10-16 May 2023
(Issue 19)
is sponsored by

Readers who encounter problems with the email version of this newsletter can
view the latest web edition here.
| Visit us on |
CONTENTS
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
- Captain James D. Stallings to be Honored on National Cryptologic Memorial Wall - NSA, 12 May 23
- She was a Muslim spy at the forefront of CSIS’s fight against terrorism. Then, she turned whistle blower - The Star, 12 May 23
- Former intelligence officer, Russia expert was asked to smear Germany to regain his freedom - Nordic Monitor, 08 May 23
- How a Secretive Swiss Dealer Is Enabling Israeli Spy Firms - Haaretz, 14 May 23
- Lankans victim of India based cyber espionage? - The Island, 09 May 23
- Israel’s Spying on Palestinians Is So Pervasive It Would Shame Some Dictatorships - The Daily Beast, 06 May 23
- Bipartisan Group Looks to Fix ‘Hopelessly Obsolete’ Classification System - Government Executive, 10 May 23
- Austin explains why the US isn't sharing intelligence on alleged Russian war crimes - Washington Examiner, 11 May 23
- Avril Haines: New ODNI Office Oversees Intelligence Community’s Fight Against Disinformation - Executive Gov, 08 May 23
- NSA Releases New Best Practices for Securing Home Networks - Security Intelligence, 10 May 23
- Under fire, CIA moves to overhaul its handling of sexual assault - Politico, 11 May 23
- DHS Intelligence Rearranges the Deck Chairs—Again - Just Security, 10 May 23
- Counterespionage Corner - A collection of recent material on arrests, convictions, expulsions, and more...
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
- "St. Ermin's Hotel London" - The History of a Legendary Spy Site with Stephen Duffy — Andrew Hammond, PhD. SpyCast
- As the war grinds on, Ukraine’s patience and preparation stands in stark contrast to the bluster of Russian leadership. — Former Acting CIA Dep. Dir. for Ops and Arkin Group President Jack Devine, In Other News
- Messaging in the Israeli-Palestinian Conflict, Elections Refocus Türkiye’s Policies, Overlooking Brutal Filipino ‘Drug War,’ U.S. Reaffirms Security Partnership, Tensions Erupt into Violence and Displacement in Manipur, Former PM Imran Khan Arrested as Chaos Envelops Pakistan — Former FBI Special Agent and Soufan Group CEO Ali Soufan, Intel Brief
- South Africa Allegedly Arms Russia, Sudan Update, China Counterespionage Crackdown, The Lennart Meri Conference 2023, The late Arman Soldin’s voice, and more... — WTOP National Security Correspondent JJ Green - Inside the SCIF, Target USA, The Hunt
- "Ghosts of Beirut," a Reflective Counterterrorism Masterpiece - Jeff Stein and Colleagues in SpyTalk (Substack)
Section III - MEMBER CONTRIBUTIONS
- Article: Why the US delayed China sanctions after shooting down a spy balloon - Reuters, 11 May 23
- Article: China expands targeting of U.S with Russian-style covert influence operations - Washington Times, 12 May
- Article: The Secret War for Asia Is Being Fought Under the Sea - Station HYPO, 28 Apr 23
- Article: US-led ‘Five Eyes’ alliance dismantled Russia’s ‘premier espionage cyber-tool’ - Intel News, 11 May 23
- Article: NSA Chief Paul Nakasone Has Said He Expects to Step Down in Coming Months - Wall Street Journal, 11 May 23
- Article: China jails US citizen for life on espionage charges - The Guardian, 15 May 23
- Article: William Burns, a C.I.A. Spymaster With Unusual Powers - New York Times, 09 May 23
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
- The Mossad: The Uniqueness of Israel’s Spy Agency - Aish, 07 May 23
- Intelligence in the Information Age | CIA Executive Carol Rollie Flynn (audio, 54 mins) - Cold War Five: America's Role Abroad, 11 May 2023
- Clandestine communications in cyber-denied environments - Journal of Policing, Intelligence, and Counterterrorism, 12 May 23
- Hunters and Gatherers: The Evolution of Strike and Intelligence Functions in Special Operations Forces - International Journal of Intelligence and Counterintelligence, 08 May 2023
- Deterring Threats from Uncertain Origins: Havana Syndrome, SolarWinds, and the Chinese Mafia - RAND Corporation, 11 May 23
- Don’t Read This If You Have a Security Clearance - The Atlantic, 12 May 23
- Infographic and Report: The Top 10 Largest Nuclear Explosions, Visualized - Visual Capitalist, 13 May 22
- Intelligence in History - A Collection of Recent Content
- True Intelligence Matters in Film: Partisan - James Marquand (in production, 2023)
- Walking Tours: The Spies of Embassy Row and Spies of Georgetown - Washington, DC. (Sundays, Dates/Times Vary)
Section V - Books, Research Requests, Academic Opportunities, Jobs, Obituaries
Books — Forthcoming, New Releases, Overlooked
- The Secret Royals: Spying and the Crown, from Victoria to Diana by Richard J. Aldrich and Rory Cormac
- Russian Intelligence: A Case-based Study of Russian Services and Missions Past and Present by USG National Intelligence University
- Agent of Change: My Life Fighting Terrorists, Spies, and Institutional Racism by Huda Mukbil
Research Requests and Academic Opportunities
- Survey for Members: Skill Sets Needed for Intelligence Analysis Degree Holders to See Success After Graduation
- Call for Information: 430th CIC in Salzburg in 1946
- Call For Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
- Call For Sources: Intelligence Officers Who Lived in Spain in the 1970s
- Call For Papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
- Call For Articles: AFIO Journal, The Intelligencer
- Retired Federal Government Employees Wanted - National Security Agency, Fort Meade, MD
- Assistant Professor - Intelligence Studies (Global Security and Intelligence Studies), Embry-Riddle Aeronautical University - Prescott, Arizona
- Teaching Associate - Intelligence and National Security Studies, Coastal Carolina University, Conway, South Carolina
- Bob Casey, CIA Retiree
- M.G. Detweiler, Decorated former CIA Executive
- Don Hardenbrook, Former OSS Officer
- 18 May 23 (Thursday), 1130 (MT) - In Person - Paul Bolt, PhD discussing “Chinese-Russian Relations: Mutual and Conflicting Interests” - AFIO Rocky Mountain Chapter
- 20 May 23 (Saturday), 1400 (ET) - In Person - David Hunt, Veteran CIA Operations Officer, discussing "USA/China/Taiwan" - AFIO Maine Chapter
- 19 Jun 23 (Monday), 1800 (PDT) - Virtual - Peter Warmka, Veteran CIA Operations Officer, on "Confessions of a CIA Spy - The Art of Human Hacking" - AFIO Columbia River Chapter
Events from Advertisers, Corporate Sponsors, Others
- 20 May 23, 1400-1600 (ET) – Book Signing: The Kneeling Man with author Leta McCollough Seletzky – International Spy Museum Program - In Person - Washington, DC
- 23 May 23, 1200-1300 (ET) Beverly Gage, "G-Man: J. Edgar Hoover and the Making of the American Century" – NASIH - Virtual
- 23 May 23, 1400-1500 (ET) SPY with Me: Memory Loss Program – International Spy Museum - Virtual
- 06 Jun 23, 1700-1900 (ET) The OSS Society Commemorates the 79th Anniversary of D-Day – OSS Society - In Person - Washington, DC
- 13 Jun 23, 1200-1300 (ET) Amy Zegart, "How Technology Is Changing American Intelligence" – NASIH - Virtual
- 13 Jun 23, 1800 (ET) An "Oh So Social" Conversation - A discussion about Michael Vickers forthcoming book, "By All Means Available: Memoirs of a Life in Intelligence, Special Operations, and Strategy" – OSS Society - Virtual
- 14 Jun 23, 1200-1300 (ET) The Making of Global Trends 2030 – Johns Hopkins University - Virtual
- 13-14 Jul 23 2023 Intelligence and Security Summit – AFCEA/INSA - In Person - National Harbor, MD
- 20-22 Jul 2023 NASIH Annual Conference 2023 – NASIH - In Person - University of Calgary, Canada
See the AFIO Calendar of Events for scheduling further in the future.
ACKNOWLEDGEMENTS
The WIN editors thank the following contributors of content for this issue:
GR, PO, EB, CPi, CPa, LR
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
The WIN editors thank the following contributors of content for this issue:
GR, PO, EB, CPi, CPa, LR
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
DISCLAIMER
Our editors include a wide range of articles and commentary in the Weekly Intelligence Notes to
inform and educate our readers. The views expressed in the articles are purely those of the authors and do not reflect support or endorsement from AFIO. WIN notices about non-AFIO events do not constitute endorsement or recommendation by AFIO.
AFIO does not vet or endorse research inquiries, career announcements, or job offers. We publish reasonable-sounding inquiries and career offerings as a service to our members. We encourage readers to exercise caution and good judgment when responding and to independently verify the source before supplying resumes, career data, or personal information.
TECHNICAL DIFFICULTIES
Readers who encounter problems with links or viewing this newsletter as an email can access
the latest web edition here.
the latest web edition here.
FROM THE AFIO STORE
 Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
In 'this remarkable book' (as intelligence historian and AFIO member Nigel West describes in his Foreword), the reader will be struck by the vibrancy of history made real. Author/AFIO member Roy Berkeley goes behind the facades of ordinary buildings, in the city that West calls 'the espionage capital of the World,' to remind us that the history of intelligence has often been made in such mundane places. With his evocative photographs and compelling observations, The 136 sites are organized into 21 manageable walks. But also a joy to armchair travelers. Among the sites: the modest hotel suite where an eager Red Army colonel poured out his secrets to a team of British and American intelligence officers; the royal residence where one of the most slippery Soviet moles was at home for years; the London home where an MP plotting to appease Hitler was arrested on his front steps in 1940.
A few copies are available at only $20 a copy (postage to a U.S.-based address included). Telephone the office at 703-790-0320 or email julie@afio.com to obtain one of these last copies.
 Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Superior quality and shrink resistant; features a detailed embroidered AFIO seal. The shirt color is royal blue.
The sale price is $25 and includes shipping.
Available in men's sizes only: small, medium, large, extra-large, XXL, and XXXL.
Due to limited quantities, please contact the AFIO National Office for availability of size and to provide payment information.
You may telephone the office at 703-790-0320 or email annettej@afio.com
LATEST FROM AFIO
Released exclusively to members today, 16 May 2023...
The Growing Capability of Foreign Countries
to Conduct Large-Scale Espionage within the U.S.
James Bamford, journalist/author, discussing
his latest book, "Spyfail"
Interview of Friday, 14 April 2023 of James Bamford, award-winning journalist/author, discussing his latest book, Spyfail: Foreign Spies, Moles, Saboteurs, and the Collapse of America's Counterintelligence.
Host: James Hughes, AFIO President, a former Senior CIA Operations Officer. Interviewer: John Quattrocki, AFIO Treasurer, a former Senior FBI Officer
TOPIC: Jim Bamford and John Quattrocki discuss SPYFAIL which describes the highly dangerous and growing capability of foreign countries to conduct large-scale espionage within the U.S. and how the FBI and other agencies have failed to prevent it. These covert operations involve a variety of foreign countries—North Korea, Russia, Israel, China, and others—and include cyberattacks, espionage, psychological warfare, the infiltration of presidential campaigns, the smuggling of nuclear weapons components, and other incredibly nefarious actions.
The interview runs 60 minutes and includes several Q&As.
Spyfail is available here.
Access the James Bamford interview here or click above image
This, and upcoming AFIO Now videos in 2023, are sponsored by Northwest Financial Advisors.
WORK AT AFIO
AFIO is seeking a Director of Outreach. (This is an In-Office Position)
A few of the responsibilities include: • Serve as focal point for a major AFIO project, to include maintaining project database and supporting a large annual formal dinner • Provide back-up support to AFIO Directors of Membership and Operations • Support AFIO's existing partners and stakeholders ... Robust Microsoft Office Skills (Excel, Outlook, Word) required.
Full job description here.

"AFIO Now" Video Interviews and Podcasts in 2023 are sponsored by
Northwest Financial Advisors
Click here to watch interviews in the AFIO Now series released in 2023.
View interviews from 2020 to 2022 here.
Watch public-release interviews on our YouTube channel or listen to them in podcast form at the links below.
Log into the member-only area for member-only features.
Latest podcast episode: Erik J. Dahl, Naval Professor/Author on The COVID-19 Intelligence Failure: Why Warning Was Not Enough Video released to members Monday 21 March 2023; Video and Podcast released to public 1 May 2023.
Erik Dahl and Jim Hughes discuss Dahl's latest book, "The COVID-19 Intelligence Failure: Why Warning Was Not Enough" which explores the roles that both traditional intelligence services and medical intelligence and surveillance systems play in providing advance warning against public health threats ― and how these systems must be improved for the future. Epidemiologists and national security agencies warned for years about the potential for a deadly pandemic, but in the end global surveillance and warning systems were not enough to avert the COVID-19 disaster.
Are you too busy to watch an entire AFIO Now episode on YouTube? Would you rather listen in your car or while accomplishing other tasks? You can download or stream episodes on any of the 8 podcasting platforms that host AFIO Now. Search for 'AFIO Podcast' for a selection of the interviews above (public released ones) on:
Podbean; iTunes; Google; Spotify; Amazon Music; Amazon TuneIn + Alexa; iHeartRadio; Pandora
Social media users, and those who wish to explore, can find or be notified about new
announcements and other material on AFIO's Twitter feed, LinkedIn
page, and YouTube channel. Access them here: LinkedIn, Twitter, and YouTube.
![]()
![]()
![]()
The OSS Society's first 2023 "Oh So Social" Virtual Conversation Series is 13 June 2023, 6-7 p.m. EDT
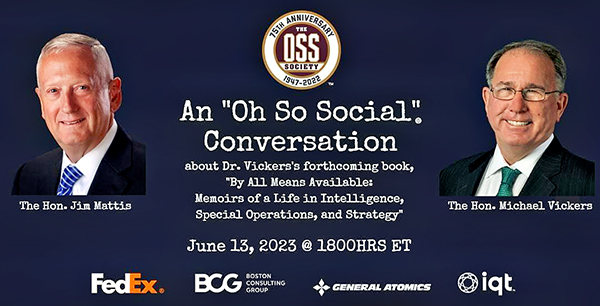
Please join The OSS Society for the first installment in its Virtual 2023 "Oh So Social" Conversation Series on June 13, 2023 — the OSS' 81st birthday — at 6 p.m. EDT. Gen. Jim Mattis will interview OSS Society Chairman Dr. Mike Vickers about his forthcoming memoir, By All Means Available: Memoirs of a Life in Special Operations, Intelligence, and Strategy. Please register for this event by clicking here.
You can pre-order a copy of "By All Means Available" by clicking here.
FOR YOUR FALL TRAVEL PLANS
10-12 November 2023 - Sante Fe, NM - Spies, Lies & Nukes Conference
Spies, Lies & Nukes - Third Conference - Santa Fe, NM
Plan Your Fall Attendance NOW to capture the lower rates


This third, enhanced running of Spies, Lies & Nukes. Join Valerie Plame and some of her legendary, highly decorated, and experienced CIA colleagues as they pull back the curtain on the real life "wilderness of mirrors" that is international espionage.
Hear from and engage with the best of CIA's spies to better understand today's world: from emergent threats, to never-before-told spy operations, black market nuclear scams, how to recruit a spy, the growth of domestic terrorism, how social media is used in espionage, and keeping your employees and your company safe from foreign spies.
Topics: "Soul Catcher: The Metaphysics of Recruiting a Spy" with Jim Lawler, Former Senior CIA Ops Officer
"Delusion and Illusion in Moscow" with Jonna Mendez in conversation with Valerie Plame, Former Covert CIA Ops Officer
"CIA in the Movies" - Panel;
"China: An Emerging Threat" with Mary Beth Long, Former Assistant Secretary of Defense for International Security Affairs
"Inside Putin's Head" with Rolf Mowatt-Larssen, Former Senior CIA Intelligence Officer
"Clarity in Crisis: Leadership Lessons from the CIA" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"Disinformation Distortions: AI, Deep Fakes, and Everything You Always Wanted to Know About Social Media and Espionage" with Alma Katsu, Former Senior CIA and NSA Analyst
"Morality and Ethics in the CIA" with Doug London, Former Senior Officer in the CIA's Clandestine Service
Michael Morrell in conversation with Valerie Plame, Former Covert CIA Ops Officer
"Eliminating Players on the Intelligence Battlefield: Havana Syndrome" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"The End of the Global Nuclear Order" with Valerie Plame, Former Covert CIA Ops Officer
Program also includes: Former Senior CIA Intelligence Officer; Michael J. Morell, Former CIA Deputy Director
FEE: Early Bird purchase window: Apr 12 - Jun 15, $1200; Regular Sale purchase window: Jun 16 - Nov 2, $1300; Late Sale purchase window: Nov 3 - Nov 10, $1450
Ticket price does not include accommodations. More about accommodations here
Tickets include breakfasts, lunches, VIP reception and all speaker presentations and activities.
Conference location: Conference Location: La Fonda On the Plaza, 100 E. San Francisco Street, Santa Fe, NM 87501
More information or to register here
Access CIA's Inhouse Gift Shop
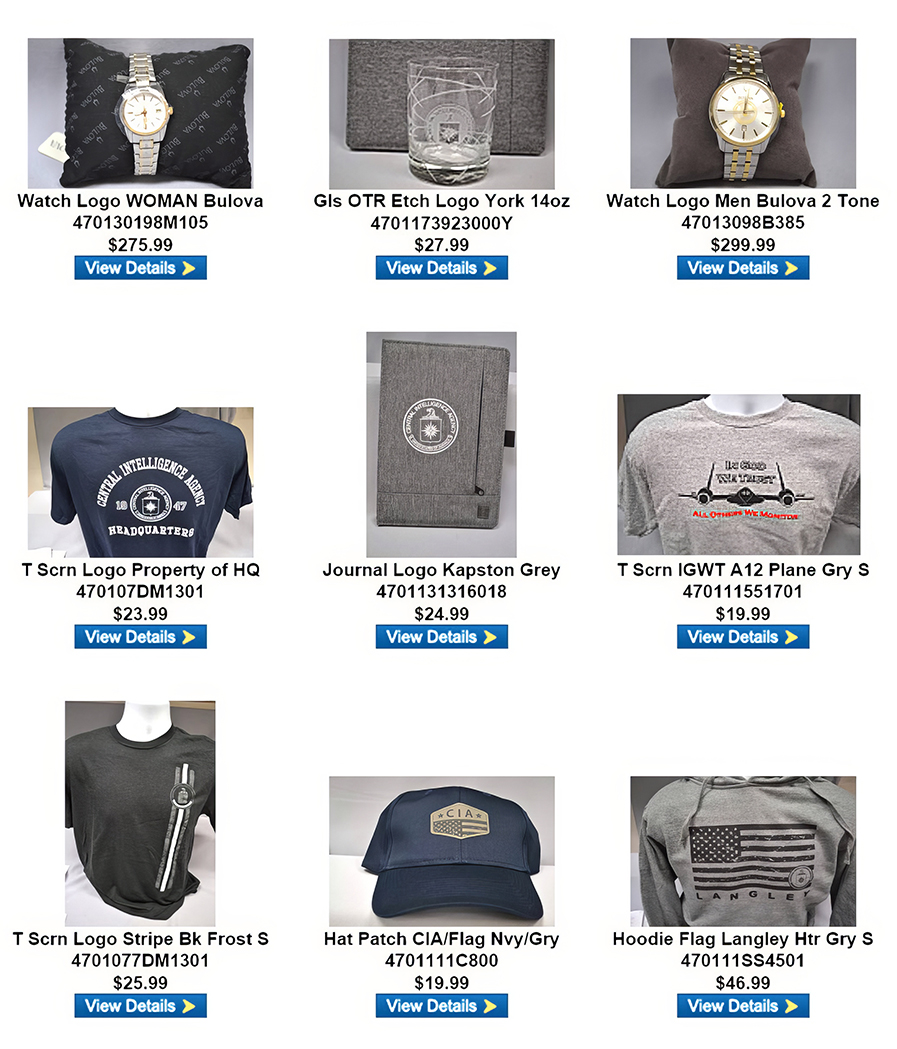
One special benefit of AFIO membership is access to CIA's EAA Store.
After completing the required, quick pre-approval process for all AFIO members, described here, you can purchase directly from the EAA online store their unusual logo'd gift items for self or colleagues. EAA on 12 May 2023 released the photo above, which features some of their newest CIA items and other gift suggestions.
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
Captain James D. Stallings to be Honored on National Cryptologic Memorial Wall - NSA, 12 May 23
The name of Captain James D. Stallings, U.S. Army, will be added to the National Security Agency’s Cryptologic Wall at a ceremony on May 25, 2023. General Paul Nakasone, Commander, U.S. Cyber Command and Director, National Security Agency/Chief, Central Security Service, will host the family of Captain Stallings at the ceremony. Captain Stallings, a native of Carthage, Tennessee, joined the Army ROTC while studying engineering at the Tennessee Polytechnic Institute. Upon graduation in 1954, he was commissioned into the Army. While working to become an electronic warfare cryptologic officer, Captain Stallings married the love of his life, Ann Parkinson. Captain Stallings was subsequently named commanding Officer of the 337th Company, whose mission was to collect critical enemy communications to gain foreknowledge of enemy plans and intentions on the battlefield. (Full article here.)
She was a Muslim spy at the forefront of CSIS’s fight against terrorism. Then, she turned whistle blower - The Star, 12 May 23
Months after two passenger planes flew into the World Trade Center and another crashed into the Pentagon on 9/11, Huda Mukbil joined Canada’s spy agency as an intelligence officer. Months after a white supremacist gunned down six Quebecers praying in a Quebec City mosque in 2017, Mukbil turned whistle blower. Those 15 intervening years are captured in a recently released book that tells the story of how Canada’s first Black Arab-Canadian Muslim spy was treated at the Canadian Security Intelligence Service. It depicts an agency dragging its heels on recognizing the relevance of diverse staff and describes how biases including misogyny, racism and homophobia obstruct the agency from doing the job with which it’s tasked: national security. In the memoir, Mukbil chalks out her service in terms of fulfillment and purpose but also glass ceilings and dashed dreams, with a pit stop at Britain’s MI5 along the way. (Full article here.)
Former intelligence officer, Russia expert was asked to smear Germany to regain his freedom - Nordic Monitor, 08 May 23
A retired veteran intelligence officer and a leading Russia expert revealed that the the government of President Recep Tayyip Erdogan asked him to level baseless accusations against Germany and opposition politicians in Turkey in exchange for his release from jail, where he was wrongfully imprisoned. Testifying at a hearing at the Ankara 28th High Criminal Court in February, Enver Altaylı, who had worked for Turkey’s National Intelligence Organization (MIT) in the ’60s and ’70s, said his captors asked him to level accusations against Germany and say Berlin was behind the 2013 anti-government protests in Turkey. “In 2017, they unlawfully questioned me in detention and offered me my freedom in exchange for making statements against the German state. I have a witnesses [to this]. They said, ‘Mr. Enver, you are a hero. We know that. Germany instigated the Gezi events [2013 anti-government protests]. It’s going to provoke incidents like this again,” Altaylı told the panel of judges. (Full article here.)
How a Secretive Swiss Dealer Is Enabling Israeli Spy Firms - Haaretz, 14 May 23
A day before he was shot dead getting into his car outside his home in Chilpancingo, the capital of the southern Mexican state of Guerrero, journalist Fredid Román Román’s phone number was silently pinged in what confidential data seen by Lighthouse Reports, Haaretz and partners seems to suggest was an attempt to geolocate the reporter using a loophole in the mobile phone system. His murder this August was not just a reminder of the dangers facing journalists: it also offers a chilling insight into the nature and use of technologies whose goal is to exploit the global cellular system - tapping into the very infrastructure of mobile communication - to provide surveillance services of different types. This is a world of surveillance contractors, telecom access brokers and an industry of grey actors with seemingly legitimate businesses. Some are regulated, some are procured by state clients - and some are sold to private actors, providing hackers and criminals alike state-like capabilities. (Full article here.)
Lankans victim of India based cyber espionage? - The Island, 09 May 23
Sri Lanka is among the south Asian nations where people’s data had been harvested by an India-based threat actor dubbed Patchwork, says the Hacker News. It said that the Meta has uncovered massive social media cyber espionage operations across South Asia, adding that three different threat actors leveraged hundreds of elaborate fictitious personas on Facebook and Instagram to target individuals located in South Asia as part of disparate attacks. “Each of these advanced persistent threats (APTs) relied heavily on social engineering to trick people into clicking on malicious links, downloading malware or sharing personal information across the internet,” Guy Rosen, chief information security officer at Meta, said. “This investment in social engineering meant that these threat actors did not have to invest as much on the malware side.” The fake accounts, in addition to using traditional lures like women looking for a romantic connection, masqueraded as recruiters, journalists, or military personnel. (Full article here.)
Israel’s Spying on Palestinians Is So Pervasive It Would Shame Some Dictatorships - The Daily Beast, 06 May 23
Imagine walking the streets of your neighborhood when a group of fully-armed soldiers stops you and demands to take photos of your face. Imagine trying to get out of the city for a day, but to leave, you need to cross a computerized checkpoint that scans your face to decide whether or not to let you through—while recording your every move. Imagine you’re a farmer, tending your sheep, when a foreign soldier shows up and takes a picture of your face. Once your picture loads on his phone, he treats you like a terrorist and detains you on the spot. This is not a sequel to 1984, nor a nightmare episode of Black Mirror. This is the day-to-day life of a Palestinian in the occupied West Bank city of Hebron. Amnesty International recently published “Automated Apartheid,” a report detailing Israel’s extensive use of digital and biometric surveillance technologies in the occupied Palestinian territories. The report uses Hebron and East Jerusalem as case studies through which to elaborate on the different systems Israel uses to surveil Palestinians. (Full article here.)
Bipartisan Group Looks to Fix ‘Hopelessly Obsolete’ Classification System - Government Executive, 10 May 23
A bipartisan group of senators unveiled legislation on Wednesday to reform the information classification system in order to reduce over-classification and prevent the mishandling of classified documents. “I’ve known for years that our system for classifying, safeguarding and declassifying national security information is hopelessly obsolete,” Sen. Mark Warner, D-Va., chairman of the Senate Select Committee on Intelligence, said during a press conference. “We’ve got a byzantine, bizarre, bureaucratic system that has not kept up with the times, has not moved at all to digitalization, so consequently we continue to vastly over-classify huge amounts of information, while at the same time not fully protecting our nation’s most important secrets.” Sen. John Cornyn, R-Texas, a member of the intelligence committee, said the discovery of classified documents in the homes or offices of former President Trump, President Biden and former Vice President Mike Pence brought this issue to light and got some thinking that when the government classifies too many documents, it’s easy to get lackadaisical with the handling of them. (Full article here.)
Austin explains why the US isn't sharing intelligence on alleged Russian war crimes - Washington Examiner, 11 May 23
Secretary of Defense Lloyd Austin issued his opposition to providing evidence of alleged war crimes in Ukraine to the International Criminal Court due to concerns of "reciprocity" against U.S. troops in the future. While other Biden administration leaders support the sharing of this intelligence, Austin expressed his "concerns about reciprocity going forward," and told a Senate Appropriations Subcommittee on Thursday that he will "always prioritize the protection of U.S. military personnel in anything we do." ICC chief prosecutor Karim Khan has told U.S. lawmakers that the U.S. has valuable information that "could accelerate his prosecution of not only [Russian President Vladimir] Putin, but of others," Sen. Lindsey Graham (R-SC) said during the hearing to Austin. The secretary repeatedly said that the department "firmly supports" the goal of holding Russian officials accountable for the war in Ukraine, though that doesn't mean providing them with intelligence. (Full article here.)
Avril Haines: New ODNI Office Oversees Intelligence Community’s Fight Against Disinformation - Executive Gov, 08 May 23
Avril Haines, director of national intelligence and a 2023 Wash100 awardee, said a new organization within her office oversees the intelligence community’s efforts to counter threats posed by foreign actors seeking to influence the U.S. government, The Intercept reported Friday. Established in September 2022, the Foreign Malign Influence Center is charged with countering foreign disinformation that compromises U.S. election security and might sway the general public’s opinion. The office uses all elements of the intelligence community, including departments and agencies with diplomatic and law enforcement functions, to combat disinformation campaigns. “It encompasses our election threat work, essentially looking at foreign influence and interference in elections, but it also deals with disinformation more generally,” Haines told the Senate Armed Services Committee. Haines added that the FMIC is also analyzing intelligence from other foreign adversaries besides Russia to help inform interagency efforts against foreign malign influence. (Full article here.)
NSA Releases New Best Practices for Securing Home Networks - Security Intelligence, 10 May 23
You depend on your home network for binge-watching your favorite shows and ordering the perfect pair of shoes. When it’s time to pay bills or manage your retirement accounts, you likely head online as well. Not to mention that home networks make it possible for you to work from home and for your kids to do schoolwork. If your home network isn’t up and running, then conducting your personal business and staying entertained can become challenging, if not impossible. Many people think of a cyberattack as something that happens to large companies. However, home networks are increasingly the targets of cyber criminals, who use them as a gateway to corporate networks through remote workers. Since you are a remote worker, your habits and setup at home can actually be the cause of a major corporate breach, which is definitely a career-limiting, not career-enhancing, move. “In the age of telework, your home network can be used as an access point for nation-state actors and cyber criminals to steal sensitive information,” said Neal Ziring, National Security Agency Cybersecurity Technical Director. “We can minimize this risk by securing our devices and networks and through safe online behavior.” (Full article here.)
Under fire, CIA moves to overhaul its handling of sexual assault - Politico, 11 May 23
Several female CIA employees have said their cases of being sexually assaulted at the agency were mishandled. The CIA is hiring an expert on sexual assault prevention and announcing a number of new other steps as it attempts to address allegations of mishandling sexual assault and misconduct in its workforce. To lead its Sexual Assault Prevention and Response Office, the agency has hired Taleeta Jackson, a psychologist who most recently oversaw the U.S. Navy’s sexual assault prevention program for more than 70 of its installations. “I am pleased that Dr. Jackson has joined our team and will bring her extensive experience to this crucial new role,” CIA Director Bill Burns said in a statement. “I have personally met with several affected officers to hear their concerns and solicit their feedback on ways we can improve as an Agency. I have heard these concerns loud and clear, and Dr. Jackson’s appointment is just one of several steps we are taking to address them.” (Full article here.)
DHS Intelligence Rearranges the Deck Chairs—Again - Just Security, 10 May 23
The U.S. Department of Homeland Security’s troubled Office of Intelligence & Analysis (IA) last Thursday announced new changes following the results of an internal review. Kenneth L. Wainstein, who now runs IA and was a senior war on terror official in George W. Bush’s Department of Justice, insisted in Bloomberg, “This isn’t just swapping out org charts to try to demonstrate progress.” But by all appearances, that is exactly the nature of this new IA reorganization. IA’s activities have been the subject of regular outrage seemingly every few months as the office finds itself in the headlines with a new scandal. Most recently, Politico revealed that IA was collecting intelligence from people in jails and prisons without notifying their lawyers and with few if any protections of their rights. When the Supreme Court overturned the constitutional right to abortion, IA was caught monitoring the social media “reactions” and “reflections” of people simply talking politics online. And during the civil rights outcry following George Floyd’s murder, IA surveilled journalists and aided a summer-long campaign to undermine and discredit demonstrators, resulting in the removal of a senior official and multiple investigations. (Full article here.)
Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
- Russian media say authorities arrested former US Embassy official - Washington Examiner, 15 May 23
- Iran releases 2 French nationals jailed for ‘spying, propaganda’ - AA, 12 May 23
- Senior members of South Korea’s largest trade union charged with espionage - Intel News, 12 May 23
- Canadian scientists ‘questioned by agents over China links - Times Higher Education, 09 May 23
- Chinese American arrested by DOJ for allegedly spying for China - AsAm News, 13 May 23
- Sweden charges man with spreading classified defence information - Reuters, 12 May 23
- Accomplice in nuclear-submarine espionage case contests 22-year sentence - Exchange Monitor, 12 May 23
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
The Latest from International Spy Museum Historian Andrew Hammond, PhD.
 Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
09 May | "St. Ermin's Hotel London" - The History of a Legendary Spy Site Stephen Duffy joins Andrew to discuss the spy stories of St. Ermin’s Hotel in London. It includes links to SOE, MI6, Ian Fleming, and the Cambridge 5.
Past episodes:
02 May | "Ukraine and the Alliance with NATO's Assistant Secretary General for Intelligence and Security"
25 Apr | "Espionage and the Two Queens" - With Kent Tiernan
18 Apr | "Irregular Warfare and Intelligence" - With IWC President Dennis Walters.
The Latest Insights from Former CIA Acting Deputy Director for Operations Jack Devine.
 In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
12 May | As the war grinds on, Ukraine’s patience and preparation stands in stark contrast to the bluster of Russian leadership. In an interview with European broadcasters aired on Thursday, Ukrainian President Zelenskyy remarked that Ukraine’s highly anticipated counteroffensive won’t begin until his troops are properly equipped and prepared. A few hours later, the UK defense secretary announced that Britain is supplying Storm Shadow cruise missiles to Ukraine, a significant development given that no other Western country has supplied Ukraine with long-range missiles. Western countries have been hesitant to send weapons that could be perceived as crossing Putin’s red lines, but we shouldn’t be, because realistically Russia has limited options to escalate from its side. (Full version available to AFIO members in the coming days here.)
Daily Analysis of Security Issues and Geopolitical Trends
 Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
16 May | The Role of Messaging in the Israeli-Palestinian Conflict
The validity of the motives for the May escalation of clashes between Israel and the Gaza Strip-based Palestinian militant group Palestine Islamic Jihad (PIJ) is subject to significant debate. The two sides have diametrically opposed and seemingly irreconcilable narratives for the genesis, scope, and potential resolution of the Israeli-Palestinian dispute. In their public messaging, each side presents a narrative that accuses the other side of provocation or aggression. PIJ launched a round of rocket and missile attacks on Israel in April, from both Gaza as well as positions in southern Lebanon, to message intense opposition to Israel’s crackdown on Palestinian protests at the Al Aqsa Mosque in Jerusalem. The PIJ’s attacks sparked Israeli airstrikes in retaliation. Even though some rockets were fired from Lebanese territory controlled by key Tehran ally, Lebanese Hezbollah, Israel pointedly messaged that it did not want a broad conflict – either with heavily armed Hezbollah or with Iran – by confining its retaliatory air strikes to PIJ targets in Gaza and south Lebanon. Significantly, Israeli leaders indicated that, although Hezbollah might have been in a position to prevent the launches from south Lebanon, they were not specifically accusing Hezbollah of facilitating the attacks. The clashes remained limited, and hostilities ceased after a few days. (Full brief here.)
15 May | Elections Might Refocus Türkiye’s Policies
12 May | Overlooking Brutal Filipino ‘Drug War,’ U.S. Reaffirms Security Partnership
11 May | Long Simmering Tensions Erupt into Deadly Violence and Mass Displacement in Manipur
10 May | Former Prime Minister Imran Khan Arrested as Chaos Envelops Pakistan
Analysis of Global Security Events with WTOP National Security Correspondent JJ Green
 Inside the SCIF - 11 May - South Africa Allegedly Arms Russia, Sudan Update, China Counterespionage Crackdown, and more...
Inside the SCIF - 11 May - South Africa Allegedly Arms Russia, Sudan Update, China Counterespionage Crackdown, and more...
 Target USA Podcast - 11 May - The Lennart Meri Conference 2023
Target USA Podcast - 11 May - The Lennart Meri Conference 2023
The Hunt Broadcast - 11 May - The late Arman Soldin’s voice
The Latest Insights from Jeff Stein and Colleagues in SpyTalk (Substack)
14 May | "Ghosts of Beirut," a Reflective Counterterrorism Masterpiece - Jeff Stein
In October 2013, I placed a call to the Central Intelligence Agency. I told the CIA’s public affairs office I wanted to talk to them about a story I’d unearthed, about the agency’s assassination of Imad Mughniyah, the world’s top terrorist for decade until he was taken out in 2008. I wasn’t looking for a simple comment, I told them, but some help fleshing out a few details of the hit, which I volunteered was a “righteous kill” since Mughniyah had been responsible for murdering hundreds of Americans in Beirut and elsewhere. They freaked out. (Full article here.)
06 May | Biden Maintains Veil Over Israeli Nuclear Bomb Program - Jefferson Morley
04 May | A Real Iran Crisis Story Behind 'The Diplomat' - Jeff Stein
27 Apr | Jack Teixeira and Me - Jeff Stein
To support SpyTalk, subscribe here.
Section III - MEMBER CONTRIBUTIONS
Article: Why the US delayed China sanctions after shooting down a spy balloon - Reuters, 11 May 23
When an alleged Chinese spy balloon traversed the United States in February, some U.S. officials were confident the incursion would galvanize the U.S. bureaucracy to push forward a slate of actions to counter China. Instead, the U.S. State Department held back human rights-related sanctions, export controls and other sensitive actions to try to limit damage to the U.S.-China relationship, according to four sources with direct knowledge of U.S. policy, as well as internal emails seen by Reuters. The delays to items on the department's "competitive actions" calendar, a classified rolling list of steps the Biden administration has planned related to China, have alarmed some U.S. officials and revealed a divide between those in the U.S. government pushing for tougher action against China and others advocating a more restrained approach. While the State Department signaled U.S. displeasure over the balloon by postponing Secretary of State Antony Blinken's scheduled visit to Beijing, an internal State Department message reviewed by Reuters shows senior U.S. officials delaying planned actions against China. (Read full report here.)
Article: China expands targeting of U.S with Russian-style covert influence operations - Washington Times, 12 May
China’s government is expanding the use of covert influence operations targeting the United States and is expected to exploit the White House-congressional clash over the debt limit crisis as part of growing anti-U.S. activities, the director of national intelligence said. The most recent DNI annual threat assessment warned that China’s efforts are nearing the aggressive intensity of similar covert disinformation operations from Russia, including the use of intelligence agents, cybertools and social media to meddle in U.S. elections, weaken national security laws and exacerbate domestic divisions. “Beijing’s growing efforts to actively exploit perceived U.S. societal divisions using its online personas move it closer to Moscow’s playbook for influence operations,” the assessment states. (Read full report here.)
Article: The Secret War for Asia Is Being Fought Under the Sea - Station HYPO, 28 Apr 23
A secret war is being fought in the Asia-Pacific. But rather than bullets and bombs, the weapons are digital, and the goal is to control the world’s flows of Big Data. Over 486 undersea cables carry over 99% of all international internet traffic globally, according to the Washington-based research firm TeleGeography. The bulk of them are controlled by just a handful American technology giants, namely Alphabet, Google’s parent company; Meta – the owner of Facebook, Instagram and WhatsApp; Amazon; and Microsoft. Transmitting everything from emails and banking transactions to military secrets, these data flows are even more valuable than oil. With information at the centre of technological innovation, controlling data is recognized as the key to driving economic productivity. As such, the world’s subsea cabling infrastructure is increasingly vulnerable not only to sabotage, but also to espionage – spy agencies can easily tap into cables on their own territory. (Read full report here.)
Article: US-led ‘Five Eyes’ alliance dismantled Russia’s ‘premier espionage cyber-tool’ - Intel News, 11 May 23
An espionage tool described by Western officials as the most advanced in the Russian cyber-arsenal has been neutralized after a 20-year operation by intelligence agencies in the United States, Australia, Canada, the United Kingdom and New Zealand. The operation targeted Turla, a hacker group that cyber-security experts have long associated with the Russian government. Turla is believed to be made up of officers from Center 16, a signals intelligence unit of Russia’s Federal Security Service (FSB), one of the Soviet-era KGB’s successor agencies. Since its appearance in 2003, Turla has used a highly sophisticated malware dubbed ‘Snake’ to infect thousands of computer systems in over 50 countries around the world. Turla’s victims include highly sensitive government computer networks in the United States, including those of the Department of Defense, the National Aeronautics and Space Administration, and the United States Central Command. (Read full report here.)
Article: NSA Chief Paul Nakasone Has Said He Expects to Step Down in Coming Months - Wall Street Journal, 11 May 23
Gen. Nakasone, 59 years old, has said he is eyeing a possible departure in August or September after spending more than five years jointly running the two organizations, one of the people said, while others said his timing was less precise. Gen. Nakasone’s plans could change, in part because his deputy at NSA, George Barnes, also is expected to retire soon, the people said. The chief of NSA and Cyber Command is considered one of the most critical national-security jobs in government. The role oversees two agencies that supply vast amounts of intelligence to senior policy makers by spying on foreign communications, while protecting government networks from cyberattacks and supporting military operations. The timing of Gen. Nakasone’s departure could be further muddled by Sen. Tommy Tuberville’s blockade on promotions of senior military officers. The Alabama Republican has been holding up the promotions, which need the Senate’s approval, for months due to objections about the Defense Department’s support for military personnel’s travel to states that allow abortion services. (Read full report here.) (NOTE: This material may require a free registration or sit behind a pay wall.)
Article: China jails US citizen for life on espionage charges - The Guardian, 15 May 23
A Chinese court has sentenced a 78-year-old US citizen to life in prison on espionage charges. John Shing Wan Leung, a Hong Kong permanent resident, was detained in April 2021 by Chinese security services. His sentence was announced on Monday by the Suzhou intermediate people’s court on its public WeChat account. No further information about his trial or charges were listed. Leung’s sentence also included deprivation of political rights for life, and confiscation of personal property in the amount of 500,000 yuan. There are no previous reports or notices of Leung’s arrest or trial. Espionage cases in China are treated with almost no transparency, with trials often conducted in secret and long delays between convictions and sentencing. China’s justice system also regularly reports a conviction rate above 99%. (Read full report here.)
Article: William Burns, a C.I.A. Spymaster With Unusual Powers - New York Times, 09 May 23
To mark the 20th anniversary of the American-led invasion of Iraq, the C.I.A. director, William J. Burns, stood in the lobby of the agency’s headquarters in Langley, Va., and sought to exorcise the ghosts of the prewar intelligence failures that haunt the building to this day. Addressing some 100 C.I.A. officials on March 19, Mr. Burns acknowledged how the agency catastrophically blundered in its assessment that Iraq had weapons of mass destruction. But he noted, according to two people present, that there was ample blame to go around. The culprits included a hubris-stricken Bush White House as well as the State Department — where Mr. Burns served at the time as a senior official — which he said had unwarranted confidence that it could derail the invasion plans. Notably Mr. Burns added, “We’ve learned from that hard lesson.” The intelligence the agency and others collected on Russia’s plans to invade Ukraine, he said, “stands as a powerful example of that. It enabled us to provide strong, resolute and confident warning, to help the Ukrainians defend themselves and to help the president cement a strong coalition.” The tableau was a reminder that Mr. Burns, 67, has for decades been a near-omnipresent if subdued actor on the American foreign policy stage, having served every Democratic and Republican president since Ronald Reagan, with the exception of Donald J. Trump. And yet the moment only hinted at how Mr. Burns, a key figure in the Biden administration’s support of Ukraine, has amassed influence beyond most if not all previous C.I.A. directors. (Read full report here.) (NOTE: This material may require a free registration or sit behind a pay wall.)
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
The Mossad: The Uniqueness of Israel’s Spy Agency - Aish, 07 May 23
Israel’s spy agency, the Mossad, has a reputation for ruthlessness, an ability to strike Israel’s enemies anywhere in the world and the capability to place agents within the deepest strongholds of the enemy. The assassinations of Iranian commanders and nuclear scientists, the placement of agents high up within the Iraqi and Egyptian governments and vengeance against terrorists all add to the agency’s street cred. All of the above fall into the classic operational patterns of most other spy agencies. But the Mossad also engages in operations that are somewhat outside the box of regular intelligence gathering and defensive activities. For example, soon after the establishment of the State of Israel in 1948, the agents of the Mossad were tasked with hunting down and killing Nazi war criminals who had escaped justice. Famously, they tracked Adolf Eichmann, one of the architects of the Holocaust, to Argentina, where they abducted him and brought him to Israel to stand trial for his crimes.1 He was found guilty of all charges and hanged on June 1st 1962. These Nazis no longer posed a danger to the Jewish people or Israel, but bringing them to justice was seen as a duty of the Mossad toward the Jewish nation as a whole. (Full report here.)
Intelligence in the Information Age | CIA Executive Carol Rollie Flynn (audio, 54 mins) - Cold War Five: America's Role Abroad, 11 May 2023
Carol “Rollie” Flynn is the President of the Foreign Policy Research Institute and a thirty-year veteran of the Central Intelligence Agency (CIA). Director of CIA’s Leadership Academy, Director of the Office of Foreign Intelligence Relationships, Associate Deputy Director of the National Counterterrorism Center, Executive Director of the CIA Counterterrorism Center, and Chief of Station in major posts in Southeast Asia and Latin America. She has extensive experience in overseas intelligence operations, security, and counterintelligence. Ms. Flynn is also an adjunct Professor at Georgetown University’s School of Foreign Service/Security Studies Program where she co-directed the National Security Critical Issue Task Force, which conducted research on Lone Wolf Terrorism, Countering Violent Extremism, and Insider Threat. She has also taught at the Fordham University Graduate School of Business and served as Adjunct Staff at Rand Corporation. Ms. Flynn is also a member of the Council on Foreign Relations. (Full report here.)
Clandestine communications in cyber-denied environments - Journal of Policing, Intelligence, and Counterterrorism, 12 May 23
Both intelligence operatives and criminals have a constant need to be able to communicate clandestinely, circumventing surveillance efforts carried out by highly capable adversaries. The recent highly-publicized breaches of internet-based clandestine communications technology and targeted malware attacks, in combination with increasingly sophisticated methods for surveillance of internet traffic has arguably resulted in a cyber-denied environment. This paper employs a red-teaming approach to explore how clandestine communications can be structured using platforms that are physically separated from the internet and thus not vulnerable to internet-based surveillance or attacks. Recent developments in computer-based radio software can be combined with legacy radio technology to provide robust solutions for clandestine communications in a cyber-denied environment. Drawing on case studies from the Cold War, contemporary observations of clandestine radio networks in use today, and technical tests carried out by the authors, this paper stresses the importance for counterintelligence and law enforcement to be prepared for a potential shift in how clandestine communications are implemented by both hostile intelligence services and organized crime. Finally, the paper addresses the issue of proactively countering these techniques by presenting concrete methods for use by counterintelligence and law enforcement to detect radio-based clandestine communications and secure evidence. (Full report here.)
Hunters and Gatherers: The Evolution of Strike and Intelligence Functions in Special Operations Forces - International Journal of Intelligence and Counterintelligence, 08 May 2023
The rapid expansion of Special Operations Forces (SOF) since the beginning of the twenty-first century is largely seen as a response to the necessity to fight the post–11 September 2001 counterterrorism wars. Strike and intelligence, previously studied as distinct functions for military forces, have been increasingly intertwined in contemporary SOF operations. This study examines the evolution of the strike and intelligence functions of the North Atlantic Treaty Organization and allied SOF in counterterrorism and counterinsurgency campaigns from 2004 to 2017. The coevolution of strike and intelligence functions in SOF operations provides unique insight into the processes of battlefield and doctrinal adaptation in counterterrorism campaigns. Opportunities for further research include links between emerging doctrine and practice in targeting enemy networks. (Full report here.)
Deterring Threats from Uncertain Origins: Havana Syndrome, SolarWinds, and the Chinese Mafia - RAND Corporation, 11 May 23
The mystery surrounding the so-called Havana Syndrome — an unexplained illness first experienced by U.S. Department of State personnel stationed in Cuba in late 2016 — illustrates the challenge of mustering a response to a national security threat when the threat, the underlying method, and the actor behind the threat are not understood with certainty. This report explores the applicability of existing concepts for deterrence and compellence using brief case studies. In addition to Havana Syndrome, the authors explore the SolarWinds cyberattack, in which hackers linked to Russian intelligence conducted a massive cyberattack against American companies and government agencies, and the Chinese Communist Party's connections to organized crime syndicates around the world. The core finding is that few of the standard response options are effective against these types of threats. Without certainty about who is conducting the actions, strategies that rely on threats of punishment, normative taboos, or rallying of international condemnation are largely ineffective. Denial-by-defense strategies are thus likely to be the most effective but may be difficult to design effectively if the method underlying the attacks is poorly understood. (Full report here.)
Don’t Read This If You Have a Security Clearance - The Atlantic, 12 May 23
In 1969, the kgb pulled off one of the cleverest deceptions of the Cold War, slipping forged documents into a leak of otherwise authentic U.S. war plans in an effort to pit America against its NATO allies. More than 50 years later, I was invited to run a training session on disinformation for a U.S. intelligence agency. In my back-and-forth with the official in charge, I proposed a game of spot-the-fake using the 1969 leak. The exercise would test whether the intelligence officers could recognize one of the best forgeries in the history of spycraft. But the official shot down my idea. The leaked material technically may still be classified, he explained, so we weren’t allowed to use it. In fact, although the documents had been sitting in public view since before most of us were born, the officers in the class weren’t even allowed to look at them. (Full report here.)
Infographic and Report: The Top 10 Largest Nuclear Explosions, Visualized - Visual Capitalist, 13 May 22
Just how powerful are nuclear explosions? The U.S.’ Trinity test in 1945, the first-ever nuclear detonation, released around 19 kilotons of explosive energy. The explosion instantly vaporized the tower it stood on and turned the surrounding sand into green glass, before sending a powerful heatwave across the desert. As the Cold War escalated in the years after WWII, the U.S. and the Soviet Union tested bombs that were at least 500 times greater in explosive power. This infographic visually compares the 10 largest nuclear explosions in history. (Access visual tool and full report here.)
Intelligence in History - A Collection of Recent Content
- Video - Atomic Spies, Part 1/2: The Klaus Fuchs Effect (43 mins) - SpyScape, 08 May 23
- Article - 4 eerily accurate things the OSS predicted about Hitler during WWII - We Are The Mighty, 11 May 23
- Video - Discovering your husband is a KGB spy (68 mins) - Cold War Conversations, 07 May 23
- Video - Codename HEXAGON: Inside the Secret Satellite Program with Phil Pressel - International Spy Museum, 04 May 23
- Video - The Invisible Shortwave Transmissions Of London's Secret Diplomatic World (17 mins) - Ringway Manchester, 10 May 23
True Intelligence Matters in Film - Partisan - James Marquand (in production, 2023)
 UK sales, production and distribution outfit Signature Entertainment has boarded global sales for Second World War spy thriller The Partisan, with a cast including French-Polish Vikings star Morgane Polański and A Clockwork Orange actor Malcolm McDowell. Sales are launching at this month’s Cannes. UK filmmaker James Marquand directs. His previous credits include Edinburgh International Film Festival premiere Dead Man’s Cards. The title, currently in production in France, is Inspired by the true story of Krystyna Skarbek (Polański), a Polish spy working for the British behind enemy lines during the Second World War. After a betrayal, she is compromised in Warsaw and finds herself in a murky world of treachery. Robert Chadaj, Matthew Whyte and Krystian Kozlowski produce. Further cast includes Frederick Schmidt, Agata Kulesza and Ingvar Sigurdsson. Signature’s director of international Andrew Nerger said: “The incredible true story of Krystyna Skarbek and her heroic exploits during the war is so gripping, we were surprised that her tale had never been told cinematically before. James Marquand’s terrific script held us from the first moment and never let us go. We are excited for audiences around the world to discover her story and learn more about one of Poland’s greatest war heroes.”
UK sales, production and distribution outfit Signature Entertainment has boarded global sales for Second World War spy thriller The Partisan, with a cast including French-Polish Vikings star Morgane Polański and A Clockwork Orange actor Malcolm McDowell. Sales are launching at this month’s Cannes. UK filmmaker James Marquand directs. His previous credits include Edinburgh International Film Festival premiere Dead Man’s Cards. The title, currently in production in France, is Inspired by the true story of Krystyna Skarbek (Polański), a Polish spy working for the British behind enemy lines during the Second World War. After a betrayal, she is compromised in Warsaw and finds herself in a murky world of treachery. Robert Chadaj, Matthew Whyte and Krystian Kozlowski produce. Further cast includes Frederick Schmidt, Agata Kulesza and Ingvar Sigurdsson. Signature’s director of international Andrew Nerger said: “The incredible true story of Krystyna Skarbek and her heroic exploits during the war is so gripping, we were surprised that her tale had never been told cinematically before. James Marquand’s terrific script held us from the first moment and never let us go. We are excited for audiences around the world to discover her story and learn more about one of Poland’s greatest war heroes.”
More information about this based-on-true-events production here.
Walking Tours - Washington, DC - Sundays (Dates/Times Vary)
Former intelligence officers guide visitors on two morning and afternoon espionage-themed walking tours: "Spies of Embassy Row" and "Spies of Georgetown." For more information and booking, click here or contact rosanna@spyher.co
Section V - Books, Research Requests, Jobs, Obituaries
Books — Forthcoming, Newly Released, Overlooked
 The Secret Royals: Spying and the Crown, from Victoria to Diana
The Secret Royals: Spying and the Crown, from Victoria to Diana
by Richard J. Aldrich and Rory Cormac
(Atlantic Books, 07 Oct 21)
For the first time, The Secret Royals uncovers the remarkable relationship between the Royal Family and the intelligence community, from the reign of Queen Victoria to the death of Princess Diana. In an enthralling narrative, Richard J. Aldrich and Rory Cormac show how the British secret services grew out of persistent attempts to assassinate Victoria and then operated on a private and informal basis, drawing on close personal relationships between senior spies, the aristocracy, and the monarchy. This reached its zenith after the murder of the Romanovs and the Russian revolution when, fearing a similar revolt in Britain, King George V considered using private networks to provide intelligence on the loyalty of the armed forces - and of the broader population. In 1936, the dramatic abdication of Edward VIII formed a turning point in this relationship. What originally started as family feuding over a romantic liaison with the American divorcee Wallis Simpson, escalated into a national security crisis. Fearing the couple's Nazi sympathies as well as domestic instability, British spies turned their attention to the King. During the Second World War, his successor, King George VI gradually restored trust between the secret world and House of Windsor. Thereafter, Queen Elizabeth II regularly enacted her constitutional right to advise and warn, raising her eyebrow knowingly at prime ministers and spymasters alike. Based on original research and new evidence, The Secret Royals presents the British monarchy in an entirely new light and reveals how far their majesties still call the shots in a hidden world.
Order book here.
 Russian Intelligence: A Case-based Study of Russian Services and Missions Past and Present
Russian Intelligence: A Case-based Study of Russian Services and Missions Past and Present
by USG National Intelligence University
(USG NIU, 14 May 22)
This United States Government National Intelligence University book, Russian Intelligence: A Case-based Study of Russian Services and Missions Past and Present, sprang from a global pandemic. When the National Intelligence University (NIU) transitioned from a traditional classroom setting to online instruction in spring 2020, NIU faculty were required to reformulate lectures to include only information that could be shared across an open video link. This initially appeared to be a daunting proposition for a course on Russian intelligence and security activities since one would assume that such information is not generally publicly available. Intelligence activities are, by nature, secret. In fact, a large amount of reliable and accurate information exists in the public domain. Although not all public information is reliable and much of it exaggerates or mischaracterizes the subject, with careful selection a comprehensive picture emerges. I also realized that no single volume existed that credibly presented a complete, unbiased picture of Russian intelligence. I set out to develop a series of lectures, which now forms the basis for this book.
Order book here.
 Agent of Change: My Life Fighting Terrorists, Spies, and Institutional Racism
Agent of Change: My Life Fighting Terrorists, Spies, and Institutional Racism
by Huda Mukbil
(McGill-Queen's University Press, 01 May 23)
In Agent of Change Huda Mukbil takes us behind the curtain of a leading spy agency during a fraught time, recounting her experiences as an intelligence officer for the Canadian Security Intelligence Service. Mukbil was the first Black Arab-Canadian Muslim woman to join CSIS and was at the forefront of the fight against terrorism after 9/11. Mukbil’s mastery of four languages quickly made her a counterterrorism expert and a uniquely valuable asset to the organization. But as she worked with colleagues to confront new international threats, she also struggled for acceptance and recognition at the agency. Following the American-led invasion of Iraq in 2003 and the rise of homegrown extremism, Mukbil was framed as an inside threat. Determined to prove her loyalty, while equally concerned about the surveillance and profiling of Muslims and revelations of Western agencies’ torture and torture by proxy, Mukbil started to question CSIS’s fluctuating ethical stance in relation to its mandate. Her stellar work on a secondment to MI5, the British Security Service, earned commendation; this shielded her, but only temporarily, from the hostile workplace culture at CSIS. Ultimately, Mukbil and a group of colleagues went public about the pervasive institutional discrimination undermining CSIS and national security from within. Mukbil’s expertise in international security and her commitment to workplace transparency drove important changes at CSIS. Dazzlingly written, her account is an eye-opener for anyone wanting to understand how racism, misogyny, and Islamophobia undermine not only individuals, but institutions and the national interest – and how addressing this openly can tackle populism and misinformation.
Order book here.
Research Requests and Academic Opportunities
Northeastern University Security and Intelligence Studies professor researching the skill sets required for Intelligence Analysis degree holders to see success after graduation welcomes the participation of AFIO members in a 5-minute survey in support of the research. Access survey here.
Call for Information: 430th CIC in Salzburg in 1946
I am currently writing about 430th CIC in Salzburg in 1946. I have a (large) CIC file and am now trying to track down further details about two officers mentioned in this: (1) Bill Taylor. The sources do not make clear whether the officer was Major Bill G. Taylor, GSC, Head of the Counter-Intelligence Bureau of G-2 (Intelligence Section), US Forces Austria, or “Mil.Reg.” Captain Taylor of Salzburg. Any information on either/both of these officers would be most welcome. (2) Pace B Rose. Rose was a CIC Special Agent in Austria, later a CIA officer who continued to be attached to the Agency after retirement. He died on 3 January 2009. I would like to contact family and friends of Pace Rose. According to the internet, Rose had children, Donna R. Hilverts and Gary W. Rose, and five grandchildren and three great grandchildren. Please contact S.Cody@westminster.ac.uk with any information.
Call for Sources: Intelligence Officers Who Lived in Spain in the 1970s
Spanish journalist Francisco Jiménez is preparing a documentary about the intelligence services in Spain in the 70s. He is looking for intelligence officers who worked in Spain in those years. If you are willing to assist Francisco, he can be reached at fjimenez@globomedia.es.
The Washington Post is developing a multipart audio documentary series (i.e. podcast) chronicling the Grenadian revolution and the US intervention in 1983. They've interviewed nearly 100 people so far, ranging from the heads of state, former Grenadian officials, current and former US officials, veterans, and intelligence officers. They're looking for people who served at the time and may be knowledgeable about intelligence activities in Grenada and the southern Caribbean between 1979 and Operation Urgent Fury. They would also be interested in speaking with anyone who knew Leonard Barrett during the same period. If anyone is interested in participating, please reach out to Washington Post reporter Ted Muldoon via email at ted.muldoon@washpost.com or on Signal at 651-497-5449.
Call for papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
History shows that without planning for post-war reconstruction, apparent victory in war can lead to long-term defeat. On the other hand, wise post-war planning can lead to friendly, peaceful, and profitable relations between victor and vanquished. For political, socio-economic and security-related planning, intelligence plays a crucial role in estimating capabilities, securing infrastructure, locating persons of interest, and rebuilding. In honor of the 75th anniversary of the European Recovery Program (Marshall Plan) after the Second World War, the editors are particularly interested in papers dealing with intelligence concerning post-war reconstruction initiatives and planning connected to historical and recent conflicts. Both case studies and theoretical and methodological approaches are welcome. The studies may include, but do not have to be focused on, the following questions and issues:
- The role of diplomatic and military intelligence during the conflict as preparation for post-war reconstruction, from the conceptual to the practical.
- What intelligence needs to be collected to secure and boost reconstruction?
- What contacts, networks, and infrastructure are necessary for intelligence to be effective?
- Who has been or should be approached and/or recruited for reconstruction efforts based on intelligence?
- When has intelligent post-war planning (or its opposite) been historically evident?
- How should intelligence interact with formerly warring parties and international organizations to empower practical reconstruction efforts?
- What intelligence collection challenges have services encountered in working for post-war peace?
- How did intelligence factor in the European Recovery Program?
- What was George C. Marshall's position on the role of intelligence in general or concrete examples related to "his" plan?
01 Nov 23 deadline. More information and submission instructions here.
Call For Articles: AFIO Journal, The Intelligencer
For the past four years, AFIO has included in The Intelligencer a series of articles on "when intelligence made a difference." Written by scholars, intelligence practitioners, students, and others, they cover events from ancient times to the modern world and in many countries. AFIO is soliciting articles for future issues. Most articles run between 2,000 and 3,000 words, although some are longer or shorter. If you have an idea for an article that fits the theme, email senior editor Peter Oleson at peter.oleson@afio.com.
Jobs
Retired Federal Government Employees Wanted - National Security Agency - Fort Meade, Maryland
The National Security Agency (NSA) may occasionally need skilled civilian retirees to augment the existing work force on high priority projects or programs. In order to fill these temporary positions quickly, we need to know who may be interested and available to return to work with us on a short notice basis as well as their skills. Retirees provide expertise and corporate knowledge to temporarily support mission requirements, manpower shortfalls, and/or mentor the next generation of Agency employees. Salary Range: $86,335 - $170,800.
Additional information and application here.
Assistant/Associate Professor of Intelligence Studies (Global Security and Intelligence Studies) - Embry-Riddle Aeronautical University - Prescott, Arizona
Embry-Riddle Aeronautical University's Prescott, Arizona campus is accepting applications for a tenure-track assistant or associate-level professor of intelligence studies to teach intelligence courses to students in the Global Security and Intelligence program. The successful candidate will teach students about the intelligence community, strategic intelligence, the intelligence cycle and intelligence analysis, writing, and briefing. Prior experience working in the intelligence community is strongly preferred. We are interested in candidates with teaching acumen in intelligence analysis and writing using structured analytical techniques.
Additional information and application here.
Teaching Associate - Intelligence and National Security Studies - Coastal Carolina University, South Carolina
The Department of Intelligence and Security Studies ( ISS ) at Coastal Carolina University is accepting applications for a pool of Teaching Associates (part-time adjunct faculty) to teach introductory and undergraduate elective course offerings for the program beginning in August 2022. While the ad is open to any specialization within the field of study, courses in the areas of homeland security, law enforcement intelligence, counter-narcotics, and cybersecurity are of particular interest. Course offerings can be in a face-to-face or synchronous online modality. To be considered, candidates must have a masters or doctoral degree in a relevant subject area. Prior professional experience in the profession, as well as prior teaching experience are preferred.
Additional information and application here.
Obituaries
![]() Bob Casey — CIA Retiree
Bob Casey — CIA Retiree
Casey, Robert F. "Bob," Age 94, of Centerville, VA passed on April 26, 2023. Born in Medford, graduate of Boston College, served in U.S. Army during Korean War, and worked as an Intelligence Officer for the CIA until his retirement to Cape Cod.
![]() M.G. Detweiler — Decorated former CIA Executive
M.G. Detweiler — Decorated former CIA Executive
Mark George "M.G." Detweiler, 95, departed this life Wednesday, May 10, 2023 after a long illness. Mark was born in Johnstown, PA. Mark earned his bachelor's degree from The George Washington University and his master's from American University. After his Army service, Mark began a distinguished 40-year career in the CIA as an intelligence officer, manager, and executive. He received various honors and awards including a Certificate of Merit from the Office of Imagery Analysis.
![]() Don Hardenbrook — Former OSS Officer
Don Hardenbrook — Former OSS Officer
Donald Orin Hardenbrook, 97, of Weiser, Idaho passed in May 2023. Born in Kirkland, Washington, he joined the Navy at age 17 after completing high school. In Fort Pierce, Florida he trained with Scouts and Raiders as a Frogman (later the SEALS). Training completed, Don hitchhiked to Long Beach, California and shipped out to Calcutta. There he learned tactical and Chinese language skills. In Chungking, Don joined SACO (Sino-American Cooperative Organization), with thousands of Navy, Marine, and Chinese Nationalist troops. Serving behind Japanese army lines (with the Office of Strategic Services-later CIA), SACO's activities remained top secret for years.
Section VI - Events
18 May 23 (Thursday), 1130 MT - In Person - Colorado Springs, CO - AFIO Colorado Springs Chapter hosts Paul Bolt, PhD discussing “Chinese-Russian Relations: Mutual and Conflicting Interests.” The presentation will address the complexity of the Sino-Russian relationship, focusing on historical foundations, energy, security, and the war in Ukraine. While outwardly relations between China and Russia look good, there are tensions beneath the surface. Dr. Paul Bolt is Professor of Political Science at the United States Air Force Academy, where he has taught since 1997. Prior to coming to USAFA, Dr. Bolt taught English at Zhejiang University and Baicheng Normal College in the People’s Republic of China. He also taught at the University of Illinois at Urbana-Champaign as a visiting assistant professor. In 2009-2010 he served as a Fulbright scholar at Nanyang Technological University in Singapore. Dr. Bolt’s most recent book is a co-edited volume on Chinese nuclear weapons and doctrine entitled China's Strategic Arsenal: Worldview, Doctrine, and Systems, published by Georgetown University Press in 2021. He is co-author, with Sharyl Cross, of China, Russia, and Twenty-First Century Global Geopolitics (Oxford, 2018), and author of China and Southeast Asia’s Ethnic Chinese: State and Diaspora in Contemporary Asia (Praeger Publishers, 2000). He has also published on Asia and security issues in a variety of journals and book chapters. For more information or to register, email Steve Pease here.
20 May 23 (Saturday), 1400 (ET) - In Person - David Hunt, Veteran CIA Operations Officer, discussing "USA/China/Taiwan" - AFIO Maine Chapter. CIA operations veteran David P. Hunt will discuss "USA/China/Taiwan: The Deeper/Regrettable Reality" at this public AFIO meeting. David Hunt served 32 years in the CIA, including tours in Italy, Vietnam, Somalia, Norway, France, and New York City. He served twice as Deputy Chief of Station (Norway and France) and twice as Chief of Station (Somalia and New York City). A Colby College graduate, he is an expert in Soviet operations, European affairs, and counterintelligence. Hunt holds the Donovan Award for Excellence, as well as the CIA's Distinguished Intelligence Medal, its highest award. Mr. Hunt will focus on recent administrations in Washington that have neglected China's stealthy approach to the US, stealing our tech, neutralizing legitimate concerns about Chinese (CCP) objectives by wooing if not compromising senior political leaders in the US, Confucius Centers and other similar institutes, sister cities programs, Chinese grants to the universities; lobbyists; all have softened attitudes towards China. Taiwan's military assistance has been slow walked. In the meantime, in China, slave labor, extreme violation of human rights, organ removals from prisoners, continues unabated, etc. Also to be discussed is John Lenczowski's article in the fall 2022 issue of the Intelligencer, "Conquest without War". Jackie Hunt, David Hunt's wife, native-born and raised in Taiwan, will present Taiwan's attitudes towards China, the importance of Taiwan Semiconductor Manufacturing Company, and other relatively unknown factors in this volatile mix. Location: The Economos Lecture Hall, Kennebunk High School, 89 Fletcher St, Kennebunk, ME This is the latest in a series of discussions relating to the importance of intelligence in current public affairs. The AFIO meeting is open to the public, and begins at 2 p.m. in the Economos Lecture Hall at Kennebunk High School, 89 Fletcher Street. A question-and-answer period will follow the presentation. No registration required. Questions? Contact Chapter President Michael Severance at 207/967-4298.
19 Jun 23 (Monday), 1800 (PDT) - Virtual - Peter Warmka, on "Confessions of a CIA Spy - The Art of Human Hacking, the topic and title of his recent book. Hosted by the Columbia River Chapter of AFIO. Warmka is a former Senior Intelligence Officer with the CIA having over 20 years of experience in breaching the security of target organizations overseas. He is an Adjunct Professor at Webster University's Masters in Cybersecurity Program and Founder of Orlando based firm Counterintelligence Institute, LLC. All AFIO members are welcome to tune in. For additional information and for the links and password to join the Zoom Meeting, email Chapter President Carl Wege here or call on 912-222-8640.
See the AFIO Calendar of Events for scheduling further in the future.
Events from Advertisers, Corporate Sponsors, Others
In the famous photograph of the assassination of Dr. Martin Luther King Jr. on the balcony of Memphis's Lorraine Motel, one man kneeled down beside King, trying to staunch the blood from his fatal head wound with a borrowed towel. This kneeling man was a member of the Invaders, an activist group that was in talks with King in the days leading up to the murder. But he also had another identity: an undercover Memphis police officer reporting on the activities of this group, which was thought to be possibly dangerous and potentially violent. Leta McCollough Seletzky is the kneeling man's daughter. Her book, The Kneeling Man: My Father's Life as a Black Spy Who Witnessed the Assassination of Martin Luther King Jr., powerfully shares her quest to learn the truth about her father, Marrell McCollough. Join SPY's Amanda Ohlke for a conversation with her and how she grappled with her father's secret history — how he, a Black man, came to be working secretly with the white power structure as a spy — which she felt was in direct opposition to her understanding of what it meant to be Black in America, and of everything she eventually devoted her life and career to. Seletzsky will discuss how she set out to learn what she could about his life, his actions and motivations, and how this has affected her. From his time as a policeman to his career at the CIA, her father's story is a unique and heart wrenching story of an undercover life. Visit www.spymuseum.org.
Beverly Gage is professor of 20th-century American history at Yale. She is the author of The Day Wall Street Exploded, which examined the history of terrorism in the late 19th and early 20th centuries. She writes frequently for the New York Times, the Washington Post, the New York Times Magazine and The New Yorker, among other publications. In this talk, she addresses J. Edgar Hoover, who we remember as a bulldog--squat frame, bulging wide-set eyes, fearsome jowls--but who in 1924, when he became director of the FBI, had been the trim, dazzling wunderkind of the administrative state, buzzing with energy and big ideas for reform. He transformed a failing law-enforcement backwater, riddled with scandal, into a modern machine. He believed in the power of the federal government to do great things for the nation and its citizens. He also believed that certain people--many of them communists or racial minorities or both-- did not deserve to be included in that American project. Hoover rose to power and then stayed there, decade after decade, using the tools of state to create a personal fiefdom unrivaled in U.S. history. Beverly Gage’s monumental work explores the full sweep of Hoover’s life and career, from his birth in 1895 to a modest Washington civil-service family through his death in 1972. In her nuanced and definitive portrait, Gage shows how Hoover was more than a one-dimensional tyrant and schemer who strong-armed the rest of the country into submission. As FBI director from 1924 through his death in 1972, he was a confidant, counselor, and adversary to eight U.S. presidents, four Republicans and four Democrats. Franklin Roosevelt and Lyndon Johnson did the most to empower him, yet his closest friend among the eight was fellow anticommunist warrior Richard Nixon. Hoover was not above blackmail and intimidation, but he also embodied conservative values ranging from anticommunism to white supremacy to a crusading and politicized interpretation of Christianity. This garnered him the admiration of millions of Americans. He stayed in office for so long because many people, from the highest reaches of government down to the grassroots, wanted him there and supported what he was doing, thus creating the template that the political right has followed to transform its party. G-Man places Hoover back where he once stood in American political history--not at the fringes, but at the center--and uses his story to explain the trajectories of governance, policing, race, ideology, political culture, and federal power as they evolved over the course of the 20th century. More information and registration here.
23 May 23, 1400-1500 (ET) - SPY with Me: Memory Loss Program – International Spy Museum - Virtual
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. To register, please email Shana Oltmans at soltmans@spymuseum.org Free but space is limited. Visit www.spymuseum.org.
Join The OSS Society for a screening of its award-winning short documentary, "Operation Overlord: OSS and the Battle for France." This film tells the story of Allied special forces whose daring exploits for D-Day changed the course of World War II. This event is by invitation only and is non-transferable. More information here.
Dr. Amy Zegart is the Morris Arnold and Nona Jean Cox Senior Fellow at the Hoover Institution and Professor of Political Science (by courtesy) at Stanford University. She is also a Senior Fellow at Stanford’s Freeman Spogli Institute for International Studies, Chair of Stanford’s Artificial Intelligence and International Security Steering Committee, and a contributing writer at The Atlantic. She specializes in U.S. intelligence, emerging technologies and national security, grand strategy, and global political risk management. In this talk, Zegart examines the past, present, and future of American espionage, focusing on how emerging technologies are radically challenging every aspect of the intelligence enterprise. An illuminating case study is nuclear threat detection. Zegart will share her findings that nuclear intelligence is not just for superpower governments anymore thanks to Internet connectivity, automated analytics, and commercial satellites. This talk will focus on the characteristics, benefits, and risks of this democratization of intelligence for threat detection and crisis management. Zegart will also discuss how technology is not a panacea for the intelligence community, how it can exacerbate existing biases, and how it must be used strategically to provide critical insights to the military, policymakers, and the American public. More information and registration here.
General Jim Mattis interviews Dr. Michael Vickers about his forthcoming book. In By All Means Available: Memoirs of a Life in Intelligence, Special Operation and Strategy, Vickers recounts his remarkable career, from his days as a Green Beret to his vision for victory in Afghanistan to his role in waging America’s war with al-Qa’ida at the highest levels of government. In captivating detail, he depicts his years in the Special Forces—including his training to parachute behind enemy lines with a backpack nuclear weapon in the event of a Soviet invasion of Western Europe, and he reveals how those experiences directly influenced his approach to shaping policy. Vickers has played a significant role in most of the military and intelligence operations of the past four decades, and he offers a deeply informed analysis of the greatest challenges facing America today, and in the decades ahead. More information here.
14 Jun 23, 1200-1300 (ET) - The Making of Global Trends 2030 – Johns Hopkins University - Virtual
Join host Michael Ard for a discussion with strategic foresight and global trend expert Mathew Burrows. Mathew Burrows is the Program Lead of the Stimson Center’s Strategic Foresight Hub and a Distinguished Fellow with the Reimagining US Grand Strategy program. Prior to joining Stimson, he served as the director of Foresight at the Atlantic Council’s Scowcroft Strategy Initiative and as the co-director of the New American Engagement Initiative. Burrows is one of the leading experts on strategic foresight and global trend analysis. In 2013 he retired from a 28-year-long career in the State Department and the Central Intelligence Agency (CIA), the last 10 years of which he spent at the National Intelligence Council (NIC), the premier analytic unit in the US Intelligence Community. In 2007, Burrows was appointed Counselor, the number three position in the NIC, and was the principal drafter for the NIC publication Global Trends 2030: Alternative Worlds, which received widespread recognition and praise in the international media. In 2005, he was asked to set up and direct the NIC’s new Long Range Analysis Unit, which is now known as the Strategic Futures Group. Other positions included assignments as deputy national security advisor to Treasury Secretary Paul O’Neill (2001-02), special assistant to the UN Ambassador Richard Holbrooke (1999-2001), and first holder of the intelligence community fellowship at the Council on Foreign Relations in New York (1998-1999). Burrows received a BA in American and European history from Wesleyan University and a PhD in European history from the University of Cambridge. Free registration here.
"The Nation's Premier Intel and National Security Event" - Save the date for the 10th Annual AFCEA/INSA Intelligence and National Security Summit! The powerful, two-day program, at the Gaylord National Resort, will feature five blockbuster plenaries, six engaging breakout sessions, and a jam-packed exhibit hall full of the latest IC technology innovations. Top leaders will discuss State of the Community, Military Intelligence Priorities, Strategic Intelligence, and Cybersecurity Challenges. Breakout sessions with senior leaders, technology experts, and thought leaders will examine some of the most pressing issues facing the community. Plus, powerful networking opportunities designed to foster partnerships and relationship building. Early registration closes 19 May. Check for for full agenda and updates here.
20-22 Jul 2023 - NASIH Annual Conference 2023 – NASIH - In Person - University of Calgary, Canada
Registration is open and the registration fee will increase on 15 Jun 23. Full two-day program, with extensive speaker line up and panels, here. Registration here.
Gifts for Friends, Colleagues, Self
 Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Show your support for AFIO with our new Black Short-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $50 each including shipping.
Sizes for (M) men, only; Small, Medium, Large, XL, XXL, and XXXL. $50 per shirt.
You may pay by check or credit card. Complete your order online here or mail an order along with payment to: AFIO, 7600 Leesburg Pike, Ste 470 East, Falls Church, VA 22043-2004. Phone orders at 703-790-0320. Questions? Contact Annette at: annettej@afio.com.

PopSocket for cellphones or tablets
Show your support to AFIO while enjoying the convenience offered by our AFIO Logo PopSocket. The PopSocket is most commonly used as a stand and as a grip for your mobile phone or tablet; handy for taking selfies, watching videos, and for texting. The PopSocket looks like a small button or sticker which, when closed, sticks flat to your mobile device. However, its accordion-like design enables it to pop open for use. The benefits of using a PopSocket make it a must-have accessory for your mobile phone or tablet. It also aids in keeping your phone from slipping off your hand during use, falling, or breaking.
Price: $15. Order this and other store items online here.

Duffel Bags - Royal Blue and Black with Full Color AFIO Logo This duffel has it all when it comes to value, style and organization.
600 denier polyester canvas with polyester double contrast; D-shaped zippered entry for easy access. Front pocket with hook and loop closure. End mesh pocket Easy-access end pockets. Four durable, protective feet and built-in bottom board for added strength. Web handles with padded grip. Detachable, adjustable shoulder strap.
Dimensions: 11"h x 19.75"w x 9.75"d; Approx. 2,118 cubic inches
Price: $50. Order this and other store items online here.
AFIO Mug with color glazed seal.
Made in the U.S.A., dishwasher-safe.
$35 includes shipping.
Sip your morning joe in style or use it to stash pens, cards, paperclips, or candy.
Order this and other store items online here.

Caps - Dark Navy with Navy AFIO Logo
An authentic silhouette with the comfort of an unstructured, adjustable fit. Fabric: 100% cotton. Unstructured. Fabric strap closure with adjustable D-clip. Price: $30. Order this and other store items online here.
PUBLISHED IN 2023
| Be informed on career opportunities in the U.S. Intelligence Community | ||
 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. AFIO's popular 47-page booklet reaches thousands of high school, college students, university guidance offices, and distributed in classes teaching intelligence, to help those considering careers in the U.S. Intelligence Community. |
 |
| This is the all new fifth edition. The publication is also popular with University Career Guidance Centers, professors and academic departments specializing in national security, and parents assisting children or grandchildren in choosing meaningful, public service careers. This booklet is provided online as a public service from the generosity of AFIO board, volunteer editors/writers, donors, and members. We thank all for their support which makes this educational effort possible. |
||
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |
||
 Guide to the Study of Intelligence...and...When Intelligence Made a Difference
Guide to the Study of Intelligence...and...When Intelligence Made a Difference
"AFIO's Guide to the Study of Intelligence" has sold out in hard-copy.
It is available in digital form in its entirety on the
AFIO website here.
Also available on the website here are the individual articles of AFIO's
history project "When Intelligence Made a Difference" that have been
published to date in The Intelligencer journal.
More articles will be appear in future editions.
Some features of the email version of the WIN do not work for readers who have chosen the Plaintext Edition, some users of AOL, and readers who access their email using web mail. You may request to change from Plaintext to HTML format here afio@afio.com. For the best reading experience, the latest web edition can be found here: https://www.afio.com/pages/currentwin.htm
To unsubscribe from the WIN email list, please click the "UNSUBSCRIBE" link at the bottom of the email. If you did not subscribe to the WIN and are not a member, you received this product from a third party in violation of AFIO policy. Please forward to afio@afio.com the entire message that you received and we will remove the sender from our membership and distribution lists.
(c) 1998 thru 2023
AFIO Members Support the AFIO Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for back issues of the WINs, information about AFIO, conference agenda and registrations materials, and membership applications and much more! .
AFIO | 7600 Leesburg Pike, Suite 470 East, Falls Church, VA 22043-2004 | (703) 790-0320 (phone) | (703) 991-1278 (fax) | afio@afio.com