31 May - 6 June 2023
(Issue 22)
is sponsored by

Readers who encounter problems with the email version of this newsletter can
view the latest web edition here.
| Visit us on |
CONTENTS
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
- Suspected Chinese spies, disguised as tourists, tried to infiltrate Alaskan military bases - USA Today, 31 May 23
- U.S., ROK Agencies Alert: DPRK Cyber Actors Impersonating Targets to Collect Intelligence - NSA, 01 Jun 23
- Lack of transparency from intelligence agencies, Taumaru report finds - RNZ, 29 May 23
- North Korea says spy satellite launch crashed into sea - BBC, 31 May 23
- How Ukrainian military spies are beating their Russian rivals - The Times, 27 May 23
- Mossad agent who died in Italy was on mission working against Iran - Jerusalem Post, 29 May 23
- ‘Spymania’ grips Russian security services amid sharp rise in treason cases - The Guardian, 04 Jun 23
- Former Spymaster Hakan Fidan Assumes Leadership Of Turkey's Foreign Ministry - Forbes, 04 Jun 23
- China’s anti-espionage chief urges stronger crackdown using legal tools - South China Morning Post, 05 Jun 23
- Counterespionage Corner - A collection of recent material on arrests, convictions, expulsions, and more...
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
- From the Vault: "El Chapo, The War on Drugs, and Intelligence" with Noah Hurowitz — Andrew Hammond, PhD. SpyCast
- Putin is downplaying recent attacks on Russia, but if these attacks continue, they could alter the nature of the conflict. — Former Acting CIA Dep. Dir. for Ops and Arkin Group President Jack Devine, In Other News
- Chinese Disinformation, Texas Legislation and Christian Nationalism, Sudan Attracting Foreign Fighters and Mercenaries?, Wagner Group Preparing to Exit Bakhmut, Central Asian Leaders Summit Advances Xi’s Geostrategy — Former FBI Special Agent and Soufan Group CEO Ali Soufan, Intel Brief
- Kremlin-backed poisonings, Whelan, Sudan, Conflicts in Ukraine and Sudan are connected, More extremist content showing up online, Tiring of Ukraine, Neo-Nazi Crashes at the White House, and more... — WTOP National Security Correspondent JJ Green - Inside the SCIF, Target USA, The Hunt
- Turncoat Hanssen Was a Very Weird Dude | Taiwan is Losing its Spy Wars with China... | About That Beluga Whale Spy... | OSS Agents in Repose, After the Guns Fell Silent - Jeff Stein and Colleagues in SpyTalk (Substack)
Section III - MEMBER CONTRIBUTIONS
- Article: Developing An Unbreakable Cybersecurity System - Semiconductor Engineering, 01 Jun 23
- Article: Exclusive: World's spy chiefs meet in secret conclave in Singapore - Reuters, 04 Jun 23
- Article: Russia's FSB says US penetrated thousands of Apple phones in spy plot - Reuters via Jerusalem Post, 01 Jun 23
- Article: North Korea targets U.S. intel figures on a secret cyber hit list - Washington Times, 02 Jun 23
- Article: CIA Chief Made Secret Trip to China - Wall Street Journal, 02 Jun 23
- Article: China Investing in Open Source Intelligence - New York Times, 01 Jun 23
- Article: U.S. Prepares New Massive Intelligence Collection Center in Hezbollah-Controlled Beirut - The Foreign Desk, 31 May 23
- Article: FBI gearing up for new anti-encryption campaign - Washington Times, 30 May 23
- Article: Intelligence Officials Say U.S. Has Retrieved Craft of Non-Human Origin - The Debrief, 05 Jun 23
- Article: Robert Hanssen, an FBI agent who was convicted of spying for Russia, dies in prison - Associated Press, 05 Jun 23
- Book Review: Code Name Blue Wren - Washington Times, 01 Jun 23
- Report: Russian forces were suffering from ‘electronic fratricide’ within days of attacking Ukraine, a new report says - Station HYPO, 05 Jun 23
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
- Cyber-enabled tradecraft and contemporary espionage: assessing the implications of the tradecraft paradox on agent recruitment in Russia and China - Journal of Intelligence and National Security, 02 Jun 23
- Iran: How to counter covert action in the digital age - Chatham House, 30 May 2023
- Chinese Next-Generation Psychological Warfare - RAND, 01 Jun 23
- Complexity in Military Intelligence - International Journal of Intelligence and Counterintelligence, 30 May 2023
- Dispelling Myths: How Classification and Declassification Actually Work - Justice Security, 02 Jun 23
- Infographic and Report: Comparing Population Pyramids Around the World - Visual Capitalist, 01 Jun 23
- Intelligence in History - A Collection of Recent Content
- True Intelligence Matters in Film: Reality - Tina Satter (2023)
- Walking Tours: The Spies of Embassy Row and Spies of Georgetown - Washington, DC. (Sundays, Dates/Times Vary)
Section V - Books, Research Requests, Academic Opportunities, Jobs, Obituaries
Books — Forthcoming, New Releases, Overlooked
- Revealing Secrets: An unofficial history of Australian Signals intelligence and the advent of cyber by Clare Birgin and John Blaxland
- The Academic-Practitioner Divide in Intelligence Studies by Rubén Arcos, Nicole K. Drumhiller, Mark Phythian
- Targeted as a Spy: Surveillance of an American Diplomat in Communist Romania by Ernest H. Latham Jr.
Research Requests and Academic Opportunities
- Survey for Members: Skill Sets Needed for Intelligence Analysis Degree Holders to See Success After Graduation
- Call for Information: 430th CIC in Salzburg in 1946
- Call For Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
- Call For Sources: Intelligence Officers Who Lived in Spain in the 1970s
- Call For Papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
- Call For Articles: AFIO Journal, The Intelligencer
- Retired Federal Government Employees Wanted - National Security Agency, Fort Meade, MD
- Assistant Professor - Intelligence Studies (Global Security and Intelligence Studies), Embry-Riddle Aeronautical University - Prescott, Arizona
- Teaching Associate - Intelligence and National Security Studies, Coastal Carolina University, Conway, South Carolina
- Vern Hayes, Decorated Airforce Officer and CIA Officer
- Larry Hatch, Career NSA Cryptographer
- Lahoma Dickey, NSA Research Analyst
- Ronald Gray, Career NSA Officer
- 19 Jun 23 (Monday), 1800 (PDT) - Virtual - Peter Warmka, veteran CIA operations officer on "Confessions of a CIA Spy - The Art of Human Hacking" - AFIO Columbia River Chapter
- 27 Jul 23 (Thursday), 1130 (Pacific) - In Person, San Francisco - Col. Robert W. Parr, USAF (ret), on "12 Days with a Soviet Pilot Defector" - AFIO Andre LeGallo Chapter
Events from Advertisers, Corporate Sponsors, Others
- 08 Jun 23, 1830 (ET) - An Interview with Kim, Hyun Woo, Former DPRK Agent – International Spy Museum - In Person - Washington, DC
- 10 Jun 23, 1400-1600 (ET) - In-Store Book Signing Event: Red London with author Alma Katsu – International Spy Museum - In Person - Washington, DC
- 13 Jun 23, 1200-1300 (ET) Amy Zegart, "How Technology Is Changing American Intelligence" – NASIH - Virtual
- 13 Jun 23, 1800 (ET) An "Oh So Social" Conversation - A discussion about Michael Vickers forthcoming book, "By All Means Available: Memoirs of a Life in Intelligence, Special Operations, and Strategy" – OSS Society - Virtual
- 14 Jun 23, 1200-1300 (ET) The Making of Global Trends 2030 – Johns Hopkins University - Virtual
- 20 Jun 23, 0800-1000 (ET) A Celebration of Excellence: Honoring Charlie Allen – INSA - In Person - Tysons Corner, VA
- 29 Jun 23, 0900-0945 (ET) Coffee and Conversation with The Hon. Michael Vickers – INSA - Virtual
- 13-14 Jul 23 2023 Intelligence and Security Summit – AFCEA/INSA - In Person - National Harbor, MD
- 20-22 Jul 2023 NASIH Annual Conference 2023 – NASIH - In Person - University of Calgary, Canada
See the AFIO Calendar of Events for scheduling further in the future.
ACKNOWLEDGEMENTS
The WIN editors thank the following contributors of content for this issue:
S, LR, GR, CP, JK, EB, PO
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
The WIN editors thank the following contributors of content for this issue:
S, LR, GR, CP, JK, EB, PO
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
DISCLAIMER
Our editors include a wide range of articles and commentary in the Weekly Intelligence Notes to
inform and educate our readers. The views expressed in the articles are purely those of the authors and do not reflect support or endorsement from AFIO. WIN notices about non-AFIO events do not constitute endorsement or recommendation by AFIO.
AFIO does not vet or endorse research inquiries, career announcements, or job offers. We publish reasonable-sounding inquiries and career offerings as a service to our members. We encourage readers to exercise caution and good judgment when responding and to independently verify the source before supplying resumes, career data, or personal information.
TECHNICAL DIFFICULTIES
Readers who encounter problems with links or viewing this newsletter as an email can access
the latest web edition here.
the latest web edition here.
FROM THE AFIO STORE
 Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
In 'this remarkable book' (as intelligence historian and AFIO member Nigel West describes in his Foreword), the reader will be struck by the vibrancy of history made real. Author/AFIO member Roy Berkeley goes behind the facades of ordinary buildings, in the city that West calls 'the espionage capital of the World,' to remind us that the history of intelligence has often been made in such mundane places. With his evocative photographs and compelling observations, The 136 sites are organized into 21 manageable walks. But also a joy to armchair travelers. Among the sites: the modest hotel suite where an eager Red Army colonel poured out his secrets to a team of British and American intelligence officers; the royal residence where one of the most slippery Soviet moles was at home for years; the London home where an MP plotting to appease Hitler was arrested on his front steps in 1940.
A few copies are available at only $20 a copy (postage to a U.S.-based address included). Telephone the office at 703-790-0320 or email julie@afio.com to obtain one of these last copies.
 Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Superior quality and shrink resistant; features a detailed embroidered AFIO seal. The shirt color is royal blue.
The sale price is $25 and includes shipping.
Available in men's sizes only: small, medium, large, extra-large, XXL, and XXXL.
Due to limited quantities, please contact the AFIO National Office for availability of size and to provide payment information.
You may telephone the office at 703-790-0320 or email annettej@afio.com
LATEST FROM AFIO
Released exclusively to members - 30 May 2023...
Experiences of a CIA Targeting Officer
as told in the novel "The Syndicate Spy"
Brittany Butler, author and former CIA Targeter,
discussing her latest book, The Syndicate Spy
Interview of Tuesday, 2 May 2023 of Brittany Butler, author and former CIA Targeter, discussing her latest book, The Syndicate Spy. Host and Interviewer: James Hughes, AFIO President, a former Senior CIA Operations Officer.
TOPIC: Brittany Butler and Jim Hughes discuss THE SYNDICATE SPY, her novel, which is based on her experiences as a CIA targeting officer. It tells the tale of two female spies as they race to uncover terrorists' conspiracies and ultimately change the course of war.
Though this is her first spy thriller, she has been writing the book in her head for years. She adores thrillers and spy novels. But none of the books she read come close to telling what it was really like for a woman working at the CIA. So, when she set out to write a spy thriller, she created a fresh female protagonist who felt human, who navigates the morally grey areas in espionage, and grapples with her ability to do good in a world where she is the outsider.
Her heroine, Juliet, embodies all those things but she's not Brittany. She partners Juliet with Mariam—a Saudi feminist who is eager to see the Kingdom flourish under more progressive rulers—these two women take off in an electrifying, page-turning thriller.
The Syndicate Spy showcases these two strong women who display the badassery that a good spy thriller demands, but with unparalleled depth not seen elsewhere in the male-dominated genre.
The interview runs 17 minutes and includes several Q&As.
The Syndicate Spy is available here
Access the Brittany Butler interview here or click above image
This, and upcoming AFIO Now videos in 2023, are sponsored by Northwest Financial Advisors.
WORK AT AFIO
A few of the responsibilities include: • Serve as focal point for a major AFIO project, to include maintaining project database and supporting a large annual formal dinner • Provide back-up support to AFIO Directors of Membership and Operations • Support AFIO's existing partners and stakeholders ... Robust Microsoft Office Skills (Excel, Outlook, Word) required.
Full job description here.

"AFIO Now" Video Interviews and Podcasts in 2023 are sponsored by
Northwest Financial Advisors
Click here to watch interviews in the AFIO Now series released in 2023.
View interviews from 2020 to 2022 here.
Watch public-release interviews on our YouTube channel or listen to them in podcast form at the links below.
Log into the member-only area for member-only features.
Latest podcast episode: Nigel West, Historian and Former MP, on "Hitler's Trojan Horse: The Fall of The Abwehr"
Video and Podcast released to public 21 May 2023.
Nigel West and Jim Hughes discuss Nigel's recent book, "Hitler's Trojan Horse: The Fall of The Abwehr." Topics include: Impact of Abwehr defections; Richard Wurmann; Erich Vermehren; SIS Officer Nicholas Elliott; Paul (Willi) Hamburger; SIGINT; Adm. Wilhelm Canaris; Operation Valkyrie; 20 July Plot; Sicherheitsdienst; Otto John - code name WHISKY; Claus von Stauffenburg; Prince Frederick III, Solms-Baruth, tortured for his attempt to assassinate Hitler on 20 July 1944, SIS officer and professor H.L.A. Hart..
Are you too busy to watch an entire AFIO Now episode on YouTube? Would you rather listen in your car or while accomplishing other tasks? You can download or stream episodes on any of the 8 podcasting platforms that host AFIO Now. Search for 'AFIO Podcast' for a selection of the interviews above (public released ones) on:
Podbean; iTunes; Google; Spotify; Amazon Music; Amazon TuneIn + Alexa; iHeartRadio; Pandora
Social media users, and those who wish to explore, can find or be notified about new
announcements and other material on AFIO's Twitter feed, LinkedIn
page, and YouTube channel. Access them here: LinkedIn, Twitter, and YouTube.
![]()
![]()
![]()
The OSS Society's first 2023 "Oh So Social" Virtual Conversation Series is 13 June 2023, 6-7 p.m. EDT
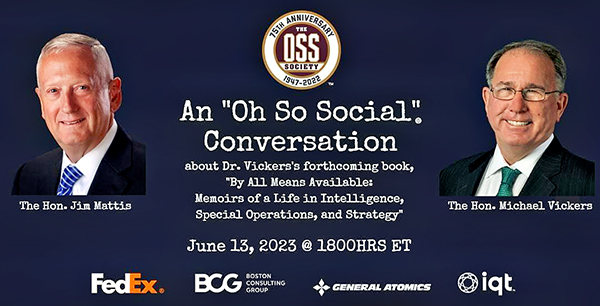
Please join The OSS Society for the first installment in its Virtual 2023 "Oh So Social" Conversation Series on June 13, 2023 — the OSS' 81st birthday — at 6 p.m. EDT. Gen. Jim Mattis will interview OSS Society Chairman Dr. Mike Vickers about his forthcoming memoir, By All Means Available: Memoirs of a Life in Special Operations, Intelligence, and Strategy. Please register for this event by clicking here.
You can pre-order a copy of "By All Means Available" by clicking here.
FOR YOUR FALL TRAVEL PLANS
10-12 November 2023 - Sante Fe, NM - Spies, Lies & Nukes Conference
Spies, Lies & Nukes - Third Conference - Santa Fe, NM
Plan Your Fall Attendance NOW to capture the lower rates


This third, enhanced running of Spies, Lies & Nukes. Join Valerie Plame and some of her legendary, highly decorated, and experienced CIA colleagues as they pull back the curtain on the real life "wilderness of mirrors" that is international espionage.
Hear from and engage with the best of CIA's spies to better understand today's world: from emergent threats, to never-before-told spy operations, black market nuclear scams, how to recruit a spy, the growth of domestic terrorism, how social media is used in espionage, and keeping your employees and your company safe from foreign spies.
Topics: "Soul Catcher: The Metaphysics of Recruiting a Spy" with Jim Lawler, Former Senior CIA Ops Officer
"Delusion and Illusion in Moscow" with Jonna Mendez in conversation with Valerie Plame, Former Covert CIA Ops Officer
"CIA in the Movies" - Panel;
"China: An Emerging Threat" with Mary Beth Long, Former Assistant Secretary of Defense for International Security Affairs
"Inside Putin's Head" with Rolf Mowatt-Larssen, Former Senior CIA Intelligence Officer
"Clarity in Crisis: Leadership Lessons from the CIA" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"Disinformation Distortions: AI, Deep Fakes, and Everything You Always Wanted to Know About Social Media and Espionage" with Alma Katsu, Former Senior CIA and NSA Analyst
"Morality and Ethics in the CIA" with Doug London, Former Senior Officer in the CIA's Clandestine Service
Michael Morrell in conversation with Valerie Plame, Former Covert CIA Ops Officer
"Eliminating Players on the Intelligence Battlefield: Havana Syndrome" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"The End of the Global Nuclear Order" with Valerie Plame, Former Covert CIA Ops Officer
Program also includes: Former Senior CIA Intelligence Officer; Michael J. Morell, Former CIA Deputy Director
FEE: Early Bird purchase window: Apr 12 - Jun 15, $1200; Regular Sale purchase window: Jun 16 - Nov 2, $1300; Late Sale purchase window: Nov 3 - Nov 10, $1450
Ticket price does not include accommodations. More about accommodations here
Tickets include breakfasts, lunches, VIP reception and all speaker presentations and activities.
Conference location: Conference Location: La Fonda On the Plaza, 100 E. San Francisco Street, Santa Fe, NM 87501
More information or to register here
Access CIA's Inhouse Gift Shop
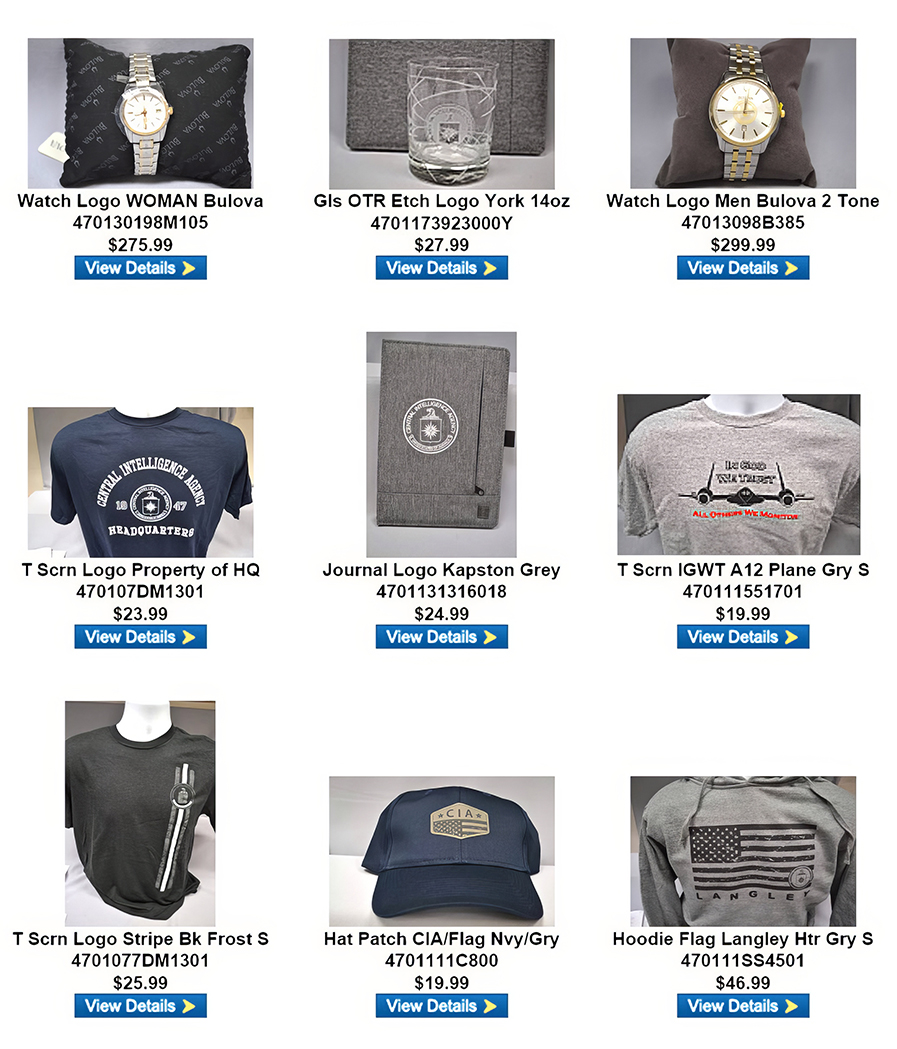
One special benefit of AFIO membership is access to CIA's EAA Store.
After completing the required, quick pre-approval process for all AFIO members, described here, you can purchase directly from the EAA online store their unusual logo'd gift items for self or colleagues. EAA on 12 May 2023 released the photo above, which features some of their newest CIA items and other gift suggestions.
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
Suspected Chinese spies, disguised as tourists, tried to infiltrate Alaskan military bases - USA Today, 31 May 23
Chinese citizens posing as tourists but suspected of being spies have made several attempts in recent years to gain access to military facilities in this vast state studded with sensitive bases, according to U.S. officials. In one incident, a vehicle with Chinese citizens blew past a security checkpoint at Fort Wainwright in Fairbanks, several soldiers told USA TODAY. The vehicle was eventually stopped, and a search found a drone inside the vehicle. The occupants claimed they were tourists who had gotten lost. Many of the encounters have been chalked up to innocent mistakes by foreign visitors intent on viewing the northern lights and other attractions in Alaska, officials say. Other attempts to enter U.S. military bases, however, seem to be probes to learn about U.S. military capabilities in Alaska, according to multiple soldiers familiar with the incidents but who were not authorized to speak publicly about them. (Full article here.)
U.S., ROK Agencies Alert: DPRK Cyber Actors Impersonating Targets to Collect Intelligence - NSA, 01 Jun 23
The National Security Agency (NSA) is partnering with several organizations to highlight the Democratic People’s Republic of Korea’s (DPRK) use of social engineering and malware to target think tanks, academia, and news media sectors. To help protect against these DPRK attacks, NSA and partners are publicly releasing the Cybersecurity Advisory (CSA), “North Korea Using Social Engineering to Enable Hacking of Think Tanks, Academia, and Media.” “DPRK state-sponsored cyber actors continue to impersonate trusted sources to collect sensitive information,” said Rob Joyce, NSA director of Cybersecurity. “Education and awareness are the first line of defense against these social engineering attacks.” The agencies — the Federal Bureau of Investigation (FBI), U.S. Department of State, and the Republic of Korea’s (ROK) National Intelligence Service, National Policy Agency, and Ministry of Foreign Affairs — have observed sustained information gathering efforts originating from a specific set of DPRK cyber actors known collectively as Kimsuky, THALLIUM, or VELVETCHOLLIMA. (Full article here.)
Lack of transparency from intelligence agencies, Taumaru report finds - RNZ, 29 May 23
A comprehensive review into New Zealand's national security system has found there is a lack of transparency from intelligence agencies on their activities, and is concerned over the effectiveness of control and oversight mechanisms. The Taumaru report is the first review into New Zealand's intelligence and security laws since the Intelligence and Security Act was established in 2017. Since then, the country has experienced two terror attacks, and seen a rise in cybersecurity threats, foreign interference, and disinformation. The 274 page report, written by former Solicitor General Sir Terence Arnold and prominent Māori lawyer Matanuku Mahuika, looked into the operations and oversight of New Zealand's two intelligence and security agencies: The Government Communications Security Bureau (GCSB) and the New Zealand Security Intelligence Service (NZSIS). It made 52 recommendations, which the government will now consider. (Full article here.)
North Korea says spy satellite launch crashed into sea - BBC, 31 May 23
Pyongyang announced earlier it planned to launch a satellite by 11 June to monitor US military activities. It now says it will attempt a second launch as soon as possible. The launch sparked a false alarm in the South Korean capital Seoul, while in Japan a warning was issued to residents of Okinawa, in the south. There was chaos and confusion in Seoul as people awoke to the sound of an air raid siren and an emergency message telling them to prepare for an evacuation - only to be told 20 minutes later it had been sent in error. The stakes are high on the Korean Peninsula, where tensions have existed between the two countries for 70 years, and this false alarm could seriously damage people's trust in the alert system. North Korea poses a threat to South Korea, and if there is an alert in the future one question being asked is whether it will be taken seriously, or brushed off as another mistake. (Full article here.)
How Ukrainian military spies are beating their Russian rivals - The Times, 27 May 23
President Volodymyr Zelensky has denied Ukraine has any designs on Vladimir Putin’s life but last week the deputy head of Ukrainian military intelligence was much less circumspect. Vadym Skibitsky told the German newspaper Die Welt that the Russian president was at the top of its death list “because he co-ordinates and decides what happens”. A British intelligence source cautioned: “I wouldn’t assume it’s just bravado.” The cross-border raid into Russia a few days earlier — carried out by Russian pro-Kyiv forces but probably organised by Ukrainian military intelligence — was proof of their ambition and capabilities. He added: “They are willing to cross a lot of red lines.” (Full article here.)
Mossad agent who died in Italy was on mission working against Iran - Jerusalem Post, 29 May 23
The Mossad and Italian intelligence personnel that were on the boat that capsized earlier this week at Lake Maggiore in northern Italy were working together to prevent Tehran from obtaining advanced weapons, according to a Friday report by the Italian newspaper La Repubblica. The operation was exposed when the boat sunk, killing four people, including one retired Mossad agent, the report said. Others that drowned include two that worked for Italian intelligence as well as the wife of the ship's captain. The collaboration of the two espionage organizations reportedly began following Italian media reports which claimed that Russian oligarchs were operating in the area and taking part in transferring Iranian-manufactured UAVs to Moscow. (Full article here.)
‘Spymania’ grips Russian security services amid sharp rise in treason cases - The Guardian, 04 Jun 23
As Russia’s war in Ukraine has grown into an existential conflict for the Kremlin over the past 15 months, its search for internal enemies has intensified, with a sharp rise in treason cases that experts have equated to a “spymania”. While many of the treason cases focus on those allegedly fighting for or aiding Ukraine, others have burrowed into seemingly loyal state institutions such as the scientific research centres that helped research the very weaponry that Russia is using to strike Ukraine. Last week, the first of three hypersonic missile scientists to be arrested on suspicion of treason went on trial in a case where the evidence and accusations remain secret. All were from a single institute in Novosibirsk, the Khristianovich Institute of Theoretical and Applied Mechanics (ITAM). Anatoly Maslov, a 76-year-old professor of aerodynamics at the institute, is thought to be suspected of passing secrets to China, possibly a result of his participation in international conferences on aerodynamics in the 2010s. (Full article here.)
Former Spymaster Hakan Fidan Assumes Leadership Of Turkey's Foreign Ministry - Forbes, 04 Jun 23
Hakan Fidan, the former head of the Turkish National Intelligence Organization (MIT), has been appointed as the country's new foreign minister. This shift isn't merely a bureaucratic reshuffle; it's a clarion call to every external stakeholder, from the U.S. to the European Union, from Russia to the labyrinthine politics of the Middle East. For years, his intelligence portfolio dictated his involvement in international affairs, shaping him as a significant figure in the nation's political landscape. However, the change in office is not just a transition from a follower of established procedures to a pioneer of original ideas. Fidan was already one of the most significant foreign policy actors in Turkey. Now, the seat of the Foreign Minister lies before him, presenting a pivotal opportunity to leave an indelible mark on the global stage. Fidan will now affix his name to the papers, endorsing the very processes he set in motion, bridging the gap between intelligence gathering and policymaking. In a previous article, I explained the strategic determinants of Turkish foreign policy, which bear Fidan’s extensive influence. (Full article here.)
China’s anti-espionage chief urges stronger crackdown using legal tools - South China Morning Post, 05 Jun 23
China’s anti-espionage chief Chen Yixin has called on senior officials to study the country’s new anti-espionage law and intensify its “legal crackdown” related to state security. Chen, a confidant of President Xi Jinping appointed as minister of state security in October, made the remarks in a bylined front page commentary published on Monday in the Study Times, an official newspaper of the Central Party School. “[We] must take the lead in the study of the law with focus on the newly amended Anti-espionage Law of the People’s Republic of China, and systematically grasp national security laws and regulations,” Chen said in the commentary. “[We] must use the law for struggles, ramp up the intensity of the crackdown in law enforcement and in judicial means, and enhance our capacity to shape state security using legal tools.” Chen added the state security apparatus must roll out anti-espionage efforts according to Chinese law and “severely crack down” on efforts to steal China’s state secrets. (Full article here.)
Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
- Court reduces sentences in spy case - Taipei Times, 03 Jun 23
- Former Air Force Intel Leader Gets Lenient Sentence for Hoarding Classified Information - Clearance Jobs, 02 Jun 23
- Taiwan raids 8 Chinese companies for alleged tech espionage - Taiwan News, 29 May 23
- Albanian court releases Russian and Ukrainian bloggers suspected of espionage - Intel News, 29 May 23
- Azerbaijani student who disappeared three months ago in Iran accused of espionage - JAM, 02 Jun 23
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
The Latest from International Spy Museum Historian Andrew Hammond, PhD.
 Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
30 May | From the Vault: "El Chapo, The War on Drugs, and Intelligence" with Noah Hurowitz Noah Hurowitz joins Andrew to discuss infamous drug kingpin El Chapo. A weak link in his cybersecurity set-up would help bring him down.
Past episodes:
23 May | "70th Anniversary of James Bond Special" with Alexis Albion, Part II
16 May | "70th Anniversary of James Bond Special" with Alexis Albion, Part I
09 May | "St. Ermin's Hotel London" - The History of a Legendary Spy Site
The Latest Insights from Former CIA Acting Deputy Director for Operations Jack Devine.
 In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
02 Jun | Putin is downplaying recent attacks on Russia, but if these attacks continue, they could alter the nature of the conflict. This week, Russia continued its unprovoked and relentless attack on Ukraine, again targeting Kyiv multiple times and killing several civilians, including children. Meanwhile, at several key meetings in Europe, Ukraine’s allies have been trying to figure out the best way to support Ukraine going forward, including potential NATO membership. Allies are also trying to navigate their response to an uptick of attacks within Russia, and how to contain regional instability in places like Kosovo. (Full version available to AFIO members in the coming days here.)
18 May | Ukraine and allies demonstrate the impact of a committed defense.
Daily Analysis of Security Issues and Geopolitical Trends
 Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
06 Jun | Disinformation with Chinese Characteristics
The People’s Republic of China (PRC) has historically utilized censorship, propaganda, and disinformationtargeting its own population, and has also utilized similar tactics to target audiences outside of the country’s borders. The PRC’s tactics, capabilities, and goals have evolved in recent years, particularly since 2019; it is now one of the more proficient state actors utilizing malign information manipulation targeting online users, especially on social media. Like many state and non-state actors, Beijing has determined it can make progress on a number of its foreign policy objectives by operating in and through the gray zone, relying on non-kinetic activities like disinformation and cyber-attacks that provide a significant return on investment. (Full brief here.)
02 Jun | Could the Conflict in Sudan Attract Significant Numbers of Foreign Fighters and Mercenaries?
01 Jun | Wagner Group Preparing to Exit Bakhmut as Uncertainty Surrounds Prighozin’s Next Move
31 May | Summit with Central Asian Leaders Advances Xi’s Geostrategy
Analysis of Global Security Events with WTOP National Security Correspondent JJ Green
 Inside the SCIF - 25 May - A Perfect Cyber Storm, Major Chinese Hack of US, Another Russian Mystery Death, and more...
Inside the SCIF - 25 May - A Perfect Cyber Storm, Major Chinese Hack of US, Another Russian Mystery Death, and more...
 Target USA Podcast - 24 May - Warning for those growing tired of the war in Ukraine
Target USA Podcast - 24 May - Warning for those growing tired of the war in Ukraine
The Hunt Broadcast - 24 May - Man carrying Nazi flag crashes U-Haul into White House barriers
The Latest Insights from Jeff Stein and Colleagues in SpyTalk (Substack)
05 Jun | Turncoat Hanssen Was a Very Weird Dude - Jeff Stein
The one thing that sticks in my mind about my Vietnamese spy all these decades later is how he picked at the black mole on his right cheek bone with an elongated pinkie finger nail. That, and the stubby, anthracitic French cigarettes he incessantly smoked during our monthly meet-ups in a stifling ramshackle hotel room. Middle aged, an anticommunist fanatic, I didn’t know him long enough to discover other bad habits. I’m sure he had them.(Full article here.)
04 Jun | Taiwan is Losing its Spy Wars with China... - Matt Brazil
If you follow developments in Beijing’s worldwide espionage and influence offensive, you’ve probably heard that the FBI opens a case regarding China every 10 hours (the 2020 figure) or 12 (2021). Doing the math, 8,760 hours per annum means something like 876 new cases a year, or in the updated version, 730. These are only the new cases, not the total figure for open investigations—which could add up to several thousand, as such inquiries can last for months or years without resolution, public or private. Beyond the small number of cases the Justice Department brings to indictment and trial each year, it does not say how many cases it has closed. The numbers suggest an overwhelming challenge, even as the Bureau bolsters its efforts to combat Chinese counterintelligence, counterespionage, tech transfer, and other matters—not to mention its drive to recruit special agents with Chinese language skills. (Full article here.)
03 Jun | About That Beluga Whale Spy... - Jeff Stein
Calder Walton is one of the world’s leading scholars of intelligence and national security. An historian at Harvard’s Kennedy School of Government, he received a doctorate in history from Trinity College, Cambridge, where he also helped to write an authorized hundred-year history of MI5, Britain’s principal counterespionage agency. Not only that, Walton, a Brit, is general editor of the three-volume Cambridge History of Espionage and Intelligence. But this week he came on the SpyTalk podcast to discuss his new book, Spies: The Epic Intelligence War between East and West. It’s chock full of interesting revelations and tidbits. (Full article here.)
29 May | OSS Agents in Repose, After the Guns Fell Silent - Jeff Stein
It’s hard to believe now, but at the outset of World War Two America had no organization in charge of synchronizing intelligence gathered by the military services and State Department, much an outfit less to wage unconventional warfare against Germany and Japan. It wasn’t until June 13, 1942, a little over six months after Japan’s surprise attack on Pearl Harbor, that President Franklin D. Roosevelt signed into law the creation of the Office of Strategic Services, which by the end of the war three years later employed 13,000 people engaged in dirty tricks ranging from espionage to sabotage, codebreaking and psychological warfare. (Full article here.)
27 May | Henry Kissinger: Killer Case Officer - Jeff Stein
To support SpyTalk, subscribe here.
Section III - MEMBER CONTRIBUTIONS
Article: Developing An Unbreakable Cybersecurity System - Semiconductor Engineering, 01 Jun 23
Cyberattacks are increasing in frequency and sophistication, and the impact of those attacks is increasing almost exponentially as the amount and value of data continues to grow. Cybersecurity Ventures projected the annual cost of cybercrime will grow from $8 trillion in 2023 to $210.5 trillion by 2025, with no end in sight. On the target list are a slew of industrial and commercial segments, including health care, infrastructure, banking, and education, as well as government agencies. The question now is how “unbreakable” can these systems really be, and what is the cost? More cyberattacks are coming. In April 2023, NCR was attacked. BlackCat ransomware hackers hit the company’s Aloha point of sales (POS) application, blacking out data center operations for NCR hospitality customers. In March 2023, Western Digital reported a ransomware attack on its online memory platform, My Cloud Home, creating frustration for its users. Bloomberg reported that the crime also compromised 16,000 Western Digital users’ Social Security numbers. The list goes on. (Read full report here.)
Article: Exclusive: World's spy chiefs meet in secret conclave in Singapore - Reuters, 04 Jun 23
Senior officials from about two dozen of the world's major intelligence agencies held a secret meeting on the fringes of the Shangri-La Dialogue security meeting in Singapore this weekend, five people told Reuters. Such meetings are organised by the Singapore government and have been discreetly held at a separate venue alongside the security summit for several years, they said. The meetings have not been previously reported. The U.S. was represented by Director of National Intelligence Avril Haines, the head of her country's intelligence community, while China was among the other countries present, despite the tensions between the two superpowers. Samant Goel, the head of India's overseas intelligence gathering agency, the Research and Analysis Wing, also attended, an Indian source said. "The meeting is an important fixture on the international shadow agenda," said one person with knowledge of the discussions. "Given the range of countries involved, it is not a festival of tradecraft, but rather a way of promoting a deeper understanding of intentions and bottom lines. (Read full report here.)
Article: Russia's FSB says US penetrated thousands of Apple phones in spy plot - Reuters via Jerusalem Post, 01 Jun 23
Russia's Federal Security Service (FSB) said on Thursday that it had uncovered a US National Security Agency (NSA) plot using previously unknown malware to penetrate specially made backdoor vulnerabilities in Apple phones. The FSB, the main successor to the Soviet-era KGB, said that several thousand Apple phones had been infected, including those of domestic Russian subscribers. The Russian spy agency also said telephones belonging to foreign diplomats based in Russia and the former Soviet Union, including those from NATO members, Israel, Syria and China, had been targeted. (Read full report here.)
Article: North Korea targets U.S. intel figures on a secret cyber hit list - Washington Times, 02 Jun 23
Details of a secret North Korean cyber hit list are spreading in Washington, with a widening slate of high-level current and former U.S. intelligence officials, media executives and national security scholars finding themselves in the hackers’ crosshairs. The Biden administration is scrambling to respond. The FBI, the National Security Agency and the State Department are preparing a new cyber strategy to specifically counter what officials describe as a sophisticated North Korean “spear phishing” threat. The administration remains tight-lipped about the effort, although sources familiar with it say the strategy will be made public in the coming days. (Read full report here.)
Article: CIA Chief Made Secret Trip to China - Wall Street Journal, 02 Jun 23
CIA Director William Burns made a secret trip to China last month in a bid to keep lines of communication open, a U.S. official said Friday, as security relations between the two global powers grow increasingly acrimonious. Burns’ trip to Beijing was the highest-level visit by a Biden administration official since the U.S. and China tangled over a suspected Chinese spy balloon earlier this year. It comes as the two countries are increasingly at odds over the self-governing island of Taiwan, the war in Ukraine and other issues. “Last month, Director Burns traveled to Beijing, where he met with Chinese counterparts and emphasized the importance of maintaining open lines of communication in intelligence channels,” the official said. (Read full report here.) (NOTE: This material may require a free registration or sit behind a pay wall.)
Article: China Investing in Open Source Intelligence - New York Times, 01 Jun 23
China’s intelligence agencies are investing deeply in open-source intelligence to learn more about the capabilities of the American military in the Pacific and beyond, according to a new report. The analysis, by the threat intelligence company Recorded Future, details efforts by China’s government and companies to collect publicly available data from the Pentagon, think tanks and private firms — information Beijing’s military can use to help plan for a potential conflict with the United States. As the relationship between the United States and China has become more adversarial, both countries are investing more in their intelligence collection capabilities. With Beijing’s investments in big data management, mining publicly available sources of information could give China an advantage in collecting intelligence on the United States and its allies. (Read full report here.) (NOTE: This material may require a free registration or sit behind a pay wall.)
Article: U.S. Prepares New Massive Intelligence Collection Center in Hezbollah-Controlled Beirut - The Foreign Desk, 31 May 23
Over the weekend, reports from United States intelligence sources revealed that the Central Intelligence Agency (CIA) is building a new regional hub in Lebanon within an embassy complex containing an area of 93,000 square meters in the country’s capital, Beirut. The new site is currently under construction in Awkar, a town in the Northern Province of Lebanon, far away from the Southern Province occupied by the Iranian-backed Islamic terrorist group Hezbollah. According to the French Intelligence Online website, the complex will cost around $1 billion, containing a hospital, arts center, swimming pool, residential towers, and data collection center for US intelligence officials. Given Lebanon’s closeness to Syria, US intelligence officials consider the country a safe and strategic location for sending intelligence agents and personnel from agencies in Washington, DC. On Twitter, the official US Embassy of Beirut page posted photographs of the project’s construction and Lebanese Foreign Minister Abdallah Bou Habib and the US State Department Overseas Buildings Operations (OBO) Director touring the building site. (Read full report here.)
Article: FBI gearing up for new anti-encryption campaign - Washington Times, 30 May 23
The FBI is ramping up its push to undermine digital encryption, which law enforcement officials say prevents them from more easily catching criminals. Civil liberties advocates oppose the FBI‘s efforts to create digital back doors for the government and say the feds’ wish means making defective tech products that may create new victims. The FBI is seeking to collect data on the number of times encryption has obstructed its work, and submitted a notice in the Federal Register. The notice set a June 23 deadline for public comment on the FBI‘s proposal to “collect data on the volume of law enforcement investigations that are negatively impacted by device and software encryption." The notice does not include a request for the number of times the FBI has tried to bypass encryption, nor does the request ask for data on the number of times the bureau has successfully breached people’s devices. (Read full report here.) (NOTE: This material may require a free registration or sit behind a pay wall.)
Article: Intelligence Officials Say U.S. Has Retrieved Craft of Non-Human Origin - The Debrief, 05 Jun 23
A former intelligence official turned whistleblower has given Congress and the Intelligence Community Inspector General extensive classified information about deeply covert programs that he says possess retrieved intact and partially intact craft of non-human origin. The information, he says, has been illegally withheld from Congress, and he filed a complaint alleging that he suffered illegal retaliation for his confidential disclosures, reported here for the first time. Other intelligence officials, both active and retired, with knowledge of these programs through their work in various agencies, have independently provided similar, corroborating information, both on and off the record. The whistleblower, David Charles Grusch, 36, a decorated former combat officer in Afghanistan, is a veteran of the National Geospatial-Intelligence Agency (NGA) and the National Reconnaissance Office (NRO). He served as the reconnaissance office’s representative to the Unidentified Aerial Phenomena Task Force from 2019-2021. From late 2021 to July 2022, he was the NGA’s co-lead for UAP analysis and its representative to the task force. (Read full report here.)
Article: Robert Hanssen, an FBI agent who was convicted of spying for Russia, dies in prison - Associated Press, 05 Jun 23
Robert Hanssen, a former FBI agent who took more than $1.4 million in cash and diamonds to trade secrets with Moscow in one of the most notorious spying cases in American history, died in prison Monday. Hanssen, 79, was found unresponsive in his cell at a federal prison in Florence, Colorado, and later pronounced dead, prison officials said. He is believed to have died of natural causes, a person familiar with the matter told The Associated Press. The person was not authorized to publicly discuss details of Hanssen's death and spoke to the AP on condition of anonymity. He had been serving a sentence of life in prison without possibility of parole since 2002, after pleading guilty to 15 counts of espionage and other charges. (Read full report here.)
Book Review: Code Name Blue Wren - Washington Times, 01 Jun 23
Some years ago, when I was a young man performing security work as a civilian Defense Department employee, I attended a briefing at the headquarters of the Defense Intelligence Agency at Bolling Air Force Base in Washington. Although I didn’t know it at the time, Ana Montes was also at Bolling, working as an intelligence analyst. Years later, I read about her arrest as a spy for Cuba. I’ve long been interested in her case, and I recently read Jim Popkin’s most interesting book about her, “Code Name Blue Wren: The True Story of America’s Most Dangerous Female Spy — and the Sister She Betrayed.” I contacted Mr. Popkin and asked him when he first became aware of Ms. Montes. (Read full report here.)
Report: Russian forces were suffering from ‘electronic fratricide’ within days of attacking Ukraine, a new report says - Station HYPO, 05 Jun 23
In the first days of Russia’s invasion of Ukraine, Russian jamming disrupted Ukraine’s air-defense radars and communications links. The problem for Russian forces is that their electronic warfare also jammed their own communications. This “electronic fratricide” became so acute that Russian troops had to stop disrupting Ukrainian communications, according to a study by the Royal United Services Institute, a British think tank. By the end of the first week of the invasion, Russian ground forces being unable to effectively communicate “became a greater threat to the Russian operation than Ukrainian [surface-to-air missile] systems, so their electronic warfare assets began to greatly scale back their operations after the first two days,” the RUSI report says. Initially, Russia’s jamming offensive was devastating and validated Moscow’s heavy investment in electronic warfare. For years, the Pentagon has worried it lags far behind Russia in electronic-warfare capabilities, which could disrupt the extensive communications networks that enable the US military to fight in a coordinated fashion. Generally, Russian electronic-warfare systems “have actually proven extremely effective,” Nick Reynolds, a coauthor of the RUSI study, told Insider, and Russia’s initial onslaught in Ukraine seemed to bear out the Pentagon’s fears. (Read full report here.)
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
Cyber-enabled tradecraft and contemporary espionage: assessing the implications of the tradecraft paradox on agent recruitment in Russia and China - Journal of Intelligence and National Security, 02 Jun 23
The acquisition of clandestine human sources – or agents – inside Russia and China likely remains the key priority for Western HUMINT agencies, and yet their ability to do this safely is quickly waning. This paper considers the utility of cyberspace for espionage recruitment in these two hard target states, and assesses its value as a potential solution to emerging surveillance threats. With the aid of history, this paper proposes that hard target espionage is fundamentally afflicted by a tradecraft paradox, one that will severely curtail the utility of cyberspace to agent recruitment. (Full report here.)
Iran: How to counter covert action in the digital age - Chatham House, 30 May 2023
Governments, military forces and non-state groups use covert action to understand – and influence – what their adversaries and allies are doing. The digital age has created many new opportunities for covert action, but has also made traditional strategies much harder to conceal. Digital capitalism’s thirst for data generates detailed online footprints, whether working, shopping or spying. In this environment, three key strategies for covert action have evolved. The first is implausible deniability, such as Russia’s ‘little green men’ in Ukraine after 2014 – a course of action forced, in part, by Russian soldiers using geolocated photos and apps on the front line. The second is to use distraction and disinformation, hiding embarrassing or sensitive facts in a forest of false counterclaims. The third is to attempt to shield certain audiences from leaks, imposing censorship to limit domestic impact from international scandal, a strategy more often used by states with authoritarian tendencies. Countering these changing strategies requires transparency, persistence and international cooperation, as evidenced by the case of Iran. (Full report here.)
Chinese Next-Generation Psychological Warfare - RAND, 01 Jun 23
China views psychological warfare, centered on the manipulation of information to influence adversary decisionmaking and behavior, as one of several key components of modern warfare. The U.S. military's increased focus on China and preparations for a potential U.S.-China conflict mean that it is important to understand how Chinese psychological warfare capabilities may evolve and what they would mean for Chinese strategic behavior in a crisis or conflict. The author explores Chinese military thinking about next-generation psychological warfare. China is interested in both advanced computing, such as big data, and brain science for their potential military applications to improve future psychological warfare capabilities. Leveraging a wide array of Chinese-language primary-source materials, the author provides an overview of Chinese thinking on psychological warfare, key capabilities, and related operational concepts that the Chinese military is pursuing and presents a hypothetical case study to illustrate how these capabilities, if realized, may be applied to a future U.S.-China contingency. One high-risk future scenario is if the Chinese military and broader leadership believes that these emerging technologies enable Beijing to predict or otherwise influence adversary decisionmaking. This could lead Beijing to have misplaced confidence in its ability to deter adversaries from fighting or coerce them to not fight at all. (Full report here.)
Complexity in Military Intelligence - International Journal of Intelligence and Counterintelligence, 30 May 2023
Intelligence studies missed social science’s “complexity turn” more than twenty years ago. The aim of this article is to examine military intelligence from a complexity science perspective and discuss related concepts such as sensemaking and reflexivity. For this, military and intelligence theory, doctrine, and practice are studied. Complexity insights from military sciences are used to review mental models and current thinking in military intelligence. Rather than viewing it as a clearly defined and autonomous field or function embodied by a closed intelligence cycle, military intelligence is best seen as a situated practice. This situatedness is illustrated in two cases regarding vertical and horizontal contextual influences. First, a discussion of North Atlantic Treaty Organization deployments in Afghanistan shows important vertical influences: the impact of (political) context and task. Second, a review of United Nations missions exemplifies the horizontal dimension: the need for informal collaboration, ad hoc organization, and a holistic approach. However, both cases show vertical and horizontal influences. Overall, this article stresses the applicability of sensemaking rather than the intelligence cycle and makes suggestions for further incorporating complexity research into intelligence. (Full report here.)
Dispelling Myths: How Classification and Declassification Actually Work - Justice Security, 02 Jun 23
The discovery of classified documents in the personal residences and offices of Donald Trump, Mike Pence, and Joe Biden have reinvigorated a public conversation surrounding the U.S. government’s classification system that seems to emerge every few years. In 2015, it was former Secretary of State Hillary Rodham Clinton’s use of a private email server. In 2010 and 2013, it was disclosures by Chelsea Manning and Edward Snowden, respectively. Yet, despite the long history of classified document scandals, many journalists, judges, lawyers, and other outside observers hold fundamental misconceptions about how classification and declassification actually work in the federal government on a day-to-day basis. Since the Mar-a-Lago scandal broke, numerous well-intentioned articles have attempted (see here, here, and here) to explain classification and declassification to the public, along with prolific pontificating from “experts” on Twitter, but this commentary often overlooks basic realities about how the U.S. classification system operates. Drawing from the authors’ experiences at the Central Intelligence Agency and Department of Defense, this article seeks to dispel several myths that have emerged about classification and declassification, particularly regarding presidential and vice-presidential authority, while also providing perspective on how these processes are carried out in the real world. (Full report here.)
Comparing Population Pyramids Around the World - Visual Capitalist, 01 Jun 23
Demographic data can reveal all kinds of insights about a population, from the country’s fertility and mortality rates to how certain events and policies have shaped the makeup of a population. Population pyramids are one of the best ways to visualize population data, and comparing the pyramids of various countries and regions side-by-side can reveal unexpected insights and differences between groups. This graphic uses population data from the United Nations to compare the demographics of some select nations and regions of the world, showcasing how much age distributions can vary. (Access visual tool and full report here.)
Intelligence in History - A Collection of Recent Content
- Article - Australian intelligence's secret hand in bringing down the Bali bombers - ABC Australia, 03 Jun 23
- Article - They served in the CIA’s first ‘secret war’ – and are finally being recognized - Yahoo News, 02 Jun 23
- Article - Leonie, Actress and Spy review – greatest-hits profile of mysterious wartime double-agent - The Guardian, 05 Jun 23
- Presentation - Queen of Codes - British National Archives, 07 Jul 23
- Paper - A seat at the president’s table? Lyndon Johnson, the CIA, and the Six Day War - Journal of Intelligence and National Security, 01 Jun 23
- Article - Anthony Blunt: The British-Russian Spy Who Collected Royal Secrets - Spyscape, 01 Jun 23
- Invitation to Join - Soviet Intelligence History Research Group : NASIH - Intelligence History, 01 Jun 23
- Readout - NSA Cryptologic History Symposium - NSA, 01 Jun 23
- Paper - Sempill, Japan, and Pearl Harbor: Traitor or Spy-Myth? - International Journal of Intelligence and Counterintelligence, 02 Jun 23 (original publication 25 Jul 22)
- Paper - Innovators, Copycats, or Pragmatists? Soviet Industrial Espionage and Innovation in the Military Aerospace Sector during the Cold War - International Journal of Intelligence and Counterintelligence, 02 Jun 23 (original publication 30 Aug 22)
True Intelligence Matters in Film - Reality - Tina Satter (2023)
 Reality is a 2023 American drama film directed by Tina Satter, from a screenplay by Satter and James Paul Dallas. It is based on the FBI interrogation transcript of American intelligence leaker Reality Winner, which Satter previously staged as the play Is This a Room. It stars Sydney Sweeney as Winner, with Marchánt Davis and Josh Hamilton in supporting roles. Reality premiered at the 2023 Berlin International Film Festival on February 18, 2023, and released on May 29, 2023, by HBO Films. It has received critical acclaim, with praise for Satter's direction and Sweeney's performance.
Reality is a 2023 American drama film directed by Tina Satter, from a screenplay by Satter and James Paul Dallas. It is based on the FBI interrogation transcript of American intelligence leaker Reality Winner, which Satter previously staged as the play Is This a Room. It stars Sydney Sweeney as Winner, with Marchánt Davis and Josh Hamilton in supporting roles. Reality premiered at the 2023 Berlin International Film Festival on February 18, 2023, and released on May 29, 2023, by HBO Films. It has received critical acclaim, with praise for Satter's direction and Sweeney's performance.
More information about this based-on-true-events production here.
Walking Tours - Washington, DC - Sundays (Dates/Times Vary)
Former intelligence officers guide visitors on two morning and afternoon espionage-themed walking tours: "Spies of Embassy Row" and "Spies of Georgetown." For more information and booking, click here or contact rosanna@spyher.co
Section V - Books, Research Requests, Jobs, Obituaries
Books — Forthcoming, Newly Released, Overlooked
 Revealing Secrets: An unofficial history of Australian Signals intelligence and the advent of cyber
Revealing Secrets: An unofficial history of Australian Signals intelligence and the advent of cyber
by Clare Birgin and John Blaxland
(New South Wales University Press, 01 May 23)
For a long time, the Australian Signals intelligence (or Sigint) story has been kept secret. Until now... Why does Australia have a national signals intelligence agency? What does it do and why is it controversial? And how significant are its ties with key partners, the United States, the United Kingdom, Canada and New Zealand, to this arrangement?Revealing Secrets is a compelling account of Australian Signals intelligence, its efforts at revealing the secrets of other nations, and keeping ours safe. It brings to light those clever Australians whose efforts were for so long entirely unknown or overlooked. Blaxland and Birgin traverse the royal commissions and reviews that shaped Australia' s intelligence community in the 20th century and consider the advent and the impact of cyber. In unearthing this integral, if hidden and little understood, part of Australian statecraft, this book increases our understanding of the past, present and what lies ahead.‘ George Orwell famously wrote during World War Two, “ we sleep safe in our beds because rough men stand ready in the night to visit violence on those who would do us harm” . Reading this superb history by John Blaxland and Clare Birgin on Australia' s involvement with Sigint and cyber we can contemplate a new formula. We sleep safer because 24/7 intelligent, technologically competent patriotic men and women who work for our agencies, develop and work our electronic defence and offence capacities at worldclass standard. This in a world now in which we are constantly under attack. The work so secret it is proving impossible to produce an official history. This is the closest we can get and it is very good.
Order book here.
 The Academic-Practitioner Divide in Intelligence Studies
The Academic-Practitioner Divide in Intelligence Studies
by Rubén Arcos, Nicole K. Drumhiller, Mark Phythian
(Rowman and Littlefield Publishers, 14 Apr 22)
Internationally, the profession of intelligence continues to develop and expand. So too does the academic field of intelligence, both in terms of intelligence as a focus for academic research and in terms of the delivery of university courses in intelligence and related areas. To a significant extent both the profession of intelligence and those delivering intelligence education share a common aim of developing intelligence as a discipline. However, this shared interest must also navigate the existence of an academic-practitioner divide. Such a divide is far from unique to intelligence – it exists in various forms across most professions – but it is distinctive in the field of intelligence because of the centrality of secrecy to the profession of intelligence and the way in which this constitutes a barrier to understanding and openly teaching about aspects of intelligence. How can co-operation in developing the profession and academic study be maximized when faced with this divide? How can and should this divide be navigated? The Academic-Practitioner Divide in Intelligence provides a range of international approaches to, and perspectives on, these crucial questions.
Order book here.
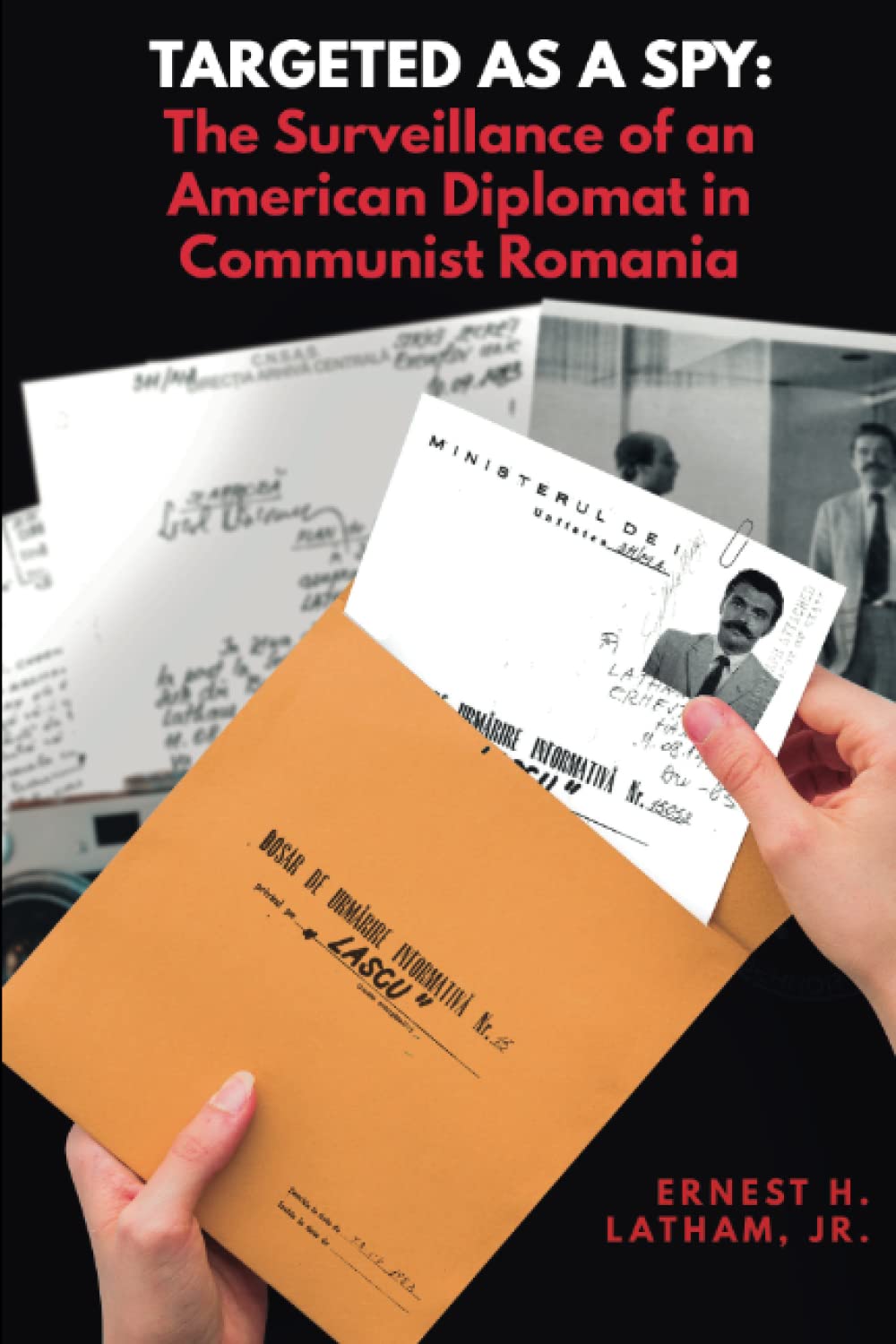 Targeted as a Spy: Surveillance of an American Diplomat in Communist Romania
Targeted as a Spy: Surveillance of an American Diplomat in Communist Romania
by Ernest H. Latham Jr.
(Histria Books, 10 Jan 23)
An often overlooked aspect of the Cold War was the extent of diplomatic espionage that went on in the countries behind the Iron Curtain. Every Western diplomat stationed in the Soviet bloc was targeted as a spy by the security apparatus in these countries. Now with the opening of archives in Eastern Europe, the extent of this diplomatic espionage is revealed for the first time. Ernest H. Latham, Jr. was a career Foreign Service Officer who served the United States in various posts in the Middle East and Central Europe. From 1983 to 1987, he was the cultural attaché at the American Embassy in Bucharest. During his time in Romania, Dr. Latham was targeted as a spy by the brutal Communist dictatorship of Nicolae Ceausescu and subjected to constant, intrusive surveillance by his dreaded and dreadful secret police, the Securitate. This book is a collection of surveillance reports that Dr. Latham obtained from the Romanian archives following the collapse of the Communist regime. They reveal the extent of the surveillance to which Western diplomats were subjected and, more importantly, they reveal a great deal about the system and society that conducted it. Latham’s introduction provides the context of his work and Romanian conditions at that time. This book is essential reading for students of the Cold War as well as anyone interested in the mindset and methods of totalitarian regimes. The esteemed professor of Romanian history and editor of this English edition, Dennis Deletant, has called it “a notable event” representing “a rare case of such a file – of a foreigner.... Latham’s role as the US cultural attaché between 1983 and 1987 marks him out in body as an outsider,” but “in spirit, an insider, sympathetic to the ambivalences and ambiguities of Romania's past.... His file reminds the reader of the intrusiveness of the Communist regime into the lives of citizens, be they Romanian or otherwise.”
Order book here.
Research Requests and Academic Opportunities
Northeastern University Security and Intelligence Studies professor researching the skill sets required for Intelligence Analysis degree holders to see success after graduation welcomes the participation of AFIO members in a 5-minute survey in support of the research. Access survey here.
Call for Information: 430th CIC in Salzburg in 1946
I am currently writing about 430th CIC in Salzburg in 1946. I have a (large) CIC file and am now trying to track down further details about two officers mentioned in this: (1) Bill Taylor. The sources do not make clear whether the officer was Major Bill G. Taylor, GSC, Head of the Counter-Intelligence Bureau of G-2 (Intelligence Section), US Forces Austria, or “Mil.Reg.” Captain Taylor of Salzburg. Any information on either/both of these officers would be most welcome. (2) Pace B Rose. Rose was a CIC Special Agent in Austria, later a CIA officer who continued to be attached to the Agency after retirement. He died on 3 January 2009. I would like to contact family and friends of Pace Rose. According to the internet, Rose had children, Donna R. Hilverts and Gary W. Rose, and five grandchildren and three great grandchildren. Please contact S.Cody@westminster.ac.uk with any information.
Call for Sources: Intelligence Officers Who Lived in Spain in the 1970s
Spanish journalist Francisco Jiménez is preparing a documentary about the intelligence services in Spain in the 70s. He is looking for intelligence officers who worked in Spain in those years. If you are willing to assist Francisco, he can be reached at fjimenez@globomedia.es.
The Washington Post is developing a multipart audio documentary series (i.e. podcast) chronicling the Grenadian revolution and the US intervention in 1983. They've interviewed nearly 100 people so far, ranging from the heads of state, former Grenadian officials, current and former US officials, veterans, and intelligence officers. They're looking for people who served at the time and may be knowledgeable about intelligence activities in Grenada and the southern Caribbean between 1979 and Operation Urgent Fury. They would also be interested in speaking with anyone who knew Leonard Barrett during the same period. If anyone is interested in participating, please reach out to Washington Post reporter Ted Muldoon via email at ted.muldoon@washpost.com or on Signal at 651-497-5449.
Call for papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
History shows that without planning for post-war reconstruction, apparent victory in war can lead to long-term defeat. On the other hand, wise post-war planning can lead to friendly, peaceful, and profitable relations between victor and vanquished. For political, socio-economic and security-related planning, intelligence plays a crucial role in estimating capabilities, securing infrastructure, locating persons of interest, and rebuilding. In honor of the 75th anniversary of the European Recovery Program (Marshall Plan) after the Second World War, the editors are particularly interested in papers dealing with intelligence concerning post-war reconstruction initiatives and planning connected to historical and recent conflicts. Both case studies and theoretical and methodological approaches are welcome. The studies may include, but do not have to be focused on, the following questions and issues:
- The role of diplomatic and military intelligence during the conflict as preparation for post-war reconstruction, from the conceptual to the practical.
- What intelligence needs to be collected to secure and boost reconstruction?
- What contacts, networks, and infrastructure are necessary for intelligence to be effective?
- Who has been or should be approached and/or recruited for reconstruction efforts based on intelligence?
- When has intelligent post-war planning (or its opposite) been historically evident?
- How should intelligence interact with formerly warring parties and international organizations to empower practical reconstruction efforts?
- What intelligence collection challenges have services encountered in working for post-war peace?
- How did intelligence factor in the European Recovery Program?
- What was George C. Marshall's position on the role of intelligence in general or concrete examples related to "his" plan?
01 Nov 23 deadline. More information and submission instructions here.
Call For Articles: AFIO Journal, The Intelligencer
For the past four years, AFIO has included in The Intelligencer a series of articles on "when intelligence made a difference." Written by scholars, intelligence practitioners, students, and others, they cover events from ancient times to the modern world and in many countries. AFIO is soliciting articles for future issues. Most articles run between 2,000 and 3,000 words, although some are longer or shorter. If you have an idea for an article that fits the theme, email senior editor Peter Oleson at peter.oleson@afio.com.
Jobs
Retired Federal Government Employees Wanted - National Security Agency - Fort Meade, Maryland
The National Security Agency (NSA) may occasionally need skilled civilian retirees to augment the existing work force on high priority projects or programs. In order to fill these temporary positions quickly, we need to know who may be interested and available to return to work with us on a short notice basis as well as their skills. Retirees provide expertise and corporate knowledge to temporarily support mission requirements, manpower shortfalls, and/or mentor the next generation of Agency employees. Salary Range: $86,335 - $170,800.
Additional information and application here.
Assistant/Associate Professor of Intelligence Studies (Global Security and Intelligence Studies) - Embry-Riddle Aeronautical University - Prescott, Arizona
Embry-Riddle Aeronautical University's Prescott, Arizona campus is accepting applications for a tenure-track assistant or associate-level professor of intelligence studies to teach intelligence courses to students in the Global Security and Intelligence program. The successful candidate will teach students about the intelligence community, strategic intelligence, the intelligence cycle and intelligence analysis, writing, and briefing. Prior experience working in the intelligence community is strongly preferred. We are interested in candidates with teaching acumen in intelligence analysis and writing using structured analytical techniques.
Additional information and application here.
Teaching Associate - Intelligence and National Security Studies - Coastal Carolina University, South Carolina
The Department of Intelligence and Security Studies ( ISS ) at Coastal Carolina University is accepting applications for a pool of Teaching Associates (part-time adjunct faculty) to teach introductory and undergraduate elective course offerings for the program beginning in August 2022. While the ad is open to any specialization within the field of study, courses in the areas of homeland security, law enforcement intelligence, counter-narcotics, and cybersecurity are of particular interest. Course offerings can be in a face-to-face or synchronous online modality. To be considered, candidates must have a masters or doctoral degree in a relevant subject area. Prior professional experience in the profession, as well as prior teaching experience are preferred.
Additional information and application here.
Obituaries
![]() Vern Hayes — Decorated Airforce Officer and CIA Officer
Vern Hayes — Decorated Airforce Officer and CIA Officer
Philip Vern Hays, retired Air Force officer, passed away on May 16, 2023, at the age of 80.V ern was born in Clinton, Indiana and attended Bedford High School and Indiana University. Wanting to serve his country, Vern joined the Air Force and shortly after graduation. Vern’s first posting was at James Connally AFB in Texas, followed by Pope AFB in North Carolina. Vern served as a C-130 navigator in Vietnam and was awarded the Distinguished Flying Cross for “extraordinary achievement while participating in aerial flight”. He attended Air Command and Staff College and earned his Master of Arts in Counseling from Troy State University. He later lived in the Philippines, Virginia, and New Jersey. Vern retired as a Lieutenant Colonel from the Air Force after 20 years. During his next phase of his life, Vern worked for the Central Intelligence Agency.
![]() Larry Hatch — Career NSA Cryptographer
Larry Hatch — Career NSA Cryptographer
Dr. Lawrence Otis Hatch, known to all as Larry Hatch, died on March 20, 2023 at the age of 88. He passed at home in Gorham, Maine. He spent his formative years growing up in Spruce Head, South Thomaston, Maine. After graduating from Rockland High School in Rockland, Maine in 1952, Larry received his BA in Mathematics from Brown University in 1956, his Master of Science in Mathematics from Purdue University in 1958 and his PhD in Statistics from the University of Connecticut in 1969. Larry had a lifelong love of Education. He was an Associate Professor of Mathematics at Northern Michigan University (1960-1962), a Professor of Mathematics at the Coast Guard Academy in New London Connecticut (1962-1969) and later served as an Adjunct Professor of Graduate Statistics at the University of MD, College Park. He had a distinguished career working in Cryptography with the National Security Agency (NSA) from 1969 to 1994 where he made many valuable contributions to our country. His love of education came into his work as well. He was key to the internal Education Program at NSA.
![]() Lahoma Dickey — NSA Research Analyst
Lahoma Dickey — NSA Research Analyst
LaHoma Esther Blackburn Johnson Dickey, 99, passed on May 13, 2023 of respiratory failure at her daughter and son-in-law’s home in Annapolis, MD. LaHoma was born in Pasadena, CA. She attended Glendale Academy in CA, Skiatook High School in OK and Pacific Union College near St Helena, CA. During WWII, she was recruited from college by the government to work someplace that they couldn’t tell her where and it would be for two years. She didn’t take that employment and instead ended up at the Pentagon and then the Army’s Signal Intelligence Service at Arlington Hall, VA which later became the National Security Agency in MD. She was a special research analyst who worked on the VENONA Project. After 26 years with the government she Temecula, CA.
![]() Ronald Gray — Career NSA Officer
Ronald Gray — Career NSA Officer
Ronald Hubert Gray, 77, of Odenton, Maryland, formerly of Kingsport, Tennessee passed peacefully in his hometown, May 27, 2023 after a brief illness. Born and raised in Sullivan County, he was a proud graduate of Dobyns-Bennett High School of 1965. He joined the U.S. Army at the age of 20 with a stint in Korea. After returning from service, he started a telecommunication career with ITT, North Electric and Siemens Automation. This led to a career of 35 years at NSA (National Security Agency).
Section VI - Events
19 Jun 23 (Monday), 1800 (Pacific) - Virtual - Peter Warmka, on "Confessions of a CIA Spy - The Art of Human Hacking, the topic and title of his recent book. Hosted by the Columbia River Chapter of AFIO. Warmka is a former Senior Intelligence Officer with the CIA having over 20 years of experience in breaching the security of target organizations overseas. He is an Adjunct Professor at Webster University's Masters in Cybersecurity Program and Founder of Orlando based firm Counterintelligence Institute, LLC. All AFIO members are welcome to tune in. For additional information and for the links and password to join the Zoom Meeting, email Chapter President Carl Wege here or call on 912-222-8640.
27 Jul 23 (Thursday), 1130 (Pacific) - In Person - Col. Robert W. Parr, USAF (ret) on "12 Days with a Soviet Pilot Defector" - Basque Cultural Center, San Francisco - The AFIO Andre LeGallo Chapter. No host cocktail at 1130 hours (Pacific). Meeting starts at 1200 hours. Basque Cultural Center, 599 Railroad Avenue, South San Francisco, CA. RSVP and pre-payment required. More information and registration here.
See the AFIO Calendar of Events for scheduling further in the future.
Events from Advertisers, Corporate Sponsors, Others
This year marks the 70th anniversary of the US-Republic of Korea (ROK) alliance. To commemorate this partnership formed for the greater good, join us for an unprecedented discussion with a former North Korean agent. International Spy Museum Historian and Curator Dr. Andrew Hammond will interview Kim, Hyun Woo about his extraordinary journey from North Korean agent to Senior fellow of the Institute for National Security Studies (INSS) in the ROK. Kim worked for the National Security Agency, DPRK—North Korea's Counterintelligence Agency—from 1998 to 2014. How did he break away from the country of his birth and become a resource for the INSS where he has worked since 2015? This organization has for more than 40 years been dedicated to intensive studies on unification, international relations, and security issues in order to ensure Korean national security. The INSS has more recently expanded its focus and scope of research to the field of global terrorism and cyber security while strengthening the existing research capability on traditional security issues. What insight does Kim's time in the DPRK bring to this mission? What does he imagine the future holds for the DPRK and its relationship to the rest of the world? Kim's unique viewpoint will inform this timely and wide-ranging conversation exploring the truth about North Korean capabilities and intentions. This program is in collaboration with the Embassy of the Republic of Korea. More information here.
International Spy Museum eventsJoin us in the Spy Museum Store for a special book signing event for Red London with author Alma Katsu. Alma Katsu is the award-winning author of seven novels, most recently Red London, Red Widow, The Deep, and The Hunger. Prior to the publication of her first novel, she had a thirty-five-year career as a senior intelligence analyst for several US agencies, including the CIA and NSA, as well as RAND, the global policy think tank. Katsu is a graduate of the masters writing program at Johns Hopkins University and received her bachelor's degree from Brandeis University. With Red London, Katsu continues to expertly layer the details and drama of some of the most elusive agencies in the nation into her story, while also capturing the complexities of the women at the center of the action. More information here.
Dr. Amy Zegart is the Morris Arnold and Nona Jean Cox Senior Fellow at the Hoover Institution and Professor of Political Science (by courtesy) at Stanford University. She is also a Senior Fellow at Stanford’s Freeman Spogli Institute for International Studies, Chair of Stanford’s Artificial Intelligence and International Security Steering Committee, and a contributing writer at The Atlantic. She specializes in U.S. intelligence, emerging technologies and national security, grand strategy, and global political risk management. In this talk, Zegart examines the past, present, and future of American espionage, focusing on how emerging technologies are radically challenging every aspect of the intelligence enterprise. An illuminating case study is nuclear threat detection. Zegart will share her findings that nuclear intelligence is not just for superpower governments anymore thanks to Internet connectivity, automated analytics, and commercial satellites. This talk will focus on the characteristics, benefits, and risks of this democratization of intelligence for threat detection and crisis management. Zegart will also discuss how technology is not a panacea for the intelligence community, how it can exacerbate existing biases, and how it must be used strategically to provide critical insights to the military, policymakers, and the American public. More information and registration here.
General Jim Mattis interviews Dr. Michael Vickers about his forthcoming book. In By All Means Available: Memoirs of a Life in Intelligence, Special Operation and Strategy, Vickers recounts his remarkable career, from his days as a Green Beret to his vision for victory in Afghanistan to his role in waging America’s war with al-Qa’ida at the highest levels of government. In captivating detail, he depicts his years in the Special Forces—including his training to parachute behind enemy lines with a backpack nuclear weapon in the event of a Soviet invasion of Western Europe, and he reveals how those experiences directly influenced his approach to shaping policy. Vickers has played a significant role in most of the military and intelligence operations of the past four decades, and he offers a deeply informed analysis of the greatest challenges facing America today, and in the decades ahead. More information here.
14 Jun 23, 1200-1300 (ET) - The Making of Global Trends 2030 – Johns Hopkins University - Virtual
Join host Michael Ard for a discussion with strategic foresight and global trend expert Mathew Burrows. Mathew Burrows is the Program Lead of the Stimson Center’s Strategic Foresight Hub and a Distinguished Fellow with the Reimagining US Grand Strategy program. Prior to joining Stimson, he served as the director of Foresight at the Atlantic Council’s Scowcroft Strategy Initiative and as the co-director of the New American Engagement Initiative. Burrows is one of the leading experts on strategic foresight and global trend analysis. In 2013 he retired from a 28-year-long career in the State Department and the Central Intelligence Agency (CIA), the last 10 years of which he spent at the National Intelligence Council (NIC), the premier analytic unit in the US Intelligence Community. In 2007, Burrows was appointed Counselor, the number three position in the NIC, and was the principal drafter for the NIC publication Global Trends 2030: Alternative Worlds, which received widespread recognition and praise in the international media. In 2005, he was asked to set up and direct the NIC’s new Long Range Analysis Unit, which is now known as the Strategic Futures Group. Other positions included assignments as deputy national security advisor to Treasury Secretary Paul O’Neill (2001-02), special assistant to the UN Ambassador Richard Holbrooke (1999-2001), and first holder of the intelligence community fellowship at the Council on Foreign Relations in New York (1998-1999). Burrows received a BA in American and European history from Wesleyan University and a PhD in European history from the University of Cambridge. Free registration here.
Join colleagues from across the intelligence, homeland and national security communities on Tuesday, June 20, from 8:00-10:00 AM at the Hilton McLean Tysons Corner, as we celebrate Charlie Allen's 65th year (and counting!) of extraordinary service to our nation. Following a plated breakfast, INSA Chairwoman Tish Long will lead a moderated Q&A with Charlie, as he reflects on key accomplishments, regrets, current challenges and opportunities, and more! Plus, special guests and fun surprises will mark this festive event. Don't miss this opportunity to celebrate an iconic intelligence professional and national treasure! Free for students and military. Register here.
29 Jun 23, 0900-0945 (ET) - Coffee and Conversation with The Hon. Michael Vickers – INSA - Virtual
Join intelligence and national security colleagues online on Thursday, June 29, from 9:00-9:45 am ET, for a special Coffee & Conversation with The Hon. Michael G. Vickers, former Under Secretary of Defense for Intelligence. In a moderated conversation with Letitia A. Long, Chairwoman, INSA Board of Directors, Mr. Vickers will discuss his latest memoir, By All Means Available: Memoirs of a Life in Intelligence, Special Operations, and Strategy, including: Key accomplishments during his time at CIA, specifically his role in the invasion of Grenada, operational response to the Beirut bombings, and the covert effort to drive the Red Army out of Afghanistan; Leading the comprehensive transformation of defense intelligence capabilities, while USD(I); Serving as the first ASD for Special Operations, Low-Intensity Conflict & Interdependent Capabilities...and much more! Plus, there will be ample time for audience Q&A! Register here.
"The Nation's Premier Intel and National Security Event" - Save the date for the 10th Annual AFCEA/INSA Intelligence and National Security Summit! The powerful, two-day program, at the Gaylord National Resort, will feature five blockbuster plenaries, six engaging breakout sessions, and a jam-packed exhibit hall full of the latest IC technology innovations. Top leaders will discuss State of the Community, Military Intelligence Priorities, Strategic Intelligence, and Cybersecurity Challenges. Breakout sessions with senior leaders, technology experts, and thought leaders will examine some of the most pressing issues facing the community. Plus, powerful networking opportunities designed to foster partnerships and relationship building. Check for for full agenda and updates here.
20-22 Jul 2023 - NASIH Annual Conference 2023 – NASIH - In Person - University of Calgary, Canada
North American Society for Intelligence History's annual event. Registration is open and the registration fee will increase on 15 Jun 23. Full details on this two-day program, with extensive speaker line up and panels, here. Registration here.
Gifts for Friends, Colleagues, Self
 Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Show your support for AFIO with our new Black Short-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $50 each including shipping.
Sizes for (M) men, only; Small, Medium, Large, XL, XXL, and XXXL. $50 per shirt.
You may pay by check or credit card. Complete your order online here or mail an order along with payment to: AFIO, 7600 Leesburg Pike, Ste 470 East, Falls Church, VA 22043-2004. Phone orders at 703-790-0320. Questions? Contact Annette at: annettej@afio.com.

PopSocket for cellphones or tablets
Show your support to AFIO while enjoying the convenience offered by our AFIO Logo PopSocket. The PopSocket is most commonly used as a stand and as a grip for your mobile phone or tablet; handy for taking selfies, watching videos, and for texting. The PopSocket looks like a small button or sticker which, when closed, sticks flat to your mobile device. However, its accordion-like design enables it to pop open for use. The benefits of using a PopSocket make it a must-have accessory for your mobile phone or tablet. It also aids in keeping your phone from slipping off your hand during use, falling, or breaking.
Price: $15. Order this and other store items online here.

Duffel Bags - Royal Blue and Black with Full Color AFIO Logo This duffel has it all when it comes to value, style and organization.
600 denier polyester canvas with polyester double contrast; D-shaped zippered entry for easy access. Front pocket with hook and loop closure. End mesh pocket Easy-access end pockets. Four durable, protective feet and built-in bottom board for added strength. Web handles with padded grip. Detachable, adjustable shoulder strap.
Dimensions: 11"h x 19.75"w x 9.75"d; Approx. 2,118 cubic inches
Price: $50. Order this and other store items online here.
AFIO Mug with color glazed seal.
Made in the U.S.A., dishwasher-safe.
$35 includes shipping.
Sip your morning joe in style or use it to stash pens, cards, paperclips, or candy.
Order this and other store items online here.

Caps - Dark Navy with Navy AFIO Logo
An authentic silhouette with the comfort of an unstructured, adjustable fit. Fabric: 100% cotton. Unstructured. Fabric strap closure with adjustable D-clip. Price: $30. Order this and other store items online here.
PUBLISHED IN 2023
| Be informed on career opportunities in the U.S. Intelligence Community | ||
 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. AFIO's popular 47-page booklet reaches thousands of high school, college students, university guidance offices, and distributed in classes teaching intelligence, to help those considering careers in the U.S. Intelligence Community. |
 |
| This is the all new fifth edition. The publication is also popular with University Career Guidance Centers, professors and academic departments specializing in national security, and parents assisting children or grandchildren in choosing meaningful, public service careers. This booklet is provided online as a public service from the generosity of AFIO board, volunteer editors/writers, donors, and members. We thank all for their support which makes this educational effort possible. |
||
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |
||
 Guide to the Study of Intelligence...and...When Intelligence Made a Difference
Guide to the Study of Intelligence...and...When Intelligence Made a Difference
"AFIO's Guide to the Study of Intelligence" has sold out in hard-copy.
It is available in digital form in its entirety on the
AFIO website here.
Also available on the website here are the individual articles of AFIO's
history project "When Intelligence Made a Difference" that have been
published to date in The Intelligencer journal.
More articles will be appear in future editions.
Some features of the email version of the WIN do not work for readers who have chosen the Plaintext Edition, some users of AOL, and readers who access their email using web mail. You may request to change from Plaintext to HTML format here afio@afio.com. For the best reading experience, the latest web edition can be found here: https://www.afio.com/pages/currentwin.htm
To unsubscribe from the WIN email list, please click the "UNSUBSCRIBE" link at the bottom of the email. If you did not subscribe to the WIN and are not a member, you received this product from a third party in violation of AFIO policy. Please forward to afio@afio.com the entire message that you received and we will remove the sender from our membership and distribution lists.
(c) 1998 thru 2023
AFIO Members Support the AFIO Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for back issues of the WINs, information about AFIO, conference agenda and registrations materials, and membership applications and much more! .
AFIO | 7600 Leesburg Pike, Suite 470 East, Falls Church, VA 22043-2004 | (703) 790-0320 (phone) | (703) 991-1278 (fax) | afio@afio.com