reservations here. Agenda here.
29-30
September 2010 - Washington, DC - Conference on the American
Experience
in Southeast Asia, 1946-1975 by the U.S. Department of State.
The U.S. Department of State's Office of the Historian is pleased to
invite AFIO members to a conference on the American Experience in
Southeast Asia, 1946-1975, which will be held in the George C.
Marshall
Conference Center at the State Dept. The conference will feature a
number of key Department of State personnel, both past and present.
Those speaking will include:
* Former Secretary of State Henry A. Kissinger
* Former Deputy Secretary of State John D. Negroponte
* Special Representative for Afghanistan and Pakistan Richard A.
Holbrooke
The conference will include a panel composed of key print and
television
media personnel from the Vietnam period discussing the impact of the
press on public opinion and United States policy. A number of
scholarly
panels featuring thought-provoking works by leading scholars will also
take place. Registration information will be available at the State
Dept
website, http://history.state.gov,
after August 1.
6 - 7 October 2011 - Laurel, MD - The NSA's Center
for Cryptologic History hosts their Biennial Cryptologic History
Symposium with theme: Cryptology in War and Peace: Crisis Points in
History.
Historians from the Center, the Intelligence Community, the defense
establishment, and the military services, as well as distinguished
scholars from American and foreign academic institutions, veterans of
the profession, and the interested public all will gather for two days
of reflection and debate on topics from the cryptologic past. The
theme
for the upcoming conference will be: “Cryptology in War and Peace:
Crisis Points in History.” This topical approach is especially
relevant
as the year 2011 is an important anniversary marking the start of many
seminal events in our nation’s military history. The events that can
be
commemorated are many.
Such historical episodes include the 1861 outbreak of the fratricidal
Civil War between North and South. Nineteen forty-one saw a surprise
attack wrench America into the Second World War. The year 1951 began
with the fall of Seoul to Chinese Communist forces with United Nations
troops retreating in the Korean War. In 1961, the United States began
a
commitment of advisory troops in Southeast Asia that would eventually
escalate into the Vietnam War; that year also marked the height of the
Cold War as epitomized by the physical division of Berlin. Twenty
years
later, a nascent democratic movement was suppressed by a declaration
of
martial law in Poland; bipolar confrontation would markedly resurge
for
much of the 1980s. In 1991, the United States intervened in the
Persian Gulf to reverse Saddam Hussein’s aggression, all while the
Soviet Union suffered through the throes of its final collapse. And
in
2001, the nation came under siege by radical terrorism.
Participants will delve into the roles of signals intelligence and
information assurance, and not just as these capabilities supported
military operations. More cogently, observers will examine how these
factors affected and shaped military tactics, operations, strategy,
planning, and command and control throughout history. The role of
cryptology in preventing conflict and supporting peaceful pursuits
will
also be examined. The panels will include presentations in a range of
technological, operational, organizational, counterintelligence,
policy,
and international themes.
Past symposia have featured scholarship that set out new ways to
consider out cryptologic heritage, and this one will be no exception.
The mix of practitioners, scholars, and the public precipitates a
lively
debate that promotes an enhanced appreciation for the context of past
events. Researchers on traditional and technological cryptologic
topics, those whose work in any aspect touches upon the historical
aspects of cryptology as defined in its broadest sense, as well as
foreign scholars working in this field, are especially encouraged to
participate.
The Symposium will be held at the Johns Hopkins Applied Physics
Laboratory’s Kossiakoff Center, in Laurel, Maryland, a location
central
to the Baltimore and Washington, D.C., areas. As has been the case
with
previous symposia, the conference will provide unparalleled
opportunities for interaction with leading historians and
distinguished
experts. So please make plans to join us for either one or both days
of
this intellectually stimulating conference.
Interested persons are invited to submit proposals for a potential
presentation or even for a full panel. While the topics can relate to
this year’s theme, all serious work on any aspect of cryptologic
history
will be considered. Proposals should include an abstract for each
paper and/or a statement of session purpose for each panel, as well as
biographical sketches for each presenter. To submit proposals or form
more information on this conference, contact Dr. Kent Sieg, the
Center’s
Symposium Executive Director, at 301-688-2336 or via email at kgsieg@nsa.gov.
For
Additional Events
two+ months or greater....view our online Calendar of
Events
-----------------------------------------------------------------------
Disclaimers
and Removal Instructions
Weekly
Intelligence Notes (WINs) are commentaries on Intelligence and related
national security matters, based on open media sources, selected,
interpreted, edited and produced for non-profit educational uses by
members
and WIN subscribers.
REMOVAL
INSTRUCTIONS: We
do not wish to add clutter to inboxes. To discontinue receiving the
WINs:
a)
IF YOU ARE A MEMBER -- click here: UNSUBSCRIBE and supply your full name and email
address
where you receive the WINs. Click SEND, you will be removed from
list.
If this link doesn't open a blank email, create one on your own and
send to afio@afio.com with the
words: REMOVE FROM WINs as the subject, and provide your full
name and
email address where you are currently receiving them.
b)
IF YOU ARE NOT A MEMBER, and you received this message, someone
forwarded this newsletter to you [contrary to AFIO policies]. Forward
to afio@afio.com the
entire WIN
or message you received and we will remove the sender from our
membership
and distribution lists. The problem will be solved for both of us.
CONTENTS
of this WIN [HTML version recipients - Click title to jump to story or
section, Click Article Title to return to Contents. This feature does
not
work for Plaintext Edition or for some AOL recipients]. If you wish to
change to HTML format, let us know at afio@afio.com. The HTML feature also does not work
for
those who access their e-mail using web mail...however NON-HTML
recipients
may view the latest edition each week in HTML at this link: https://www.afio.com/pages/currentwin.htm
-----------------------------------------------------------------------
WINs
are protected by copyright laws and intellectual property laws, and
may
not be reproduced or re-sent without specific permission from the
Producer. Opinions expressed in the WINs are solely those of the
editor(s)
or author(s) listed with each article. AFIO Members Support the AFIO
Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for
back issues of the WINs, information about AFIO, conference agenda
and
registrations materials, and membership applications and much more!
(c)
2010, AFIO, 6723 Whittier Ave Suite 200, McLean, VA
22101. Voice: (703) 790-0320; Fax: (703) 991-1278; Email: afio@afio.com
Click here to return to top.