05 - 11 July 2023
(Issue 26)
is sponsored by

Readers who encounter problems with the email version of this newsletter can
view the latest web edition here.
CONTENTS
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
- How the Supreme Court Has Shaped Security Clearances - Clearance Jobs, 09 Jul 23
- Proposed Espionage Act reforms are vital for investigative journalism - Freedom of the Press Foundation, 07 Jul 23
- New Chinese Counterespionage Law Aimed at US Tech Sector - Bank Info Security, 05 Jul 23
- Russia, China ramp up spying on Germany, counter-espionage service warns - Politico, 07 Jul 23
- Pentagon Aims to Stop China and Russia from Spying on Academia - Air and Space Forces, 06 Jul 23
- China has had a spy base in Cuba for decades, former intelligence officer says - Miami Herald, 05 Jul 23
- US special envoy for Iran's security clearance under review - Reuters, 29 Jun 23
- Pentagon looks to improve classified information tracking in wake of secret documents leak - Stripes, 05 Jul 23
- US Spies Are Buying Americans’ Private Data. Congress Has a New Chance to Stop It - Wired, 05 Jul 23
- Tanzania: Time To Have Two Separate Intelligence Services? - The Chanzo, 03 Jul 23
- Counterespionage Corner - A collection of recent material on arrests, convictions, expulsions, and more...
- Cyberespionage Collection - Newly identified actors and operations, countermeasures, policy, other...
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
- From the Vault: “Baseball and Espionage” – with World Series Champion Ryan Zimmeram and Marc Polymeropolous (Part 1 of 2) — Andrew Hammond, PhD. SpyCast
- Ukraine has rightfully been at the forefront of the European Union’s foreign policy and security discussions over the past 18 months, but the larger battle also necessitates curbing threats like North Korea. — Former Acting CIA Dep. Dir. for Ops and Arkin Group President Jack Devine, In Other News
- Far-Right Populism is Back, No Easy West Bank Solutions, High Stakes NATO Summit, Manipur Violence Shakes New Delhi, Russia’s Partners Might Recalibrate After Mutiny — Former FBI Special Agent and Soufan Group CEO Ali Soufan, Intel Brief
- Trouble in Moscow, Swiss Intelligence, Iranian Espionage, Russian Plane Lands in Washington, 4 children stabbed in France: Terrorism?, and more... — WTOP National Security Correspondent JJ Green - Inside the SCIF, Target USA, The Hunt
- FBI’s Comey Commits an Act of Crime Fiction | Evan Gershkovich Could Use a Whole Lotta Love | Biden Gives Israel a Pass on West Bank Violence | Japan’s Spy Buildup Faces Obstacles - Jeff Stein and Colleagues in SpyTalk (Substack)
Section III - MEMBER CONTRIBUTIONS
- Letter to the Editor: Politicization of Intelligence and Forthcoming Book - John Gentry, Georgetown University, 14 Jun 23
- Article: Inside the Secretive Russian Security Force That Targets Americans - Wall Street Journal, 07 Jul 23
- Article: Spinning towards the future: crisis response from space - The Space Review, 03 Jul 23
- Podcast Episode: Sinclair in Focus (67 mins) - Bletchley Park Podcast, 25 June 23
- Free Book: Security Analysis: A Critical Thinking Approach - Michael W. Collier, Eastern Kentucky University, 20 Jun 23
- Article: Brazil launches investigation into illegal activities of Russian deep-cover spies - Intel News, 03 Jul 23
- Article: Satellite images appear to show build-up at Wagner base in Belarus - Reuters, 29 Jun 23
- Interview: Jack Devine on The Tape - Ukraine and Russia, IBM, PacWest, and VCs (10 mins) - Bloomberg, 28 Jun 23
- Article: Russia Building A Vast Industry Of Spying Tools - New York Times, 03 Jul 23
- Article: ‘Urban Explorers’ and Accused Spies Chafe in Legal Limbo in Albania - New York Times, 03 Jul 23
- Article: Russia’s Many Spies in Mexico - Wall Street Journal, 02 Jul 23
- Article: CIA Fears ‘Disastrous Consequences’ As Ukraine Ignores US Warnings Against Sabotage Operations - MSN, 06 Jul 23
- Article: Kim Jong-un Wants a Satellite in Space. Seoul Says He Has a Long Way to Go - New York Times, 05 Jul 23
- OpEd: Our system will unravel if presidents take classified information - Former DDNI Sue Gordon - Washington Post, 27 Jun 23
- Article: Julian Assange and Arnon Milchan: The Lopsided Scales of American Justice - The Nation, 27 Jun 23
- Article: Switzerland overrun with foreign spies, Swiss intelligence service warns - Intel News, 28 Jun 23
- Article: CIA Director Burns: What U.S. intelligence needs to do today and tomorrow - Washington Post, 07 Jul 23
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
- Truth Decay Is Putting U.S. National Security at Risk - RAND, 28 Jun 23
- Reading between the lines of the new North Korea intelligence estimate - The Atlantic Council, 28 Jun 23
- The impact of COVID-19 on police intelligence reports in the United Kingdom - Journal of Policing, Intelligence, and Counterterrorism, 03 Jul 23
- Why Do We Need a New Research Agenda for the Study of Intelligence? - International Journal of Intelligence and Counterintelligence, 06 Jul 23
- Exclusive: The CIA's Blind Spot about the Ukraine War - Newsweek, 05 Jul 23
- Infographic and Report: Economic Coercion: China’s Leverage in Trade - Visual Capitalist, 28 Jun 23
- Intelligence in History - A Collection of Recent Content
- True Intelligence Matters in Film: The Great Escape - John Sturges (1963)
- Walking Tours: The Spies of Embassy Row and Spies of Georgetown - Washington, DC. (Sundays, Dates/Times Vary)
Section V - Books, Research Requests, Academic Opportunities, Jobs, Obituaries
Books — Forthcoming, New Releases, Overlooked
- The Real Special Relationship: The True Story of How MI6 and the CIA Work Together by Michael Smith (Author), Sir John Scarlett (Introduction), Michael Hayden (Foreword)
- American Traitor: General James Wilkinson's Betrayal of the Republic and Escape from Justice by Howard W. Cox
- OSINT Tools: A Practical Guide to Collection, Analysis, and Visualization by Paul Michel
Research Requests and Academic Opportunities
- Call for Information: Arnold M. Silvier aka "Ritchie Boy," US Army during WWII and CIA (1949 to 1978)
- Survey for Members: Skill Sets Needed for Intelligence Analysis Degree Holders to See Success After Graduation
- Call for Information: 430th CIC in Salzburg in 1946
- Call For Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
- Call For Sources: Intelligence Officers Who Lived in Spain in the 1970s
- Call For Papers: Energy Concerns in National Security and Business Intelligence: Identifying Threats and Developing Solutions - International Journal of Intelligence and Counterintelligence
- Call For Papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
- Call For Articles: AFIO Journal, The Intelligencer
- Retired Federal Government Employees Wanted - National Security Agency, Fort Meade, MD
- Assistant Professor - Intelligence Studies (Global Security and Intelligence Studies), Embry-Riddle Aeronautical University - Prescott, Arizona
- Teaching Associate - Intelligence and National Security Studies, Coastal Carolina University, Conway, South Carolina
- Dennis Sysko, Career NSA Lawyer
- David Bitzer, Career NSA Officer
- Jack Hennessey, Decorated Military Intelligence and CIA Officer
- POSTPONED - 27 Jul 23 (Thursday), 1130 (Pacific) - In Person, San Francisco - Col. Robert W. Parr, USAF (ret), on "12 Days with a Soviet Pilot Defector" - AFIO Andre LeGallo Chapter
Events from Advertisers, Corporate Sponsors, Others
- 13-14 Jul 23 2023 Intelligence and Security Summit – AFCEA/INSA - In Person - National Harbor, MD
- 20 Jul 23, 1830 (ET) Chameleon with former Navy SEAL Remi Adeleke – International Spy Museum - Virtual
- 20-22 Jul 2023 NASIH Annual Conference 2023 – NASIH - In Person - University of Calgary, Canada
- 03 Aug 23, 1730-2130 (ET) Leadership Dinner with DDNI Stacey Dixon – INSA - In Person - Tysons Corner, VA
See the AFIO Calendar of Events for scheduling further in the future.
ACKNOWLEDGEMENTS
The WIN editors thank the following contributors of content for this issue:
LR, PO, DB, KB, JDe, JDa, JH, JG, S, GD
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
The WIN editors thank the following contributors of content for this issue:
LR, PO, DB, KB, JDe, JDa, JH, JG, S, GD
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
DISCLAIMER
Our editors include a wide range of articles and commentary in the Weekly Intelligence Notes to
inform and educate our readers. The views expressed in the articles are purely those of the authors and do not reflect support or endorsement from AFIO. WIN notices about non-AFIO events do not constitute endorsement or recommendation by AFIO.
AFIO does not vet or endorse research inquiries, career announcements, or job offers. We publish reasonable-sounding inquiries and career offerings as a service to our members. We encourage readers to exercise caution and good judgment when responding and to independently verify the source before supplying resumes, career data, or personal information.
TECHNICAL DIFFICULTIES
Readers who encounter problems with links or viewing this newsletter as an email can access
the latest web edition here.
the latest web edition here.
FROM THE AFIO STORE
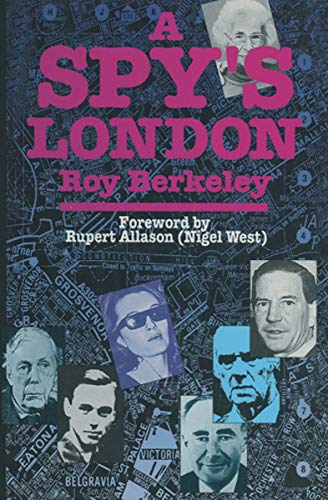 Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
In 'this remarkable book' (as intelligence historian and AFIO member Nigel West describes in his Foreword), the reader will be struck by the vibrancy of history made real. Author/AFIO member Roy Berkeley goes behind the facades of ordinary buildings, in the city that West calls 'the espionage capital of the World,' to remind us that the history of intelligence has often been made in such mundane places. With his evocative photographs and compelling observations, The 136 sites are organized into 21 manageable walks. But also a joy to armchair travelers. Among the sites: the modest hotel suite where an eager Red Army colonel poured out his secrets to a team of British and American intelligence officers; the royal residence where one of the most slippery Soviet moles was at home for years; the London home where an MP plotting to appease Hitler was arrested on his front steps in 1940.
A few copies are available at only $20 a copy (postage to a U.S.-based address included). Telephone the office at 703-790-0320 or email julie@afio.com to obtain one of these last copies.
 Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Superior quality and shrink resistant; features a detailed embroidered AFIO seal. The shirt color is royal blue.
The sale price is $25 and includes shipping.
Available in men's sizes only: small, medium, large, extra-large, XXL, and XXXL.
Due to limited quantities, please contact the AFIO National Office for availability of size and to provide payment information.
You may telephone the office at 703-790-0320 or email annettej@afio.com
LATEST FROM AFIO
Released exclusively to members 11 July 2023...and to the public on 16 July 2023
Update on the Fast-Breaking Events in Russia and Ukraine
Interview of Friday, 7 July 2023 between Shane Harris, Intelligence and National Security Reporter for The Washington Post, and AFIO President James Hughes, a former senior CIA Operations Officer.
They discuss the confusing and dangerously fluctuating situation in Ukraine. From Yevgheny Prigozhin's Wagner Group's role and possible coup attempt, to a missing Russian general, and the uncertain new role of Belarus and its leader, Lukashenko. And Putin's renewed threats to use tactical nuclear weapons if its positions in Ukraine deteriorate.
The interview runs 25 minutes and includes many Q&As.
Shane Harris books and podcasts can be found here.
His recent reporting at The Washington Post is here
Access the HARRIS interview here or click above image
This, and upcoming AFIO Now videos in 2023, are sponsored by Northwest Financial Advisors.
Preview of Summer-Fall 2023 Intelligencer:
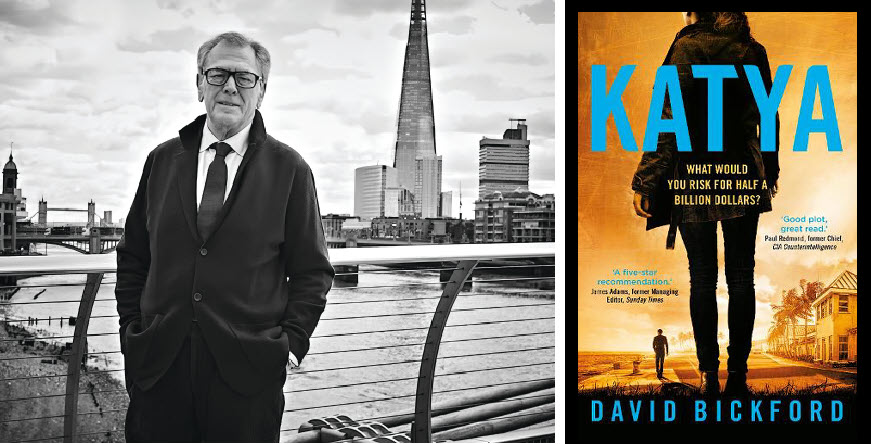
Review of former Under Secretary of State and MI5 & MI6's Legal Director David Bickford's remarkable new novel: "Katya: What Would You Risk for Half a Billion Dollars?" - reviewed by AFIO Chairman Stewart Baker
WORK AT AFIO
A few of the responsibilities include: • Serve as focal point for a major AFIO project, to include maintaining project database and supporting a large annual formal dinner • Provide back-up support to AFIO Directors of Membership and Operations • Support AFIO's existing partners and stakeholders ... Robust Microsoft Office Skills (Excel, Outlook, Word) required.
Full job description here.
HOLD THE DATE FOR IMPORTANT EVENT THIS OCTOBER
AFIO National's Fall Luncheon
features fireside chat with Avril Haines, Director of National Intelligence,
and Jennifer K. Ewbank, the Deputy Director of CIA for Digital Innovation
Friday, 13 October 2023, 10:30am - 2pm - In-Person Tysons VA
Registration opens here on 4 September and closes when all spaces taken (or NLT 9 October).
Check-in and badge pickup for Registered Attendees begins at 10:30 a.m.
NO registrations or walk-ins at hotel. No payment accepted for this event by mail or at the venue.

Fireside chat with Avril Haines, Director of National Intelligence, begins at 11:00 a.m.
Lunch served noon to 1:00 p.m.

Jennifer Ewbank, Deputy Director of CIA for Digital Innovation speaks at 1:00 p.m.
Q&A follows each presentation. Event ends at 2:00 p.m.
Luncheon prices are $60 for Members; $75 for nonmember guests and all Subscribers. Payment by credit card required at time of registration. No mailed checks or at the door or at venue payments accepted or permitted.
Registration opens here on 4 September, and closes 5 pm Monday 9 October.
Though we do not provide special overnight room rates, if you wish to make room reservations at the hotel, do so here.
Cancellation Schedule: AFIO must commit to the hotel facilities and regrets it must charge a cancellation fee. 100% refund until close of registration. No refunds or cancellations thereafter. You will receive a donation receipt for fees forfeited. A donor statement will be sent showing that you made a "gift to AFIO" in such instances. Gifts to AFIO are tax-deductible.
All attendees must be members of AFIO or accompanied by a current member.
Learn more about becoming a member at www.afio.com. Questions regarding membership? Contact office at 703-790-0320 or email afio@afio.com
Questions regarding this event to events@afio.com

"AFIO Now" Video Interviews and Podcasts in 2023 are sponsored by
Northwest Financial Advisors
Click here to watch interviews in the AFIO Now series released in 2023.
View interviews from 2020 to 2022 here.
Watch public-release interviews on our YouTube channel or listen to them in podcast form at the links below.
Log into the member-only area for member-only features.
The Real Life Impacts of Russian Oligarchs Being Welcomed into London and Then Becoming Problems as Putin Struck Out at Perceived Betrayers
Latest podcast: James Bamford, award-winning journalist/author, discussing his latest book, Spyfail: Foreign Spies, Moles, Saboteurs, and the Collapse of America's Counterintelligence
Video and Podcast released to public 3 July 2023.
Jim Bamford and John Quattrocki discuss SPYFAIL which describes the highly dangerous and growing capability of foreign countries to conduct large-scale espionage within the U.S. and how the FBI and other agencies have failed to prevent it. These covert operations involve a variety of foreign countries—North Korea, Russia, Israel, China, and others—and include cyberattacks, espionage, psychological warfare, the infiltration of presidential campaigns, the smuggling of nuclear weapons components, and other incredibly nefarious actions.
The interview runs 60 minutes and includes several Q&As.
Are you too busy to watch an entire AFIO Now episode on YouTube? Would you rather listen in your car or while accomplishing other tasks? You can download or stream episodes on any of the 8 podcasting platforms that host AFIO Now. Search for 'AFIO Podcast' for a selection of the interviews above (public released ones) on:
Podbean; iTunes; Google; Spotify; Amazon Music; Amazon TuneIn + Alexa; iHeartRadio; Pandora
FOR YOUR FALL TRAVEL PLANS
10-12 November 2023 - Sante Fe, NM - Spies, Lies & Nukes Conference
Spies, Lies & Nukes - Third Conference - Santa Fe, NM
Plan Your Fall Attendance NOW to capture the lower rates
Special Rate Available for AFIO Members Here
 This third, enhanced running of Spies, Lies & Nukes. Join Valerie Plame and some of her legendary, highly decorated, and experienced CIA colleagues as they pull back the curtain on the real life "wilderness of mirrors" that is international espionage.
This third, enhanced running of Spies, Lies & Nukes. Join Valerie Plame and some of her legendary, highly decorated, and experienced CIA colleagues as they pull back the curtain on the real life "wilderness of mirrors" that is international espionage.
Hear from and engage with the best of CIA's spies to better understand today's world: from emergent threats, to never-before-told spy operations, black market nuclear scams, how to recruit a spy, the growth of domestic terrorism, how social media is used in espionage, and keeping your employees and your company safe from foreign spies.
Topics: "Soul Catcher: The Metaphysics of Recruiting a Spy" with Jim Lawler, Former Senior CIA Ops Officer
"Delusion and Illusion in Moscow" with Jonna Mendez in conversation with Valerie Plame, Former Covert CIA Ops Officer
"CIA in the Movies" - Panel;
"China: An Emerging Threat" with Mary Beth Long, Former Assistant Secretary of Defense for International Security Affairs
"Inside Putin's Head" with Rolf Mowatt-Larssen, Former Senior CIA Intelligence Officer
"Clarity in Crisis: Leadership Lessons from the CIA" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"Disinformation Distortions: AI, Deep Fakes, and Everything You Always Wanted to Know About Social Media and Espionage" with Alma Katsu, Former Senior CIA and NSA Analyst
"Morality and Ethics in the CIA" with Doug London, Former Senior Officer in the CIA's Clandestine Service
Michael Morrell in conversation with Valerie Plame, Former Covert CIA Ops Officer
"Eliminating Players on the Intelligence Battlefield: Havana Syndrome" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"The End of the Global Nuclear Order" with Valerie Plame, Former Covert CIA Ops Officer
Program also includes: Former Senior CIA Intelligence Officer; Michael J. Morell, Former CIA Deputy Director


FEE: Regular Sale purchase window: Jun 16 - Nov 2, $1300; Late Sale purchase window: Nov 3 - Nov 10, $1450. Special AFIO rate here.
Ticket price does not include accommodations. More about accommodations here
Tickets include breakfasts, lunches, VIP reception and all speaker presentations and activities.
Conference location: Conference Location: La Fonda On the Plaza, 100 E. San Francisco Street, Santa Fe, NM 87501
More information or to register here
Access CIA's Inhouse Gift Shop
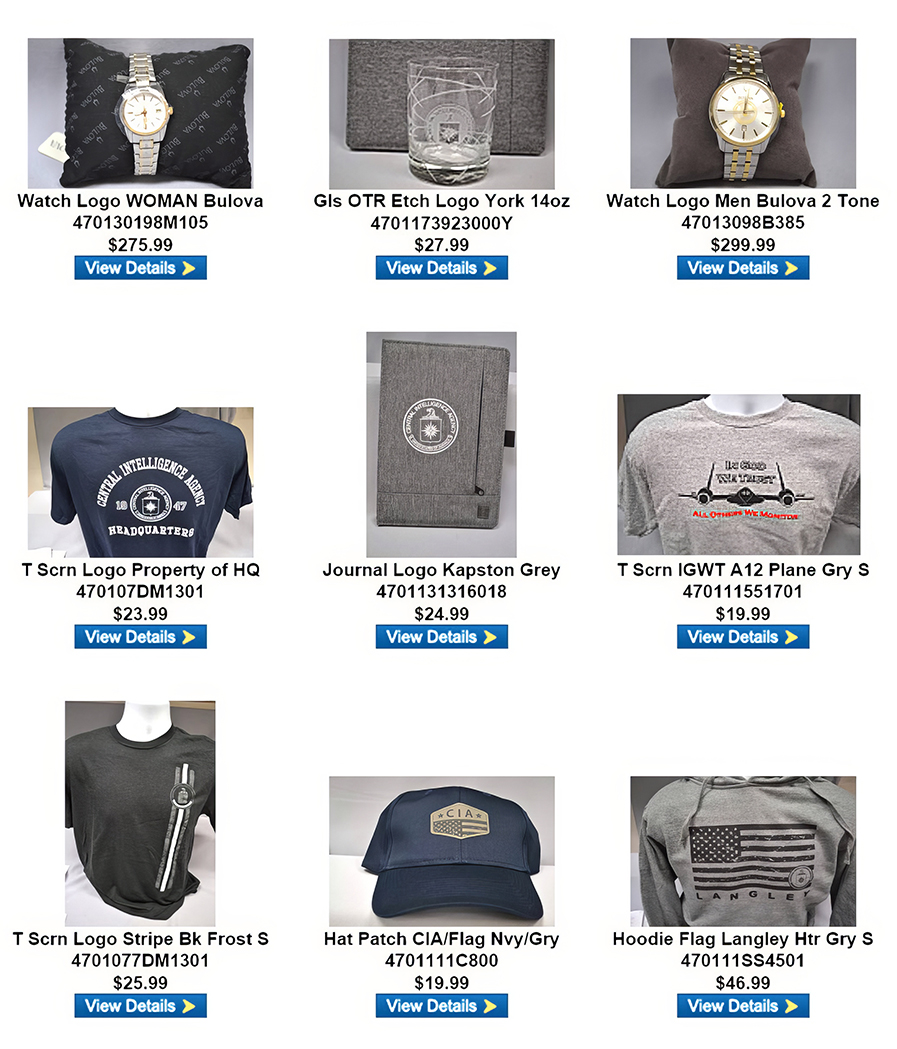
One special benefit of AFIO membership is access to CIA's EAA Store.
After completing the required, quick pre-approval process for all AFIO members, described here, you can purchase directly from the EAA online store their unusual logo'd gift items for self or colleagues. EAA on 12 May 2023 released the photo above, which features some of their newest CIA items and other gift suggestions.
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
How the Supreme Court Has Shaped Security Clearances - Clearance Jobs, 09 Jul 23
The Supreme Court took top-billing in last week’s news cycle, capping an otherwise unremarkable court term with a triple-whammy of major decisions on affirmative action, student loan debt, and the First Amendment. Apart from these infrequent (albeit significant) blips on the proverbial radar, the Supreme Court is perhaps the least-visible of our three branches of government. This is certainly the case when it comes to security clearance issues. But visibility and power are not always synonymous. Here are four times from 1959 to 2023 where the Supreme Court has played a significant role in shaping the security clearance as we know it. (View report here.)
Proposed Espionage Act reforms are vital for investigative journalism - Freedom of the Press Foundation, 07 Jul 23
I may have just violated the Espionage Act by linking to this Washington Post report on leaked documents about the Russian-Ukrainian war. You may have just violated the act by reading it. That sounds ridiculous because it is. But the act says anyone who accesses national defense information must return it to the appropriate government official to avoid prison. I didn’t, did you? It’s true, the government hasn’t invoked the 100-plus year-old law to prosecute news readers and probably won’t anytime soon. But the government has routinely abused its broad discretion under the law’s vague and ambiguous language to prosecute investigative journalism — including both publishers and sources. (Full article here.)
New Chinese Counterespionage Law Aimed at US Tech Sector - Bank Info Security, 05 Jul 23
China on July 1 set into motion a revamped Counter-Espionage Law that seeks to protect national security agencies and documents, data, and materials related to national security from foreign adversaries. The measure gives Chinese authorities sweeping powers to investigate and even seize property of companies doing business in China. China's National People's Congress first passed the Counter-Espionage Law in November 2014, signaling the Chinese Communist Party's intent to safeguard state secrets the party designated as critical to national security, giving security agencies the power to take proactive action against suspected espionage activities. The revised law, passed by the National People's Congress Standing Committee on April 26, went into effect on Saturday and covers all forms of cyberattacks that target government bodies and China's information infrastructure. (Full article here.)
Russia, China ramp up spying on Germany, counter-espionage service warns - Politico, 07 Jul 23
Germany’s military spy agency is warning that Russia and China are boosting their espionage activities in the country. In a new report published Friday, Germany’s Military Counterintelligence Service said that it is of “prominent value” for Russia, hence why a “high number of Russian intelligence operatives” are deployed there. Since Germany started actively backing Ukraine with ammunition and weapons to fend off Russia’s full-scale aggression, it is “being reconnoitered even more intensively by Russian services,” according to the report. Russia’s ability to spy on Germany has been weakened, however, since Berlin expelled 40 Russian diplomats over the last year. Russia is expected to “try to compensate by other methods of obtaining information,” as Moscow seeks to have an advantage over NATO countries. (Full article here.)
Pentagon Aims to Stop China and Russia from Spying on Academia - Air and Space Forces, 06 Jul 23
The Pentagon is moving to block Chinese and Russian organizations from obtaining U.S. technology secrets through academia, according to a Department of Defense memo made public on June 30. The memo, signed by Heidi Shyu, undersecretary of defense for research and engineering, lists more than 80 Chinese and Russian academic, scientific, engineering, or cultural institutions that have engaged in “problematic activity” geared at improperly gaining access to classified U.S. research or influencing teaching staff or students. The memo is a response to the 2019 National Defense Authorization Act, which sought a Pentagon response to foreign intelligence exploitation of U.S. academic institutions. The memo requires a review of new research contracts and prohibits Pentagon money going to projects that involve one of the blacklisted entities, based on their previous track record in harvesting U.S. technology secrets, or simply having suspect relationships with Chinese and Russian intelligence organizations. (Full article here.)
China has had a spy base in Cuba for decades, former intelligence officer says - Miami Herald, 05 Jul 23
China’s espionage efforts in Cuba targeting the United States are not recent and date back at least three decades, a retired army counterintelligence agent has told the Miami Herald. It took U.S. intelligence agencies nine years to figure out who was behind the repair and enhancements spotted during the 1990s at a “signals intelligence facility” — a reference to the interception of electronic communications — in the town of Bejucal, a 45-minute drive from Havana. “We saw the enhancements over a decade, a steady evolution; clearly something was going on, but we didn’t know what,” said Chris Simmons, a former chief of a counterintelligence research branch on the Western Hemisphere at the U.S. Defense Intelligence Agency, which had Cuba as its number one target. “And then, in 2001, we discovered that the Chinese had been there already for nine years. We were told at that time that when the Chinese arrived in 1992, they were embedded in a single building within Bejucal, and they were 50 officers in this facility.”(Full article here.)
US special envoy for Iran's security clearance under review - Reuters, 29 Jun 23
U.S. Special Envoy for Iran Robert Malley said on Thursday his security clearance is under review, saying that he expects the investigation to end "favorably and soon" and in the meantime he was on leave. "I have been informed that my security clearance is under review. I have not been provided any further information, but I expect the investigation to be resolved favorably and soon," Malley told Reuters, confirming an earlier Axios report. "In the meantime, I am on leave," he added. Earlier, State Department spokesman Matt Miller said Malley was on leave but did not say why or for how long, saying Abram Paley was filling in on an acting basis. (Full article here.)
Pentagon looks to improve classified information tracking in wake of secret documents leak - Stripes, 05 Jul 23
The Defense Department does not intend to scale back the number of its military and civilian employees with classified information access, but it plans to better track who is accessing what secrets, a Pentagon official said Wednesday. A 45-day review of policies and procedures ordered in April by Defense Secretary Lloyd Austin found most department officials with clearance are trustworthy, but policies meant to protect national secrets were interpreted differently across the vast, worldwide military organization. Austin ordered the review in the wake of hundreds of classified documents being leaked to a private group of social media users. Airman 1st Class Jack Teixeira, a 21-year-old with the Massachusetts Air National Guard, is accused of leaking the military documents in a chatroom on Discord. (Full article here.)
US Spies Are Buying Americans’ Private Data. Congress Has a New Chance to Stop It - Wired, 05 Jul 23
A “must-pass” defense bill wending its way through the United States House of Representatives may be amended to abolish the government practice of buying information on Americans that the country’s highest court has said police need a warrant to seize. Though it’s far too early to assess the odds of the legislation surviving the coming months of debate, it’s currently one of the relatively few amendments to garner support from both Republican and Democratic members. Introduction of the amendment follows a report declassified by the Office of the Director of National Intelligence—the nation’s top spy—which last month revealed that intelligence and law enforcement agencies have been buying up data on Americans that the government’s own experts described as “the same type” of information the US Supreme Court in 2018 sought to shield against warrantless searches and seizures. A handful of House lawmakers, Republicans and Democrats alike, have declared support for the amendment submitted late last week by representatives Warren Davidson, a Republican from Ohio, and Sara Jacobs, a California Democrat. The bipartisan duo is seeking stronger warrant requirements for the surveillant data constantly accumulated by people’s cellphones. They argue that it shouldn’t matter whether a company is willing to accept payment from the government in lieu of a judge’s permission. (Full article here.)
Tanzania: Time To Have Two Separate Intelligence Services? - The Chanzo, 03 Jul 23
The debate over the recent Tanzania Intelligence and Security Service (TISS) amendment bill has opened up the agency to scrutiny and discussion in a way we have not seen in a while. Due to the service’s secretive nature, discussions usually centre around myths and hearsay. However, with the TISS amendment bill, gazetted on May 15, 2023, the public got an insight into the service’s inner workings for the first time in a long time. After having gone through the amendment, which has recently passed through the parliament, I would like to delve into some of the changes that have been proposed to suggest the service’s improvement. However, I would like to caution the readers that I am neither a security nor intelligence expert; hence, any suggestions are from an observer’s perspective and might not be feasible regarding implementation! (Full article here.)
Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
- Poland detains another man suspected of spying for Russia Free Polskie Radio, 10 Jul 23
- The Hunt for Spies in the U.S. - Cipher Brief, 09 Jul 23
- DRDO Scientist Espionage Case: ATS Chargesheet Says Kurulkar Was Attracted To Pakistani Spy, Shared Classified Missile Info - Free Press Journal, 08 Jul 23
- Russian Embassy Says Demands Warsaw Provide Information About Citizen Accused Of Espionage - Urdu Point, 06 Jul 23
- Turkey says it busted Mossad ring of 56 operatives gathering intelligence; 7 arrested - Times of Israel, 03 Jul 23
- 20 Years of Cybersecurity – A Look at the 2003 and 2023 National Cybersecurity Strategies - Meritalk, 05 Jul 23
- White House Trying to Block Hollywood Producer’s Takeover of Israeli Cyber Intelligence Company - Jewish Press, 30 Jun 23
- CISA adds new faces to its top leadership team’s cybersecurity division - Federal News Network, 06 Jul 23
- Safeguarding National Security: Leveraging the Department of Homeland Security’s Cybersecurity Mission - Clearance Jobs, 30 Jun 23
- China, cyber intrusion, cyber security - Homeland Security Newswire, 05 Jul 23
- Chinese Cyber Espionage: Unmasking the HTML Smuggling Technique - The Final Hop, 01 Jul 23
- Urgent warning for Gmail and Outlook users to check inbox for ‘Charming Kitten cyber espionage’ – data is at risk - The Sun, 04 Jul 23
- Spy agency urges deletion of auth app, citing North Korean hackers - The Readable, 28 Jun 23
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
The Latest from International Spy Museum Historian Andrew Hammond, PhD.
 Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
04 Jul | From the Vault: “Baseball and Espionage” – with World Series Champion Ryan Zimmeram and Marc Polymeropolous (Part 1 of 2) Ryan Zimmerman and Marc Polymeropoulos join Andrew to discuss intelligence and America’s pastime. From the SpyCast Field of Dreams.
Past episodes:
27 Jun | "Venice's Secret Service" - with Loanna Lordanou
20 Jun | “The North Korean Defector” – with former DPRK Agent Kim Hyn Woo
13 Jun | “Spies: The Epic Intelligence War Between East vs. West” – with Calder Walton
The Latest Insights from Former CIA Acting Deputy Director for Operations Jack Devine.
 In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
06 Jul | Ukraine has rightfully been at the forefront of the European Union’s foreign policy and security discussions over the past 18 months, but the larger battle also necessitates curbing threats like North Korea. For over a decade, under the leadership of Kim Jong-un, North Korea has repeatedly tested nuclear weapons, ballistic delivery systems, and satellite launches. And the continued development of these capabilities presents an unlikely, but direct, threat to South Korea, Japan and the ~30,000 U.S. military personnel on the peninsula. Until now, however, Europe has primarily viewed North Korea’s potential nuclear program of distant, secondary concern. But if the European Union (EU) wants to support the security of its global, democratic allies at a moment of geopolitical realignment, it should take North Korea’s nuclear capabilities more seriously. (Full version available to AFIO members in the coming days here.)
29 Jun | Putin would never have been this vulnerable if he’d just stayed out of Ukraine
16 Jun | Putin is prioritizing control over efficiency, and it’s not going to serve him well in the long run.
Daily Analysis of Security Issues and Geopolitical Trends
 Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
11 Jul | Far-Right Populism is Back on the Menu
The far-right populist Alternative for Germany (AfD) party won two local elections in breakthrough victories in recent weeks, marking the first time the party has captured either a prominent regional or mayoral post. Although both posts may not hold significant national political weight – one being a district administrator seat comparable to the mayorship of a mid-sized town, the other a mayoral post in a small town – the victories have resonated throughout the country and are indicative of the party’s resurgent strength in Germany. They are also important symbolically. While AfD currently holds 78 seats in the Bundestag, it had not previously claimed either the majority of a district’s electoral support or bureaucratic authority over an area. Both of these recent wins reflect broader national trends: several recent polls project that if elections were held in Germany today, AfD would claim 20 percent of the vote, equal to that of German Chancellor Olaf Scholz’s center-left Social Democratic Party. This level of support marks a distinct shift for the AfD, reflecting the broadening of its voter base beyond its political center of gravity. Further, AfD’s strengthening popularity not only seemingly counters pre-mature prognostications that far-right populists in the West may be on the back foot, but also reflects the increasing resonance of its messaging to the electorate. (Full brief here.)
10 Jul | No Easy Solutions in the West Bank
07 Jun | High Stakes for Upcoming NATO Summit
06 Jun | Resurgent Violence in Manipur Makes Waves in New Delhi
05 Jun | Mutiny Might Prompt Russia’s Partners to Recalibrate
Analysis of Global Security Events with WTOP National Security Correspondent JJ Green
 Inside the SCIF - 29 June - Trouble in Moscow, Swiss Intelligence, Iranian Espionage, and more...
Inside the SCIF - 29 June - Trouble in Moscow, Swiss Intelligence, Iranian Espionage, and more...
 Target USA Podcast - 29 Jun - Russian government plane lands in Washington after weekend rebellion
Target USA Podcast - 29 Jun - Russian government plane lands in Washington after weekend rebellion
The Hunt Broadcast - 14 Jun - 4 children were stabbed in France. Was it terrorism?
The Latest Insights from Jeff Stein and Colleagues in SpyTalk (Substack)
10 Jul | FBI’s Comey Commits an Act of Crime Fiction - Henry Allen
James Comey, former director of the Federal Bureau of Investigation, has written a novel. No surprise. Big-time political players write novels all the time — Jimmy Carter, Newt Gingrich, Bill Clinton, Hillary Clinton, Winston Churchill, Benjamin Disraeli. Insiders! Lawyer/novelist Michael Connelly blurbs Comey’s novel by saying he “knows this world like the back of his hand.” Writing a novel isn’t that hard, as long as the author isn’t trying to make it literature. There is no sign Comey is trying to make this novel literature. It’s called Central Park West, as if we’re in for a big social novel giving the lowdown on the higher-ups. We aren’t. This is a crime procedural with three murders and a lot of courtroom action sprinkled with nifty details and the trick of doing narrative exposition through testimony. (Full article here.)
09 Jul | Evan Gershkovich Could Use a Whole Lotta Love - Jeff Stein
Evan Gershkovich passed his hundredth day in a Moscow prison on July 7th. Falsely accused of being a U.S. spy, the 31-year-old Wall Street Journal reporter may well have been arrested by Russian authorities to set up in a prisoner swap. WNBA star Brittney Griner, imprisoned on a minor drug charge for 10 months in 2022, was swapped last year for notorious Russian arms dealer Viktor Bout, who was serving a 25-year sentence in a U.S. federal prison. Then again, Russia has refused to release Paul Whelan, a former U.S. Marine and corporate security director convicted on espionage charges in 2018. He is serving a 16-year sentence. Last month Russian police also arrested Moscow-based record producer Michael Travis Leake on a drug trafficking charge. He, Whelan and Gershkovich have all said they are innocent of the charges. (Full article here.)
29 Jun | Biden Gives Israel a Pass on West Bank Violence - Jonathan Broder
In the last episode of Fauda, the Israeli counterterrorism thriller on Netflix, things go terribly wrong for the show’s main characters, all members of an undercover intelligence unit fighting Palestinian militants in the West Bank and Gaza Strip. As the Israelis stealthily close in on a West Bank house where a wanted Palestinian resistance leader is holed up, they come under withering automatic weapons fire from Palestinian militants in surrounding buildings. An Israeli armored car moves in to protect them, but the militants detonate a powerful IED that blows the vehicle to fiery pieces. With most of the unit’s members now either wounded or running out of ammo, the Palestinians inch forward, moving in for the kill. . . (Full article here.)
28 Jun | Japan’s Spy Buildup Faces Obstacles - Matt Brazil
Japan’s efforts to re-arm in response to escalating threats from China and North Korea are well-known. Less understood are controversial efforts by some in Japan’s ruling Liberal Democratic Party (LDP) to reestablish world class intelligence and counterespionage capabilities. Not everyone is on board. “There has been a group interested in getting intelligence right for decades,” says MIT’s Richard Samuels, author of Special Duty: A History of the Japanese Intelligence Community. “They’ve tried a lot of engineering and reengineering but have encountered much institutional inertia.” (Full article here.)
To support SpyTalk, subscribe here.
Section III - MEMBER CONTRIBUTIONS
Letter to the Editor: Politicization of Intelligence and Forthcoming Book - John Gentry, Georgetown University, 14 Jun 23
I write to call your attention to my new book, titled Neutering the CIA: Why US Intelligence versus Trump has Long-Term Consequences, which is being published by Armin Lear Press and will be released on July 26. It recently has gone on pre-order by online booksellers (an Amazon link is below). The book is available in hardcover, paperback, and e-versions. Neutering the CIA: Why US Intelligence Versus Trump Has Long-Term Consequences - Kindle edition by Gentry, John, A. Politics & Social Sciences Kindle eBooks @ Amazon.com.
A little background on this project for you: I am a former CIA analyst who experienced politicization of intelligence in the 1980s and has been sensitive to it ever since. Now an academic, I teach intelligence courses and write on intelligence topics -- two previous books and over 30 articles to date, including a few on the topic of politicization. Soon after the recent round of politicization emerged in 2016, I determined to write a book and quickly identified three research questions that guide the final version: (1) What happened, at what agencies? (2) Why and how did politicization develop? (3) What are the implications for national decision making, the IC agencies, and the country as a whole? In short, I identify six causes, prominently including efforts by Obama administration officials. The bulk of the activity occurred at CIA and the ODNI. Contrary to the claims of Trump's intelligence critics, the consequences of current and former intelligence officers' attitudes and actions are major, negative, and likely to be very long-lasting.
It took some time for me to find a publisher. University presses did not like that I identify Obama's diversity policies as one of the causes of politicization. Conservative publishers did not like that I do not defend Trump. Thus, I am pleased that Armin Lear Press has let me publish a book that is as true to traditional academic standards as I can make it (although it did change my title to be more eye-catching), The book is heavily footnoted. I think it will inform even people knowledgeable about intelligence issues.
I hope you and many AFIO members find the book interesting and perhaps useful. I expect it will be controversial. While the book went to press before Michael Morell admitted the political purposes of the "Laptop 51" letter of October 2020 regarding Hunter Biden's computer that he helped organize, there is plenty on Morell in the book and his admissions help increase the credibility of my book.
Regards,
John Gentry
About the Author: John A. Gentry is an adjunct professor with Georgetown University’s Edmund A. Walsh School of Foreign Service and also teaches for the Department of Defense and Strategic Studies, Missouri State University. He was for 12 years an intelligence analyst at the Central Intelligence Agency, where he worked mainly economic issues associated with the Soviet Union and Warsaw Pact countries; for two of those years, he was senior analyst on the staff of the National Intelligence Officer for Warning. He is a retired U.S. Army Reserve officer, with most assignments in special operations and intelligence arenas. He was mobilized in 1996 and spent much of 1996 as a civil affairs officer in Bosnia. Dr. Gentry formerly taught at Columbia University, the College of International Security Affairs of National Defense University, and National Intelligence University. His research interests primarily are in intelligence and security studies. He has written or co-authored four books, edited or co-edited two other books, and written or co-authored about 40 articles and book chapters, mainly on intelligence subjects. He is a member of the Editorial Committee of the International Journal of Intelligence and CounterIntelligence. He received his Ph.D. in political science from The George Washington University.
(Pre-order book here.)
Article: Inside the Secretive Russian Security Force That Targets Americans - Wall Street Journal, 07 Jul 23
For years, a small group of American officials watched with mounting concern as a clandestine unit of Russia’s Federal Security Service covertly tracked high-profile Americans in the country, broke into their rooms to plant recording devices, recruited informants from the U.S. Embassy’s clerical staff and sent young women to coax Marines posted to Moscow to spill secrets. On March 29, that unit, the Department for Counterintelligence Operations, or DKRO, led the arrest of Wall Street Journal reporter Evan Gershkovich, according to U.S. and other Western diplomats, intelligence officers and former Russian operatives. DKRO, which is virtually unknown outside a small circle of Russia specialists and intelligence officers, also helped detain two other Americans in Russia, former Marines Paul Whelan and Trevor Reed, these people said. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: Spinning towards the future: crisis response from space - The Space Review, 03 Jul 23
In the early morning of June 5, 1967, hundreds of Israeli aircraft took off from their bases and headed out over the Mediterranean and the Red Sea before turning toward Egypt. They attacked multiple Egyptian airbases, and soon more than 300 Egyptian aircraft were smoking wrecks with their airfields torn to shreds. Shortly thereafter, the Six-Day War was over. In August 1968, Soviet tanks rolled across the border into Czechoslovakia, suppressing a movement that threatened Soviet control over the country. The Americans learned a lot about how Soviet forces operated, but had no clear warning that the attack was about to take place, and thus no ability to take diplomatic action to try and stop it. In both cases, American intelligence agencies were caught flatfooted. American reconnaissance satellites only returned images of the events on the ground long after they were over. These two incidents prompted American intelligence officials to consider development of a new “crisis reconnaissance” capability in the late 1960s. A leading candidate was a satellite proposal named SPIN SCAN, which would have used a mature, but limited technology to return images to the ground. (Read full report here.)
Podcast Episode: Sinclair in Focus (67 mins) - Bletchley Park Podcast, 25 June 23
Who chose Bletchley Park – a vacant estate in Buckinghamshire – as the wartime home of the Codebreakers? That decision was made by the man in charge of the Secret Intelligence Service, known as ‘C’ – Admiral Sir Hugh Sinclair. A very public man with a very secretive profession, Sinclair was widely-known and well-respected. He passed away just a couple of months after World War Two began in 1939, but his influence was far-reaching. Bletchley Park Trust is proud to be displaying, for the first time, a collection of medals awarded to Sinclair throughout his life. This recent generous donation, from members of his family, forms this year’s ‘Object in Focus’ exhibition. The display is an opportunity to reveal a lesser-known character in Bletchley Park’s story, and a chance to honour this important and charismatic individual. (Listen here.)
Free Book: Security Analysis: A Critical Thinking Approach - Michael W. Collier, Eastern Kentucky University, 20 Jun 23
Security Analysis: A Critical-Thinking Approach is for anyone desiring to learn techniques for generating the best answers to complex questions and best solutions to complex problems. It furnishes current and future analysts in national security, homeland security, law enforcement, and corporate security an alternative, comprehensive process for conducting both intelligence analysis and policy analysis. The target audience is upper-division undergraduate students and new graduate students, along with entry-level practitioner trainees. The book centers on a Security Analysis Critical-Thinking Framework that synthesizes critical-thinking and existing analytic techniques. Ample examples are provided to assist readers in comprehending the material. Newly created material includes techniques for analyzing beliefs and political cultures. The book also functions as an introduction to Foreign Policy and Security Studies. The book is published online for free downloads by the Eastern Kentucky University Libraries. The author is Michael W. Collier a retired former U.S. Coast Guard intelligence officer and college professor who taught intelligence studies and security policy analysis courses. (Access free book here.)
Article: Brazil launches investigation into illegal activities of Russian deep-cover spies - Intel News, 03 Jul 23
AUTHORITIES IN BRAZIL HAVE launched a nationwide probe into the abuse of the country’s citizenship documentation system by Russian spies, who are allegedly using it to build forged identities. According to The Wall Street Journal, Brazil was placed “in an uncomfortable international profile” in the past year, after at least three alleged Russian deep-cover spies were outed by intelligence services in the Netherlands, Norway and Greece. In June of 2022, authorities in the Netherlands expelled Sergey Cherkasov after he attempted to enter the country using a Brazilian-issued passport under the name of Victor Muller Ferreira. As intelNews explained at the time, Dutch and American counterintelligence outed Cherkasov as an intelligence officer of the Main Directorate of the Russian Armed Forces’ General Staff, which is commonly known as GRU. (Read full report here.)
Article: Satellite images appear to show build-up at Wagner base in Belarus - Reuters, 29 Jun 23
June 29 (Reuters) - Satellite images of a military base southeast of the Belarus capital Minsk appear to show new facilities set up in recent days, suggesting the swift construction of a base for Wagner, the Russian mercenary company behind an abortive mutiny. Russian media have reported that Wagner, whose leader Yevgeny Prigozhin arrived in Belarus on Tuesday, could set up a new base at a vacant military facility near the town of Asipovichi, about 90 km (50 miles) from Minsk. Images captured by the European Space Agency's Sentinel 2 satellites on June 27 show rows of long structures in the nearby village of Tsel, in a field which had appeared empty on June 14. Reuters could not verify the nature of the construction. The images are publicly available through searches on the ESA website. Belarus President Alexander Lukashenko invited Wagner to set up operations in his country as part of a deal that ended the mutiny on Saturday. (Read full report here.)
Interview: Jack Devine on The Tape - Ukraine and Russia, IBM, PacWest, and VCs (10 mins) - Bloomberg, 28 Jun 23
Former Acting CIA Dep. Dir. for Ops Jack Devine comments on recent events in Ukraine and Russia and more. (Listen here.)
Article: Russia Building A Vast Industry Of Spying Tools - New York Times, 03 Jul 23
As the war in Ukraine unfolded last year, Russia’s best digital spies turned to new tools to fight an enemy on another front: those inside its own borders who opposed the war. To aid an internal crackdown, Russian authorities had amassed an arsenal of technologies to track the online lives of citizens. After it invaded Ukraine, its demand grew for more surveillance tools. That helped stoke a cottage industry of tech contractors, which built products that have become a powerful — and novel — means of digital surveillance. The technologies have given the police and Russia’s Federal Security Service, better known as the F.S.B., access to a buffet of snooping capabilities focused on the day-to-day use of phones and websites. The tools offer ways to track certain kinds of activity on encrypted apps like WhatsApp and Signal, monitor the locations of phones, identify anonymous social media users and break into people’s accounts, according to documents from Russian surveillance providers obtained by The New York Times, as well as security experts, digital activists and a person involved with the country’s digital surveillance operations. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: ‘Urban Explorers’ and Accused Spies Chafe in Legal Limbo in Albania - New York Times, 03 Jul 23
Striking pictures of urban decay, including Soviet-era bomb shelters overgrown with weeds and the crumbling remains of factories across Eastern Europe, won a Russian photographer hundreds of thousands of Instagram followers eager to track her travels. But these days, the photographer, Svetlana Timofeyeva, 34, cannot travel much to satisfy fans of her exploits. Her passport was confiscated by the authorities in Albania, where she spent much of the past year in a women’s jail detained on accusations that have gained her a different kind of fame: that she is a Russian spy. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: Russia’s Many Spies in Mexico - Wall Street Journal, 02 Jul 23
As the dust settles around the Wagner Group revolt in Russia, inquiring minds want to know if Vladimir Putin is better or worse off than before the apparent challenge to his authoritarian rule. The answer matters to the Western Hemisphere, where Nikolai Patrushev, secretary of the Russian security council and one of Mr. Putin’s closest confidants, spearheads a shadowy spy network intent on undermining U.S. interests. It may surprise some Americans to learn that Mexico is an especially high-value target. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: CIA Fears ‘Disastrous Consequences’ As Ukraine Ignores US Warnings Against Sabotage Operations - MSN, 06 Jul 23
A slate of suspected Ukraine-backed sabotage operations set of a CIA alarm that Kyiv's actions and refusal to heed repeated warnings from the agency could lead to disastrous consequences for the war, Newsweek reported, citing military and intelligence officials. Ukrainian President Volodymyr Zelenskyy has openly pledged not to attack Russia, and early in the war entered an implicit "non-agreement" with the U.S. to avoid attempting sabotage operations as a condition of more U.S. assistance with better, longer-range weapons, according to Newsweek. However, a series of mysterious attacks likely perpetrated by Ukraine or pro-Ukraine partisans, including the explosions on the Nord Stream pipelines, the truck bomb on the Kerch Strait bridge near Crimea and drone attacks deep inside Russia, threaten to upend the conflict's delicate clandestine underworld. (Read full report here.)
Article: Kim Jong-un Wants a Satellite in Space. Seoul Says He Has a Long Way to Go - New York Times, 05 Jul 23
The satellite that North Korea attempted to put into orbit in May was so rudimentary that it could never serve as a functioning spy satellite as North Korea wished, the South Korean military said on Wednesday. North Korea launched a new rocket, the Collima-1, on May 31, with the hope of putting its first military reconnaissance satellite, the Malligyong-1, into orbit. The rocket, which set off alarms and a false evacuation order in Seoul, malfunctioned and crashed into the sea off South Korea’s west coast shortly after launch. South Korea sent military aircraft, vessels and deep-sea divers to search for debris that would yield clues about the North’s rocket and satellite technology. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
OpEd: Our system will unravel if presidents take classified information - Former DDNI Sue Gordon - Washington Post, 27 Jun 23
Just before President Donald Trump left office in January 2021, I recommended in these pages that Joe Biden forgo the courtesy of providing to his predecessor the occasional intelligence briefings some former presidents have received after leaving office. I briefed Trump many times in the Oval Office, and I cautioned that he had too many overseas interests — as well as obvious plans to remain a political actor and too little understanding of the tradecraft involved in gathering the information — to add more risk of exposure. As it was, I cautioned, “he leaves office with knowledge of some of our most precious intelligence assets in his head.” But I can see now that I underestimated the situation. Trump left office, federal prosecutors now assert, with some of our most precious intelligence assets in his pocket. I know too many people risked far too much to get that information for it to be stacked in boxes, unsecured, in a ballroom of a Florida resort. This is not something I imagined could ever occur. Nor do I believe our system accounts for not being able to trust a former commander in chief to feel the same responsibilities and live with the same burden that others who have access to that information do. If it did, we would have individual intelligence officers deciding what information to safely give a president while in office, and that would be an abysmal situation. Our system assumes that swearing to uphold and defend the Constitution creates mutual trust for each party to do their assigned job. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
OpEd: Julian Assange and Arnon Milchan: The Lopsided Scales of American Justice - The Nation, 27 Jun 23
The lopsided scales of the American justice system were on vivid display in England last weekend. In London’s His Majesty’s Prison Belmarsh—a fortress-like maximum security prison encircled by 18-foot water-stained concrete walls, balls of shinny razor wire and a dozen menacing guard towers—inmate A9397AY, otherwise known as Julian Assange, was into his fifth year of confinement. His accommodations consist of a plastic chair, a metal bed, and a steel toilet. That is where, for over four years, he has fought extradition to the United States on charges of espionage and computer intrusion in connection with the publication of hundreds of thousands of documents about the wars in Afghanistan and Iraq. Last Saturday, a crowd of supporters and campaigners marched through central London calling for Assange’s freedom. “It is now or never,” the inmate’s wife, Stella Assange, told the audience in Parliament Square. “Julian could be a few weeks away from extradition. We don’t have a clear timeline, but this really is the end game.” (Read full report here.)
Article: Switzerland overrun with foreign spies, Swiss intelligence service warns - Intel News, 28 Jun 23
Intensifying competition between the superpowers has turned Switzerland into an espionage battlefield, with more foreign spies being active there than in most other European countries, according to a new report. The report, published earlier this week by the Swiss Federal Intelligence Service (FIS), notes that Russian operatives are particularly active in the alpine country. Many Russian intelligence officers have relocated there after being expelled by a host of European countries in the past 18 months, according to the report. (Read full report here.)
Article: CIA Director Burns: What U.S. intelligence needs to do today and tomorrow - Washington Post, 07 Jul 23
This essay was adapted from remarks CIA Director William J. Burns delivered July 1 for the annual Ditchley Foundation lecture in Oxfordshire, England. The topic was “A World Transformed and the Role of Intelligence.”... "I worked early in my career as an American diplomat for Secretary of State James Baker. It was one of those rare “plastic moments” in history. The Cold War was ending, the Soviet Union was about to collapse, Germany would soon be reunified, and Saddam Hussein’s invasion of Kuwait would soon be defeated. It was a world of uncontested American primacy. History's currents seemed to flow in our direction, the power of our ideas driving the rest of the world in a slow but irresistible surge toward democracy and free markets. Our sometimes overbearing self-assurance seemed well-founded in the realities of power and influence, but it also obscured other gathering trends. Our moment of post-Cold War dominance was never going to be a permanent condition. History had not ended, nor had ideological competition. Globalization held great promise for human society, with hundreds of millions of people lifted out of poverty, but it was also bound to produce counter-pressures." (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
Truth Decay Is Putting U.S. National Security at Risk - RAND, 28 Jun 23
America's troubled relationship with facts is putting national security at risk. A recent RAND paper warned that “Truth Decay”—the diminishing role of facts and analysis in public life—could weaken our military, costs us credibility with our allies, and calls into question our ability to respond to the next big crisis. Experts from across RAND described Truth Decay as a “huge vulnerability,” an “obvious one,” “a strong weapon” in the hands of our adversaries. Yet the full extent of the damage we are doing to ourselves is only just beginning to come into focus. “We're stuck in a cycle,” said Caitlin McCulloch, an associate political scientist at RAND who coauthored the paper. “Polarization is feeding into Truth Decay, Truth Decay is feeding into polarization, and round and round we go. The harm that cycle is doing to our national security has not been fully explored.” Truth Decay is more than just a fact-free rant on cable television or a conspiracy theory bouncing around social media. RAND uses the term to describe a society pulling apart over basic facts, with opinion too often standing in for analysis and debates hardening into distrust. It helps explain why nearly two-thirds of Americans in a recent NPR/Ipsos poll said U.S. democracy is in crisis and at risk of failing. (Full report here.)
Reading between the lines of the new North Korea intelligence estimate - The Atlantic Council, 28 Jun 23
June 22 marked a watershed moment for analysis of North Korea. For the first time in over a decade, the US intelligence community publicly released a National Intelligence Estimate (NIE) on North Korea, titled “North Korea: Scenarios for Leveraging Nuclear Weapons Through 2030.” Completed in January 2023, this NIE is more than thirty years more recent than all the previously released North Korea NIEs, which date back to the 1980s or before. The new NIE lays out three pathways through 2030 for how North Korean leader Kim Jong Un’s strategy could evolve as his nuclear weapons capabilities improve. The NIE concludes that the by far most likely pathway is for Kim to leverage his nuclear capability for “coercion, potentially including non-nuclear lethal attacks, aimed at advancing the North’s goals.” It also delineates two additional low-likelihood pathways: North Korea could employ an offensive strategy to dominate the Korean Peninsula through the use of force, or it could turn to a defensive strategy, in which nuclear weapons are used solely as a deterrent. According to the estimate, Kim is most likely to continue pursuing coercion because he will be “confident that his growing nuclear capabilities will deter any unacceptable retaliation or consequences” but that he would not actually attack with them unless he “believes his regime is in peril.” (Full report here.)
The impact of COVID-19 on police intelligence reports in the United Kingdom - Journal of Policing, Intelligence, and Counterterrorism, 03 Jul 23
The coronavirus pandemic affected policing in a number of both anticipated, and unexpected ways. However, the impact on police intelligence remains an unexplored area. Understanding how the pandemic affected the volume of police intelligence is important as it underpins the intelligence-led policing model, which is as a key system that helps drive police activity. In this study, data from 20 police services over a 4-year period that outlines the annual volume of intelligence reports retained by services is analysed using inferential statistics to establish that during 2020 there was a significant rise in intelligence held by the police. In this study, several hypothesis are considered as causal factors that contributed to the rises and conclude that the pandemic is the most likely reason, which is caused by a rise in public order intelligence related to breaches of coronavirus legislation. The impact on the division of labour that arises from tasking such police intelligence is discussed, and the article calls upon similar research on the issuance of coronavirus fixed penalties and stop and search activity during the pandemic, to suggest that the rises have the potential to contribute to the disproportionate targeting of black and minority ethnic communities. We call for further research to explore this further. (Full report here.)
Why Do We Need a New Research Agenda for the Study of Intelligence? - International Journal of Intelligence and Counterintelligence, 06 Jul 23
Why do we need a new research agenda to study contemporary intelligence? This is in essence the question to which the recently published book Problematising Intelligence Studies aims to respond. The ambition to revisit and recast the study of intelligence is pressing in order to address an analytical problem currently facing intelligence studies (IS). Its exaggerated focus on states’ intelligence services and their performance, combined with modes of inquiry that largely ignore the plethora of social actors and practices that currently make up intelligence, means that much of what is going on in intelligence today largely escapes the focus of IS. To address this issue, the book aims to shape a renewed research approach and agenda. This article outlines this approach in more detail. (Full report here.)
Exclusive: The CIA's Blind Spot about the Ukraine War - Newsweek, 05 Jul 23
One of the biggest secrets of the Ukraine war is how much the CIA doesn't know. The Agency is as uncertain about Volodymyr Zelensky's thinking and intentions as it is about Vladimir Putin's. And as the Russian leader faces his biggest challenge in the aftermath of a failed mutiny, the Agency is straining to understand what the two sides will do—because President Joe Biden has determined that the United States (and Kyiv) will not undertake any actions that might threaten Russia itself or the survival of the Russian state, lest Putin escalate the conflict and engulf all of Europe in a new World War. In exchange, it expects that the Kremlin won't escalate the war beyond Ukraine or resort to the use of nuclear weapons. America's stance is under threat because the near-mutiny by Yevgeny Prigozhin, head of the Wagner Group, raises the question as to whether Moscow has run out of options. (Full report here.)
Economic Coercion: China’s Leverage in Trade - Visual Capitalist, 28 Jun 23
China’s rise as a global economic superpower has brought with it an ability for the nation to utilize its economic dominance for geopolitical purposes. In this infographic sponsored by The Hinrich Foundation, we explore China’s dominant position in the solar photovoltaic (PV) supply chain, and how this could be used as leverage against countries that are dependent on it for clean energy. (Access visual tool and full report here.)
Intelligence in History - A Collection of Recent Content
- Smuggling Weapons for the IRA with John Crawley - Spycraft 101 Podcast, 09 Jul 23
- Jay Lovestone and the British - Intelligence History, 09 Jul 23
- The Secret Role the CIA Played in Producing Alfred Hitchcock’s ‘North By Northwest’ - The Vintage News, 05 Jul 23
- ‘An anarchy of treason’: public history, insider knowledge and the early spy novels of John le Carré - Journal of Intelligence and National Security, 03 Jul 23
- KGB Espionage, Theft, and Murder: The Farewell Dossier - Cold War Documentary - The Cold War, 01 Jul 23
- Operation Chrysler and Murder Behind Enemy Lines in WWII with Pate McMichael - Secrets and Spies Podcast, 30 Jun 23
True Intelligence Matters in Film - The Great Escape - John Sturges (1963)
 A fictionalized account of one of the largest and most famous POW prison escapes in WWII, if not history more broadly. Chock full of operational tradecraft--disguise, document fabrication, forgery, covert tunneling, signaling, concealments, misdirection, covert procurement. A Royal Canadian Air Force pilot and former miner who was the operation's real-life "tunnel king" was engaged as a technical advisor for the film. In 2009, seven of the former POWs returned to actual POW camp, Stalag Luft III, for the 65th anniversary of the escape and watched the film. According to the veterans, many details of the first half depicting life in the camp were authentic, e.g. the death of Ives, who tries to scale the fence, and the actual digging of the tunnels. The film has for decades kept alive the memory of the 50 airmen executed for involvement in the operation and has made their story known worldwide.
A fictionalized account of one of the largest and most famous POW prison escapes in WWII, if not history more broadly. Chock full of operational tradecraft--disguise, document fabrication, forgery, covert tunneling, signaling, concealments, misdirection, covert procurement. A Royal Canadian Air Force pilot and former miner who was the operation's real-life "tunnel king" was engaged as a technical advisor for the film. In 2009, seven of the former POWs returned to actual POW camp, Stalag Luft III, for the 65th anniversary of the escape and watched the film. According to the veterans, many details of the first half depicting life in the camp were authentic, e.g. the death of Ives, who tries to scale the fence, and the actual digging of the tunnels. The film has for decades kept alive the memory of the 50 airmen executed for involvement in the operation and has made their story known worldwide.
More information about this based-on-true-events production here.
Walking Tours - Washington, DC - Sundays (Dates/Times Vary)
Former intelligence officers guide visitors on two morning and afternoon espionage-themed walking tours: "Spies of Embassy Row" and "Spies of Georgetown." For more information and booking, click here or contact rosanna@spyher.co
Section V - Books, Research Requests, Jobs, Obituaries
Books — Forthcoming, Newly Released, Overlooked
 The Real Special Relationship: The True Story of How MI6 and the CIA Work Together
The Real Special Relationship: The True Story of How MI6 and the CIA Work Together
by Michael Smith (Author), Sir John Scarlett (Introduction), Michael Hayden (Foreword)
(Arcade, 18 Jul 23)
The Special Relationship between the United States and Britain is touted by politicians when it suits their purpose and, as frequently, dismissed as myth, not least by the media. Yet the truth is that the two countries are bound together more closely than either is to any other ally. In The Real Special Relationship, Michael Smith reveals how it all began, eighty years ago, when a top-secret visit by four American codebreakers to Bletchley Park in February 1941—ten months before the US entered World War II—marked the start of a close collaboration between the intellitence services of the two nations. When that war ended and the Cold War began, both sides recognized that the way they worked together to decode German and Japanese ciphers could be used to counter the Soviet threat. They laid the foundation for the behind-the-scenes intelligence sharing that has continued—despite rivalries among the services and occasional political conflict and public disputes between the two nations—through the collapse of the Soviet Union, 9/11, the wars in Afghanistan and Iraq, and to the threats of the present moment. Smith, who served in British military intelligence, brings together a fascinating range of characters, from Winston Churchill and Ian Fleming to John F. Kennedy, Ronald Reagan, Margaret Thatcher, and Edward Snowden. Supported by in-depth interviews and a broad range of personal contacts in the intelligence community, he takes the reader into the workings of MI6, the CIA, the NSA, and all those who strive to keep us safe. Sir John Scarlett, former chief of MI6, has written the introduction, and Michael Hayden, former director of the CIA and the NSA, has provided the foreword.
Order book here.
 American Traitor: General James Wilkinson's Betrayal of the Republic and Escape from Justice
American Traitor: General James Wilkinson's Betrayal of the Republic and Escape from Justice
by Howard W. Cox
(Georgetown University Press, 01 Jun 23)
American Traitor examines the career of the notorious Gen. James Wilkinson, whose corruption and espionage exposed the United States to grave dangers during the early years of the republic. Wilkinson is largely forgotten today, which is unfortunate because his sordid story is a cautionary tale about unscrupulous actors who would take advantage of gaps in the law, oversight, and accountability for self-dealing. Wilkinson's military career began during the Revolutionary War and continued through the War of 1812. As he rose to the rank of commanding general of the US Army, Wilkinson betrayed virtually everyone he worked with to advance his career and finances. He was a spy for Spain, plotted to have western territories split from the United States, and accepted kickbacks from contractors. His negligence and greed also caused the largest peacetime disaster in the history of the US Army. Howard W. Cox picks apart Wilkinson's misdeeds with the eye of an experienced investigator. American Traitor offers the most in-depth analysis of Wilkinson's court-martial trials and how he evaded efforts to hold him accountable. This astounding history of villainy in the early republic will fascinate anyone with an interest in the period as well as readers of espionage history.
Order book here.
 OSINT Tools: A Practical Guide to Collection, Analysis, and Visualization
OSINT Tools: A Practical Guide to Collection, Analysis, and Visualization
by Paul Michel
(21 May 23)
OSINT Tools - A Practical Guide to Collection, Analysis, and Visualization, written by Paul Michel, is a comprehensive guidebook that equips readers with the necessary knowledge and skills to effectively leverage open source intelligence (OSINT) tools for information gathering, analysis, and visualization. In today's digital age, where vast amounts of data are available online, OSINT has become an invaluable resource for various fields, including cybersecurity, law enforcement, intelligence, journalism, and corporate investigations. This book serves as an essential resource for professionals and enthusiasts alike who seek to harness the power of OSINT tools in their work. With his extensive experience in OSINT and passion for the subject matter, Paul Michel provides readers with a step-by-step approach to navigate the ever-expanding landscape of OSINT tools. The book begins by laying a solid foundation, covering the evolution and importance of OSINT, key principles and concepts, and its applications in law enforcement, intelligence agencies, corporate investigations, journalism, and open-source investigations. The author also delves into the ethical considerations surrounding OSINT, highlighting the need for responsible and ethical practices in data collection and analysis. Throughout the book, Paul Michel introduces readers to a wide array of tools and techniques that enhance OSINT capabilities. Essential hardware requirements, operating systems, virtualization, and software tools are discussed, ensuring readers have a comprehensive understanding of the technical aspects necessary for effective OSINT investigations. The book also explores secure communication and encryption tools, data organization and management, collaboration platforms, automation through scripting and APIs, and the availability of training and certification programs. The author provides practical insights into web scraping techniques, including HTML parsing, XPath, API integration, and overcoming anti-scraping measures. Readers learn how to extract information from popular social media platforms such as Twitter, Facebook, LinkedIn, Instagram, and YouTube, as well as how to monitor online discussions, detect misinformation, and navigate the dark web. The book also delves into advanced search techniques, geolocation analysis, image and video forensics, and data visualization methods. One of the standout features of this book is its emphasis on ethical considerations. Paul Michel addresses privacy laws, consent, data protection, anonymization techniques, and intellectual property rights, ensuring readers understand the legal and ethical boundaries of OSINT investigations. The book also explores the responsible use of emerging technologies, such as facial recognition, object recognition, and deepfake detection, encouraging readers to approach these tools with a critical and ethical mindset. OSINT Tools - A Practical Guide to Collection, Analysis, and Visualization is written in a clear and accessible manner, making complex concepts and techniques easily understandable for readers at various skill levels. The book is enriched with real-world case studies, practical examples, and screenshots of tools and platforms, providing readers with a hands-on learning experience. In summary, OSINT Tools - A Practical Guide to Collection, Analysis, and Visualization is a comprehensive and authoritative resource that equips readers with the knowledge, skills, and ethical framework needed to effectively utilize OSINT tools in their investigations. Whether you are a professional in the field or an enthusiast interested in exploring the world of OSINT, this book is an invaluable companion on your journey to mastering the art of open source intelligence.
Order book here.
Research Requests and Academic Opportunities
Call for Information: Arnold M. Silvier
Relative of Silvier, aka "Richie Boy," seeks information on the person (or works of) Silver, who was in the US Army during WWII and, later, CIA (1949 - 1978), with postings in Austria, Luxembourg, Germany, Turkey and Washington DC. Please contact nboicecounseling@gmail.com
Northeastern University Security and Intelligence Studies professor researching the skill sets required for Intelligence Analysis degree holders to see success after graduation welcomes the participation of AFIO members in a 5-minute survey in support of the research. Access survey here.
Call for Information: 430th CIC in Salzburg in 1946
I am currently writing about 430th CIC in Salzburg in 1946. I have a (large) CIC file and am now trying to track down further details about two officers mentioned in this: (1) Bill Taylor. The sources do not make clear whether the officer was Major Bill G. Taylor, GSC, Head of the Counter-Intelligence Bureau of G-2 (Intelligence Section), US Forces Austria, or “Mil.Reg.” Captain Taylor of Salzburg. Any information on either/both of these officers would be most welcome. (2) Pace B Rose. Rose was a CIC Special Agent in Austria, later a CIA officer who continued to be attached to the Agency after retirement. He died on 3 January 2009. I would like to contact family and friends of Pace Rose. According to the internet, Rose had children, Donna R. Hilverts and Gary W. Rose, and five grandchildren and three great grandchildren. Please contact S.Cody@westminster.ac.uk with any information.
Call for Sources: Intelligence Officers Who Lived in Spain in the 1970s
Spanish journalist Francisco Jiménez is preparing a documentary about the intelligence services in Spain in the 70s. He is looking for intelligence officers who worked in Spain in those years. If you are willing to assist Francisco, he can be reached at fjimenez@globomedia.es.
The Washington Post is developing a multi-part audio documentary series (i.e. podcast) chronicling the Grenadian revolution and the US intervention in 1983. They've interviewed nearly 100 people so far, ranging from the heads of state, former Grenadian officials, current and former US officials, veterans, and intelligence officers. They're looking for people who served at the time and may be knowledgeable about intelligence activities in Grenada and the southern Caribbean between 1979 and Operation Urgent Fury. They would also be interested in speaking with anyone who knew Leonard Barrett during the same period. If anyone is interested in participating, please reach out to Washington Post reporter Ted Muldoon via email at ted.muldoon@washpost.com or on Signal at 651-497-5449.
Call for papers: Energy Concerns in National Security and Business Intelligence: Identifying Threats and Developing Solutions - International Journal of Intelligence and Counterintelligence
The link between energy and national security is well established and is a continuing multifaceted problem. Every facet of the intelligence process (e.g., collection, analysis, and production) has played a significant role for governments and private industry in anticipating threats to this vital sector. For example, current intelligence assessments focusing on Europe’s major energy concerns are stemming from supply-chain disruptions caused by a pandemic, Russia’s war in Ukraine, climate change, and the phasing out of coal and phasing in of renewable sources. This conference provides an opportunity to discuss the contribution of business intelligence in understanding the threat to role of energy and national security interests. It brings together prominent academic voices, experienced practitioners, and policymakers, offering an opportunity to “bridge the gap” between these sectors. We are looking for conference participants to identify critical issues and challenges, competing perspectives, new and existing trends, creative solutions for new technologies, and the emergence of new market conditions.
Proposals, abstracts, or papers should be submitted by September 1.
More information, topic suggestions, and submission instructions here.
Call for papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
History shows that without planning for post-war reconstruction, apparent victory in war can lead to long-term defeat. On the other hand, wise post-war planning can lead to friendly, peaceful, and profitable relations between victor and vanquished. For political, socio-economic and security-related planning, intelligence plays a crucial role in estimating capabilities, securing infrastructure, locating persons of interest, and rebuilding. In honor of the 75th anniversary of the European Recovery Program (Marshall Plan) after the Second World War, the editors are particularly interested in papers dealing with intelligence concerning post-war reconstruction initiatives and planning connected to historical and recent conflicts. Both case studies and theoretical and methodological approaches are welcome. The studies may include, but do not have to be focused on, the following questions and issues:
- The role of diplomatic and military intelligence during the conflict as preparation for post-war reconstruction, from the conceptual to the practical.
- What intelligence needs to be collected to secure and boost reconstruction?
- What contacts, networks, and infrastructure are necessary for intelligence to be effective?
- Who has been or should be approached and/or recruited for reconstruction efforts based on intelligence?
- When has intelligent post-war planning (or its opposite) been historically evident?
- How should intelligence interact with formerly warring parties and international organizations to empower practical reconstruction efforts?
- What intelligence collection challenges have services encountered in working for post-war peace?
- How did intelligence factor in the European Recovery Program?
- What was George C. Marshall's position on the role of intelligence in general or concrete examples related to "his" plan?
01 Nov 23 deadline. More information and submission instructions here.
Call For Articles: AFIO Journal, The Intelligencer
For the past four years, AFIO has included in The Intelligencer a series of articles on "when intelligence made a difference." Written by scholars, intelligence practitioners, students, and others, they cover events from ancient times to the modern world and in many countries. AFIO is soliciting articles for future issues. Most articles run between 2,000 and 3,000 words, although some are longer or shorter. If you have an idea for an article that fits the theme, email senior editor Peter Oleson at peter.oleson@afio.com.
Jobs
Retired Federal Government Employees Wanted - National Security Agency - Fort Meade, Maryland
The National Security Agency (NSA) may occasionally need skilled civilian retirees to augment the existing work force on high priority projects or programs. In order to fill these temporary positions quickly, we need to know who may be interested and available to return to work with us on a short notice basis as well as their skills. Retirees provide expertise and corporate knowledge to temporarily support mission requirements, manpower shortfalls, and/or mentor the next generation of Agency employees. Salary Range: $86,335 - $170,800.
Additional information and application here.
Assistant/Associate Professor of Intelligence Studies (Global Security and Intelligence Studies) - Embry-Riddle Aeronautical University - Prescott, Arizona
Embry-Riddle Aeronautical University's Prescott, Arizona campus is accepting applications for a tenure-track assistant or associate-level professor of intelligence studies to teach intelligence courses to students in the Global Security and Intelligence program. The successful candidate will teach students about the intelligence community, strategic intelligence, the intelligence cycle and intelligence analysis, writing, and briefing. Prior experience working in the intelligence community is strongly preferred. We are interested in candidates with teaching acumen in intelligence analysis and writing using structured analytical techniques.
Additional information and application here.
Teaching Associate - Intelligence and National Security Studies - Coastal Carolina University, South Carolina
The Department of Intelligence and Security Studies ( ISS ) at Coastal Carolina University is accepting applications for a pool of Teaching Associates (part-time adjunct faculty) to teach introductory and undergraduate elective course offerings for the program beginning in August 2022. While the ad is open to any specialization within the field of study, courses in the areas of homeland security, law enforcement intelligence, counter-narcotics, and cybersecurity are of particular interest. Course offerings can be in a face-to-face or synchronous online modality. To be considered, candidates must have a masters or doctoral degree in a relevant subject area. Prior professional experience in the profession, as well as prior teaching experience are preferred.
Additional information and application here.
Obituaries
![]() Dennis Sysko — Career NSA Lawyer
Dennis Sysko — Career NSA Lawyer
Dennis J. Sysko of Millersville, Maryland peacefully passed away on June 30, 2023 due to Parkinson’s disease at the age of 76. Dennis was born in Derby, Connecticut. He received his Bachelor of Science in Electrical Engineering from the University of New Haven in 1970 and his Juris Doctorate from the University of Baltimore in 1976. He was employed by the National Security Agency from 1970 to 1996 and co-founded The Law Office of Henault and Sysko, chartered in 1980 and remained a senior partner until his retirement in 2017. Some of his areas of practice were National Security Law; Security Clearance Appeals; Technology Law; Intellectual Property; Business Start-Ups; Government Contracting; Corporate Law; Adverse Actions; Business Associations; Intellectual Property Law; and National Security Agency Cases. Dennis served as an adjunct professor, University of Baltimore School of Law; served as Administrative Judge, U.S. Equal Opportunity Commission; and provided pro-bono legal services for Assistance League® of the Chesapeake.
![]() David Bitzer — Career NSA Officer
David Bitzer — Career NSA Officer
On Thursday, June 15, 2023, David Bitzer passed away at the age of 87 in his home in New Carrollton, MD. David was born in Charleston, WV. David's passion for knowledge led him to pursue a physics and engineering degree from the University of Richmond, and then an advanced degree from Industrial College of the Armed Forces from the National Defense University. He dedicated 41 years of his life to the National Security Agency, where his expertise and dedication made a significant impact. A few projects under his leadership were the development of tactical secure communications equipment for use by the military and the Blacker program that was the first DoD computer network to achieve trusted end-to-end encryption under the Trusted Computer Security Evaluation Criteria. He was also a former member of the Phoenix Society.
![]() Jack Hennessey — Decorated Military Intelligence and CIA Officer
Jack Hennessey — Decorated Military Intelligence and CIA Officer
Hennessey, John (Jack) Francis passed on Sunday, July 2, 2023 at the age of 90. John was born in Oswego, New York. He served as class president and graduated as valedictorian of the class of 1951 from Oswego High School. He attended Syracuse University on scholarship and joined Delta Tau Delta Fraternity. Jack graduated from Syracuse University with a Bachelor of Arts degree in Russian Language/Russian Studies. Jack served in the Syracuse University Air Force ROTC program and was commissioned an officer in the United States Air Force 6 June 1955. Jack attended flight school and became a Navigator/Bombardier on the B-47 aircraft. In 1959, Jack became an intelligence officer and transferred to the US Air Force Reserve. He served honorably for 30 years, commanding intelligence detachments at Homestead and Scott Air Force bases. His decorations included the Meritorious Service Medal with oak leaf cluster, and the Air Force Reserve Medal with oak leaf cluster. Jack retired from the reserve in 1985. In 1959, Jack began his civilian career with the Central Intelligence Agency. He served as an analyst and was selected to attend Harvard University in 1963. Jack graduated from Harvard with a Masters Degree in Public Administration 17 June 1965. He returned to the CIA in the Operations Division, ultimately serving as Chief of Station in several locations. Jack was awarded the Career Intelligence Medal and retired from the CIA as a GS-15 in 1992. Following retirement, Jack continued to work on contract with the Agency until 2012.
Section VI - Events
EVENT POSTPONED - 27 Jul 23 (Thursday), 1130 (Pacific) - In Person - Col. Robert W. Parr, USAF (ret) on "12 Days with a Soviet Pilot Defector" - Basque Cultural Center, San Francisco - The AFIO Andre LeGallo Chapter. No host cocktail at 1130 hours (Pacific). Meeting starts at 1200 hours. Basque Cultural Center, 599 Railroad Avenue, South San Francisco, CA. RSVP and pre-payment required. Event has been postponed to autumn.
See the AFIO Calendar of Events for scheduling further in the future.
Events from Advertisers, Corporate Sponsors, Others
"The Nation's Premier Intel and National Security Event" - Save the date for the 10th Annual AFCEA/INSA Intelligence and National Security Summit! The powerful, two-day program, at the Gaylord National Resort, will feature five blockbuster plenaries, six engaging breakout sessions, and a jam-packed exhibit hall full of the latest IC technology innovations. Top leaders will discuss State of the Community, Military Intelligence Priorities, Strategic Intelligence, and Cybersecurity Challenges. Breakout sessions with senior leaders, technology experts, and thought leaders will examine some of the most pressing issues facing the community. Plus, powerful networking opportunities designed to foster partnerships and relationship building. Check for for full agenda and updates here.
Our recommended SPY beach read this summer comes from former Navy SEAL Remi Adeleke. Hot on the heels of his featured roles in the hit film Plane and FOX's Special Forces: World's Toughest Test, this is his first book in a new thriller series, featuring Nigerian-born and New York-raised Kali Kent and the top-secret Black Box program. Like Kali Kent, Adeleke was born in western Africa. Following his father's death, he relocated permanently to the Bronx with his mother and brother. After years of making regrettable decisions, Adeleke joined the Navy in 2002 and later became a Navy SEAL. He separated from the Navy in 2016, and now he delivers his first action-packed thriller inspired by his own time in the military. Chameleon opens when a mysterious former South African commando, Lucas Van Groot, begins taking wealthy hostages all over the world, it appears at first to be a typical ransom gambit. However, it soon becomes clear that his "Hostage Inc." venture is manipulating worldwide stock markets and threatening global economic collapse. Enter Black Box, the CIA's elite, secret special operations branch—so surreptitious that not even the Director of CIA is fully privy to the unit's activities. International Spy Museum Director of Adult Education Amanda Ohlke and Adeleke will discuss how the author drew on his real-life experiences to create Kent and the Black Box. Listen in on the conversation with your favorite beachy cocktail. Your host will be enjoying something with an umbrella. Program is free of charge but requires advanced registration. Visit www.spymuseum.org.
20-22 Jul 2023 - NASIH Annual Conference 2023 – NASIH - In Person - University of Calgary, Canada
North American Society for Intelligence History's annual event. Registration is open. Full details on this two-day program, with extensive speaker line up and panels, here. Registration here.
Join intelligence and national security colleagues at the Hilton McLean Tysons Corner for INSA's Leadership Dinner honoring Dr. Stacey Dixon, Principal Deputy Director of National Intelligence, ODNI. Following her opening remarks, Dr. Dixon will join INSA Chairwoman Letitia A. Long for a moderated Q&A. Topics for discussion include: AI and emerging tech, IC data strategy, Future of Open Source, Collaboration with industry partners...and more! Plus, there will be audience Q&A. More information and registration here.
Gifts for Friends, Colleagues, Self
 Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Show your support for AFIO with our new Black Short-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $50 each including shipping.
Sizes for (M) men, only; Small, Medium, Large, XL, XXL, and XXXL. $50 per shirt.
You may pay by check or credit card. Complete your order online here or mail an order along with payment to: AFIO, 7600 Leesburg Pike, Ste 470 East, Falls Church, VA 22043-2004. Phone orders at 703-790-0320. Questions? Contact Annette at: annettej@afio.com.

PopSocket for cellphones or tablets
Show your support to AFIO while enjoying the convenience offered by our AFIO Logo PopSocket. The PopSocket is most commonly used as a stand and as a grip for your mobile phone or tablet; handy for taking selfies, watching videos, and for texting. The PopSocket looks like a small button or sticker which, when closed, sticks flat to your mobile device. However, its accordion-like design enables it to pop open for use. The benefits of using a PopSocket make it a must-have accessory for your mobile phone or tablet. It also aids in keeping your phone from slipping off your hand during use, falling, or breaking.
Price: $15. Order this and other store items online here.

Duffel Bags - Royal Blue and Black with Full Color AFIO Logo This duffel has it all when it comes to value, style and organization.
600 denier polyester canvas with polyester double contrast; D-shaped zippered entry for easy access. Front pocket with hook and loop closure. End mesh pocket Easy-access end pockets. Four durable, protective feet and built-in bottom board for added strength. Web handles with padded grip. Detachable, adjustable shoulder strap.
Dimensions: 11"h x 19.75"w x 9.75"d; Approx. 2,118 cubic inches
Price: $50. Order this and other store items online here.
AFIO Mug with color glazed seal.
Made in the U.S.A., dishwasher-safe.
$35 includes shipping.
Sip your morning joe in style or use it to stash pens, cards, paperclips, or candy.
Order this and other store items online here.

Caps - Dark Navy with Navy AFIO Logo
An authentic silhouette with the comfort of an unstructured, adjustable fit. Fabric: 100% cotton. Unstructured. Fabric strap closure with adjustable D-clip. Price: $30. Order this and other store items online here.
| PUBLISHED
IN 2023 Be informed on career opportunities in the U.S. Intelligence Community |
||
 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. AFIO's popular 47-page booklet reaches thousands of high school, college students, university guidance offices, and distributed in classes teaching intelligence, to help those considering careers in the U.S. Intelligence Community. |
 |
| This is the all new fifth edition. The publication is also popular with University Career Guidance Centers, professors and academic departments specializing in national security, and parents assisting children or grandchildren in choosing meaningful, public service careers. This booklet is provided online as a public service from the generosity of AFIO board, volunteer editors/writers, donors, and members. We thank all for their support which makes this educational effort possible. |
||
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |
||
 Guide to the Study of Intelligence...and...When Intelligence Made a Difference
Guide to the Study of Intelligence...and...When Intelligence Made a Difference
"AFIO's Guide to the Study of Intelligence" has sold out in hard-copy.
It is available in digital form in its entirety on the
AFIO website here.
Also available on the website here are the individual articles of AFIO's
history project "When Intelligence Made a Difference" that have been
published to date in The Intelligencer journal.
More articles will be appear in future editions.
Some features of the email version of the WIN do not work for readers who have chosen the Plaintext Edition, some AOL users, and readers who access their email using web mail. You may request to change from Plaintext to HTML format here afio@afio.com. For the best reading experience, the latest web edition can be found here: https://www.afio.com/pages/currentwin.htm
To unsubscribe from the WIN email list, please click the "UNSUBSCRIBE" link at the bottom of the email. If you did not subscribe to the WIN and are not a member, you received this product from a third party in violation of AFIO policy. Please forward to afio@afio.com the entire message that you received and we will remove the sender from our membership and distribution lists.
(c) 1998 thru 2023
AFIO Members Support the AFIO Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for back issues of the WINs, information about AFIO, conference agenda and registrations materials, and membership applications and much more! .
AFIO | 7600 Leesburg Pike, Suite 470 East, Falls Church, VA 22043-2004 | (703) 790-0320 (phone) | (703) 991-1278 (fax) | afio@afio.com