AFIO
Weekly Intelligence Notes #26-10 dated 13 July 2010
REMOVAL
INSTRUCTIONS: We
do not wish to add clutter to inboxes. To discontinue receiving
the WINs, click here: |
CONTENTS
Section I -
INTELLIGENCE HIGHLIGHTS
Section
II - CONTEXT & PRECEDENCE
Section
III - COMMENTARY
Section
IV - OBITUARIES AND
COMING
EVENTS
Obituaries
Coming Events
Current
Calendar New and/or Next Two Months ONLY
- 16, 23 July 2010, 8 and 10 pm - Washington, DC - THE SPY
MAGIC SHOW - An incredible exploration into the secrets of
spies, shown
through stunning sleight-of-hand magic by master magician
Michael
Gutenplan.
- Thursday, 15 July 2010, 11:30 am - Colorado
Springs, CO - The Rocky Mountain Chapter hears Tim
Murphy on R&D Platform Usage in Intelligence.
- Wednesday,
21 July 2010, 10 am - 12:45 pm - Annapolis Junction, MD -
"The
Mysterious Rosetta Stone: A Code-Cracking International
Treasure" with
Dr. Joel Freeman, is topic at the National Cryptologic
Museum Foundation
Summer Cryptologic meeting.
- 22
July 2010 – San Francisco, CA – The AFIO Jim Quesada
Chapter hosts John
Yoo, former deputy assistant attorney general in the
Office of Legal
Counsel of the U.S. Department of Justice, where he worked
on national
security and terrorism after the September 11 attacks.
- 24 July 2010 - Abilene, KS - Korea
60: Eisenhower the Peacemaker - Honoring Those who Served
in Korea - CIA
joint conference at Dwight D. Eisenhower Presidential
Library and
Museum, Abilene, Kansas
- 28 July 2010, 9 am - 5 pm - Miami, FL -
INFRAGARD South Florida and the FBI invite AFIO MEMBERS
to their South
Florida Conference
- Saturday, 31 July 2010, 10 am - 12 noon - Coral Gables,
FL - AFIO/Miami Police Department Counter-Terrorism
Training
- Saturday, 14 August 2010, 11 am - Orange Park, FL - AFIO Northern Florida Chapter hears expert on technology capabilities of FBI/DEA/ATF regarding air travel.
- 17-20
August 2010 - Cleveland, OH - AFIO
National Symposium
on the Great Lakes. Details....
- Saturday,
25 September 2010, 10:30 am - Coral Gables, FL - "Management of Kidnap
and Extortion Incidents" the topic at the AFIO Miami Chapter event.
- 29-30 September 2010 - Washington, DC -
Conference on the American Experience in Southeast Asia,
1946-1975
featuring Kissinger, Negroponte & Holbrooke, by the
U.S. Department
of State.
- Saturday, 2 October 2010, 6:30 pm - Washington, DC - William J. Donovan Award Dinner Honoring Ross Perot by The OSS Society
Events at the International Spy Museum in
July & August with full details
- Wednesday, 7 July 2010; 6:30 pm - Washington, DC - "A
New Cold War: Inside Nuclear Iran" at the International
Spy Museum
- Thursday, 15 July 2010; 12 noon – 1 pm - Washington, DC -
"Eyes in the Sky: Eisenhower, the CIA, and Cold War Aerial
Espionage"
at the International Spy Museum
- Thursday, 5 August 2010, noon - Washington, DC -
"Silent Sentry: The Untold Story of the National Security
Agency" - at
the International Spy Museum
- Wednesday, 11 August 2010, 6:30 pm - Washington, DC -
"Uneasy Alliance: The CIA and ISI in Pakistan" - at the
International
Spy Museum
|
REGISTER NOW
18 - 20 August 2010

AFIO National GREAT LAKES
Intelligence Symposium 2010
"Intelligence and National Security on the
Great Lakes and Northern Border"
at the Crowne Plaza Hotel, Cleveland, OH
Co-Hosted with the AFIO Northern Ohio
Chapter
Includes presentations by U.S. Coast Guard
on Great Lakes/Northern Border security;
National Air/Space Intelligence Center; Air Force Technical
Applications Center; Ohio Aerospace Institute, Dinner/Cruise
on Nautica
Queen on Lake Erie.
Spies-in-Black-Ties Reception and Banquet
Make your reservations here.
Agenda is here.
To reserve rooms at the
Crowne Plaza Hotel in Cleveland, Ohio now at the $89/nite
special event
rate, use the following link: http://tinyurl.com/37frwnl
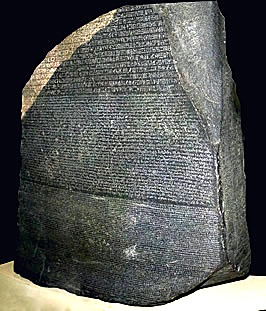
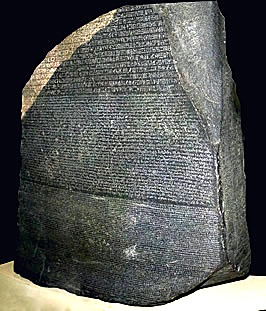
The Mysterious Rosetta Stone: A
Code-Cracking International Treasure
Dr. Joel Freeman speaks at the
National Cryptologic Museum Foundation Summer Cryptologic
meeting.
Wednesday, 21 July 2010, 10 am - 12:45
pm - Annapolis Junction, MD
All AFIO members are invited to hear guest speaker, Dr.
Joel Freeman, CEO and President of the Freeman
Institute, discuss the history of the Rosetta Stone, focusing
on the
historical connection between the Rosetta Stone and the
breaking of
codes. Guests will have an opportunity to view the
full-sized,
three-dimensional Rosetta Stone replica normally on display in
the lobby
of the National Cryptologic Museum. Dr. Freeman is a gifted
speaker and
author. As part of the program there will be a brief
presentation to
acknowledge the Milt Zaslow Memorial Award for Cryptology that
was
presented for the first time at this year's Maryland History
Day
Ceremony on 24 April.
Location: the L3 Conference Center in
the National Business Park. Lunch will be served at 11:45
following the
presentation. L3 Conference Center is located at 2720
Technology Dr,
Annapolis Junction, MD 21076 in the Rt. 32 National Business
Park.
Cost: the fee is $25 to cover program
& lunch costs.
Confirm your attendance by Wednesday, 14 July, by
calling (301) 688-5436 to pay by credit card or by mailing
a
check to NCMF, POB 1682, Ft. Meade, MD 20755. We look forward
to seeing
you there.
SpyCruise� Eastern Caribbean setting
sail November 13th, 2010. For information on the upcoming
cruise, visit https://www.afio.com/index.html#spycruise
SpyCruise Stateroom Discount Program
As some of you may know, you may earn a free stateroom if
you acquire 15 other stateroom bookings (double
occupancy). For some
this can prove difficult. Therefore, in order for
each of you to
be able to benefit from this program, we want to offer
everyone a
discount based whatever number of additional staterooms
you are able to
fill. For every additional stateroom you get booked
for
SpyCruise, your stateroom will be discounted by 1/15th of
the cost of
the additional stateroom. In
order for
your stateroom to be completely free, you would need to
acquire 15
additional bookings of the same category or greater than
the one you
book. When your friends, colleagues, family or
neighbors book
their SpyCruise, they will need to tell the agent that
you recruited
them. This way we can track who has earned the
discounts.
Of course, each of those guests may participate in this
program as
well.
WIN
CREDITS FOR THIS
ISSUE: The WIN editors thank the following special
contributors to
this issue: dh, pjk, fm, cjlc, th, and fwr.
They have contributed one or more
stories used in this issue.
For Additional Events two+ months or more....
view our online Calendar of Events |
Section
I - INTELLIGENCE
HIGHLIGHTS
Afghan NSA Blasts Pak for Providing Safe Havens to Al-Qaeda, Other Terror Groups. In what appears to be a significant change in Afghanistan's policy after continuous overtures to Pakistan, National Security Advisor Rangin Dadfar Spanta has called on Islamabad to take "serious measures" against militants using the country's soil to launch attacks on the war-torn nation.
In an interview with a foreign news agency, Spanta said there was "tremendous evidence" that Pakistani authorities were allowing Al-Qaeda and other terror groups to operate from safe havens based inside the country, and that Kabul, on many occasions, had presented that evidence to Islamabad.
"My expectation is that Pakistan after nine years - because theoretically Pakistan is part of the anti-terror alliance - they have to begin to take some serious measures against terrorism," The Dawn quoted Spanta, as saying.
"We have evidence that the terrorists from Pakistan are involved in daily attacks against our people and international 'jihadi' groups are active here. They have their base and sanctuaries behind our border and this is a serious problem," he added.
Spanta said Pakistan has failed to tackle extremists on a whole, and has also been unsuccessful in carrying out action against any militant group be it Al-Qaeda, the Haqqani network or the less powerful Hekmatyar group and the Hizb-u-Tahrir.
"It is not a particular secret that the terrorists have sanctuaries in Pakistan, that they have training centres, that they have the possibility to come to Afghanistan, attack us and go back," he said.
[SIFY/6July2010]
Britain Pledges Inquiry Into Torture. Prime Minister David Cameron announced that Britain's new coalition government would appoint an independent inquiry into allegations that its security services, MI5 and MI6, colluded with the Central Intelligence Agency and other foreign organizations in the rendition and torture of terrorism suspects held in foreign prisons after the 9/11 attacks.
Mr. Cameron had called for the inquiry before the spring election campaign against the former Labor government, which had endured years of criticism at home for being too cozy with the Bush administration in the reaction to terrorism.
Mr. Cameron said a 76-year-old retired appeals court judge, Sir Peter Gibson, would head a three-member panel to review actions by the security services that have led to a dozen cases before British courts in which former detainees have alleged that the British agencies knew - or should have known - that the detainees were being mistreated.
"It's time to clear this matter up once and for all," he told the House of Commons.
He said he hoped that the inquiry would start before 2011, and that he would have the panel's full report within 12 months of its first sitting. While the panel would hold "some of its hearings" in public, he said, much of its work would be conducted behind closed doors.
"Let's be frank," he said, "it is not possible to have a full public inquiry into something that is meant to be secret."
In a further bid to end the controversy, he said the government was committed to a role of "mediation" in the civil suits for damages that former detainees had brought against the British security services and, "wherever appropriate," to pay compensation. It was the closest any British minister had come to acknowledging outright that British agents knew or suspected that the detainees were being abused, and did little or nothing to prevent it.
"While there is no evidence that any British officer was directly engaged in torture in the aftermath of 9/11, there are questions over the degree to which British officers were working with foreign security services who were treating detainees in ways they should not have done," Mr. Cameron said. He said this had "led to accusations that Britain may have been complicit in the mistreatment of detainees."
Under the Labor government, MI5, responsible for Britain's internal security, and MI6, responsible for external security, issued strong denials that their agents were complicit in mistreatment. The agencies received vigorous backing from the government, at least until court disclosures began to show that the detainees' allegations against them might have had some validity.
Mr. Cameron said that the security agencies were being "paralyzed by paperwork" as they defended themselves against the allegations in court, and that Britain's international reputation was being damaged, too.
"Public confidence is being eroded, with people doubting the ability of our services to protect us and questioning the rules under which they operate," he said. "And terrorists and extremists are able to exploit these allegations for their own propaganda."
Former detainees have said that British agents who questioned them while they were detained, or who were working closely with American and other foreign agencies overseeing their interrogations, were complicit in their being shuttled through the C.I.A.'s secret archipelago of "ghost prisons." In several cases, the detainees said the agents either witnessed the abuse or knew enough to conclude that they were being mistreated.
Among other charges, the detainees have claimed that they were subjected to sleep deprivation and painful "stress positions," as well as to excessive noise, cold and threats of being killed or "disappeared." One widely publicized case involved Binyam Mohamed, an Ethiopian-born former detainee with a British right of residency who was released from the prison at Guant�namo Bay last year and returned to Britain; among the charges are that his genitals were sliced with a razor while he was being held in Morocco.
In his Commons statement, Mr. Cameron trod warily around the implications of the inquiry for relations with the United States. In Mr. Mohamed's court case, the Labour government fought - and lost - a bid to keep secret information about his treatment that was provided to Britain by the C.I.A. At one point, Secretary of State Hillary Rodham Clinton warned Britain's Foreign Office that security cooperation between the countries would be harmed if the information provided to Britain in secret were made public by the court.
Mr. Cameron said the inquiry would be expected to review aspects of Britain's cooperation on terrorism matters with the United States. "Did we allow our own high standards to slip - either systematically or individually?" he asked. "Did we give clear enough guidance to officers in the field?"
But the prime minister also stressed the damage that could result if the United States lost confidence in Britain. There were doubts, he said, about the British agencies' ability to "protect the secrets" of allied agencies like the C.I.A. He added, "This has strained some of our oldest and most important security partnerships in the world - in particular, that with America."
[NYTimes/7July2010]
North Korean Female Spy Spared. South Korean prosecutors will not charge a woman forced to spy for North Korea because she is in poor health and cooperated with investigators, a spokesman said.
The 36-year-old identified only as Kim was arrested in May for allegedly obtaining classified information on Seoul's subway system from a male employee in return for providing him with sexual services. Her arrest came eight months after she entered South Korea via China and Laos in the guise of a defector.
The subway employee, who first met Kim online when she was operating a travel agency in China in 2006 and 2007, has been charged with espionage.
'Prosecution authorities have decided not to indict Kim as she has clearly expressed her intention to shift loyalty to the South and she was in poor health,' the Seoul central district prosecution office spokesman told AFP. She needs a liver transplant, he said.
Authorities also took into account the fact that she was forced into espionage to avoid punishment for losing her communist party membership card on a train in 1997 in North Korea.
'She became disillusioned with the North after she arrived in the South,' a prosecution source was quoted as saying by Yonhap news agency. 'We expect her to cooperate well not only in her own case but in other spy cases as well.' Spies can in theory face the death sentence but are sometimes treated leniently if they renounce the North's regime and cooperate.
[StraitsTimes/8July2010]
British Government Curbs Stop-and-Search Terrorism Powers. The British government said it was suspending anti-terror legislation allowing people to be searched by police without good reason after European judges ruled it was unlawful.
Home Secretary Theresa May said she was introducing interim guidelines for police stating they could only use stop and search powers if they reasonably suspect the person of terror-related activities.
She was responding to a European Court of Human Rights judgment earlier this year that Section 44 of the Terrorism Act 2000, which allows police to search people without suspicion, was illegal.
"Officers will no longer be able to search individuals using section 44 powers. Instead, they will have to rely on section 43 powers - which require officers to reasonably suspect the person to be a terrorist," May told the House of Commons.
"And officers will only be able to use section 44 in relation to the searches of vehicles.
"I will only confirm these authorizations where they are considered to be necessary - and officers will only be able to use them when they have 'reasonable suspicion'."
The new guidelines will be in place until a wide-ranging review of counter-terrorism legislation has been conducted by Prime Minister David Cameron's new coalition government, she said.
Shami Chakrabarti, director of civil liberties group Liberty, welcomed the move, saying Section 44 had "criminalized and alienated more people than it ever protected".
"It is a blanket and secretive power that has been used against school kids, journalists, peace protesters and a disproportionate number of young black men," she said.
"To our knowledge, it has never helped catch a single terrorist. This is a very important day for personal privacy, protest rights and race equality in Britain."
In a unanimous ruling in January, seven European Court judges said the searches breached the complainants' right to respect for their private life under Article 8 of the European Convention on Human Rights.
May said the government could not appeal the ruling but would not have done so even if it wanted to.
[Breitbart/8July2010]
Two U.S. Spies for Cuba Ask Court to Jail Them Near Each Other. A Washington, D.C., couple who spent 30 years spying for Cuba are asking a federal judge to recommend that they be incarcerated near each other - but not in Florida, where they say the federal prisons "will likely have populations of Cuban-Americans who might react strongly to their offense."
Walter Kendall and Gwendolyn Myers pleaded guilty in November to sending secrets to the United States' longtime antagonist. They are scheduled to be sentenced Friday before U.S. District Judge Reggie B. Walton.
Walter Myers - a former State Department employee with top-secret clearance - agreed to a life sentence without parole and to cooperate with the federal government in a deal that offered his wife a much lighter sentence than the 20 years she might have faced at trial.
In court documents filed late Friday, the couple's defense attorneys are asking Walton to sentence Gwendolyn Myers to the low end of the plea deal - six years, rather than seven-and-a-half years.
"The eighteen-month difference between 72 and 90 months could potentially represent a significant percentage of her remaining life span," her lawyers wrote, noting that Gwendolyn Myers, whom they portray as a doting grandmother, will be 72 on Friday and has suffered cardiac complications, including a heart attack since her incarceration last June.
In arguing for a lighter sentence, her attorneys note that although Gwendolyn Myers "shared her husband's political beliefs, she had no capacity to commit the offense on her own."
They include letters of support from friends, former employees and family members who plead for leniency.
"Mrs. Myers has positively impacted each community in which she has lived, and her release from prison would allow her to continue contributing to those around her, starting with, but by no means limited to, her extended family," her attorneys wrote.
They argued that she and Walter Myers "within days of their arrest" offered to cooperate with the government and have undergone nearly 100 debriefings with the FBI and other intelligence agencies. They noted that Gwendolyn Myers has worked as a teacher's assistant in the jail's life-skills class, helping teach other inmates.
Government prosecutors, however, are asking for the maximum sentence, with U.S. Attorney Ronald Machen writing that the couple "committed one of the worst crimes a citizen can perpetrate against his or her own country - espionage on behalf of a long-standing foreign adversary."
In addition, he noted that "without Gwendolyn Myers's deference to, if not active support and encouragement of, seemingly everything her husband did, (Walter) Kendall Myers's desire to become a Cuban spy 30 years ago may well have been short-lived."
At one point, he calls her "far more than just a knowing wife of a spy," noting that they both were recruited by Cuban intelligence and that she, like her husband, had a code name supplied by the Cubans. "He was Agent 202. She was Agent 123," Machen wrote. "She not only supported and encouraged her husband's theft of U.S. secrets from the Department of State, but she also actively engaged in their espionage."
Machen argued that her "criminal culpability" was greater than other past spouses of spies, including Rosario Ames, the wife of Russian spy Aldrich Ames, and Anne Case Pollard, the wife of Israeli spy Jonathan Pollard.
"Unlike Gwendolyn Myers, neither Rosario Ames nor Anne Pollard decrypted coded messages from, assisted in the transmission of classified information to, nor had repeated, substantive operational meets with, the foreign intelligence service at issue," he said.
Machen also suggested that Walter Myers was not always forthcoming during the briefings, which remain classified. He wrote that the couple was "generally outwardly cooperative" during the briefings and never refused to attend a session.
But he said, "there were times when the FBI assessed that (Walter) Kendall Myers, in particular, gave inconsistent or uncooperative responses or was intentionally withholding information."
The pair is asking that Walton recommend to the Bureau of Prisons that they be incarcerated in facilities near each other, to allow their siblings, their six children, and seven grandchildren to visit them. They suggest placing Gwendolyn Myers in the Satellite Camp in Lexington, Ky., and Walter Myers in an adjacent Administrative Facility.
Or alternatively, that Walter Myers be placed at the U. S. penitentiary for male inmates in Atwater, Calif., and Gwendolyn Myers at the Federal Correctional Institution for women in Dublin, California.
"Such proximity also means something to Dr. and Mrs. Myers personally: both will derive some comfort from knowing the other is not physically far away. In light of the depth of the emotional bonds of their marriage - a relationship numerous letter writers comment upon as exceptionally loving and close."
They also are asking that Walton recommend that the prison allow Walter to continue to teach fellow inmates and "continue his scholarly writing," noting that he is working on a book on.
"At all turns, they have attempted to benefit in some small way their fellow inmates and to salvage some larger good from their situation. Their behavior has reflected their determination, as they serve out their punishments, to use their talents in the service of others. Their conduct since their arrest is entirely consistent with the idealism that brought them before this court."
[Clark/KansasCity/10July2010]
CIA to Debrief Agents Freed by Russia. CIA officials were expected to whisk agents freed by Moscow to a safe house for a long debriefing, a former top security aide said, adding they could provide valuable information to the spy agency.
"They will be taken to a safe facility... by intelligence officers who will go through a period of debriefing them and preparing them for a new life and arranging for new identities," Fran Townsend said.
Townsend, the homeland security adviser to former president George W, Bush, was speaking after the White House confirmed the CIA chief Leon Panetta had led negotiations with Russia for the biggest spy swap since the Cold War.
Ten convicted Russian agents were exchanged for four Russians convicted of spying for Western countries in a dramatic deal completed Friday at Vienna airport.
But it was not immediately clear how many of the four released by Moscow arrived in the United States, after their plane stopped briefly in England.
US and British media reports suggested at least one, and possibly two of the four, had stayed behind in Britain. The CIA did not immediately respond to an AFP inquiry on the issue.
A spokesman for President Barack Obama told reporters that Panetta, director of the Central Intelligence Agency, had led the swap negotiations and that Obama himself was first briefed on the situation as far back as a month ago.
"The United States government came up with the four individuals to be freed by the Russians based on humanitarian concerns, health concerns, and other reasons that we put forward to the Russians," the White House official, who asked not to be named, said.
"Director Panetta led these conversations and we received a response soon after the names were offered," the official said.
Townsend said the CIA will offer the freed agents housing and financial assistance as they start their new lives.
And they will quiz them closely to "understand what were the sorts of questions that Russian officials were asking them when they were in prison and arrested and how were they treated," she said.
The debriefings, which could take weeks or even months, will help "from a counterintelligence perspective," she added, saying: "We will likely learn a fair amount from these people."
The US administration said security agencies first briefed the White House in February and that Obama was briefed in person on June 11.
Obama chaired a National Security Council meeting to discuss the agents on June 18th, who were arrested June 27.
"At the time of the arrests, the president was kept fully apprised of developments," the official said.
The deal was seen as a high-level solution to a spy scandal that threatened to disrupt improving US-Russian relations.
The 10 Russian agents, who were arrested last month, pleaded guilty Thursday to being foreign agents and were ordered to leave the country immediately, avoiding the need for a politically embarrassing trial.
[AP/9July2010]
NSA Offers Explanation of Perfect Citizen. The Perfect Citizen project is purely a research-and-engineering effort, not an attempt to monitor companies against cyberattack, the National Security Agency said.
The NSA issued a brief explanation of the new project in response to a Wall Street Journal story that described Perfect Citizen as a government system designed to monitor vital agencies and private utilities against potential cyberthreats. The project would establish a series of sensors installed throughout various computer networks that would raise an alarm in case of a pending cyberattack, according to the Journal.
But in an e-mail statement attributed to NSA spokeswoman Judith Emmel, the agency denied that Perfect Citizen would involve any type of monitoring activity or sensors, and labeled it as "purely a vulnerabilities assessment and capabilities development contract." She added that "it does not involve the monitoring of communications or the placement of sensors on utility company systems."
Although the agency called the Journal's story an "inaccurate portrayal of the work performed at the National Security Agency," it said that due to the highly sensitive nature of its work, it could not confirm or deny specific allegations addressed in the article. As a result, the NSA shared few details on the project.
Specifically referring to it as a contract, the NSA said Perfect Citizen "provides a set of technical solutions that help the agency better understand the threats to national-security networks, which is a critical part of NSA's mission of defending the nation." The Journal had pinpointed Raytheon as the recipient of the initial phase of the contract in a deal worth up to $100 million, though neither the NSA nor Raytheon would confirm that report, according to Reuters.
As described in the Journal, the project has reportedly triggered mixed reactions, with some eyeing it as an effort by the NSA to intrude into domestic affairs and others seeing it as an important step in combating cyberattacks.
Addressing those allegations in the statement, Emmel said "any suggestions that there are illegal or invasive domestic activities associated with this contracted effort are simply not true. We strictly adhere to both the spirit and the letter of U.S. laws and regulations."
Whether Perfect Citizen is a monitoring system, as reported by the Journal, or a simply an R&D contract, as defined by the NSA, the threat of cyberattacks against the United States remains real. Security experts both inside and outside the beltway have long been warning that a serious cyberattack against the nation's infrastructure could do significant damage.
Although cybersecurity has been on the government's agenda for the past few years, many believe that the United States remains highly vulnerable and still has much work to do to shore up its cyberdefenses.
[Whitney/CNET/9July2010]
Ex-CIA Chief: Secrecy After Attack on Syrian Nuclear Plant Unjustified. The secrecy surrounding the attack on the nuclear plant in eastern Syria in September 2007 was justified only for the period immediately after the operation, according to the CIA head at the time, Gen. Michael Hayden. That secrecy had been meant to save President Bashar Assad from embarrassment that could have provoked him to retaliate.
Hayden's comments, published in a journal on intelligence published by the CIA, reflect a view different from that of Israel, which has not commented on the attack, widely attributed to its air force.
Before being appointed CIA head by George W. Bush, Hayden was a senior officer in the U.S. Air Force and head of the National Security Agency - the main signals-intelligence service in the United States. He resigned last February after President Barack Obama turned down his request to have his tenure extended by six months.
Some analysts were critical of the CIA's release of information related to the air strike, and argued that the main motivation was for the organization to show an intelligence success following the failure to prevent the attacks on the United States on September 11, 2001.
In the interview, Hayden was asked to explain his support for exposing the role of intelligence in unveiling the presence of the Syrian reactor.
"It was a very complex political problem," he said. "First of all, when we became aware of it, it became very important to keep it secret. Arguably secret, because it had to be dealt with in a way that didn't create a war in the Middle East. And the more public it became, the more difficult it would be for the Syrians to act responsibly. So no question that it needed to be kept secret.
"But after a time, after the facility had been destroyed, there were two lines working - because you had two bad actors here, the Syrians and the North Koreans," Hayden said.
"With the Syrians, you needed to keep it secret, otherwise they might do something stupid if they were publicly embarrassed. With the North Koreans on the other hand, we were moving in the direction of a new arrangement with regard to things 'nuclear,' including proliferation."
In the dispute between the two approaches, it appears that Hayden was right and those who advocated secrecy were wrong. Nearly three years after the strike and two years and three months since the CIA officially released the information, Syria did not do "something stupid" and Assad did not go to war.
[Oren/Haaretz/9July2010]
Microsoft Gives Source Code for Windows to KGB Successor. American software titan Microsoft has released the source code for Windows 7 and Office 2010 to Russia's intelligence services. The move is expected to bolster government contracts and is an extension to an agreement signed back in 2002.
According to Russian newspaper Vedomosti, Microsoft has signed an extension to an agreement with Atlas, a unitary enterprise that develops information security systems. In 2002, Atlas signed an agreement with Microsoft that allowed it access to the source code for Windows 2000, Windows XP, and Server 2000.
The amended agreement will include source code access for Windows 7, Office 2010, and Windows Server 2008, as well as SQL Server. The idea is to allow Russian officials access to the whole platform, not just pieces of it.
The list of official Russian government branches that will gain access to the data includes the Federal Security Service of the Russian Federation (FSB), which replaced the Cold War intelligence agency better known ask the KGB.
While the inclusion of the FSB looks like the beginning of a spy novel, the intelligence agency will be allowed to share conclusions with Atlas. If things go well, defenses can be created for Microsoft's newest line of products that will position them for government purchase and usage. The real purpose is to get Microsoft's foot through the door while gaining more government contracts.
Speaking to Russian media organization RT, Microsoft's PR director in Russia, Marina Levin, said that during the eight years the initial agreement with Atlas had been in place, there were no information leaks and a mutual trust had been built between the two parties.
According to Microsoft, contracts with the state in Russia account for about 10 percent of its revenue, which is estimated to top one billion dollars annually. In order for Microsoft to sell Server 2008, Windows 7, and Office 2010 to the state, its programs must be vetted to ensure they meet the requirements of the FSB and other agencies.
In addition to selling to Russia, Microsoft hopes that other countries will ask for access as well, leading to more opportunities to close lucrative contracts.
[TheTechHerald/12July2010]
Lack of Ethnic Minorities a Concern in Intelligence Services. Britain's anti-terrorism capabilities are being compromised by a lack of ethnic minority staff with key language skills employed in the intelligence services, according to a leaked report.
A culture of racism was also said to exist at the Government Communication Headquarters (GCHQ), which intercepts telephone calls and emails between suspected terrorists for MI5 and MI6.
The report, leaked to the Sunday Times, found that black and Asian officers felt racially discriminated against and their loyalty to Britain was often questioned.
A shortage of specialist knowledge in languages such as Arabic and Urdu was also shown to pose a potential problem when conducting counter-terrorism surveillance.
Approximately 2.5 per cent of GCHQ's 5,500 strong workforce are from an ethnic minority background, and the report was critical of the lack of diversity within GCHQ and its record for recruiting from ethnic minority communities around Britain.
The report stated: "It is critical to have a diverse staff group who are able to profile and recognize certain behavior patterns and communications.
"There is a very small pool of black and minority ethnic employees within the total workforce... specific concerns have been raised by both management and staff around the language team."
The Representation of Black and Minority Ethnic People report was authorised by the head of the civil service, Sir Gus O'Donnell, and written by Whitehall race advisor, Sharon Ferguson, who spent four months interviewing ethnic minority staff at GCHQ in Cheltenham.
The discussions revealed that some black and Asian staff were made to feel unwelcome by both recruiters and white colleagues. The report also discovered that an "unprecedented" number of ethnic minority staff were employed in junior roles, while all the agency's 60 senior civil servants were white and only 1 per cent of management black or Asian.
The report recommended the "embedding" of equality and diversity into recruitment practice, and expanding the recruitment area outside Cheltenham to include nearby cities such as Birmingham and Gloucester.
Chris Marshall, GCHQ's director of corporate communications, denied the organization was "institutionally racist". Although acknowledging GCHQ was "falling short" in meeting diversity targets, he added that the current recruitment freeze, plus "strict nationality and residency requirements", had hampered attempts to increase diversity within the organisation.
[PeopleManagement/12July2010]
Yemen Arrests Journalist Over Links Al-Qaeda. A Yemeni journalist was arrested over suspicion of having links with Al-Qaeda's attack on a Yemeni intelligence agency, a top intelligence official said.
"An arrest warrant was issued late today by the Director of the Political Security Agency (the intelligence) to capture Abdulelah Haidar Shaiee, a Yemeni analyst and journalist on the security affairs and Al-Qaeda group," the official told Xinhua.
"The arrest came following a statement that released on the same day by the Yemeni-based Al-Qaeda militants, in which they claimed responsibility for the June 19 attack on the intelligence headquarters in the southern port city of Aden," he said on condition of anonymity.
The intelligence official said that Shaiee is facing charges of having links with al-Qaida in the Arabian Peninsula (AQAP).
"He is accused of having close relations with the al-Qaida attackers who targeted the building of the intelligence service in Aden that left nearly 20 intelligence officers dead," he added.
Shaiee was taken by four gunmen from his friends' car in Hadda street, near the main intelligence headquarters in Sanaa late Sunday, said lawyer Abdulrahman Barman, a director of a non-governmental human right organization based in Sanaa.
On the same day, Yemeni al-Qaida group released a statement, claiming the responsibility for the June 19 attack on the intelligence headquarters in Aden.
"Battalion of martyr broke into the intelligence headquarters' building in Aden on June 19 and successfully managed to kill at least 24 security officers and soldiers," said the statement posted on al-Qaida-related jihadist website.
It added the attack was a "revenge for the government air raid on the group's stronghold in Marib province, northeast of Sanaa."
Shaiee is a journalist with the official Saba News Agency, and also a freelancer for other international medias. He reportedly managed to conduct several exclusive interviews with AQAP's top leaders, such as the group's leader Naser al-Wiheshi and the US-wanted Yemeni-American fugitive radical imam Anwar al-Awlaqi.
Yemen, the ancestral homeland of al-Qaida network leader Osama bin Laden, has intensified security operations and air raids against terrorist groups, after the Yemen-based al-Qaida wing claimed responsibility for a failed Christmas Day attempt to blow up a US passenger plane bound for Detroit last year.
[GlobalTimes/12July2010]
Section
II -
CONTEXT & PRECEDENCE
Everything You Wanted to Know About the KGB But Were Afraid to Ask. Boris Volodarsky was trained as an officer in the GRU
Spetsnaz, the Soviet military's intelligence arm. When I met him while on book research in London in 2007, he was writing The KGB's Poison Factory, his own book on Moscow's fascination with murder-by-poison. With his encyclopedic knowledge and understanding of the KGB and its history, he is finishing a new book called The Orlov KGB File. I asked whether Volodarsky would reply to a few questions about last week's arrest of 10 Russian
"illegals," sleeper agents planted without diplomatic cover, in the United States.
What would you say is most misunderstood about the illegals indicted in the U.S.?
Volodarsky: As most people, including some journalists who write long articles commenting on the arrests, have no knowledge of the Russian intelligence tradecraft or the intelligence history in general, the activities of the members of this group seem a bizarre collection of strange actions looking like a bad movie about the
Russkies. But many things shown even in bad movies are unfortunately true: Yes, the Russians like to wear fur hats, drink vodka, eat caviar, take pretty girls to the sauna. And, apart from some modern innovations like ad hoc networks, burst transmissions and stenography, the old proven tradecraft is pretty much the same. It is good and it normally works well (except in cases, when somebody is already being shadowed - then nothing works). The public and writers alike do not really realize that this is not a film - a very large group of very experienced FBI agents and watchers spent a very considerable sum of taxpayers' money and plenty of time to uncover a real group of the Russian undercover operators who brazenly operated in the United States, as they had been absolutely sure that no one would ever catch them because their education, training, intelligence tradition, and the belief that the wealth of the country behind them is much superior than the FBI. They forgot that the FBI of 2010 is much different from the Bureau of the 1950s. All 11 accused are trained professionals whose task was to penetrate American society. It is the first time that such a large group of illegals has been uncovered. Normally, there have been one or a maximum of two, while I have on record a great number of documented illegal operations in the U.S. for at least the last 80 years. It must be added that very few of them like Fisher/Abel and
Molody/Lonsdale were successful. But we probably know only about 50 percent of the operations that were mounted and the people deployed.
Is it possible that this is simply a rogue operation by someone in Moscow who, as some commentators have suggested, misunderstand what type of information is openly available? In other words, are illegals a relic, or is there real continuing value to be gained by illegals today?
Volodarsky: No way it is a rogue operation. It took a lot of time, effort and money, and all was done by the book. It is always done this way. Again, I can list several dozen examples when, after training, the Soviet illegals were sent first to Europe, then almost always to Canada, and then relocated to the U.S.
Concerning the information. First of all, the illegals are not here to collect intelligence. Their role is to control important agents already recruited in the government structures, those who have access to secret information (CIA, FBI, other intelligence services, military, scientists, R&D people, IT specialists, etc), or they may exert influence (on journalists or politicians). The Russian foreign intelligence service
(SVR) has all information that is available from open sources. This has always been the case, but it is never enough. What Russian intelligence in striving to get is secret information (political, economic, industrial, military, etc) and have a chance to influence decision-making and public opinion in favor of Russia. This is why agents are recruited or penetrated into sensitive or politically important targets.
The role of illegals is threefold: to act as cut-outs between important sources and the Center (directly or via the SVR station); to serve as talent-spotters finding potential candidates for further intelligence cultivation and possible recruitment (a rather long and complex process, where the illegals only act at its early stage); and to establish the right contacts that would allow other intelligence operators (members of the SVR station) or the Center (visiting intelligence officers under different covers, journalists, diplomats or scientists tasked by the
SVR) to get intelligence information and/or receive favors that the Center is interested in. The illegals also have a number of technical tasks like renting accommodations that could be used as safe houses, finding places for dead drops, planning hit operations like assassinations that are also carried out by illegals (but from a different department of the same directorate). They also collect sample documents that could be used in other covert operations and update Moscow about some standard proceedings (buying a house, getting a job, registering a company, and so on).
The illegals are no relic, they have been always used full scale. The last known case was in Canada when 'Paul William
Hampel' was arrested in the middle of the Alexander Litvinenko case (November 2006). As I seek to prove in The KGB Poison Factory, the Litvinenko operation itself was the work of a Russian illegal. Certainly, the illegals are used in other countries with difficult counterintelligence environments like Britain, for example, but rarely in "soft" countries like Austria or Finland.
Illegals could be used for corporate and commercial penetration as much as government or military penetration, correct?
Volodarsky: As mentioned above, very seldom, as this is normally not their task. But in many cases their children, born American citizens, are prepared for penetrations. In this group only Mikhail Semenko seems to have made attempts to penetrate sensitive institutions by trying to get a job there (the American Foreign Policy Council, for example). But in one case, a Soviet illegal served as the Costa Rican ambassador to Italy. His detailed story is in The Orlov KGB File, my next book. In principle, corporate and commercial penetration by the illegals is possible - in the 1960s "Rudi Herrmann" was tasked to penetrate the Hudson Institute.
Illegals could also be present in other nations, just like in the Cold War?
Volodarsky: Certainly, and other nationals, not only the Russians, can be used. There are many examples, especially with East Germans.
What is your sense of why they were arrested at this time?
Volodarsky: Two obvious reasons: first of all, Anna Kuschenko-Chapman sensed that she was dealing with an undercover FBI agent, and called her controller from the Russian UN mission; second, 'Richard Murphy' was going to leave for Moscow on Sunday with, some believe, important intelligence.
The Obama administration is on "reset" with Russia. President Medvedev had just left the U.S. Is there a discordant note here?
Volodarsky: Not at all. The Security Service works according to the operational situation disregarding what's going on in the White House and what the President thinks about it.
Anna Chapman has attracted the most public attention of all the accused. Is she a serious spy?
Volodarsky: Everything shows that Anna Vasilievna Kuschenko started to collaborate with the SVR shortly after she finished secondary school at the age of 16 in 1998 and before she entered the university. Her father is a
KGB-SVR officer, possibly from Line N (illegal support), so this would be a normal thing. After a year, she enrolled in a course at the People's Friendship University of Moscow, which is the alma mater of many Soviet and Russian intelligence officers and agents. During her second year, in 2001, she went to London (extremely unusual) and quickly picked up a na�ve young Englishman in a disco. She took him to bed on their second meeting, and by his and another account of her use of sex toys seems to have been specifically trained in the art of love. She told him how much she loved him, burst into tears when leaving for Moscow and quickly arranged an invitation, so he came and they were married in March 2002 without the usual formalities.
After getting settled in London (still being a full-time student in Moscow), she worked in several places for a short time and on small jobs, serving as a personal assistant in a hedge fund, and as a secretary in a private jet company. She dumped her husband after three years, having moved in with a young French playboy who took her to expensive private clubs in London, where she got the right contacts. He also advised her to open an Internet real estate company. In 2004, she miraculously graduated from the university (without studying there and still living in London), returned to Moscow in 2007, opened such an Internet company there, then opened a similar company in New York in February 2010, using $1 million she received from a Kremlin-backed investment fund. Almost immediately she started to send reports to her New York controller using her laptop. It is a big and interesting story worth writing much more.
[Levine/ForeignPolicy/6July2010]
Former Top CIA Spy: How US Intelligence Became Big Business. Few who have seen the dramatic privatization of US intelligence operations from the inside ever speak about the role private contractors play in covert operations - certainly not in public. In late June, however, the CIA's former top counterterrorism official, Robert Grenier, participated in a rare public discussion on issues ranging from the incredible extent to which the US has relied on contractors to fill sensitive national security positions; to battlefield contractors in Afghanistan; to allegations of contractor involvement in "direct action" (lethal) operations, as well as commenting on Blackwater owner Erik Prince's reported involvement in a secret CIA assassination program. The former spy also criticized what he called attempts by the US military to "overstep their bounds" by conducting intelligence operations that traditionally have fallen under the purview of the CIA.
Grenier was undoubtedly one of the US intelligence community's heavy hitters in the aftermath of 9/11. He was CIA station chief in Islamabad, Pakistan when the 9/11 attacks took place and coordinated the initial incursions by CIA personnel and contractors in the first year of the US invasion of Afghanistan. After a stint in what Grenier jokingly called "our excellent adventure in Iraq," where, as chief of the Iraq Issues Group, he planned covert US actions in the lead up to and ultimate invasion of the country, Grenier was named as director of the CIA's Counterterrorism Center (CTC), the unit coordinating the tip of the spear of the CIA's covert activities. In 2006, Grenier left the CIA, reportedly over disagreements with then-CIA director Porter Goss, including the issue of treatment of detainees and prisoners. After leaving the agency, Grenier worked at Kroll Inc., a security consulting firm, and is currently chairman of ERG Partners, a small consulting company.
Grenier and I participated in a frank discussion, along with Professor Katerie Carmola, author of Private Security Contractors and New Wars: Risk, Law, and Ethics, at the International Spy Museum in Washington, DC, where I had a chance to publicly ask Grenier some specific questions.
Grenier estimated that "many more than half" of the personnel who worked under him at the CIA's counterterrorism center were private contractors. Contractors "were coming in and they were all over the place," Grenier said of his time at CTC. "Often I would go down and talk to people in my work force and I would say, 'Hey, that was a great job and I saw what you did last night, I saw that cable that you turned up, thank you very much.' And I'd be startled when they would give me a business card."
It is difficult to access detailed information about the extent to which US intelligence activities are privatized, primarily because the budgets of the eighteen intelligence agencies operated by the United States are mostly classified. In 2007, journalist Tim Shorrock, who wrote the definitive book on the privatization of intelligence, Spies for Hire, obtained and published an unclassified document from the Office of the Director of National Intelligence showing that 70 percent of the US intelligence budget was spent on private contractors. No documents on these classified budgets have been made public since.
Grenier largely defended the use of contractors, primarily because he said he believes that the government, in a time of war, needs to be able to hire skilled, specialized personnel capable of securing the necessary security clearances. "It's far easier to go through the process to get a contractor if time is an issue than it would be to bring somebody on as a regular employee," Grenier said. He said that when he was running CIA operations in Afghanistan immediately after 9/11, he was working with several of his predecessors who had left the CIA, but returned, with their experience and clearances, as independent contractors. Grenier cited another "very prosaic" reason for the reliance on contractors: the federal budgeting process.
Grenier called the system of allocating funds to US agencies the "most illogical process ever devised by the mind of man." He described Congressional funding restrictions that provided huge sums of money to the CIA post-9/11 to purchase goods and services, but not to hire new employees. Instead, he said, Congress provided one year supplemental funding packages to the CIA for "non-personal services." That funding, Grenier asserted, "you can spend for anything."
"You can buy armored vehicles, you can buy drones, or you can buy contractors. Contractors are not considered persons in the context of the federal budgeting process," Genier added. The CIA, therefore, got creative. "So, here was the Congress saying, 'What can we do for you, what can we give you?' Money was not the object - they'd give us anything we asked for and what we got was non-personal services dollars on a supplemental basis. And so, what did we have to do? We went out and bought contractors."
In the early stages of the US war in Afghanistan, Grenier said, many people were hired as individual independent contractors. Then, he says, small companies began popping up that specialized in providing the government and other entities with seasoned veterans of US special forces and intelligence agencies for hire. Within months, companies like Blackwater jumped head first into the rent-a-soldier industry. These companies offered what they called "turnkey solutions" in the war zone.
"Well, they figured out that they could extort - I should say that they could command - more money form the federal government if they somehow banded together," says Grenier, who described the rise of what he called "body shops" providing personnel. "It was like a form of unionization. They got together and they formed these little companies and they could engage in what we might call collective bargaining and thereby raise their salaries."
Shorrock, who analyzes government contracts for an AFL-CIO union, found Grenier's description interesting. "CIA and NSA employees are banned by statute from engaging in collective bargaining. But forming a company might be one way a group of operatives could get a better deal from the CIA on wages, health benefits or insurance," said Shorrock. "That shouldn't be confused with union rights, though."
While Grenier provided a utilitarian rationale for the CIA using contractors, he veered away from discussing the political expediency private forces offer the CIA by providing unattributable forces specializing in plausible deniability.
Several times during our discussion, I asked Grenier about the use of contractors in lethal "direct action" operations, some of which have been characterized as part of a secret CIA assassination program. I specifically asked him about the report in January in Vanity Fair that Blackwater owner Erik Prince had trained a CIA team whose ultimate job would be to "find, fix and finish" suspected terrorists across the globe. Prince's men, according to the article, never "finished" a suspect, but they did do everything but pull the trigger in several countries, including in Germany. Prince claims to have paid for some operations "out of my own pocket."
Many of the activities alleged to have been carried out by Prince and Blackwater occurred while Grenier was director of CTC.
Grenier was visibly uncomfortable discussing the issue of Blackwater and "direct action," saying, "Although some of these things have been revealed and some of what has been revealed is perhaps true and some of it is perhaps untrue and some of it is perhaps exaggerated or misrepresented, but all of it is still classified and so it's difficult for me to speak to it directly to the extent that I know about it." He added: "There were things that frankly were new to me in what I read in that article."
Grenier rejected the notion that Blackwater would have been specifically hired by the CIA for assassination operations, offering a denial that carefully relied on the CIA's contracting process. "CIA would not be soliciting or putting out an RFP [a Request for Proposal] to solicit bids for a company, perhaps for the lowest bidder, to come out and perform services like [direct lethal action]."
While there is little chance that there is a US government contract with Blackwater floating around showing the CIA hired Blackwater to kill people, this type of contracting inherently creates gray areas that ultimately benefit the secrecy of the operations. There is no doubt that Blackwater forces have killed plenty of people in Iraq and Afghanistan and that not all of these "kills" have been defensive security operations.
Without confirming details of Blackwater's involvement in any lethal direct action operations, Grenier did say that to the extent that Prince and his men were potentially involved, they likely were not fully aware of the role they were playing in broader CIA operations. "By [Prince's] own admission those actions have never been carried out," Grenier said. "And certainly, if I had anything to do with it, they would not be carried out by private individuals." He then added: "A Navy SEAL in a buzz cut is probably not the individual that I would put on the street in Ain al-Hilweh refugee camp in Lebanon to do surveillance on a potential target."
What Grenier did describe, in a careful and circumspect way, is a major reason why a company like Blackwater would be hired for involvement in such operations: the combination of experienced personnel and the networks of foreign nationals they cultivated over years of government intelligence work. At the time Grenier was running CTC, Blackwater was flush with well-connected CIA veterans who had vast networks of assets and contacts across the globe. In addition to Cofer Black, Prince counted among his most valued employees Enrique "Ric" Prado, a former CIA paramilitary officer who served as chief of operations for the CTC and Robert Richer, former deputy director of operations at the CIA. All of these men were deeply connected in a wide array of countries where the US was operating under the banner of "the war on terror."
"If, let us say, that one wanted to find individuals, probably foreign nationals who can go out and mount an effective surveillance against a particular target for whatever purpose - intelligence collection or whatever - then you are going to be looking for the right group of individuals who provide you with the right combination of skills that you are seeking," said Grenier. "I just wanted the right people with the right skills doing the job. Depending on the operation and what you want to get done, there really is no standard template. Every time is the first time."
According to Vanity Fair, while Grenier was at CTC, "[Erik] Prince was developing unconventional means of penetrating 'hard target' countries - where the C.I.A. has great difficulty working either because there are no stations from which to operate or because local intelligence services have the wherewithal to frustrate the agency's designs."
Grenier described the value of access to such networks and connections held by some contractors: "It may well be that you're dealing with an individual and let's just say for the sake of discussion that he's a Blackwater employee and perhaps that individual knows some other individual - perhaps foreigners with whom he or she has dealt in the past - that you want to gain access to and bring in on the team. And maybe you want them to know what they're supposed to be doing and maybe you don't. Maybe you're going to have them only partially aware of what they're doing and not aware of what the ultimate purpose for it."
I pressed Grenier on why the CIA might use a company like Blackwater at any stage of a lethal operation instead of using US military special forces teams like those from the Joint Special Operations Command. Grenier pointed to the complicated logistics of preparing such operations. "It's not just a matter of sending in a direct action team, a JSOC squad to go and hit somebody. There's a tremendous amount of preparation, if you will, that has to be done beforehand - most of it having to do with intelligence collection."
As for Erik Prince's claims about his work with covert CIA teams, Grenier said, "The characterization that Erik Prince has provided - to the extent that he fully understood himself what he was saying - I think is easily subject to misinterpretation. I don't know what was in his mind when he spoke."
Overall, Grenier was generally supportive of the use of private contractors, though he did offer some criticisms. He expressed concerned about the "revolving door" between government and the private sector, saying he endorsed moves to ban CIA personnel from returning as contractors less than a year after leaving the agency before official retirement. "Many of these relationships are far too cozy, far too clubby and there are serious risks associated with the revolving door," he said.
He also said he believes that contractors who work with US intelligence agencies should not subsequently or concurrently be working with foreign governments. "I can assure you that if the CIA were employing a contractor who had, thereby, access to very sensitive information, [the CIA] would take a very dim view of that same individual working for that company under a different contract, say, for the Israelis or for some other foreign government," said Grenier.
I asked Grenier about the US military classifying operations that might traditionally be considered intelligence operations, such as US special forces activities in countries like Yemen or Somalia, as "preparing the battlefield," making them a military rather than an intelligence operation. Some critics have suggested that such classification is an attempt to avoid Congressional oversight of certain covert operations. "That's a very interesting dodge," Grenier said. "It has not kept the Department of Defense from trying, at least in my view and the view of others in the intelligence community, to at least to some degree overstep their bounds." Grenier also said Congress "is complicit in it," saying, "One of the things that keeps the military from having to report its intelligence-related activities to the relevant intelligence committees is the very jealous armed services committees who don't want to have their military reporting to these other committees."
The Obama administration has continued the US policy of overwhelming reliance on private contractors at every level of the US national security apparatus and the wars in Iraq and Afghanistan. In Afghanistan, the administration has dramatically increased the number of contractors from Bush-era levels. In Iraq, while the overall US presence is decreasing, the percentage of contractors within the total US force continues to rise. But it is not just on the battlefield. According to a recent Congressional investigation, some 69 percent of all Department of Defense personnel are private contractors. The CIA's recent $100 million contract with Blackwater for "security" services globally is a clear sign that this trend continues unabated at the agency under Leon Panetta.
The Commission on Wartime Contracting recently examined the issue of the use of contractors in sensitive operations at a hearing called, "Are Private Security Contractors Performing Inherently Governmental Functions?" One of the experts who testified, Dr. Allison Stanger, professor and director of the Rohatyn Center for International Affairs at Middlebury College, said that the government use of contractors has become a necessity, rather than a choice, but she painted a sober picture of the implications of the United States using such forces. It "blurs the line between the legitimate and illegitimate use of force, which is just what our enemies want. Al Qaeda's operatives have no country and are private actors waging war on the United States. Terrorists may receive funding from states, but they are by definition non-state actors," Stanger said. "If the United States can legitimately rely on non-state actors wielding weapons to protect our interests, why can't Al Qaeda or the Taliban, especially when contractor misdeeds appear to go completely unpunished?"
[Scahill/TheNation/8July2010]
Ex-KGB General: Soviet Spy Stood Ready to Poison DC's Water. A Soviet "sleeper agent" had orders in the mid-1960s to poison the District's water and to sabotage its power supply if war with the United States became imminent, a former chief of KGB operations in North America said.
The deep-cover spy was inside the United States around 1963 to 1965, "during the Kennedy-Johnson era," said Oleg Kalugin, a former KGB major general who is now a U.S. citizen.
Kalugin said he learned about the operation in the 1970s, when he was moving up the intelligence service's ranks. He would eventually become the KGB's youngest-ever major general.
Kalugin made the revelation during a question-and-answer session at the International Spy Museum. It followed a screening of "Salt," a new spy thriller starring Angelina Jolie.
Afterward, Kalugin told SpyTalk that he had not previously mentioned the sabotage operation in any of his books.
No intelligence official from the period could be immediately located to verify Kalugin's claim.
Kalugin also said the KGB had only "a couple" of long-term, deep-cover agents here in the 1980s,when he was head of North American operations and controlled such infamous American turncoats as John Walker Jr., a U.S. Navy warrant officer who sold Moscow the communication codes used by U.S. submarines.
He called the 11-person Russian spy ring indicted here two weeks ago "a waste of money and time" for Moscow.
[Stein/WashingtonPost/9July2010]
Five Spy Experts Discuss Lessons Learned from the Spy Swap. The arrest and speedy deportation of ten suspected Russian spies in U.S. suburbs has raised concerns about relations between Moscow and Washington, and prompted speculation about methods associated with 21st century spy craft.
Five former members of the U.S. intelligence community offer insight into lessons learned from one of the largest cases of espionage to surface on U.S. soil with the Council on Foreign Relations Greg Bruno.
Eric M. O'Neill, a former undercover operative for the FBI who helped bring down Russian spy Robert Hanssen in 2001, believes that in this most recent case, "Russia took a large risk of political embarrassment" by embedding illegal agents, but thought it would pay off.
Burton L. Gerber, a former CIA chief of station during the Cold War, notes this is because human intelligence sources are still absolutely vital for a country like Russia seeking "to understand the full scope of a competing nation's goals/intentions/capabilities."
Jack Devine, a former CIA deputy director of operations, adds that the details of the case - as cloaked in mystery as they are - suggest a major Russian operation.
And Mark Stout, an intelligence community veteran and historian at the International Spy Museum, says this incident underscores the fact that for many countries, open sources of information will never replace human assets, a point Peter Brookes, a former deputy assistant secretary of defense, concurs with.
Eric M. O'Neill, Partner, the Georgetown Group: The world is growing smaller. Extraordinary advances in information sharing have made distances irrelevant. As the virtual world shrinks, difficulties arise in protecting information. Entire lives are posted on social networking sites. Companies lose trade secrets to regulatory requests, accidental publishing on web pages, and to "dumpster divers" who sort through discarded trash. What we don't volunteer may still fall into the public eye through cybercrime, fraud, and espionage.
The ten Russian "illegal" spies recently arrested and swapped in a historic exchange emphasize that foreign intelligence services continue to rely on human intelligence to feed their voracious need for information. The best spies are people, not machines. To both spy and catch a spy, a person must be able to rely on instinct, experience, and luck, often making decisions based on a gut feeling, something a mechanical device cannot emulate.
The FBI's investigation into the Russian illegal spy network relied on human fieldwork and professional counterintelligence. The ten-year operation to dismantle the spy network suggests a level of severity that is not balanced by the purposefully brief indictment. Numerous experts have cited the lack of an espionage charge to label the illegal spies ineffective amateurs that passed little more than publicly available policy information. Russia took a large risk of political embarrassment by training and embedding illegal agents - a risk that requires more than what is available on Google.
Reading between the lines of the indictment, one finds reference to a more insidious task - recruitment of Americans with access to sensitive policy information. Russia swept the illegals away through a hasty swap only eleven days after the arrest - far too little time for a useful debrief. Time will tell whether the FBI learned enough to truly understand the purpose of the illegal network - perhaps enough to find additional conspirators.
Burton L. Gerber, Center for Peace and Security Studies, Georgetown University: When U.S. officials announced the arrest of ten alleged Russian "illegals," much of the media and other commentary seemed to see this as old stuff, inconsistent with the post-Cold War-age and the reset of Russian/American relations. How serious could this be? What kind of access could these Russians have had? What possibly could they have reported?
Nations still need to understand adversaries, real and potential. While much data and insights are available through other means, intelligence operations, using human officers and recruited agents, are still vital to understand the full scope of a competing nation's goals/intentions/capabilities. And for a nation with the history and tradition of Russia, turning to clandestine collection is second nature.
Russian - and earlier Soviet - intelligence, has usually been noted for its patience. The dispatch of "illegal" officers to establish themselves, develop contacts as appropriate, serve as couriers or support agents, or even [deploy] themselves to get into position to collect important information, is consistent with Russian experience and goals. While their exact technical communications capabilities may not yet be known to us outside observers, it appears they had access to devices/systems that go well beyond traditional dead drops and brush contacts. This was a serious Russian program.
American counterintelligence, the FBI, was on to several of the illegals early, perhaps ten years or so ago, and apparently there were some Russian missteps in the course of those years which caused additional illegals to be identified. Using a support agent to service more than one illegal, as was apparently done, is not sound tradecraft.
While we cannot be sure of the scope of the illegals' success, we can conclude that their pay-off may have been larger than we first can understand, or that the Russian SVR [Russia's foreign intelligence service] was prepared to invest time and resources in the expectation of greater achievement. American counterintelligence impeded this program. Russia and other countries will likely introduce successive ones.
Jack Devine, President, the Arkin Group LLC: Twenty-five years ago, much of what a country's intelligence agencies knew was collected by operatives abroad. Today, much of that information is available instantaneously to anyone with an Internet connection and access to twenty-four-hour news channels. In addition to the problems around verifying data found on the Internet, it contains only as much as people load onto its networks. There is also a great deal of copycat reporting in the press. It is amazing how quickly the media settles into "conventional wisdom," which is often misplaced.
Web sites and the media provide us with easy access to basic information, but the questions of critical importance to intelligence professionals can rarely if ever be answered online. In this regard, computers are no match for human operators and agents in gleaning insights into the plans, intentions, and psychologies of their targets. The United States, other major powers, and very clearly the Russians understand this. All continue to invest in field collection activities. Recently, we've even seen an uptick in the number of smaller, less developed countries funding and fielding collection efforts abroad, including inside the United States.
Instead of questioning the relevance of human agents and operatives in the cyber-era of the 21st century, we should question why the Russians, over the course of ten years, invested so heavily in developing a large network of operatives spanning the American Northeast and Central Atlantic regions. Despite the reported lack of intelligence obtained from the group's operations and their various tradecraft failures, let's not be mistaken about their intended role either; the eleven "illegals" were most likely in the United States to handle American moles. According to what is known publicly, they were to become intermediaries, unconnected from the recruitment process. The Russians either had or anticipated having a large number of American assets to handle and they'd laid in the plumbing for this task with the eleven alleged spies placed strategically outside "hot zones" to avoid detection.
What is baffling is why the SVR would break a cardinal rule of the spy game - always keep your operatives compartmentalized so that the compromise of one doesn't lead to the collapse of the network. Perhaps we should take some satisfaction or comfort from this mystifying oversight, but I remain alarmed by the Russians' optimism about recruiting Americans.
Mark Stout, Historian, International Spy Museum: Americans are so enamored with technology that they often miss the continued relevance of espionage in this age of Google, "Total Information Awareness," signals intelligence, and Predator drones. However, espionage remains an indispensable component of the intelligence capabilities of modern states.
Though their recently thwarted operation may have been feckless, the Russian services - like all serious intelligence services - understand that espionage and other forms of human intelligence can provide nuances that open-source information or technical means often cannot. For instance, an analyst who wanted to know whether Saddam's soldiers would stand and fight would certainly want to have reporting from human sources to provide a feel for morale in the ranks.
As for the vaunted power of open sources, the history of the stealth fighter plane provides a useful cautionary tale. In the early 1980s, everyone knew that the United States Air Force had the first ever stealth fighter, but nobody without a security clearance had ever seen it. However, extensive research in the open sources allowed the Testor model company to sell a 1:48 model of the curvaceous F-19. The models flew off the shelves, and even the impeccably well-informed Tom Clancy was convinced, featuring the F-19 in one of his novels. There was just one problem. There was no F-19. There was an F-117A, but it was angular to the point of ugliness. The open sources were utterly wrong; the real secrets had been kept.
An intelligence service that wishes to have a deep understanding of its adversaries will conduct espionage. Furthermore, an intelligence service which wishes to avoid being deceived will collect intelligence in as many ways as possible. Espionage has been around for thousands of years. It is here to stay. The Russians have been leading practitioners for many years. While this case may well turn out to be an embarrassment for them, other Russian agents could well be stealing serious American secrets right now.
Peter Brookes, Senior Fellow, Heritage Foundation: In the wake of the recent round of U.S.-Russia spy swaps, people are asking: With all the high-tech intelligence collecting gadgets that exist today - from drones to satellites to cybersnooping - who needs a bunch of James or Jane Bonds running around? [The answer]: We do.
Sure, you can get a lot of intelligence from satellites that can practically read license plates or even from translating open-source journals and newspapers, but the human spy still plays a unique role in getting access to privileged information this country needs for its national security. Who is going to "borrow" the briefing book on a country's illicit nuclear weapons plans and programs that will inform American policymaker decisions? A satellite can't do that.
You might respond that you can get that briefing book by hacking into a ministry's computer system and stealing the files. Fair enough, but a drone can't plant the "bug" in the ministry's conference room to listen - live - to discussion on that topic.
Or how about finding the terrorist who doesn't use a cell phone or a computer and who travels around at night concealed in the back of a truck or ambulance? Maybe the spy who has penetrated that terrorist's inner circle can. Good luck recruiting that spy from a laptop.
The list goes on and on of examples of what the human spy can do that the electronic spy can't, ranging from espionage's ridiculous to the sublime. Unfortunately, the world's second oldest profession can be wrought with danger or even national embarrassment under certain circumstances. [But] there is still a robust need for the human spy in the cloak and dagger game.
[MSNBC/12July2010]
Cuban Ex-Intelligence Chief Recalls JFK Assassination. Like many, Fabian Escalante remembers what he was doing when he heard U.S. President John F. Kennedy had been shot: he was trying to stop the Central Intelligence Agency from toppling the Cuban government with the help of anti-Castro exiles.
Years later, when he had risen to head Cuba's Department of State Security, he was well placed to consider whether those same exiles may have had a hand in the November 22, 1963 slaying of the dashing young president in Dallas.
Escalante does not claim to know who killed JFK, but says that Cuban exiles recruited by the CIA had planned to kill Kennedy twice in November 1963, because they felt the U.S. president had done too little to topple the government on the Caribbean island.
"They had the capability, the means and the intent," he said in an interview on the sidelines of the Semana Negra crime writing festival in Gijon, northern Spain.
"How was this meant to turn out? To assassinate Kennedy, launch a furious campaign against Cuba, blaming it for the assassination, which they did, then kill Fidel Castro a few days later, on December 12, and invade Cuba."
Escalante worked with members of the U.S. House Select Committee on Assassinations investigating the JFK killing when they travelled to Cuba in 1978 to collect data on the activities of Cuban exiles.
In his retirement, he has published many of his findings in book form, along with research he has conducted since he set up the Centre for Security Studies in 1993.
Escalante says one anti-Castro exile and former CIA operative who may hold clues to the JFK assassination is Luis Posada Carriles, who lives in Miami and is wanted in Cuba on charges of masterminding the 1976 bombing of a Cubana Airlines jet which killed 73 people.
Posada Carriles is also accused of involvement in a 1997 wave of hotel bombings, which were aimed at destabilizing Cuba and scaring away tourists, but Escalante doubts the U.S. government will deport him to Cuba to face trial.
"He has a life insurance policy, which is what he knows about the Kennedy plot," Escalante said.
"He and (fellow exile) Orlando Bosch were in the thick of the Kennedy plot. Remember, both he and Posada were part of this terrorist mechanism set up in New Orleans, which is where the plot was hatched to assassinate Kennedy."
Now 69, Escalante was just 18 when a revolution led by Fidel Castro took power in 1959. In the next few years, he and other young novices built up a counter-intelligence service from scratch.
He was invited to participate in the Spanish crime-writing festival because organizers say fiction falls short of a world Escalante has uncovered, in which the CIA plotted to make Castro's beard fall off or poison Cubans with infected coins.
Escalante belonged to the Q Section in 1961, which had 50 case officers to thwart the efforts of the so-called JMWAVE CIA base in Florida assigned to conduct sabotage operations in Cuba with a $100 million budget and 4,000 agents.
In his book "Executive Action," Escalante lists 634 conspiracies to kill Castro between 1959 and 2000, including 168 plots which may have succeeded.
He says the closest the Cuban leader came to death was when a CIA agent working at Havana's former Hilton hotel tried to poison a chocolate milk shake Castro ordered.
However, a capsule containing botulin stuck to the side of the freezer compartment in the bar and broke when the agent tried to pry it loose.
Escalante says the Q Section often intercepted false documents sent by the CIA to their agents in Cuba, which were as good as genuine ones, so he used one for himself.
"Security measures for documents in those days were very lax. There was just ordinary paper, a photo, stamp and plastic cover. So that was how I began to drive, with a CIA license."
[Roberts/Reuters/12July2010]
Timeline: Spy Swaps in History. 10 February 1962: Crossing the "Iron Curtain." On the border between West Berlin and East Germany, a US photo-reconnaissance pilot named Francis Gary Powers is exchanged for the reputed director of a Soviet spy cell in the US named Rudolf Ivanovich Abel. Powers' U-2 plane was shot down over the U.S.S.R. in 1960; Abel was arrested in the US in the late 1950s.
"It was a peaceful scene, static and unreal," a Reuters reporter present during the exchange wrote in 1962. "The men, wrapped in winter coats, who stood on the bridge, were in two groups, divided by a white line that was brushed across the tarmac to declare that here was the Iron Curtain."
One group walked Eastwards, the other Westwards, the reporter said. Then they "took off like rockets" in separate limousines.
11 October 1963: Two for two. In a two-for-two swap, a 24-year-old American student arrested while touring Kiev in 1961 and a Jesuit missionary arrested in the USSR in 1941 are exchanged for a Russian couple arrested and held by the U.S. on charges of espionage.
22 April 1964: Berlin border exchange. A British businessman convicted of spying for the U.S. and Britain is exchanged for a Russian army officer who had been imprisoned in Britain in 1961 for allegedly operating a spy ring seeking to gain information about British submarines. The swap, once again, takes place on the West Berlin-East Germany border.
24 June 1969: Handing over the Krogers. Britain releases Peter and Helen Kroger in exchange for Gerald Brooke, a lecturer who had been jailed for spying in the Soviet Union. The Krogers allegedly passed on secrets to Moscow from the Royal
Navy's underwater warfare headquarters in southern England.
30 April 1978: Three-country deal. In a three-way exchange between Mozambique, the U.S. and East Germany, Mozambique releases an Israeli citizen held for two years, the U.S. releases a former Air Force intelligence clerk convicted of
passing secrets to the Soviets, and East Germany releases a Minnesota man arrested for trying to smuggle a German doctor's family to the West.
27 April 1979: The Ginzburg swap. Russia releases five political and religious dissidents for two Russians convicted of spying in the U.S. Alexander Ginzburg - a notable Russian writer and activist - is among the five sent back to New York.
1 October 1981: One for many. Guenter Guillaume, an East German agent who served as a close aide to West Germany Chancellor Willy Brandt, is exchanged for a number of Western spies.
11 June 1985: Largest swap since WWII. Twenty-nine people are exchange din one of the largest swaps since World War II. In the massive exchange, which took place on the Glienecke Bridge between East Germany and West Berlin, four people indicted for spying in the U.S. were exchanged for five Polish prisoners and 20 other
alleged spies held in East Germany and Poland.
30 September 1986: Journalist for U.N. spy. Around three weeks after their respective arrests, American journalist Nicholas Daniloff and accused Soviet spy and United Nations worker Gennadiy Zakharov are released just days apart.
9 July 2010: Suburban spies Russia-bound. In the biggest spy swap since the Cold War, 10 convicted Russian agents were exchanged for four people convicted of spying for the U.S. on an airstrip in Vienna, Austria.
[MSNBC/July2010]
Section
III - COMMENTARY
Defense Department Broadens Congressional Oversight of Secret Programs, by Marc
Ambinder. As House Speaker Nancy Pelosi tussles with the White House over expanded intelligence oversight, the Department of Defense quietly and subtly offered Congress an olive branch last week, setting out a formal procedure for the investigative arm of Congress, the Government Accountability Office, to be granted access to special access programs, or SAPs. The change of policy, contained in a directive issued July 1, was first noticed by the Project on Government Secrecy at the Federation of American Scientists.
Pelosi wants the Government Accountability Office to oversee special access programs across the intelligence community, including those established by the Office of the Director of National Intelligence and the Central Intelligence Agency. The White House has vehemently resisted GAO oversight on the grounds that it interferes with the prerogative of the executive branch to protect national security information.
According to the Pentagon instruction, GAO personnel "shall be granted SAP access if" the director of the DoD oversight committee on SAPs agrees, after receiving a request from the chair and ranking member of either the defense or intelligence committees, and if the GAO employee who would review the SAP has the appropriate security clearance level.
In practice, as Secrecy News notes, GAO personnel who work with Congress on these programs have the clearance level, and regularly undergo a counterintelligence polygraph to keep their clearances current. Previously, the DoD had no formal mechanism for complying with, or refusing, congressional requests to have the GAO investigate its secret programs.
There are three kinds of SAPS - open SAPs, which are acknowledged and reported to Congress in an unclassified manner; black or "closed" SAPs, which are reported to Congress in a classified annex to the Defense Department budget; "waived" SAPs, which are orally briefed to the chairs and ranking members of the intelligence committees, their staff directors, and the chairs and ranking members of the appropriations subcommittee for defense.
Most SAPs involve technology projects. At the Department of Defense there are relatively few SAPs involving sensitive human intelligence collection or exploitation methods. Examples of ongoing non-technology SAPs include interrogation protocols for high-level battlefield detainees in Afghanistan managed by the Defense Counterintelligence and HUMINT Center of the DIA, and every single capability of all of special missions units of the Joint Special Operations Command. One entire government agency, the National Underwater Reconnaissance Office, is protected by a SAP.
SAPs are managed by security officers in charge of "Special Technical Operations." [Marc Ambinder is the politics editor of The Atlantic. He has covered Washington for ABC News and the Hotline, and he is chief political consultant to CBS News.]
[Ambinder/TheAtlantic/7July2010]
Why Doesn't the FBI Prosecute More Spies? The Logic Behind Swapping the Russian Agents Rather Than Bringing Them to Trial, by Asha
Rangappa. After a tantalizing two weeks involving the arrest of 10 Russian intelligence agents in three U.S. cities, the anticlimactic denouement came yesterday with a spy-swap deal between the United States and Russia in which the accused spies will go free after spending just 10 days in jail. It may seem odd to end a 10-year investigation on suspected foreign agents this way, even if their intelligence amounted to Google searches and pool-party gossip. But given the way the FBI normally deals with spies, putting them in jail probably wasn't its only goal in the first place.
Relative to the large number of foreign spies tracked and monitored by the FBI, very few are brought to light through criminal prosecution. This is partly due to the limited number of laws against spying. Apart from the federal espionage statute, which requires prosecutors to prove the intentional passage of classified information, the only law against spies (and the one under which the latest Russian agents have been charged) is the Foreign Agent Registration Act. FARA requires anyone acting on behalf of a foreign government to register as a foreign agent with the Department of Justice. If you're caught breaking the law, the penalty is fairly weak: five years in prison. Only four criminal cases have been brought under the statute since 1966. The dearth of spies prosecuted under either the espionage statute or FARA reflects the FBI's reluctance to lay all of its cards on the table, which is what it generally has to do at trial in a criminal case.
In the game of spy vs. spy, the FBI's strongest weapon is keeping its adversary from knowing what it knows. The investigation into the 10 Russian spies shows that Russia's foreign intelligence service, the Sluzhba Vneshney Razvedki (successor to the KGB) apparently felt confident that it was operating undetected. Working under this assumption, the SVR unwittingly enabled the FBI to collect a steady stream of information on the SVR's agents, contacts, interests, and capabilities. By staying behind the scenes, the FBI ensured that the SVR was giving up all these goodies for almost 10 years.
Criminal cases, by contrast, are public, and unless a judge chooses to seal sensitive evidence, they require the government to present exactly what it knows. The criminal complaint against the Russian spies, many note, reads like a Cold War spy thriller, complete with secret rendezvous, false identities, and messages written in invisible ink. For the Russians, though, it should read more like a McKinsey report for how the SVR can improve its game. The complaint names - or, in spytalk, "burns" - the specific FBI agents who conducted this investigation. While FBI counterintelligence agents normally operate overtly - meaning that they don't have to hide the fact that they are with the FBI - they generally do not reveal the country whose agents they are targeting. Now that the complaint has revealed the identities of the SVR's adversaries, the Russian intelligence service can keep an eye out for the specific agents working against them in the United States. (The FBI could, of course, counter-counter-counter by moving these agents to a different target, but given their institutional knowledge and Russian expertise, that would be a loss for our intelligence capabilities).
More significantly, the complaint reveals what the FBI knew about the SVR's tactics and tradecraft. For instance, the FBI learned that in addition to old-school techniques like the "brush pass" (casually exchanging bags between two people while passing), the Russians were using Web imaging encryption software to encode secret messages into ordinary pictures on the Internet, a technique known as steganography. Discovering and decrypting this software allowed the FBI to analyze more than 100 coded text files related to this investigation and likely more communications related to other classified investigations. Now that the SVR knows we know, it will no doubt improve its codes, or abandon this technique entirely, drying up a potential intelligence source for the FBI. (Other, less sophisticated notes to self for future SVR spies include not using bright orange bags, mentioning "Siberia" in conversations, or throwing cell phone receipts into the garbage.)
Despite the information it reveals to the other side, criminal prosecution has been necessary and inevitable to stop exchanges of highly classified information such as the secrets passed on to the Russians by former FBI agent Robert Hansen. Still, even that case revealed more about the FBI's own shortcomings than about the Russians. After all, as a Russian counterintelligence agent himself, Hansen had the knowledge and training to outmaneuver the traditional techniques of his FBI colleagues for almost two decades. The investigation into his activities gave the FBI guidance on internal security loopholes that needed to be fixed. The FBI adapted accordingly, enhancing its computer security and requiring regular financial disclosures and polygraphs of its agents.
Trading the Russian spies makes sense to ensure that the FBI doesn't leak any more than it already has. But in light of what the FBI lost to the Russians with Hansen, officials must have thought carefully before making the decision to arrest the spies at all. The FBI's Russian counterintelligence program is the agency's oldest and the most protective of its methods and sources. Its agents were well-aware that they were killing (or at least maiming) the goose with the golden eggs by making this case public, and only an anticipated benefit would justify the injury. One possibility is that the arrests were necessary to force the SVR to shut down other activities that pose a greater threat to national security - one that the American public will never know about. Another may be that these arrests will serve to as an example to more important spies on the FBI's radar and help persuade them to work for us as double agents rather than risk being sent home, or to jail. What is certain is that the FBI must have thought it had more to gain than lose - otherwise, the normal course of business would have been to let the spies continue their charade, at the Russians' expense. [Rangappa/Slate/10July2010]
Spy Swap Was a Mistake, by Gene Coyle.
[Gene Coyle is a retired, Russian-speaking, 30-year veteran of the CIA, who specialized for most of his career on Russian affairs. He is a recipient of the CIA's Intelligence Medal of Merit. He is now an adjunct professor at Indiana University and the author of two spy novels.] The Obama administration's rush to sweep the recent Russian spy scandal off the table as quickly as possible with this swap is a bad move on several counts.
It is understandable and correct that President Barack Obama values the overall U.S.-Russian relationship above the question of whether a few Russian spies spend years in jail.
The "reset" campaign was an excellent idea; too bad no one in our Department of State knew how to correctly spell the word in Russian when Secretary Hillary Clinton presented the "button" to the Russian Foreign Minister. However, there is a line between seeking a mutually beneficial relationship and delusional pandering.
The history of U.S.-Russian relations shows that dealing respectfully but firmly is what works best. Most importantly, Moscow only agrees to anything that it perceives to be at least 50 percent in its self-interest, not because we've been nice guys. The only thing releasing all of these deep-cover Russian intelligence officers within a matter of days is going to teach Prime Minister Vladimir Putin, an old KGB officer, is that Obama is a pushover - overly focused on making sure not to offend Russia.
Aside from sending the wrong political message, the quick swap also tells the leadership of the Russian government and the SVR, its intelligence service, that there is really no downside to being caught carrying out espionage in America.
Any intelligence service in the world, including Russia's, when deciding whether to carry out a particular espionage operation looks at the "risk factor." What will be the blow back if this becomes known?
Running "illegals" - that is, Russians posing as citizens from a third country and who have no overt connection to the Russian embassy or consulates in America - would usually be considered a high-risk operation by Moscow because those Russian citizens don't have diplomatic immunity if caught. It's bad press and it's bad for morale within the SVR if one, much less 11, of your deep cover officers get caught and are facing decades in prison. But Obama has now just told the SVR, "Hey, there is no penalty for spying in America. If we catch you, we'll just let you go so as not to damage 'big picture' relations."
We did show Russia certain appropriate courtesies in these arrests, which would have indicated we didn't want to harm our political relationship with Russia.
We waited until Russian President Dmitry Medvedev had made his visit to America. We waited until after the G20 meetings in Canada. We haven't even publicly named or expelled the Russian diplomats who were apparently observed being involved in the communications with these illegals. (Hopefully, the Department of State has at least told the Russian ambassador that certain of his diplomats should quietly leave America.) And speaking of morale, what message does this send to the hundreds of FBI special agents who spent thousands of hours working these cases?
According to various press accounts, the number of Russian intelligence officers in America and Western Europe has already returned to Cold War levels. Obama has now told the Russians, there isn't even a problem if we catch you. Try anything you want.
Normally, when any intelligence service has a major flap as this was, it would order an immediate stand down of other operations in that country for perhaps several months while it tried to figure out what had gone wrong. By immediately sending these SVR officers back to Moscow, they will be available to assist in that investigation.
Not knowing what all they were involved in - it was certainly more than "penetrating the local PTA" - I don't necessarily advocate having kept these people in prison for decades, but a year or two in prison before offering a swap would have sent a strong message to Putin and the SVR. And if the press accounts are accurate, getting four people out of Russian jails in return for these 10 doesn't seem like much of a bargain either. (An 11th suspect detained in Cyprus remains on the loose after being released on bail.)
Obama is no doubt an intelligent fellow, but he certainly didn't get very good advice from his intelligence community or Russian experts about how to handle this spy caper.
[Coyle/CNN/11July2010]
Section
IV - OBITUARIES AND COMING
EVENTS
Obituaries
Sergei Tretyakov: Former Russian Spy Defected to U.S. in 2000. Sergei Tretyakov, a high-ranking Russian spy whose defection to the United States in 2000 was regarded as one of the most significant coups against the Russian government since the collapse of the Soviet Union, died June 13 at his home in Osprey, Fla.
Mr. Tretyakov's wife said he died after suffering a heart attack, according to Pete Earley, the author of a book about Mr. Tretyakov. The former Russian spy was 53 and news of his death was withheld at the request of his family pending an investigation into the cause, Earley said.
"This man literally held the keys to a Russian intelligence gold mine," an unnamed FBI official was quoted as saying in Earley's 2007 book, "Comrade J: The Untold Secrets of Russia's Master Spy in America After the End of the Cold War." "He used those keys to unlock its doors and go into the mine every day to bring us nuggets."
Mr. Tretyakov was born into a spying family and rose through the ranks of Russian intelligence to become a colonel in the SVR, the successor to the Soviet KGB espionage agency.
At the time of his defection on Oct. 11, 2000, Mr. Tretyakov allegedly had been working as a double agent for the United States for three years while he was the SVR's second-in-command in New York. From 1995 to 2000, he oversaw all Russian covert operations in the city and had more than 60 intelligence officers under his command, according to Earley's book.
The intelligence Mr. Tretyakov handed over during his time as a double agent amounted to more than 5,000 top-secret SVR cables and scores of classified Russian intelligence reports. He wrote an estimated 400 papers for the CIA, the FBI, the State Department and the White House.
For his efforts, Mr. Tretyakov and his family were given U.S. citizenship, and he reportedly netted the highest amount ever paid to a U.S. intelligence source - a fortune that was said to be in the millions of dollars, which he used to buy himself a Lexus SUV and his wife a Porsche.
Sergei Olegovich Tretyakov was born in Moscow on Oct. 5, 1956. His grandmother was a typist and secretary in the forerunner of the KGB. His father worked in the Soviet nuclear weapons program, and his mother worked in the financial office of the KGB and helped her son gain entry into the spy service.
Mr. Tretyakov was born with a heart defect that would have denied him entry into the KGB, but his mother bribed a doctor to leave the condition out of his application to the agency.
When the ruse was discovered, his commander recognized that Mr. Tretyakov's skill at beating the system suggested great potential as a spy.
Early in his career, Mr. Tretyakov impressed senior officers by analyzing seemingly innocuous, and unclassified, U.S. reports and gleaning valuable intelligence from their pages.
In one instance, he was able to extrapolate from a congressional report on U.S. military installations which types of aircraft could land at certain bases, judging from the length of their runways.
He was dispatched to Ottawa on his first overseas assignment in 1990 and was known under the code name "Comrade Jean." There, he recruited several high-ranking Canadian officials, allegedly including a member of Parliament.
In Earley's book, Mr. Tretyakov revealed much of the SVR's structure, including technical details about operations and the identities of agents and sources. He also revealed that his agents had skimmed $500 million in profits for the Russian government from the U.N. oil-for-food program in Iraq.
He claimed to have unmasked dozens of SVR undercover agents, including several ambassadors and U.N. representatives, but despite the sweeping accusations, no one cited by Mr. Tretyakov has been charged with espionage.
Many critics said Mr. Tretyakov exaggerated his persona as a good guy, but he never denied his role within the ruthless intelligence agency, saying, "I'm not a Boy Scout."
Newspaper accounts speculated that Mr. Tretyakov had taken part in outing FBI double agent Robert Hanssen in 2001 and in the recent arrests of Russian agents living deep undercover in the United States for more than a decade. But Earley said that Mr. Tretyakov never admitted to being the Hanssen source and that he apparently had no role in the investigation of the spy ring.
Survivors include his wife, Helen, and a daughter, Ksenia, both of Osprey.
Earley, a former Washington Post reporter, said he was skeptical of Mr. Tretyakov's motivations when he first met the former spy. But Mr. Tretyakov said he came forward only because of his disgust with the Russian government.
"Of course I want people to know what I have done," Mr. Tretyakov told Earley in the book. "However, most Americans can't pronounce Tretyakov, nor will they remember the name for longer than a few seconds."
[Shapiro/WashingtonPost/10July2010]
Arnold Kramish: Physicist Worked on Manhattan Project. Arnold Kramish, 87, a physicist, historian and author who worked on the Manhattan Project during World War II, died June 15 at George Washington University Hospital of normal pressure hydrocephalus, a neurological disorder.
Mr. Kramish participated in the Manhattan Project, the U.S. program to develop the atomic bomb, as a member of the special engineering division at Oak Ridge, Tenn., the Philadelphia Navy Yard and Los Alamos, N.M.
On Sept. 2, 1944, he was severely burned during an explosion at an experimental uranium enrichment facility at the Philadelphia Navy Yard. According to Mr. Kramish, who described the accident in an article published in The Washington Post, the result was "perhaps then the largest release in history of radioactive materials."
Two men were killed in the blast, and the cause of their deaths was kept confidential to avoid leaking information about the top-secret bomb project. Years later, Mr. Kramish campaigned for official recognition of their contributions to the war effort.
After the war, Mr. Kramish served with the Atomic Energy Commission and later as a nuclear weapons research strategist at the Rand Corp., a Santa Monica, Calif.-based think tank that often advised the government.
During the 1970s, he was posted in Paris as a State Department counselor, and he served as nuclear arms control and security adviser to UNESCO and the Organization for Economic Co-operation and Development.
He wrote "The Griffin" (1986), a biography of Paul Rosbaud, an Austrian spy who during World War II provided the Allies with information about Nazi attempts to build an atomic bomb.
In a Washington Post review of the book, author and historian Gregg Herken wrote, "Despite Kramish's careful research, which included interviews with approximately 500 of those who knew Rosbaud, it is an ironic tribute to this bookish spy's mastery of his trade that the Griffin remains a surprisingly shadowy figure, one who continues to defy the effort to capture him."
Arnold Kramish was born in Denver on June 6, 1923. He graduated from the University of Denver in 1945 and received a master's degree in physics from Harvard University in 1947.
He moved frequently for his career, settling in Reston in 1976.
During the Reagan administration, Mr. Kramish directed a White House study on the Strategic Defense Initiative and served as an adviser to the undersecretary of defense for policy. He received a Carnegie Fellowship and a Guggenheim Fellowship, and was a fellow at the Woodrow Wilson International Center for Scholars.
Mr. Kramish taught courses at the University of California at Los Angeles, the London School of Economics and other institutions.
His books included "Atomic Energy in the Soviet Union" (1959), "The Peaceful Atom in Foreign Policy" (1963) and "The Future of Non-Nuclear Nations" (1970). He held a patent for a nuclear radiometer.
Mr. Kramish was a member of the Northern Virginia Hebrew Congregation and the Authors Guild.
Survivors include his wife of 57 years, Vivian Raker of Reston; two children, Pamela Jones of Hickory, N.C., and Robert Kramish of Berkeley, Calif.; a sister; and four grandchildren.
[Brown/WashingtonPost/10July2010]
Coming
Events
EVENTS
IN COMING
TWO MONTHS....
MANY Spy Museum
Events in August
with full details are listed on the AFIO Website at www.afio.com. The
titles for some of these are as follows:
- Thursday, 15 July 2010; 12 noon – 1 pm - Washington, DC -
"Eyes in the Sky: Eisenhower, the CIA, and Cold War Aerial
Espionage"
at the International Spy Museum
- Thursday, 5 August 2010, noon - Washington, DC - "Silent Sentry:
The Untold Story of the National Security Agency" - at the
International
Spy Museum
- Wednesday, 11 August 2010, 6:30 pm - Washington, DC - "Uneasy
Alliance: The CIA and ISI in Pakistan" - at the International Spy
Museum
Thursday,
15 July 2010, 11:30 am - Colorado Springs, CO - The Rocky Mountain
Chapter hears Tim Murphy on R&D Platform Usage in Intelligence.
The Chapter presents an expert on Special Ops whose firm is doing an
R&D intelligence platform for the Intelligence community. Retired
Air Force Col. Timothy Murphy, High Altitude Balloon Surveillance,
Vice President, Star Tower Division, Global Near Space Services
(GNSS),
who is also a graduate of the Air Force
Academy. To be held at a new location the AFA Eisenhower Golf Course
Club House. Please RSVP to Tom VanWormer at robsmom@pcisys.net.
16, 23 July 2010, 8 and 10 pm - Washington, DC - THE SPY MAGIC SHOW -
An
incredible exploration into the secrets of spies, shown through
stunning sleight-of-hand magic by master magician Michael Gutenplan.
Michael Gutenplan, an expert in sleight-of-hand magic is about to
expose the secrets of the CIA and you are invited to watch! In an
intimate room at the famed Ritz Carlton Hotel in Washington, D.C.,
Michael will perform world-class magical effects and tell how
magicians
and the CIA have worked together since its creation in 1947. Using
cards, money and mind reading Michael will expose the secrets and
skills
that have only been rumored to exist. From thought transference and
teleportation to lie detection and invisible ink, Michael will
transport
you to another world where fact and legend go hand- in-hand and spies
are around every corner. Grab a drink, have a seat and join us for
this
once in a lifetime event!
Tickets can be purchased through www.spymagicshow.com or by calling 1-866-811-4111. All tickets are $40.00.
The Spy Magic Show plays Friday, July 16 and 23rd at 8:00 PM and
10:00 in the Roosevelt Room at the Ritz Carlton, located at 1150 22nd
Street, N.W., Washington, D.C. 20037
Michael Gutenplan is a professional magician originally from New York
and now residing in Los Angeles. He has performed his signature brand
of
magic around the world including in Great Britain, Spain, Israel,
Jordan and across the United States. He was the creator and star of
Extraordinary Deceptions, an Off-Broadway magic show that earned
Michael
rave reviews in the New York Times, Variety and other prestigious
publications.
Wednesday, 21 July 2010, 10 am - 12:45 pm - Annapolis
Junction, MD - "The Mysterious Rosetta Stone: A Code-Cracking
International Treasure" with Dr. Joel Freeman, is topic at the
National
Cryptologic Museum Foundation Summer Cryptologic meeting.
All AFIO members are invited to hear our guest speaker, Dr.
Joel Freeman, CEO and President of the Freeman Institute,
discuss the history of the Rosetta Stone, focusing on the historical
connection between the Rosetta Stone and the breaking of codes.
Guests
will have an opportunity to view the full-sized, three-dimensional
Rosetta Stone replica normally on display in the lobby of the National
Cryptologic Museum. Dr. Freeman is an gifted speaker and author. As
part
of the program there will be a brief presentation to acknowledge the
Milt Zaslow Memorial Award for Cryptology that was presented for the
first time at this year's Maryland History Day Ceremony on 24 April.
Location: the L3 Conference Center in the National Business Park.
Lunch will be served at 11:45 following the presentation. L3
Conference
Center is located at 2720 Technology Dr, Annapolis Junction, MD 21076
in
the Rt. 32 National Business Park.
Cost: the fee is $25 to cover program & lunch costs.
Confirm your attendance by Wednesday, 14 July, by calling (301)
688-5436
to pay by credit card or by mailing a check to NCMF, POB 1682, Ft.
Meade, MD 20755. We look forward to seeing you there.
22
July 2010 – San Francisco, CA – The AFIO Jim Quesada San Francisco Chapter hosts
John
Yoo, former deputy assistant attorney general in the Office of Legal
Counsel of the U.S. Department of Justice, where he worked on national
security and terrorism after the September 11 attacks.
John Yoo is currently a professor of law at UC Berkeley. Yoo will
be discussing his new book, Crisis and Command: A History of Executive
Power from George Washington to George W. Bush. RSVP and pre-payment
required. The meeting will be held in San Francisco: 11:30 AM no host
cocktails; noon - luncheon. $25 member rate with advance reservation
and
payment; $35 non-member. E-mail RSVP to Mariko Kawaguchi (please
indicate chicken or fish): afiosf@aol.com and mail check made out to
"AFIO" to: Mariko Kawaguchi, P.O. Box 117578 Burlingame, CA 94011
24 July 2010 - Abilene, KS - Korea
60: Eisenhower the Peacemaker - Honoring Those who Served in Korea - CIA
joint conference at Dwight D. Eisenhower Presidential Library and
Museum, Abilene, Kansas
The Eisenhower Presidential Library and Museum will host a day of
programs on July 24 to honor the service of Americans who have served
in
the Republic of Korea from 1950 to the present.
The day begins with a presentation by intelligence agency historians
and ends with dinner and entertainment. All events are free and open
to
the public with the exception of the dinner, which costs $20 per
person.
The schedule is as follows: Eisenhower, Intelligence, and Korea
Visitors Center Auditorium, 10:30 a.m. - noon -Dr. Clayton
Laurie, CIA "Baptism by Fire: CIA Analysis of the Korean War"
-Dr.
David Hatch, NSA historian, "DDE and COMINT: Astute Consumer
and Agent of Change" The Korean War was the Agency's first role in an
international conflict. The opening of classified material as featured
in the "Baptism By Fire" book will contribute significantly to the
historic record of the Korean War, making possible new research and
great understanding of early Cold War history.
Korean War and Service Veterans Panel Discussion Visitors Center
Auditorium, 1 to 2:45 p.m. The panel will feature Dr. Paul
Edwards, Director Emeritus, Center for the Study of the
Korean
War, as moderator. Panel members include veterans who have served in
Korea at various times from the 1950s to the 1990s.
Keynote Address | Lt. Gen. Robert Arter, U.S. Army (Ret.) Presentation of Eisenhower Peacemaker Coins Visitors Center
Auditorium, 3 to 4:30 p.m.
Keynote speaker retired Lt. Gen. Robert Arter is a veteran of the wars
in Korea and Vietnam and former commander of the U.S. Sixth Army.
Arter
is a Civilian Aide to the Secretary of the Army, and a consultant and
bank director. In 2009 he received the Distinguished Civilian Service
Award for his work as a Civilian Aide. It is the highest award a
civilian can receive from the Army.
The Eisenhower Peacemaker Coin is available to Korean War veterans and
all those who have served to keep the peace in Korea since the signing
of the armistice on July 27, 1953. (Coin recipients or their
representatives MUST be present at the ceremony.) If you or a loved
one
served in Korea and are able to attend the ceremony, sign up to
receive
the Eisenhower Peacemaker Coin.
Reception and Dinner 5:30 p.m. Social | Library Lobby 6:00 p.m.
Dinner | Library Courtyard Cost is $20 per person and includes the
remarks by retired Maj. Gen. Singlaub and
entertainment
by Ray Marco. RSVPs required by July 16. Please send check, made
payable to Eisenhower Foundation, to P.O. Box 339, Abilene, Kan.
67410.
Remarks | Maj. Gen. John K. Singlaub, U.S. Army (Ret.) -
Singlaub is a veteran of WWII, Korea and Vietnam. From July 1976 to
June 1977 he served as Chief of Staff, United Nations Command, U.S.
Forces Korea. He is recipient of many decorations and awards. His
autobiography, Hazardous Duty, was published in 1991.
Entertainment | Ray Marco Mr. Marco is a veteran
performer of the stage, television and motion picture screen. His 1956
hit "Abilene" was the unofficial campaign song for President
Eisenhower's successful re-election. Mr. Marco is a veteran of the
U.S.
Air Force Security Service.
This program is in partnership with the Harry S. Truman Library and
Museum. Please visit the Truman Library web site at www.trumanlibrary.org for a full schedule of events. The Truman Library programming focuses
on the early time period of the war while the Eisenhower Library
focuses
on the latter time period and years since the signing of the
armistice.
This program is sponsored by the Eisenhower Foundation and
Duckwall-ALCO Stores, Inc. It is dedicated to President Eisenhower's
successful conclusion of the conflict on July 27, 1953.
28 July 2010, 9 am - 5 pm - Miami, FL -
INFRAGARD South Florida and the FBI invite AFIO MEMBERS to their
South
Florida Conference
Location: Florida International University, Management Advanced
Research Center, Room # 125, 11200 SW 8th St, Miami, FL 33199
Speakers: Eric S. Ackerman, PhD, InfraGard South Florida Chapter
President, Stewart L. Appelrouth, CPA, InfraGard Treasurer, SA Nelson
J.
Barbosa, InfraGard Coordinator/FBI Miami
Sam Fadel, Florida Regional Field Investigator, Corporate Security
Department, This presentation will focus on data breach
investigations,
specifically credit card/account number breaches. Defines the roles of
the issuers, law enforcement and forensic experts.
SA Kathleen J. Cymbaluk, Miami FBI Recruiter on FBI Employment Needs.
This presentation will discuss current hiring needs of the FBI and
requirements on how to qualify and apply.
Stewart Appelrouth and Ed Farath, CPA, Appelrouth/Farah & Co.,
P.A., This presentation will focus on Financial Fraud, Specifically
Ponzi Schemes.
Richard Wickliffe, Team Manager, Special Investigation Unit, State
Farm Insurance Companies, Will discuss Fraud, White Collar Financial
Issues- and Possible Counterterrorism Implications.
Randall C. Culp, Supervisory Special Agent, FBI, This presentation
will discuss Health Care Fraud – Adapting Investigations and
Prosecutions to deal with emerging trends.
Gun Running from Broward and Palm Beaches Counties - Mark A.
Hastbacka, Supervisory Special Agent, FBI, This presentation will
touch
on IRA gun running operation in the above counties from a
counterterrorism investigation point-of view
RSVP TO Nelson Barbosa at FBI Miami Field Office:Nelson.Barbosa@ic.fbi.gov
Saturday, 31 July 2010, 10 am - 12 noon - Coral Gables,
FL - AFIO/Miami Police Department Counter-Terrorism Training. In cooperation with the City of Miami Police Dept, Office of Emergency
Management & Homeland Security, Officer Marcos T. Perez, AFIO will
be presenting a Counter-Terrorism Training and Program. "Operation
Miami
Shield." There is limited space available for this program.
Please RSVP with checks enclosed before July 21, 2010. There is a $10
charge for AFIO Members. Guests will be charged at $25 per person.
Checks payable to "AFIO" and mailed to Tom Spencer at 999 Ponce de
Leon
Blvd Ste 510, Coral Gables, FL 33134
Saturday, 14 August 2010, 11 am - Orange Park, FL - AFIO Northern Florida Chapter hears expert on technology capabilities of FBI/DEA/ATF regarding air travel.
Social hour from 11:00 am, lunch at noon, and speaker and meeting to follow until 3:00 pm. This meeting's guest speaker will be Mr. Bob DeFrancesco, Security Chief at Jacksonville International Airport. In concert with Ken Nimmich, DeFrancesco will delve privately and confidentially into the technology requirements and capabilities of his systems. He will address successes and failures of both the technology and the dependency of interagency regimes, including the FBI, DEA, ATF, etc. Also in preparation for the meeting, there will be a review of the Nova video on NSA (www.youtube.com/ watch?v=ZWtEp3fLLvo) and 9/11 (www.youtube.com/ watch?v=8EiiZUUGQyI) ramp up from an interagency perspective. Chapter President Dane Baird applauds Bill Webb on this effort and hopes all members can watch the videos, twice if possible, prior to the meeting. Hopefully these are the right YouTube links to access these videos - let me know if not! For potential upcoming meetings, President Baird has uncovered some impressive resumes of generals and admirals living within reach of Ponte Vedra, including one who flew with the Nationalist Chinese Air Force. Think about it, and let us know if a special China program would be interesting – and we're sure that Bill could certainly enhance and enlighten such presentation(s).
RSVP right away for the 14 August 2010 meeting to Quiel at qbegonia@comcast.net or 904-545-9549. The cost will be $16 each, pay the Country Club at the event.
17 - 20 August 2010 -
Cleveland, OH - AFIO National Symposium on the Great Lakes
- "Intelligence and National Security on the Great Lakes"
Co-Hosted with the AFIO Northern Ohio Chapter at the Crowne Plaza
Hotel, Cleveland, OH. Includes presentations by U.S. Coast Guard on
Great Lakes security; Canadian counterparts to explain double-border
issues;
National Air/Space Intelligence Center; Air Force Technical
Applications Center; Ohio Aerospace Institute.
Cruise on Lake Erie
.
Spies-in-Black-Ties Dinner and Cruise on Lake Erie. Make your
reservations here. Agenda here.
Saturday,
25 September 2010, 10:30 am - Coral Gables, FL - "Management of Kidnap
and Extortion Incidents" the topic at the AFIO Miami Chapter event. This program is a seminar conducted by a former Intelligence Officer
expert in the subject. More details to follow soon or email trsmiami@aol.com
29-30
September 2010 - Washington, DC - Conference on the American
Experience
in Southeast Asia, 1946-1975 by the U.S. Department of State.
The U.S. Department of State's Office of the Historian is pleased to
invite AFIO members to a conference on the American Experience in
Southeast Asia, 1946-1975, which will be held in the George C.
Marshall
Conference Center at the State Dept. The conference will feature a
number of key Department of State personnel, both past and present.
Those speaking will include:
* Former Secretary of State Henry A. Kissinger
* Former Deputy Secretary of State John D. Negroponte
* Special Representative for Afghanistan and Pakistan Richard A.
Holbrooke
The conference will include a panel composed of key print and
television
media personnel from the Vietnam period discussing the impact of the
press on public opinion and United States policy. A number of
scholarly
panels featuring thought-provoking works by leading scholars will also
take place. Registration information will be available at the State
Dept
website, http://history.state.gov,
after August 1.
Saturday, 2 October 2010, 6:30 pm - Washington, DC - William J. Donovan Award Dinner Honoring Ross Perot by The OSS Society
The OSS Society celebrates the historical accomplishments of the OSS during WWII through a William J. Donovan Award Dinner. This year the annual dinner honors Ross Perot. Event includes special performance by humorist Mark Russell. Black Tie/Dress Mess. Location: Mandarin Oriental Hotel, 1330 Maryland Ave SW, Washington, DC. By invitation. Tables of ten: $25,000; Table of ten: $15,000; Table of eight: $10,000; Table of Six: $5000; Seating of four: $3,000; One guest: $1,000. Some tickets available for $175 pp. Donations welcomed. Inquiries to The OSS Society at oss@osssociety.org
For
Additional Events
two+ months or greater....view our online Calendar of
Events
-----------------------------------------------------------------------
Disclaimers
and Removal Instructions
Weekly
Intelligence Notes (WINs) are commentaries on Intelligence and related
national security matters, based on open media sources, selected,
interpreted, edited and produced for non-profit educational uses by
members
and WIN subscribers.
REMOVAL
INSTRUCTIONS: We
do not wish to add clutter to inboxes. To discontinue receiving the
WINs:
a)
IF YOU ARE A MEMBER -- click here: UNSUBSCRIBE and supply your full name and email
address
where you receive the WINs. Click SEND, you will be removed from
list.
If this link doesn't open a blank email, create one on your own and
send to afio@afio.com with the
words: REMOVE FROM WINs as the subject, and provide your full
name and
email address where you are currently receiving them.
b)
IF YOU ARE NOT A MEMBER, and you received this message, someone
forwarded this newsletter to you [contrary to AFIO policies]. Forward
to afio@afio.com the
entire WIN
or message you received and we will remove the sender from our
membership
and distribution lists. The problem will be solved for both of us.
CONTENTS
of this WIN [HTML version recipients - Click title to jump to story or
section, Click Article Title to return to Contents. This feature does
not
work for Plaintext Edition or for some AOL recipients]. If you wish to
change to HTML format, let us know at afio@afio.com. The HTML feature also does not work
for
those who access their e-mail using web mail...however NON-HTML
recipients
may view the latest edition each week in HTML at this link: https://www.afio.com/pages/currentwin.htm
-----------------------------------------------------------------------
WINs
are protected by copyright laws and intellectual property laws, and
may
not be reproduced or re-sent without specific permission from the
Producer. Opinions expressed in the WINs are solely those of the
editor(s)
or author(s) listed with each article. AFIO Members Support the AFIO
Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for
back issues of the WINs, information about AFIO, conference agenda
and
registrations materials, and membership applications and much more!
(c)
2010, AFIO, 6723 Whittier Ave Suite 200, McLean, VA
22101. Voice: (703) 790-0320; Fax: (703) 991-1278; Email: afio@afio.com
Click here to return to top.