26 July - 01 August 2023
(Issue 29)
is sponsored by

Readers who encounter problems with the email version of this newsletter can
view the latest web edition here
CONTENTS
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
- Intelligence Community Releases Data Strategy Emphasizing Better Interoperability and Agility Needed for Critical Missions - Homeland Security Today, 31 Jul 23
- White House recommends scaling back FBI authority under intelligence act - Reuters, 31 Jul 23
- Germany warns of spying 'risks' with some China students - Spacewar, 29 Jul 23
- How is the FBI preparing to Combat AI Disinformation Threat ahead of 2024 election? - Cryptopolitan, 30 Jul 23
- Biden selects NSA veteran as national cyber director nominee - NextGov, 25 Jul 23
- Cutting-edge new aircraft have increased NZ’s surveillance capacity – but are they enough in a changing world? - The Conversation, 26 Jul 23
- NATO says it's boosting Black Sea surveillance, condemns Russian grain deal exit - Reuters, 26 Jul 23
- Aspire To Be A RAW Officer? Your Guide To Joining The Prestigious Agency - News18, 28 Jul 23
- French Investigate Chinese, Locals Over Chip-Spying Allegations - Bloomberg, 27 Jul 23
- Military intelligence: Russia beginning to collect intel on Ukraine's energy infrastructure - Kyiv Independent, 23 Jul 23
- North Korea debuts new spy and combat drones that mimic US models - NKNews, 27 Jul 23
- Open source intelligence has been crucial for tracking Iran’s drone supply to Russia - Defense One, 28 Jul 23
- Counterespionage Corner - A collection of recent material on arrests, convictions, expulsions, and more...
- Cyberespionage Collection - Newly identified actors and operations, countermeasures, policy, other...
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
- “Intelligence, Special Operations, and Strategy” – with Michael Vickers — Andrew Hammond, PhD. SpyCast
- The recent NATO summit succeeded in solidifying the alliance’s goals - now it’s time for implementation. — Former Acting CIA Dep. Dir. for Ops and Arkin Group President Jack Devine, In Other News
- Niger: Moody Coups in the Sahel | Wagner Group's New Home in Belarus | Saudi-UAE Differences Affect Regional Security, Conflict Resolution | Russia’s Africa Summit, Moscow’s Projection of Influence in the Global South | Do Spanish Elections Reveal Anything About Europe’s Far-Right' Momentum? — Former FBI Special Agent and Soufan Group CEO Ali Soufan, Intel Brief
- Prigozhin Appears Again, Wildfires, Coup in Niger, and more... | What Does North Korea Want from the US? | Germany foils a terror plot by ISIS terrorists posing as Afghan refugees — WTOP National Security Correspondent JJ Green - Inside the SCIF, Target USA, The Hunt
- In Oppenheimer Red Hunt, FBI Missed Real Atomic Spies | Fate of Top Chinese Official Remains Unknown | Netanyahu Says He May Ignore High Court, Putting Israel's Spy Agencies at Crossroads in Political Crisis - Jeff Stein and Colleagues in SpyTalk (Substack)
Section III - MEMBER CONTRIBUTIONS
- Article: U.S. Hunts Chinese Malware That Could Disrupt American Military Operations - New York Times, 29 Jul 23
- Article: What’s Fact and What’s Fiction in Oppenheimer? - Vulture, 25 Jul 23
- Video: Director Wray's Remarks at the FBI Atlanta Cyber Threat Summit (16 mins) - FBI, 26 Jul 23
- Article: Three ways a technological revolution will impact the intel community - Defense News, 26 Jul 23
- Article: Academy gives insight on intelligence field - University of Northern Georgia, 26 Jul 23
- Article: Western Agencies Offer an Open Door for Russian Defectors - Foreign Policy, 26 Jul 23
- Article: A Close and Critical Look at the 'Five Things' the ACLU Says You Need to Know About 'NSA Mass Surveillance' - Just Security, 26 Jul 23
- Article: NATO isn’t the only alliance that countries are eager to join – a brief history of the Five Eyes - The Conversation, 25 Jul 23
- Paper: China - Intelligence and Security Committee of Parliament, U.K., 13 Jul 23
- Article: The U.S. Is Falling Behind on Encryption Standards – And That’s a Global Problem - eSecurity Planet, 24 Jul 23
- Article: The Cryptographer Who Ensures We Can Trust Our Computers - Quanta Magazine, 27 Jul 23
- Article: Greece Opens Office for Support of Terror Victims - Greek Reporter, 18 Jan 21
- Article: Cosmonaut Crashed Into Earth 'Crying In Rage' - Quanta Magazine, 18 Mar 11
- Article: Former intel officer turned whistleblower alleges government coverup of UFO sightings, recovery efforts - NextGov, 26 Jul 23
- Article: The UFO Congressional Hearing Was 'Insulting', a top Pentagon Official Says - Time, 29 Jul 23
Section IV - DEEPER DIVES, OPINION, ANALYSIS, FILM, HISTORY, POP CULTURE
- Regulating National Security AI Like Covert Action? - The Lawfare Institute, 25 Jul 23
- National Security Employment - RAND Corporation, 26 Jul 23
- Encryption, quantum encryption, cybersecurity, UK Online Safety Bill - Homeland Security Newswire, 28 Jul 23
- Survey of Chinese Espionage in the United States Since 2000 - Center for Strategic and International Studies, July 2023
- Analysis: Whistleblower testimonies did not change our basic understanding of UFOs - PBS, 29 Jul 23
- January 6’s Intelligence Failures - The Dispatch, 26 Jul 2023
- Infographic and Report: Mapped: The State of Economic Freedom in 2023 - Visual Capitalist, 30 Jun 23
- Intelligence in History - A Collection of Recent Content
- True Intelligence Matters in Film: Operation Finale - Chris Weitz (2018)
- Walking Tours: The Spies of Embassy Row and Spies of Georgetown - Washington, DC. (Sundays, Dates/Times Vary)
Section V - Books, Research Requests, Academic Opportunities, Jobs, Obituaries
Books — Forthcoming, New Releases, Overlooked
- Errand into the Wilderness of Mirrors: Religion and the History of the CIA by Michael Graziano
- Foxtrot in Kandahar: A Memoir of a CIA Officer in Afghanistan at the Inception of America’s Longest War by Duane Evans
- Active Measures by Thomas Rid
Research Requests and Academic Opportunities
- Call for Sources: Cyprus 1974
- Call for Information: Rueben Efron (1911-1993), former CIA translator, HTLINGUAL
- Call for Information: Arnold M. Silvier aka "Ritchie Boy," US Army during WWII and CIA (1949 to 1978)
- Survey for Members: Skill Sets Needed for Intelligence Analysis Degree Holders to See Success After Graduation
- Call for Information: 430th CIC in Salzburg in 1946
- Call For Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
- Call For Sources: Intelligence Officers Who Lived in Spain in the 1970s
- Call For Papers: Energy Concerns in National Security and Business Intelligence: Identifying Threats and Developing Solutions - International Journal of Intelligence and Counterintelligence
- Call For Papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
- Call For Articles: AFIO Journal, The Intelligencer
- Retired Federal Government Employees Wanted - National Security Agency, Fort Meade, MD
- Assistant Professor - Intelligence Studies (Global Security and Intelligence Studies), Embry-Riddle Aeronautical University - Prescott, Arizona
- Doug Humphries, Career CIA Officer and Army Reservist and National Security Studies Academic
- Jerry Hemmen, Career CIA Communications Officer
- Steve Mrotek, Career NGA Cartographer
- Chuck Shankland, Former Dep. Dir. DIA and Decorated Career Air Force Intelligence Officer
- EVENT POSTPONED - 27 Jul 23 (Thursday), 1130 (Pacific) - In Person, San Francisco - Col. Robert W. Parr, USAF (ret), on "12 Days with a Soviet Pilot Defector" - AFIO Andre LeGallo Chapter
Events from Advertisers, Corporate Sponsors, Others
- 31 Jul - 04 Aug 2023 - 0900-1500 (ET) Spy Camp 2023 - In Person - International Spy Museum, Washington DC
- 03 Aug 23, 1730-2130 (ET) Leadership Dinner with DDNI Stacey Dixon – INSA - In Person - Tysons Corner, VA
- 10 Aug 23, 0900-0945 (ET) Strategic Intelligence Insights: Perspectives from Six Decades of National Security Leadership – INSA - Virtual
- 16 Aug 23, 1200-1300 (ET) Spying And Covert Action Made Simple - with Jack Devine, former Acting Director of CIA's operations outside of the United States – Johns Hopkins University - Virtual
- Tuesday, August 29, 2:00-3:00pm – Washington, DC – SPY with Me: Memory Loss Program – Virtual International Spy Museum Program
- Thursday, August 31, 2:00-3:00pm – Washington, DC – SPY with Me: Memory Loss Program – Virtual International Spy Museum Program
See the AFIO Calendar of Events for scheduling further in the future.
ACKNOWLEDGEMENTS
The WIN editors thank the following contributors of content for this issue:
PO, CP, EB, EM, JG, FR, KB, PK
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
The WIN editors thank the following contributors of content for this issue:
PO, CP, EB, EM, JG, FR, KB, PK
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
DISCLAIMER
Our editors include a wide range of articles and commentary in the Weekly Intelligence Notes to
inform and educate our readers. The views expressed in the articles are purely those of the authors and do not reflect support or endorsement from AFIO. WIN notices about non-AFIO events do not constitute endorsement or recommendation by AFIO.
AFIO does not vet or endorse research inquiries, career announcements, or job offers. We publish reasonable-sounding inquiries and career offerings as a service to our members. We encourage readers to exercise caution and good judgment when responding and to independently verify the source before supplying resumes, career data, or personal information.
TECHNICAL DIFFICULTIES
Readers who encounter problems with links or viewing this newsletter as an email can access
the latest web edition here.
the latest web edition here.
WORK AT AFIO
A few of the responsibilities include: • Serve as focal point for a major AFIO project, to include maintaining project database and supporting a large annual formal dinner • Provide back-up support to AFIO Directors of Membership and Operations • Support AFIO's existing partners and stakeholders ... Robust Microsoft Office Skills (Excel, Outlook, Word) required.
Full job description here.
Access CIA's Inhouse Gift Shop
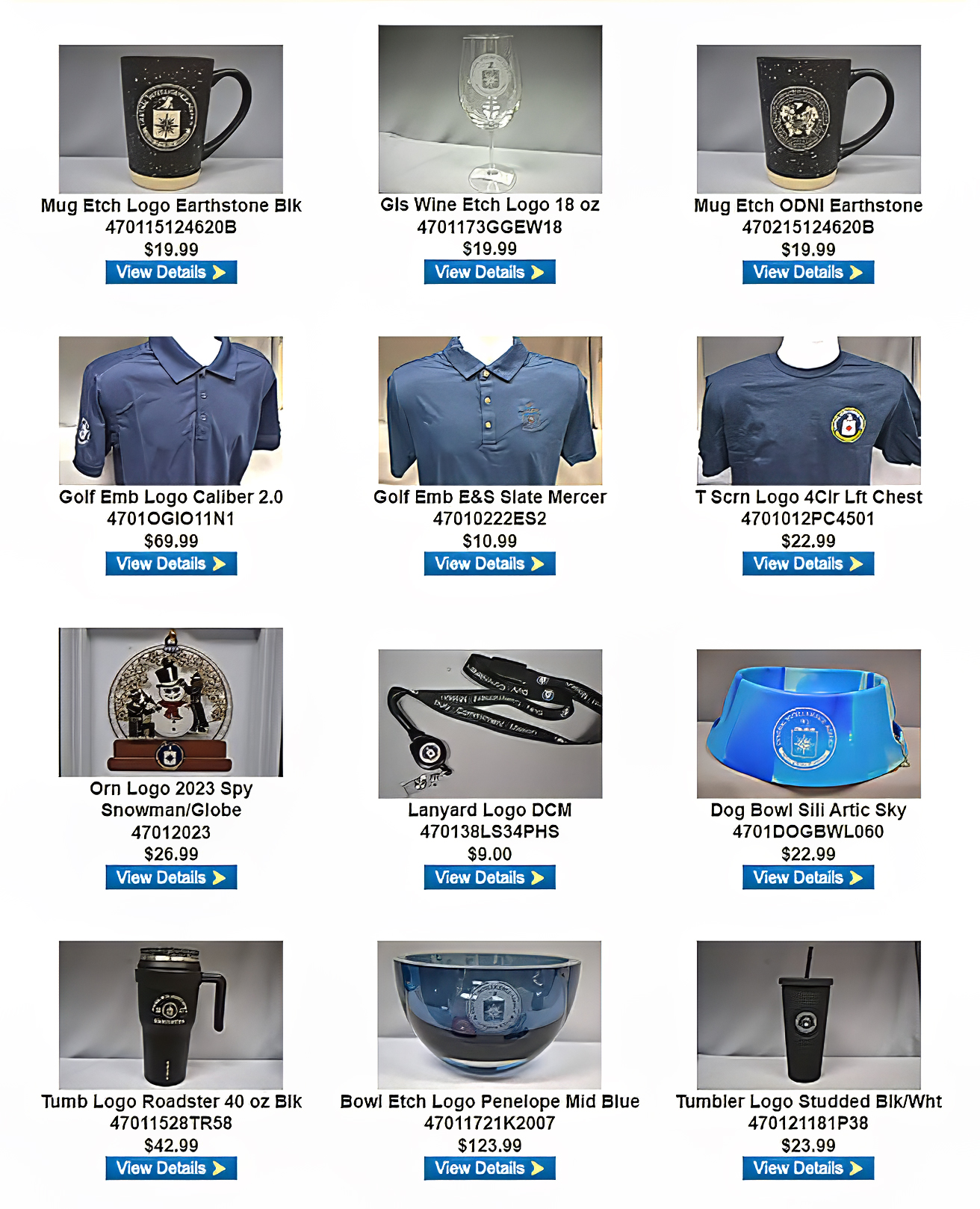
One special benefit of AFIO membership is access to CIA's EAA Store.
After completing the required, quick pre-approval process for all AFIO members, described here, you can purchase directly from the EAA online store their unusual logo'd gift items for self or colleagues. EAA on 1 July 2023 released the photo above, which features some of their newest CIA items and other gift suggestions.
LATEST FROM AFIO
Released exclusively last week to members-only
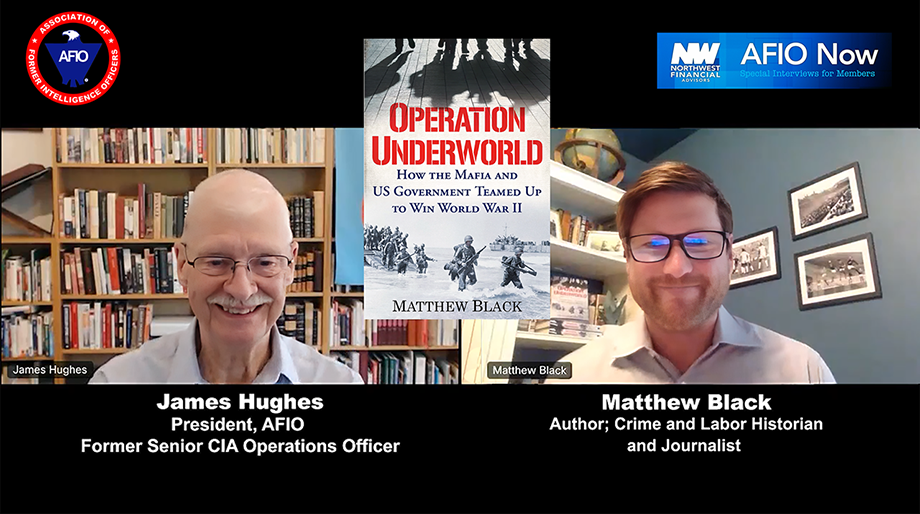
How the Mafia and U.S. Government Teamed Up to Win WW II
Interview of Friday, 2 June 2023 of Matthew Black, Author; Crime and Labor Historian and Journalist, discussing "Operation Underworld." Host and Interviewer: James Hughes, AFIO President, a former Senior CIA Operations Officer.
TOPIC: Matthew Black and Jim Hughes discuss "Operation Underworld: How the Mafia and U.S. Government Teamed Up to Win World War II" - the full story of how Charles “Lucky” Luciano, the U.S. Mafia boss, was recruited by U.S. Naval Intelligence in 1942 to aid the Allied war effort in the U.S. invasion of Sicily, a turning point in WWII.
The interview runs 37.5 minutes and includes several Q&As.
Purchase a copy of "Operation Underworld" here
Access the BLACK interview here or click above image
This, and upcoming AFIO Now videos in 2023, are sponsored by Northwest Financial Advisors.
Preview of Summer-Fall 2023 Intelligencer:
Review of former Under Secretary of State and MI5 & MI6's Legal Director David Bickford's remarkable new novel: "Katya: What Would You Risk for Half a Billion Dollars?" - reviewed by AFIO Chairman Stewart Baker
HOLD THE DATE FOR IMPORTANT EVENT THIS OCTOBER
AFIO National's Fall Luncheon
features fireside chat with Avril Haines, Director of National Intelligence,
and Jennifer K. Ewbank, the Deputy Director of CIA for Digital Innovation
Friday, 13 October 2023, 10:30am - 2pm - In-Person Tysons VA
Registration opens here on 4 September and closes when all spaces taken (or NLT 9 October).
Check-in and badge pickup for Registered Attendees begins at 10:30 a.m.
NO registrations or walk-ins at hotel. No payment accepted for this event by mail or at the venue.

Fireside chat with Avril Haines, Director of National Intelligence, begins at 11:00 a.m.
Lunch served noon to 1:00 p.m.

Jennifer Ewbank, Deputy Director of CIA for Digital Innovation speaks at 1:00 p.m.
Q&A follows each presentation. Event ends at 2:00 p.m.
Luncheon prices are $60 for Members; $75 for nonmember guests and all Subscribers. Payment by credit card required at time of registration. No mailed checks or at the door or at venue payments accepted or permitted.
Registration opens here on 4 September, and closes 5 pm Monday 9 October.
Though we do not provide special overnight room rates, if you wish to make room reservations at the hotel, do so here.
Cancellation Schedule: AFIO must commit to the hotel facilities and regrets it must charge a cancellation fee. 100% refund until close of registration. No refunds or cancellations thereafter. You will receive a donation receipt for fees forfeited. A donor statement will be sent showing that you made a "gift to AFIO" in such instances. Gifts to AFIO are tax-deductible.
All attendees must be members of AFIO or accompanied by a current member.
Learn more about becoming a member at www.afio.com. Questions regarding membership? Contact office at 703-790-0320 or email afio@afio.com
Questions regarding this event to events@afio.com

"AFIO Now" Video Interviews and Podcasts in 2023 are sponsored by
Northwest Financial Advisors
Click here to watch interviews in the AFIO Now series released in 2023.
View interviews from 2020 to 2022 here.
Watch public-release interviews on our YouTube channel or listen to them in podcast form at the links below.
Log into the member-only area for member-only features.
LATEST PODCAST: Experiences of a CIA Targeting Officer as told in the novel "The Syndicate Spy"
Brittany Butler, author and former CIA Targeter, discussing her latest book, The Syndicate Spy
Brittany Butler and AFIO's President Jim Hughes discuss THE SYNDICATE SPY, her novel, which is based on her experiences as a CIA targeting officer. It tells the tale of two female spies as they race to uncover terrorists' conspiracies and ultimately change the course of war.
Though this is her first spy thriller, she has been writing the book in her head for years. She adores thrillers and spy novels. But none of the books she read come close to telling what it was really like for a woman working at the CIA. So, when she set out to write a spy thriller, she created a fresh female protagonist who felt human, who navigates the morally grey areas in espionage, and grapples with her ability to do good in a world where she is the outsider.
Her heroine, Juliet, embodies all those things but she's not Brittany. She partners Juliet with Mariam—a Saudi feminist who is eager to see the Kingdom flourish under more progressive rulers—these two women take off in an electrifying, page-turning thriller.
The Syndicate Spy showcases these two strong women who display the badassery that a good spy thriller demands, but with unparalleled depth not seen elsewhere in the male-dominated genre.
The interview runs 17 minutes and includes several Q&As.
Are you too busy to watch an entire AFIO Now episode on YouTube? Would you rather listen in your car or while accomplishing other tasks? You can download or stream episodes on any of the 8 podcasting platforms that host AFIO Now. Search for 'AFIO Podcast' for a selection of the interviews above (public released ones) on:
Podbean; iTunes; Google; Spotify; Amazon Music; Amazon TuneIn + Alexa; iHeartRadio; Pandora
FOR YOUR FALL TRAVEL PLANS
10-12 November 2023 - Sante Fe, NM - Spies, Lies & Nukes Conference
Spies, Lies & Nukes - Third Conference - Santa Fe, NM
Plan Your Fall Attendance NOW to capture the lower rates
Special Rate Available for AFIO Members Here
 This third, enhanced running of Spies, Lies & Nukes. Join Valerie Plame and some of her legendary, highly decorated, and experienced CIA colleagues as they pull back the curtain on the real life "wilderness of mirrors" that is international espionage.
This third, enhanced running of Spies, Lies & Nukes. Join Valerie Plame and some of her legendary, highly decorated, and experienced CIA colleagues as they pull back the curtain on the real life "wilderness of mirrors" that is international espionage.
Hear from and engage with the best of CIA's spies to better understand today's world: from emergent threats, to never-before-told spy operations, black market nuclear scams, how to recruit a spy, the growth of domestic terrorism, how social media is used in espionage, and keeping your employees and your company safe from foreign spies.
Topics: "Soul Catcher: The Metaphysics of Recruiting a Spy" with Jim Lawler, Former Senior CIA Ops Officer
"Delusion and Illusion in Moscow" with Jonna Mendez in conversation with Valerie Plame, Former Covert CIA Ops Officer
"CIA in the Movies" - Panel;
"China: An Emerging Threat" with Mary Beth Long, Former Assistant Secretary of Defense for International Security Affairs
"Inside Putin's Head" with Rolf Mowatt-Larssen, Former Senior CIA Intelligence Officer
"Clarity in Crisis: Leadership Lessons from the CIA" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"Disinformation Distortions: AI, Deep Fakes, and Everything You Always Wanted to Know About Social Media and Espionage" with Alma Katsu, Former Senior CIA and NSA Analyst
"Morality and Ethics in the CIA" with Doug London, Former Senior Officer in the CIA's Clandestine Service
Michael Morell in conversation with Valerie Plame, Former Covert CIA Ops Officer
"Eliminating Players on the Intelligence Battlefield: Havana Syndrome" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"The End of the Global Nuclear Order" with Valerie Plame, Former Covert CIA Ops Officer
Program also includes: Former Senior CIA Intelligence Officer; Michael J. Morell, Former CIA Deputy Director


FEE: Regular Sale purchase window: Jun 16 - Nov 2, $1300; Late Sale purchase window: Nov 3 - Nov 10, $1450. Special AFIO rate here.
Ticket price does not include accommodations. More about accommodations here
Tickets include breakfasts, lunches, VIP reception and all speaker presentations and activities.
Conference location: Conference Location: La Fonda On the Plaza, 100 E. San Francisco Street, Santa Fe, NM 87501
More information or to register here
FROM THE AFIO STORE
 Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
In 'this remarkable book' (as intelligence historian and AFIO member Nigel West describes in his Foreword), the reader will be struck by the vibrancy of history made real. Author/AFIO member Roy Berkeley goes behind the facades of ordinary buildings, in the city that West calls 'the espionage capital of the World,' to remind us that the history of intelligence has often been made in such mundane places. With his evocative photographs and compelling observations, The 136 sites are organized into 21 manageable walks. But also a joy to armchair travelers. Among the sites: the modest hotel suite where an eager Red Army colonel poured out his secrets to a team of British and American intelligence officers; the royal residence where one of the most slippery Soviet moles was at home for years; the London home where an MP plotting to appease Hitler was arrested on his front steps in 1940.
A few copies are available at only $20 a copy (postage to a U.S.-based address included). Telephone the office at 703-790-0320 or email julie@afio.com to obtain one of these last copies.
 Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Superior quality and shrink resistant; features a detailed embroidered AFIO seal. The shirt color is royal blue.
The sale price is $25 and includes shipping.
Available in men's sizes only: small, medium, large, extra-large, XXL, and XXXL.
Due to limited quantities, please contact the AFIO National Office for availability of size and to provide payment information.
You may telephone the office at 703-790-0320 or email annettej@afio.com
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
Intelligence Community Releases Data Strategy Emphasizing Better Interoperability and Agility Needed for Critical Missions - Homeland Security Today, 31 Jul 23
With “opportunities and vulnerabilities” posed by digital transformation that “cross every facet of the IC,” the Intelligence Community released a new data strategy that aims to respond to current and future threats with “significant agility and refinement of data-driven activities.” “Embracing the complexity of the challenges in front of us, we will focus on data curation and advanced analytics to ensure data is consumable by both humans and machines,” the IC Data Strategy 2023-2025 states. “We must reduce the time from collection and data acquisition to mission insight based on a foundation of end-to-end data lifecycle management. Improving our capabilities and the associated outcomes requires changes to historical, system-centric paradigms, years of legacy practices, culture, critical partnerships across organizations, and disciplines.” The IC published its first data strategy in 2017. The new document will guide the 18 elements that comprise the IC down a stronger data-driven path as both the threat landscape and technology rapidly evolve. (View report here.)
White House recommends scaling back FBI authority under intelligence act - Reuters, 31 Jul 23
A White House review on Monday recommended that the FBI's ability to conduct non-national security queries under a controversial surveillance law be removed as part of reforms aimed at getting the law reauthorized. The Foreign Intelligence Surveillance Act's Section 702 permits the U.S. government to collect digital communications of foreigners located outside the United States. The law expires at the end of this year unless it is reauthorized and some lawmakers, both Democrat and Republican, are calling for major reforms out of concern that Section 702 has been used against Americans. "If Congress fails to reauthorize Section 702, history may judge the lapse of Section 702 authorities as one of the worst intelligence failures of our time," concluded the review, which was conducted for the White House by the president's Intelligence Advisory Board. (View report here.)
Germany warns of spying 'risks' with some China students - Spacewar, 29 Jul 23
Germany's education minister on Saturday called for a revision of student exchange practices with China, citing an increased risk of scientific espionage posed by Chinese students who come to study in Germany on full state scholarships. "China is becoming more and more competitive and is a systemic rival in the domain of science and research," Bettina Stark-Watzinger said in an interview published on Saturday by the Mediengruppe Bayern. The minister hailed a decision by the Friedrich-Alexander University (FAU) in Bavaria, which regularly partners with German industry in research projects, to no longer accept China students whose sole financing comes from the China Scholarship Council (CSC), which is a state institution. According to recent reports published in Deutsche Welle and the Corrective investigative platform, recipients of these scholarships must sign a loyalty oath to the Chinese state or risk legal proceedings. (View report here.)
How is the FBI preparing to Combat AI Disinformation Threat ahead of 2024 election? - Cryptopolitan, 30 Jul 23
As the 2024 presidential election approaches, the Federal Bureau of Investigation (FBI) is expressing grave concerns about the potential role of artificial intelligence (AI) in influencing and manipulating the electoral process. In a rare background briefing call with reporters, a senior FBI official unveiled a daunting “threat landscape,” highlighting China’s interest in stealing U.S. AI technology and data to further their own AI programs and potentially sway American opinions. Also, the FBI is closely monitoring the rising risk of disinformation campaigns fueled by AI and the alarming spread of deep fake videos. The agency also sheds light on how criminals and terrorists are capitalizing on AI to devise dangerous substances, exploit cyber vulnerabilities, and create synthetic AI-generated content that poses a formidable challenge to detection and mitigation efforts. (Full article here.)
Biden selects NSA veteran as national cyber director nominee - NextGov, 25 Jul 23
After nearly six months without a permanent National Cyber Director, the White House announced its nominee Tuesday. President Joe Biden selected former National Security Agency executive director and intelligence community veteran Harry Coker, Jr. to fill the role vacated by Chris Inglis in February and currently held in an acting capacity by Kemba Walden. Coker’s nomination comes as industry and stakeholders have been clamoring for the White House to name a permanent successor to Inglis and to help further shepherd the implementation of the National Cyber Strategy, which was unveiled in March. Coker has more than 20 years of experience in the intelligence community, including as executive director of the NSA from 2017 to 2019, in addition to multiple positions within the CIA. During his tenure at CIA, he led the agency’s Open Source Enterprise — which collects and analyzes a wide range of open source data, intelligence and information — from 2015 to 2017 and served in its Directorate of Science & Technology for more than a decade. (Full article here.)
Cutting-edge new aircraft have increased NZ’s surveillance capacity – but are they enough in a changing world? - The Conversation, 26 Jul 23
New Zealand’s national security was strengthened this month when the Royal New Zealand Air Force’s newest Boeing P-8A Poseidon aircraft became operational. A cutting-edge maritime surveillance aircraft, the P-8A is also operated by Australia, India, Norway, South Korea, the United Kingdom and the United States. It is now the New Zealand Airborne Surveillance and Response Force’s primary asset. The NZ$2.436 billion order of four P-8As allowed the retirement of six aging turbo-prop P-3K Orions. The P-8A’s cruising speed of 470 knots (903km per hour) is 40% better than the P-3K’s, and its 1,200 nautical mile (2,222km) range nearly double. With a crew of nine (pilots, flight engineers, and air warfare and ordinance specialists), it carries a suite of sensors, satellite communications, data links, and self-protection systems. As well as search and rescue, the aircraft will conduct maritime surveillance and intelligence gathering, and are capable of anti-submarine and anti-surface warfare. (Full article here.)
NATO says it's boosting Black Sea surveillance, condemns Russian grain deal exit - Reuters, 26 Jul 23
NATO said on Wednesday it was stepping up surveillance of the Black Sea region as it condemned Russia's exit from a deal assuring the safe passage of ships carrying Ukrainian grain. The announcement came after a meeting of the NATO-Ukraine Council, a body established earlier this month to coordinate cooperation between the Western military alliance and Kyiv. "Allies and Ukraine strongly condemned Russia’s decision to withdraw from the Black Sea grain deal and its deliberate attempts to stop Ukraine’s agricultural exports on which hundreds of millions of people worldwide depend," NATO said in a statement. "NATO and Allies are stepping up surveillance and reconnaissance in the Black Sea region, including with maritime patrol aircraft and drones," the statement said. (Full article here.)
Aspire To Be A RAW Officer? Your Guide To Joining The Prestigious Agency - News18, 28 Jul 23
The Research and Analysis Wing (RAW), India’s premier foreign intelligence agency, commemorates a remarkable milestone as it completes 53 years of dedicated service to the nation. Established on September 21, 1968, in the aftermath of the Indo-China War of 1962 and 1965, RAW has been at the forefront of safeguarding India’s interests on the global stage. Under the visionary guidance of its first director, Rameshwar Nath Kao, RAW has earned a reputation for its strategic expertise and operational prowess. Headquartered in Delhi, the agency’s primary mission encompasses gathering crucial foreign intelligence, counter-terrorism efforts, counter-proliferation measures, offering valuable advice to Indian policymakers, and advancing the country’s foreign strategic interests. RAW also plays a pivotal role in ensuring the security of India’s nuclear program, a vital aspect of the nation’s defence. As an elite intelligence organization, RAW recruits its officers and agents through various channels, ensuring a diverse pool of talent. One of the prominent routes to join the agency is through the UPSC Civil Services Exam (CSE), which opens opportunities for candidates aspiring to become Group-A IAS, IPS, IRS, and IFS officers. Interested individuals can register on the official website of upsc.gov.in to initiate the process. (Full article here.)
French Investigate Chinese, Locals Over Chip-Spying Allegations - Bloomberg, 27 Jul 23
French prosecutors are investigating a clutch of French and Chinese citizens accused of sharing key semiconductor technologies with foreign powers including China and Russia. Four people face prosecution, including two who are being pursued for allegedly sharing documents with a foreign power, which is likely to harm the interests of the French state, said a person who asked not to be identified because the probe isn’t public. The investigation concerns suspicions of illegal exports, criminal conspiracy, forgery and misuse of corporate assets, the person said. (Full article here.) (NOTE: This material may require a one time free subscription.)
Military intelligence: Russia beginning to collect intel on Ukraine's energy infrastructure - Kyiv Independent, 23 Jul 23
Russian intelligence services are assessing Ukraine’s energy infrastructure to identify targets that overall impact the energy system, Defense Intelligence Deputy Chief Vadym Skibitskyi said on July 23. Skibitskyi added that Russia is using different methods of reconnaissance, including satellites. "We are monitoring all issues related to the Russian intelligence on our energy facilities," Skibitskyi told in an interview with the “We-Ukraine” channel, published on July 23. Since last October, Russia launched over 1,200 missiles and drones against Ukrainian energy infrastructure. The attacks killed dozens of people and forced authorities to impose blackouts. The state-owned power grid operator Ukrenergo's key network facilities suffered extensive damage due to Russian missile and drone attacks. The reparation is still underway. UNDP and Ukraine’s Security Service estimate $1 billion is needed in 2023 to restore the energy infrastructure. (Full article here.)
North Korea debuts new spy and combat drones that mimic US models - NKNews, 27 Jul 23
North Korea unveiled two new unmanned aerial vehicles (UAVs) that closely resemble known U.S. drone models on Thursday, signaling via state media that the country is well on its way to achieving both combat and reconnaissance drone capabilities. It is unclear when Pyongyang began developing the new drones, but their reveal comes around two and a half years after the Jan. 2021 party congress, where DPRK leader Kim Jong Un ordered the military to produce “unmanned striking equipment” and “reconnaissance drones” with a range of 310 miles (500 km). Both appear in photos of the “Weapons and Equipment Exhibition 2023” held in Pyongyang on Wednesday, and both appear to be models that NK Pro first identified on runways at an airbase in the northwest of the country last month, a sign of flight testing. (Full article here.)
Open source intelligence has been crucial for tracking Iran’s drone supply to Russia - Defense One, 28 Jul 23
The Pentagon’s lead military intelligence agency has been relying on public and commercially available information to keep tabs on Russia’s movements in Ukraine. The Defense Intelligence Agency recently invited a small cadre of reporters to view recovered remnants of unmanned aerial vehicles made in Iran and used by Russia in its war on Ukraine, noting that open-source intelligence has played “an outsized” and “critical” role. “When we get a requirement, in this case, monitoring the Russian military and their aggression, the general public around the world is our source,” a senior defense intelligence official told reporters. “There's a lot more data outside in the world than there is that the IC’s collected, and so we're getting better organized to use it, and it's paying great dividends to understand what's happening.” The White House has flagged increased defense ties between Iran and Russia, and DIA confirmed Russia was using Iran-made drones earlier this year. Iran admitted last year that it sent Russia drones before the war started, but denied continued involvement, despite reports and public accusations that it was sending materials and working with Russia to build a factory. The declassification is part of a broader push to reduce disinformation, officials said. (Full article here.)
Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
- Taiwan Says China Releases Man Accused of Spying US News, 27 Jul 23
- Iran arrests members of Baha’i faith accused of spying for Israel - Alarabiya, 25 Jul 23
- Two German ministry personnel were allegedly involved in espionage on behalf of Russia. - Industry Global News 24, 27 Jul 23
- DRDO Scientist Told Pakistani Agent He Would Show Her BrahMos Missile Report, Discussed Drones And Other Missiles: Report - Outlook India, 19 Jul 23
- Russian embassy staff in Helsinki departs in large numbers after spy expulsion - Yle, 29 Jul 23
- Taiwan Busts Alleged Espionage Ring Tied To Chinese Intelligence - Overt Operator, 25 Jul 23
- Moldova expels 45 Russian diplomats, administrative staff reduced by 60 - Pravda, 26 Jul 23
- Russian Cyber Expert Accused of Spying for U.S. Gets 14 Years Behind Bars - Newsweek, 26 Jul 23
- Brazil Denies Extradition Requests From U.S., Moscow for Accused Russian Spy - The Moscow Times, 28 Jul 23
- Iran claims it dismantled Mossad-led spy network planning to blow up Soleimani’s tomb - Times of Israel, 24 Jul 23
- [ChatGPT Assisted] Mandiant: Chinese cyber espionage actors evolve tactics to avoid detection - The Readable, 24 Jul 23
- Norway investigates cyberattack affecting 12 government ministries - The Record, 24 Jul 23
- North Korean Cyberspies Target GitHub Developers - Dark Reading, 24 Jul 23
- Researchers uncover a malware network possibly linked to nation-state cyberattacks - Axios, 25 Jul 23
- Chinese Cyberespionage Group APT31 Targets Eastern European Entities - Cyware, 25 Jul 23
- Cyber Espionage Incident Involving Microsoft Cloud Expands, Chinese Hackers May Have Compromised “Hundreds of Thousands” of Government Email Accounts - CPO Magazine, 26 Jul 23
- Palo Alto Networks uncovers hackers targeting diplomats - Security Brief Asia, 28 Jul 23
- Senate opens path for a cyber-focused military branch - The Record, 28 Jul 23
- Industrial Organizations in Eastern Europe Targeted by Chinese Cyberspies - OODA Loop, 24 Jul 23
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
The Latest from International Spy Museum Historian Andrew Hammond, PhD.
 Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
25 Jul | “Intelligence, Special Operations, and Strategy” – with Michael Vickers Michael Vickers joins Andrew to discuss his remarkable career and memoir. He was formerly the Undersecretary of Defense for Intelligence.
Past episodes:
18 Jul | “Leader, Lecturer, Analyzer, Nerd” – with Jorhena Thomas
11 Jul | "The Kneeling Man" - with Letta McCollough Seletsky
04 Jul | From the Vault: “Baseball and Espionage” – with World Series Champion Ryan Zimmeram and Marc Polymeropolous (Part 1 of 2)
The Latest Insights from Former CIA Acting Deputy Director for Operations Jack Devine.
 In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
27 Jul | The recent NATO summit succeeded in solidifying the alliance’s goals - now it’s time for implementation. In mid-July, NATO leaders assembled in Vilnius, Lithuania at a meeting where painstaking diplomatic preparations and intense deliberations yielded ambitious results. While the summit gave a clear political signal of unity and opposition against Russia, the NATO commitments likely fell short of Ukraine’s expectations. However, the total package was better than many Ukrainian allies had expected, and it included commitments to provide Kyiv with ongoing political support as well as arms, munitions, supplies, and training. It also made provisions for a simplified NATO accession process for Ukraine. (Full version available to AFIO members in the coming days here.)
12 Jul | U.S. and China with little room to maneuver.
Daily Analysis of Security Issues and Geopolitical Trends
 Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
01 Aug | Niger “Un Mouvement d’humeur,” the Moody Coups in the Sahel Region
The recent coup in Niger is only the latest in a string of government upheavals across the increasingly unstable Sahel region after Nigerien military officers sequestered the democratically elected President Mohamed Bazoum. Many analysts have been unable to discern a tangible political objective behind the coup beyond maintaining access to resources and largesse for both the entrenched powerbrokers as well as an emerging new guard. The Wall Street Journal reports that prior to the coup, Bazoum had reduced financial benefits enjoyed by the presidential guard, led by General Abdourahamane Tchiani, who declared himself president of the transition council on June 28. Besides Tchiani, another leader of the coup – General Salifou Mody – was also an important figure in the previous establishment, having served as chief of staff for Niger’s armed forces before his appointment as ambassador to the United Arab Emirates in June. While Russia does not appear to have instigated the coup, it stands ready to capitalize on it, either through the Wagner Group or some other private military entity working at the behest of Moscow. (Full brief here.)
31 Jul | The Wagner Group Finds a New Home in Belarus
28 Jul | Saudi-UAE Differences Cloud Prospects for Regional Security and Conflict Resolution
27 Jul | Russia’s Africa Summit and Moscow’s Continued Quest to Project Influence in the Global South
26 Jul | Do Spanish Elections Reveal Anything About the Momentum of Europe’s Far-Right?
Analysis of Global Security Events with WTOP National Security Correspondent JJ Green
 Inside the SCIF - 27 July - Prigozhin Appears Again, Wildfires, Coup in Niger, and more...
Inside the SCIF - 27 July - Prigozhin Appears Again, Wildfires, Coup in Niger, and more...
 Target USA Podcast - 26 Jul - What Does North Korea Want from the US?
Target USA Podcast - 26 Jul - What Does North Korea Want from the US?
The Hunt Broadcast - 26 Jul - Germany foils a terror plot by ISIS terrorists posing as Afghan refugees
The Latest Insights from Jeff Stein and Colleagues in SpyTalk (Substack)
31 Jul | In Oppenheimer Red Hunt, FBI Missed Real Atomic Spies - Jeff Stein
Of the many ironies in the story of J. Robert Oppenheimer, the FBI searched for reds under the beds of virtually every suspected communist in the famed nuclear scientist’s circles, only to fail to catch the real atomic spies stealing A-bomb secrets for the Soviet Union. Oppenheimer himself, who sympathized with many communist causes, such as racial integration and support for leftists in the Spanish Civil War, was under close watch by Army counterintelligence agents and the FBI throughout his stewardship of the Manhattan Project, the super secret program in the New Mexico desert that produced the first nuclear bomb. “Despite all this surveillance and intelligence, they were completely unaware of Ted Hall, Klaus Fuchs and any of the other spies,” Kai Bird, co-author of American Prometheus, The Triumph and Tragedy of J. Robert Oppenheimer, told me in a SpyTalk podcast interview. “And there were at least three or four of them at Los Alamos. And so, it was an intelligence failure as usual in this business.” (Full article here.)
29 Jul | Fate of Top Chinese Official Remains Unknown - Matt Brazil
He’s back—in digital form, anyway. Only a few days after official Beijing erased almost all traces of the erstwhile up-and-coming foreign minister Qin Gang, his photo, along with accounts of his diplomatic forays last month, have suddenly reappeared. Why? “Maybe full erasure of a foreign minister was a bad look externally and domestically?” China expert Bill Bishop speculated on Twitter. But Beijing did not fully refresh Qin’s profile, much less his career. Today he’s listed only as a state councilor, a position technically above that of a government minister and below the level of a vice premier. His retention in this senior position on the State Council, even as he was officially removed as Foreign Minister on July 25, is a curious contradiction in Qin Gang’s downfall from his high perch as the fast-tracked protégé of President Xi Jinping. All this may indicate that Xi Jinping has not quite decided what to do with Qin. (Full article here.)
27 Jul | Breaking: Netanyahu Says He May Ignore High Court, Putting Israel's Spy Agencies at Crossroads in Political Crisis - Jonathan Broder
Prime Minister Benjamin Netayanu says he will not commit to honor a Supreme Court ruling that strikes down his newly-passed judicial overhaul law, which strips the High Court of its authority to nullify government actions. In an interview with CNN's Wolf Blitzer, Netanyahu warned Israel would be entering "uncharted territory" if the High Court issued such a ruling. “What you’re talking about is a situation, or potential situation, where in American terms, the United States’ Supreme Court would take a constitutional amendment and say that it’s unconstitutional, " Netanyahu said. “That’s the kind of spiral that you’re talking about, and I hope we don’t get to that.” As SpyTalk reported yesterday, Israel’s intelligence agencies will face a moment of truth if Netanyahu’s far-right government presents them with an order that the country’s Supreme Court has deemed illegal. (Full article here.)
To support SpyTalk, subscribe here.
Section III - MEMBER CONTRIBUTIONS
Article: U.S. Hunts Chinese Malware That Could Disrupt American Military Operations - New York Times, 29 Jul 23
The Biden administration is hunting for malicious computer code it believes China has hidden deep inside the networks controlling power grids, communications systems and water supplies that feed military bases in the United States and around the world, according to American military, intelligence and national security officials. The discovery of the malware has raised fears that Chinese hackers, probably working for the People’s Liberation Army, have inserted code designed to disrupt U.S. military operations in the event of a conflict, including if Beijing moves against Taiwan in coming years.(Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: What’s Fact and What’s Fiction in Oppenheimer? - Vulture, 25 Jul 23
Few films have ever been more based on a book than Oppenheimer. Christopher Nolan’s adaptation of Kai Bird and Martin J. Sherwin’s biography, American Prometheus, manages the astonishing feat of distilling almost every single one of the book’s 591 pages onto celluloid. Seemingly no bit of dialogue, nor stray anecdote, about the life of J. Robert Oppenheimer goes unused. In fact, Nolan’s chief creative license comes not in the film’s content but its form. While American Prometheus is told in rough chronological order, Oppenheimer skips around the timeline thanks to a pair of nesting framing devices built around a pair of 1950s hearings. Nolan also frequently cuts to fantastical imagery that attempts to dramatize what it was like inside Oppenheimer’s head. As Matt Zoller Seitz notes in his review, this method recalls the experience of getting through a book like American Prometheus: It “paradoxically captures the mental process of reading a text and responding to it emotionally and viscerally as well as intellectually.” Nevertheless, Oppenheimer is still a movie, which means that even this most rigorous of biopics must at times employ shortcuts and shorthand. With American Prometheus as our guide, here’s a rundown of what’s fact and what’s fiction. (Read full report here.)
Video: Director Wray's Remarks at the FBI Atlanta Cyber Threat Summit (16 mins) - FBI, 26 Jul 23
On 26 July 2023, FBI Director Christopher Wray addressed the FBI Atlanta Cyber Threat Summit and spoke on a variety of issues, including cybercrime and foreign threats, as well as advocating for the reauthorization of Section 702 of the Foreign Intelligence Surveillance Act. (Watch here.)
Article: Three ways a technological revolution will impact the intel community - Defense News, 26 Jul 23
In his thoughtful and significant speech titled “A World Transformed and the Role of Intelligence,” CIA Director Bill Burns laid out his case for how intelligence plays a pivotal role at this “plastic moment” in history. He led his Ditchley Annual Lecture with the challenge of Russia and China, but his most revealing point was his discussion of how intense disruption by new technologies may be the most important and wide-ranging shock to the system we face today. He called this moment “a revolution in technology more profound than the industrial revolution or the dawn of the nuclear age.” He is, of course, correct. Rapid technological change is reshaping the way we live, work and fight. The U.S. and China are competing to be first in space tech, biotech, quantum tech and a whole host of other techs that will create everything from life-saving medicine and climate solutions to life-ending bioweapons and artificial intelligence-enabled autonomous weapons systems. (Read full report here.)
Article: Academy gives insight on intelligence field - University of Northern Georgia, 26 Jul 23
The University of North Georgia (UNG) hosted a weeklong National Intelligence Summer Academy (NISA) at the Cumming Campus for 47 high school students who traveled from California, Florida, Georgia, Massachusetts, North Carolina, and Texas. The academy concluded with a visit to UNG's Dahlonega Campus where they met UNG President Michael Shannon and learned about the Corps of Cadets and some of UNG's academic programs. Held July 17-21, this was the second year of the academy. "I was amazed to see that these students were keen to learn more about the role that strategic intelligence plays in helping to safeguard our national security interests. I was pleasantly surprised by some of the students who had read up on intelligence even before the camp started and impressed to see their critical thinking skills displayed by asking complex and insightful questions," Dr. Edward L. Mienie, executive director of UNG's strategic and security studies bachelor's degree program and partnerships and professor of strategic and security studies, said. (Read full report here.)
Article: Western Agencies Offer an Open Door for Russian Defectors - Foreign Policy, 26 Jul 23
On July 19, Richard Moore, chief of the British Secret Intelligence Service (SIS, also known as MI6), offered rare public comments during his visit to Prague—including a direct appeal to Russians to “join hands” with MI6. “Our door is always open. We will handle their offers of help with the discretion and professionalism for which my service is famed. Their secrets will always be safe with us, and together we will work to bring the bloodshed to an end. My service lives by the principle that our loyalty to our agents is lifelong—and our gratitude eternal.” Coming on the heels of the mercenary Wagner Group’s short-lived mutiny, this must be a very worrying message for Russian President Vladimir Putin. The Russian autocrat understands that his last bastion of power is his security services. But Moore’s message was that even—and especially—they can choose to be on the right side of history—and do it securely, at a time when Russia’s security apparatus is already in a heightened state of angst. (Read full report here.)
Article: A Close and Critical Look at the 'Five Things' the ACLU Says You Need to Know About 'NSA Mass Surveillance' - Just Security, 26 Jul 23
On its website, the American Civil Liberties Union (ACLU) presents “Five Things to Know About NSA Mass Surveillance and the Coming Fight in Congress.” The “Coming Fight in Congress” refers to the debate that already has begun over the reauthorization of Section 702 of the Foreign Intelligence Surveillance Act (FISA). Section 702 permits the U.S. government to acquire critical intelligence from foreign targets using U.S. telecommunications services. Unlike the other collection authorities provided in FISA, Section 702 requires periodic reauthorization by Congress. The most compelling national security question this year is whether Congress will reauthorize Section 702 and, if so, what form that reauthorization will take. With the surveillance program scheduled to sunset at the end of 2023 unless renewed, an odd pairing of opponents of Section 702 on the left (who have long expressed disdain for U.S. intelligence agencies) and the “Freedom Caucus” Republicans in the House of Representatives, who have expressed their own, very different, concerns regarding the “weaponization” of the federal government, are opposing its reauthorization. (Read full report here.)
Article: NATO isn’t the only alliance that countries are eager to join – a brief history of the Five Eyes - The Conversation, 25 Jul 23
After the recent NATO summit in Vilnius, Lithuania, it is anticipated that Sweden will soon become the alliance’s 32nd member. The heart of this alliance – which was established in the aftermath of World War II to promote the collective security of its mostly Western European members – is Article 5 of the North Atlantic Treaty, which requires that if one member is attacked, then all of the other members will respond as if they themselves had been attacked. Its most recent addition came in April 2023, when Finland became the 31st country to join. At present, NATO currently recognizes Bosnia and Herzegovina, Georgia, and Ukraine as aspiring members. But NATO isn’t the only alliance that countries across the globe are eager to join. For more than 75 years, Australia, Canada, New Zealand, the U.K. and the U.S. have been sharing intelligence with one another as part of what they call the Five Eyes alliance. I am a former U.S. Army intelligence analyst who now studies and teaches political science. I know from personal experience that the Five Eyes is still very active in the 21st century, even though it’s not as well known as its younger sibling NATO. (Read full report here.)
Paper: China - Intelligence and Security Committee of Parliament, U.K., 13 Jul 23
This comprehensive intelligence assessment on China is a product of The Intelligence and Security Committee of Parliament (ISC), a statutory committee of Parliament that has responsibility for oversight of the UK Intelligence Community. The Committee was originally established by the Intelligence Services Act 1994 and was reformed, and its powers reinforced, by the Justice and Security Act 2013. The Committee oversees the intelligence and security activities of the Agencies,** including the policies, expenditure, administration and operations of MI5 (the Security Service), MI6 (the Secret Intelligence Service or SIS) and GCHQ (the Government Communications Headquarters). The Committee also scrutinises the work of other parts of the Intelligence Community, including the Joint Intelligence Organisation (JIO) and the National Security Secretariat (NSS) in the Cabinet Office; Defence Intelligence (DI) in the Ministry of Defence; and Homeland Security Group in the Home Office. The Committee consists of nine Members drawn from both Houses of Parliament. Members are appointed by the Houses of Parliament, having been nominated by the Prime Minister in consultation with the Leader of the Opposition. The Chair of the Committee is elected by its Members. (Read full report here.)
Article: The U.S. Is Falling Behind on Encryption Standards – And That’s a Global Problem - eSecurity Planet, 24 Jul 23
The U.S. National Institute of Standards and Technology (NIST) is charged with setting cybersecurity standards and validating products, yet is woefully behind on both. As new threats emerge — we’re looking at you, quantum computing — continued delays could become a crisis. Two areas that are particularly concerning are delays in FIPS 140-3 validations and the development of post-quantum cryptography. FIPS 140-3 sets encryption and protection standards for everything from software, SSDs and HDDs to network switches and new quantum encryption standards, yet product validations have been running far behind historical norms. As quantum computing technology continues to develop, this problem will become a crisis if it can’t be resolved now. (Read full report here.)
Article: The Cryptographer Who Ensures We Can Trust Our Computers - Quanta Magazine, 27 Jul 23
Yael Tauman Kalai is a pioneering theoretical computer scientist who’s won impressive awards and changed the way people think about the internet. But as a kid, she wasn’t exactly a model student. “I was a troublemaker,” she said. “I was basically — not quite, but basically — kicked out of high school.” Kalai was born and raised in Tel Aviv, Israel, in an academic family. Her father, Yair Tauman, is an economist and game theorist. Her high school classes bored her — one report card documented something like 150 school absences, she recalls, as she preferred to spend her time water skiing and socializing. But her analytical skills were always there. “When my parents didn’t let me go out, often the only way to get my dad to agree was to tell him, ‘OK, give me a math riddle. As hard as you want, but if I solve, I go.’” She usually went. (Read full report here.)
Article: Greece Opens Office for Support of Terror Victims - Greek Reporter, 18 Jan 21
Greece opened an office for the support of victims of terrorism on Monday in hopes that, as Minister of Civil Protection Michalis Chrysochoidis says, the nation can “pay its dues” to them. The Minister opened the office in a ceremony while saying “With the hope that there will never be more victims of terrorism in our country.” Chrisochoidis stated that the Office will serve as the indelible place of remembrance for the victims of terrorism, where a “memory wall” was created where the relatives of the victims can write a tribute to their loved ones who have been killed in a terrorist attack. (Read full report here.)
Article: Cosmonaut Crashed Into Earth 'Crying In Rage' - Quanta Magazine, 18 Mar 11
So there's a cosmonaut up in space, circling the globe, convinced he will never make it back to Earth; he's on the phone with Alexei Kosygin — then a high official of the Soviet Union — who is crying because he, too, thinks the cosmonaut will die. The space vehicle is shoddily constructed, running dangerously low on fuel; its parachutes — though no one knows this — won't work and the cosmonaut, Vladimir Komarov, is about to, literally, crash full speed into Earth, his body turning molten on impact. As he heads to his doom, U.S. listening posts in Turkey hear him crying in rage, "cursing the people who had put him inside a botched spaceship." This extraordinarily intimate account of the 1967 death of a Russian cosmonaut appears in a new book, Starman, by Jamie Doran and Piers Bizony, to be published next month. The authors base their narrative principally on revelations from a KGB officer, Venyamin Ivanovich Russayev, and previous reporting by Yaroslav Golovanov in Pravda. This version — if it's true — is beyond shocking. (Read full report here.)
Article: Former intel officer turned whistleblower alleges government coverup of UFO sightings, recovery efforts - NextGov, 26 Jul 23
A former intelligence official told lawmakers Wednesday that the federal government has misappropriated funds to retrieve and reverse engineer technology from crashed unidentified flying objects and has “non-human” remains in its possession from these recovery efforts. During his explosive testimony under oath before the House Oversight Subcommittee on National Security, the Border and Foreign Affairs, David Grusch — a former national reconnaissance officer who served as a member of the Pentagon’s task force on unidentified anomalous phenomena, or UAP — alleged that the federal government has relied on intimidation, budgetary trickery and classified reporting to conceal its decades-long awareness of extraterrestrial aircraft. Grusch made international news last month after he publicly shared his allegations. (Read full report here.)
Article: The UFO Congressional Hearing Was 'Insulting', a top Pentagon Official Says - Time, 29 Jul 23
A top Pentagon official has attacked this week's widely watched congressional hearing on UFOs, calling the claims “insulting” to employees who are investigating sightings and accusing a key witness of not cooperating with the official U.S. government investigation. Dr. Sean Kirkpatrick's letter, published on his personal LinkedIn page and circulated Friday across social media, criticizes much of the testimony from a retired Air Force intelligence officer that energized believers in extraterrestrial life and produced headlines around the world. Retired Air Force Maj. David Grusch testified Wednesday that the U.S. has concealed what he called a “multi-decade” program to collect and reverse-engineer “UAPs,” or unidentified aerial phenomena, the official government term for UFOs. Part of what the U.S. has recovered, Grusch testified, were non-human “biologics," which he said he had not seen but had learned about from “people with direct knowledge of the program." (Read full report here.)
Section IV - DEEPER DIVES, OPINION, ANALYSIS, FILM, HISTORY, POP CULTURE
Regulating National Security AI Like Covert Action? - The Lawfare Institute, 25 Jul 23
Congress is trying to roll up its sleeves and get to work on artificial intelligence (AI) regulation. In June, Sen. Chuck Schumer (D-N.Y.) launched a framework to regulate AI, a plan that offered high-level objectives and plans to convene nine panels to discuss hard questions, but no specific legislative language. Sen. Michael Bennet (D-Colo.) has advocated for a new federal agency to regulate AI. With others, Rep. Ted Lieu (D-Calif.) is proposing to create a National Commission on Artificial Intelligence. And at a more granular level, Sen. Gary Peters (D-Mich.) has proposed three AI bills that would focus on the government as a major purchaser and user of AI, requiring agencies to be transparent about their use of AI, to create an appeals process for citizens wronged by automated government decision-making, and to require agencies to appoint chief AI officers. But only a few of these proposed provisions implicate national security-related AI, and none create any kind of framework regulation for such tools. (Full report here.)
National Security Employment - RAND Corporation, 26 Jul 23
The U.S. government will need to proactively recruit, hire, screen, onboard, and provide continuous career-growth opportunities — while providing an exceptional candidate experience — to attract and retain new generations to the national security workforce. This report explores how existing security, suitability, and credentialing (SSC) mechanisms might benefit from a formalized candidate experience strategy and framework to create a more positive vetting experience. Organizations that provide investigative and adjudicative services (e.g., investigative service providers, authorized adjudicative agencies) and other SSC stakeholders will need to increase engagement to promote, gauge, and maintain candidate commitment throughout initial personnel vetting. SSC processes may benefit from consideration of the adoption or adaptation of some of the hiring, onboarding, and retention practices from across the private sector that are focused on creating a more engaging candidate experience. (Full report here.)
Encryption, quantum encryption, cybersecurity, UK Online Safety Bill - Homeland Security Newswire, 28 Jul 23
The U.K. Parliament is pushing ahead with a sprawling internet regulation bill that will, among other things, undermine the privacy of people around the world. The Online Safety Bill, now at the final stage before passage in the House of Lords, gives the British government the ability to force backdoors into messaging services, which will destroy end-to-end encryption. No amendments have been accepted that would mitigate the bill’s most dangerous elements. If it passes, the Online Safety Bill will be a huge step backwards for global privacy, and democracy itself. Requiring government-approved software in peoples’ messaging services is an awful precedent. If the Online Safety Bill becomes British law, the damage it causes won’t stop at the borders of the U.K. The sprawling bill, which originated in a white paper on “online harms” that’s now more than four years old, would be the most wide-ranging internet regulation ever passed. At EFF, we’ve been clearly speaking about its disastrous effects for more than a year now. (Full report here.)
Survey of Chinese Espionage in the United States Since 2000 - Center for Strategic and International Studies, July 2023
This updated survey is based on publicly available information and lists 224 reported instances of Chinese espionage directed at the United States since 2000. It does not include espionage against other countries, against U.S. firms or persons located in China, nor the many cases involving attempts to smuggle controlled items from the U.S. to China (usually munitions or controlled technologies) or the more than 1200 cases of intellectual property theft lawsuits brought by U.S. companies against Chinese entities in either the U.S. or China. The focus is on the illicit acquisition of information by Chinese intelligence officers or their agents and on the increasing number of Chinese covert influence operations. Chinese espionage is undertaken in pursuit of China’s strategic objectives. This is a change from the past where commercial motives were often equally important, but commercial espionage by both private and government entities remains a feature of Chinese spying. When Xi Jinping took office, first as Chair of the Central Military Commission in November 2012 and after he became President in March 2013, one of his first acts was to repurpose and reorient China’s collection priority to better serve long -term goals, clamping down on what appeared to be collection by some PLA units intended for personal gain (i.e. stealing commercial technology and providing it to private companies for cash or favors) as part of his larger campaign against corruption. Of the 224 incidents, we found that 69% were reported after Xi took office. (Full report here.)
Analysis: Whistleblower testimonies did not change our basic understanding of UFOs - PBS, 29 Jul 23
In May 2022, a House Intelligence subcommittee held the first congressional hearing in over half a century on military reports of UFOs. Little new light was shed on the true nature of the sightings, but the officials tried to clarify the situation by ruling things out. A congressional subcommittee met on June 26, 2023, to hear testimony from several military officers who allege the government is concealing evidence of UFOs. By holding a hearing on UFOs – now called “unidentified anomalous phenomena” by government agencies – the subcommittee sought to understand whether these UAPs pose a threat to national security. I’m an astronomer who studies and has written about cosmology, black holes, exoplanets and life in the universe. I’m also on the advisory council for an international group that strategizes how to communicate with an extraterrestrial civilization should the need ever arise. While the hearings brought attention to UAPs and could lead to more reporting from people who work in the military and aviation, the testimonies did not produce evidence to fundamentally change the understanding of UAPs. (Full report here.)
January 6’s Intelligence Failures - The Dispatch, 26 Jul 2023
Late last month, the majority staff of the Senate’s Homeland Security and Governmental Affairs Committee issued a 106-page report on the intelligence failures leading up to the January 6 “surprise” attack on the U.S. Capitol. Reading through the report, one can’t help but be gobsmacked by the amount of available, open-source information officials had about individuals traveling to Washington armed and threatening violence. Nor was there a shortage of online discussion and tips about attendees directing their ire toward the Capitol, Congress, and the final tallying of the Electoral College votes. Nevertheless, neither the FBI nor the intelligence arm of the Department of Homeland Security assessed that there was a “credible” threat of civil disobedience, let alone actual violence. There were no official warnings given to the police and security officials responsible for protecting the Capitol or congressional proceedings. Why the failure? (Full report here.)
Mapped: The State of Economic Freedom in 2023 - Visual Capitalist, 06 Jun 23
The concept of economic freedom serves as a vital framework for evaluating the extent to which individuals and businesses have the freedom to make economic decisions. In countries with low economic freedom, governments exert coercion and constraints on liberties, restricting choice for individuals and businesses, which can ultimately hinder prosperity. The map above uses the annual Index of Economic Freedom from the Heritage Foundation to showcase the level of economic freedom in every country worldwide on a scale of 0-100, looking at factors like property rights, tax burdens, labor freedom, and so on. The ranking categorizing scores of 80+ as free economies, 70-79.9 as mostly free, 60-69.9 as moderately free, 50-59.9 as mostly unfree, and 0-49.9 as repressed. (Access visual tool and full report here.)
Intelligence in History - A Collection of Recent Content
- The WWI-era Espionage Act is back in the news; its use in the Pacific Northwest marks a dark chapter of local history - Inlander, 27 Jul 23
- When a Hong Kong reporter tasted freedom after jail in China for espionage - South China Morning Post, 25 Jul 23
- The FBI surveilled J. Robert Oppenheimer for months on one man's suggestion. During the surveillance, interviewees alleged he was feeding nuclear secrets to the Soviet Union - Business Insider, 29 Jul 23
- UPDATE - On This Day — Richard Sorge is Executed for Espionage (November 7 1944) [“The spy who changed the world”] - Intel Today, 29 Jul 23
- The First Compiled History of the KL-7 - SIGINT Chatter, 23 Jul 23
- How the Soviets Stole Nuclear Secrets and Targeted Oppenheimer, the 'Father of the Atomic Bomb' - Harvard's Belfer Center, 24 Jul 23
- The Secret History of Bigfoot and the CIA - Top Secret Umbra, 29 Jul 23
True Intelligence Matters in Film - Operation Finale - Chris Weitz (2018)
 Director Chris Weitz's historical thriller is based on the true story of how a group of Israeli secret agents arrested notorious SS officer Adolf Eichmann - the man who masterminded the "Final Solution" - in Argentina. Oscar Isaac plays the legendary Mossad agent Peter Malkin, while Ben Kingsley plays his emotionally manipulative arch-nemesis. After tracking Eichmann down to Buenos Aires, Malkin and his men captured him and brought him to Israel for a historic 8-month trial.
Director Chris Weitz's historical thriller is based on the true story of how a group of Israeli secret agents arrested notorious SS officer Adolf Eichmann - the man who masterminded the "Final Solution" - in Argentina. Oscar Isaac plays the legendary Mossad agent Peter Malkin, while Ben Kingsley plays his emotionally manipulative arch-nemesis. After tracking Eichmann down to Buenos Aires, Malkin and his men captured him and brought him to Israel for a historic 8-month trial.
More information about this based-on-true-events production here.
Walking Tours - Washington, DC - Sundays (Dates/Times Vary)
Former intelligence officers guide visitors on two morning and afternoon espionage-themed walking tours: "Spies of Embassy Row" and "Spies of Georgetown." For more information and booking, click here or contact rosanna@spyher.co
Section V - Books, Research Requests, Jobs, Obituaries
Books — Forthcoming, Newly Released, Overlooked
 Errand into the Wilderness of Mirrors: Religion and the History of the CIA
Errand into the Wilderness of Mirrors: Religion and the History of the CIA
by by Michael Graziano
(University of Chicago Press, 04 Aug 23 paperback release (17 Jun 21 original hardback release))
Michael Graziano’s intriguing book fuses two landmark titles in American history: Perry Miller’s Errand into the Wilderness (1956), about the religious worldview of the early Massachusetts colonists, and David Martin’s Wilderness of Mirrors (1980), about the dangers and delusions inherent to the Central Intelligence Agency. Fittingly, Errand into the Wilderness of Mirrors investigates the dangers and delusions that ensued from the religious worldview of the early molders of the Central Intelligence Agency. Graziano argues that the religious approach to intelligence by key OSS and CIA figures like “Wild” Bill Donovan and Edward Lansdale was an essential, and overlooked, factor in establishing the agency’s concerns, methods, and understandings of the world. In a practical sense, this was because the Roman Catholic Church already had global networks of people and safe places that American agents could use to their advantage. But more tellingly, Graziano shows, American intelligence officers were overly inclined to view powerful religions and religious figures through the frameworks of Catholicism. As Graziano makes clear, these misconceptions often led to tragedy and disaster on an international scale. By braiding the development of the modern intelligence agency with the story of postwar American religion, Errand into the Wilderness of Mirrors delivers a provocative new look at a secret driver of one of the major engines of American power.
Order book here.
 Foxtrot in Kandahar: A Memoir of a CIA Officer in Afghanistan at the Inception of America’s Longest War
Foxtrot in Kandahar: A Memoir of a CIA Officer in Afghanistan at the Inception of America’s Longest War
by Duane Evans
(Savas Beatie, 15 Aug 23 paperback release (08 Aug 17 original hardback release)
Kandahar. The ancient desert crossroads and, as of fall of 2001, ground zero for the Taliban and al-Qa’ida in southern Afghanistan. In the northern part of the country, the U. S.-supported Northern Alliance (the Afghan organization opposed to the Taliban regime) has made progress on the battlefield, but in the south, the country is still under the Taliban’s bloody hold and al-Qa’ida continues to operate there. With no “Southern Alliance” for the US to support, a new strategy is needed if victory is to be achieved. Veteran CIA officer Duane Evans is dispatched to Pakistan to “get something going in the South.” Foxtrot in Kandahar is his story. Evans’s unexpected journey from the pristine halls of Langley to the badlands of southern Afghanistan began within hours after watching the horrors of 9/11 unfold during a chance visit to FBI Headquarters. It was then he decided to begin a personal and relentless quest to become part of the US response against al-Qa’ida. Evans’s gripping memoir tracks his efforts to join one of CIA’s elite teams bound for Afghanistan, a journey that eventually takes him to the front lines in Pakistan, first as part of the advanced element of CIA’s Echo team supporting Hamid Karzai, and finally as leader of the under-resourced and often overlooked Foxtrot team. Relying on rusty military skills from his days as a Green Beret, and brandishing a traded-for rifle, Evans moves toward Kandahar in the company of Pashtun warriors—one of only a handful of Americans pushing forward across the desert into some of the most dangerous, yet mesmerizingly beautiful, landscape on earth. The ultimate triumph of the CIA and Special Forces teams, when absolutely everything was on the line, is tempered by the US tragedy that catalyzed what is now America’s longest war. Evans concludes his memoir with an analysis of opportunities lost in the years since his time in Afghanistan. Brilliantly crafted and fast-paced, Foxtrot in Kandahar: A Memoir of a CIA Officer in Afghanistan at the Inception of America’s Longest War fills a major gap in the literature of the war’s critical and complex early months. It is required reading for anyone interested in modern warfare, complicated tribal politics, and the ancient land where they intersect.
Order book here.
 Active Measures
Active Measures
by Thomas Rid
(09 Mar 21)
We live in the age of disinformation―of organized deception. Spy agencies pour vast resources into hacking, leaking, and forging data, often with the goal of weakening the very foundation of liberal democracy: trust in facts. Thomas Rid, a renowned expert on technology and national security, was one of the first to sound the alarm. More than four months before the 2016 election, he warned that Russian military intelligence was “carefully planning and timing a high-stakes political campaign" to disrupt the democratic process. But as crafty as such so-called active measures have become, they are not new. The story of modern disinformation begins with the post-Russian Revolution clash between communism and capitalism, which would come to define the Cold War. In Active Measures, Rid reveals startling intelligence and security secrets from materials written in more than ten languages across several nations, and from interviews with current and former operatives. He exposes the disturbing yet colorful history of professional, organized lying, revealing for the first time some of the century’s most significant operations―many of them nearly beyond belief. A White Russian ploy backfires and brings down a New York police commissioner; a KGB-engineered, anti-Semitic hate campaign creeps back across the Iron Curtain; the CIA backs a fake publishing empire, run by a former Wehrmacht U-boat commander, that produces Germany’s best jazz magazine. Rid tracks the rise of leaking, and shows how spies began to exploit emerging internet culture many years before WikiLeaks. Finally, he sheds new light on the 2016 election, especially the role of the infamous “troll farm” in St. Petersburg as well as a much more harmful attack that unfolded in the shadows. Active Measures takes the reader on a guided tour deep into a vast hall of mirrors old and new, pointing to a future of engineered polarization, more active and less measured―but also offering the tools to cut through the deception.
Order book here.
Research Requests and Academic Opportunities
A British history journalist, Andrew Southam, is writing a book about events in Cyprus 1974, which saw an attempted coup against president Archbishop Makarios, two interventions by Turkey, the fall of the Greek Junta, the cutting of aid to Turkey and the assassination of Ambassador Ron Davies; and contributed to the murder a year later of Athens CIA station chief Dick Welch besides other British, Greek and American officials over the subsequent 27 years. This work is an accurate narrative of events (initially called ‘Cyprus’74, no control, no conspiracy’), rebutting with evidence various conspiracy allegations of US and/or British collusion with either Greece or Turkey. He would warmly welcome speaking to any intelligence officers who played a role in these events. He can be contacted at andrew2southam@yahoo.co.uk.
Call for Information: Rueben Efron (1911-1993), former CIA translator, HTLINGUAL.
Please contact Mark S. Zaid, Esq. at mark@markzaid.com or (202) 330-5610.
Call for Information: Arnold M. Silvier
Relative of Silvier, aka "Richie Boy," seeks information on the person (or works of) Silver, who was in the US Army during WWII and, later, CIA (1949 - 1978), with postings in Austria, Luxembourg, Germany, Turkey and Washington DC. Please contact nboicecounseling@gmail.com
Northeastern University Security and Intelligence Studies professor researching the skill sets required for Intelligence Analysis degree holders to see success after graduation welcomes the participation of AFIO members in a 5-minute survey in support of the research. Access survey here.
Call for Information: 430th CIC in Salzburg in 1946
I am currently writing about 430th CIC in Salzburg in 1946. I have a (large) CIC file and am now trying to track down further details about two officers mentioned in this: (1) Bill Taylor. The sources do not make clear whether the officer was Major Bill G. Taylor, GSC, Head of the Counter-Intelligence Bureau of G-2 (Intelligence Section), US Forces Austria, or “Mil.Reg.” Captain Taylor of Salzburg. Any information on either/both of these officers would be most welcome. (2) Pace B Rose. Rose was a CIC Special Agent in Austria, later a CIA officer who continued to be attached to the Agency after retirement. He died on 3 January 2009. I would like to contact family and friends of Pace Rose. According to the internet, Rose had children, Donna R. Hilverts and Gary W. Rose, and five grandchildren and three great grandchildren. Please contact S.Cody@westminster.ac.uk with any information.
Call for Sources: Intelligence Officers Who Lived in Spain in the 1970s
Spanish journalist Francisco Jiménez is preparing a documentary about the intelligence services in Spain in the 70s. He is looking for intelligence officers who worked in Spain in those years. If you are willing to assist Francisco, he can be reached at fjimenez@globomedia.es.
The Washington Post is developing a multi-part audio documentary series (i.e. podcast) chronicling the Grenadian revolution and the US intervention in 1983. They've interviewed nearly 100 people so far, ranging from the heads of state, former Grenadian officials, current and former US officials, veterans, and intelligence officers. They're looking for people who served at the time and may be knowledgeable about intelligence activities in Grenada and the southern Caribbean between 1979 and Operation Urgent Fury. They would also be interested in speaking with anyone who knew Leonard Barrett during the same period. If anyone is interested in participating, please reach out to Washington Post reporter Ted Muldoon via email at ted.muldoon@washpost.com or on Signal at 651-497-5449.
Call for papers: Energy Concerns in National Security and Business Intelligence: Identifying Threats and Developing Solutions - International Journal of Intelligence and Counterintelligence
The link between energy and national security is well established and is a continuing multifaceted problem. Every facet of the intelligence process (e.g., collection, analysis, and production) has played a significant role for governments and private industry in anticipating threats to this vital sector. For example, current intelligence assessments focusing on Europe’s major energy concerns are stemming from supply-chain disruptions caused by a pandemic, Russia’s war in Ukraine, climate change, and the phasing out of coal and phasing in of renewable sources. This conference provides an opportunity to discuss the contribution of business intelligence in understanding the threat to role of energy and national security interests. It brings together prominent academic voices, experienced practitioners, and policymakers, offering an opportunity to “bridge the gap” between these sectors. We are looking for conference participants to identify critical issues and challenges, competing perspectives, new and existing trends, creative solutions for new technologies, and the emergence of new market conditions.
Proposals, abstracts, or papers should be submitted by September 1.
More information, topic suggestions, and submission instructions here.
Call for papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
History shows that without planning for post-war reconstruction, apparent victory in war can lead to long-term defeat. On the other hand, wise post-war planning can lead to friendly, peaceful, and profitable relations between victor and vanquished. For political, socio-economic and security-related planning, intelligence plays a crucial role in estimating capabilities, securing infrastructure, locating persons of interest, and rebuilding. In honor of the 75th anniversary of the European Recovery Program (Marshall Plan) after the Second World War, the editors are particularly interested in papers dealing with intelligence concerning post-war reconstruction initiatives and planning connected to historical and recent conflicts. Both case studies and theoretical and methodological approaches are welcome. The studies may include, but do not have to be focused on, the following questions and issues:
- The role of diplomatic and military intelligence during the conflict as preparation for post-war reconstruction, from the conceptual to the practical.
- What intelligence needs to be collected to secure and boost reconstruction?
- What contacts, networks, and infrastructure are necessary for intelligence to be effective?
- Who has been or should be approached and/or recruited for reconstruction efforts based on intelligence?
- When has intelligent post-war planning (or its opposite) been historically evident?
- How should intelligence interact with formerly warring parties and international organizations to empower practical reconstruction efforts?
- What intelligence collection challenges have services encountered in working for post-war peace?
- How did intelligence factor in the European Recovery Program?
- What was George C. Marshall's position on the role of intelligence in general or concrete examples related to "his" plan?
01 Nov 23 deadline. More information and submission instructions here.
Call For Articles: AFIO Journal, The Intelligencer
For the past four years, AFIO has included in The Intelligencer a series of articles on "when intelligence made a difference." Written by scholars, intelligence practitioners, students, and others, they cover events from ancient times to the modern world and in many countries. AFIO is soliciting articles for future issues. Most articles run between 2,000 and 3,000 words, although some are longer or shorter. If you have an idea for an article that fits the theme, email senior editor Peter Oleson at peter.oleson@afio.com.
Jobs
Retired Federal Government Employees Wanted - National Security Agency - Fort Meade, Maryland
The National Security Agency (NSA) may occasionally need skilled civilian retirees to augment the existing work force on high priority projects or programs. In order to fill these temporary positions quickly, we need to know who may be interested and available to return to work with us on a short notice basis as well as their skills. Retirees provide expertise and corporate knowledge to temporarily support mission requirements, manpower shortfalls, and/or mentor the next generation of Agency employees. Salary Range: $86,335 - $170,800.
Additional information and application here.
Assistant/Associate Professor of Intelligence Studies (Global Security and Intelligence Studies) - Embry-Riddle Aeronautical University - Prescott, Arizona
Embry-Riddle Aeronautical University's Prescott, Arizona campus is accepting applications for a tenure-track assistant or associate-level professor of intelligence studies to teach intelligence courses to students in the Global Security and Intelligence program. The successful candidate will teach students about the intelligence community, strategic intelligence, the intelligence cycle and intelligence analysis, writing, and briefing. Prior experience working in the intelligence community is strongly preferred. We are interested in candidates with teaching acumen in intelligence analysis and writing using structured analytical techniques.
Additional information and application here.
Obituaries
![]() Doug Humphries — Career CIA Officer and Army Reservist and National Security Studies Academic
Doug Humphries — Career CIA Officer and Army Reservist and National Security Studies Academic
Paul Douglas "Doug" Humphries, 67, died in Waynesboro, Virginia, on July 13, 2023. He was born in El Paso, Texas. When he was four, his family moved to West Covina, California, where he spent his childhood. After graduating from West Covina High School in 1974 and the University of California, Los Angeles in 1978, Doug entered the Army through the ROTC program. He completed a three-year tour in Germany, 1979-1982. He left active duty in 1982 to pursue his MA in History at UCLA, graduating in one year. Doug had a successful 30-year career with the Central Intelligence Agency where he served mainly in analysis and analytic management positions with regional focus on the Middle East, South Asia, and the Balkans as well as functional specialties in military and security affairs. He also served tours in the Directorate of Operations, the Office of Policy Support, and the Counterterrorism Center, as well as external rotations to the Departments of State and Defense (including earning an MS in National Security Strategy from the National War College in 2012), the Federal Bureau of Investigation, and the Office of the Director of National Intelligence. In 2015, he retired and completed his Doctorate of Liberal Studies in Interdisciplinary Humanities and International Affairs from Georgetown University. Doug taught courses and guest lectured on international affairs, national security, intelligence, and military history at the National Defense University, Columbia University, and American University as well as, in retirement, VMI, Southern Virginia University, and Washington & Lee University. In addition, he retired as a Colonel with 30 years combined active and reserve duty with the US Army, serving mainly as an Infantry officer with joint special operations elements, including in overseas tours and war zone deployments.
![]() Jerry Hemmen — Career CIA Communications Officer
Jerry Hemmen — Career CIA Communications Officer
Gerald "Jerry" Hemmen, 91, was born in Granville, Iowa. He was a graduate of Fulda High School, Fulda, Minnesota. Jerry passed away on July 21, 2023 at home in Ocala, Florida surrounded by family. Jerry served four years in the Air Force and then 26 years in the Central Intelligence Agency as a communications specialist. He and Thelma were stationed in several overseas posts, including, Cyprus, Philippines, Syria, Finland and Ethiopia, enjoying "various" experiences.
![]() Steve Mrotek — Career NGA Cartographer
Steve Mrotek — Career NGA Cartographer
Steven P. Mrotek passed on Saturday, July 22nd, 2023. Steve was born in Manitowoc, Wisconsin and graduated from University of Wisconsin Platteville. He moved to St. Louis in 1985 for federal employment as a cartographer for DMAAC, which later became NGA. He retired from National Geospatial-Intelligence Agency in St. Louis in April 2017.
![]() Chuck Shankland — Former Dep. Dir. DIA and Decorated Career Airforce Intelligence Officer
Chuck Shankland — Former Dep. Dir. DIA and Decorated Career Airforce Intelligence Officer
Colonel Charles "Chuck" Shankland, a highly decorated U.S. Air Force Colonel, career Intelligence Officer and Defense Contractor Executive, has died at the age of 83. Colonel Shankland was born in Eureka in 1939. He was raised in Rapid City, attending Rapid City High School where he played Varsity Baseball and graduated in 1957. He then attended South Dakota State University, where he was Class President and graduated in 1961 and would go on to get a graduate degree from the University of Oklahoma. Colonel Shankland's Air Force Intelligence Officer career began in 1961 at the Strategic Air Command Headquarters in Omaha, Nebraska, followed quickly by an overseas assignment to Taipei, Taiwan in the Democratic Republic of China. Next was his first assignment at the Pentagon and then overseas to a combat duty tour in Vietnam where he was awarded the Bronze Star Medal. After the tour in Vietnam, (then Captain) Shankland returned to South Dakota State University as an Air Force ROTC Instructor & Professor. While there he led the SDSU ROTC detachment to Top honors in the country in 1972. After a promotion to Major and a 2nd assignment at the Pentagon, he and his family were off to another overseas assignment, 3 years in Stuttgart, Germany. Then, having been promoted to Colonel, he was back to Omaha where he served as Director of Intelligence at the Strategic Air Command Headquarters, then to Hawaii as a member of the Commander in Chief Pacific's staff. His final military tour of duty was back at the Pentagon after he was selected to serve as the Deputy Director of the Defense Intelligence Agency. A couple of his most noteworthy Intelligence efforts included the Chernobyl Nuclear meltdown, and the shoot down of Korean Air 007. During his extensive Air Force career, Colonel Shankland was awarded 11 medal citations, including the Bronze Star, Defense Superior Service Medals, Legion of Merit, and Meritorious Service Medals. Following his storied military career, retired Colonel Shankland continued to serve as a Program Director at U.S. defense contractor Northrup-Grumman, and held positions on two Defense Department Committees, the Armed Forces Communications and Electronic Association and the Strategic Development Committee.
Section VI - Events
EVENT POSTPONTED - 27 Jul 23 (Thursday), 1130 (Pacific) - In Person - Col. Robert W. Parr, USAF (ret) on "12 Days with a Soviet Pilot Defector" - Basque Cultural Center, San Francisco - The AFIO Andre LeGallo Chapter. No host cocktail at 1130 hours (Pacific). Meeting starts at 1200 hours. Basque Cultural Center, 599 Railroad Avenue, South San Francisco, CA. RSVP and pre-payment required. Event has been postponed to autumn.
See the AFIO Calendar of Events for scheduling further in the future.
Events from Advertisers, Corporate Sponsors, Others
Somewhere deep inside the Museum an elite group of recruits is lurking in the shadows preparing to take on top secret missions. No one really knows who they are, or for that matter, what they're really up to. Now it's your turn to join their ranks. Each day at Spy Camp is filled with top secret briefings and activities that will put spy skills and street smarts to the test. Aspiring KidSpy® recruits will hone their tradecraft, learn from real spies, and hit the streets of DC to run training missions. Develop a disguise for cover, make and break codes, discover escape and evasion techniques, create, and use spy gadgets, uncover the science behind spying—all of this and more awaits young recruits. Price per child (ages 9-12): $595 for regular; $515 for members. Visit www.spymuseum.org.
Join intelligence and national security colleagues at the Hilton McLean Tysons Corner for INSA's Leadership Dinner honoring Dr. Stacey Dixon, Principal Deputy Director of National Intelligence, ODNI. Following her opening remarks, Dr. Dixon will join INSA Chairwoman Letitia A. Long for a moderated Q&A. Topics for discussion include: AI and emerging tech, IC data strategy, Future of Open Source, Collaboration with industry partners...and more! Plus, there will be audience Q&A. More information and registration here.
Join INSA and AFCEA on Thursday, August 10 from 9:00 - 9:45 AM ET for a special Fireside Chat with Admiral William O. Studeman, USN, (Ret.), and his son, Rear Admiral Michael Studeman, Commander, Office of Naval Intelligence and Director, NMIO Office of Naval Intelligence. Moderated by the Honorable Joan Dempsey, the two will discuss: National security strategy and strategic intelligence; Global Cold Wars in the 20th and 21st centuries, from Europe to Asia; The role and value of open-source information; Intelligence support by industry, then and now. Plus, audience Q&A. All attendees will receive a link to the session recording! More information and free registration here.
Join Michael Ard for a curated conversation with Jack Devine, former Acting Director of CIA's operations outside of the United States on "Spying and Covert Action Made Simple." Jack Devine is a founding partner and President of The Arkin Group LLC, which specializes in international crisis management, strategic intelligence, investigative research and business problem solving. He is a 32-year veteran of the Central Intelligence Agency (“CIA”). Mr. Devine served as both Acting Director and Associate Director of CIA’s operations outside the United States from 1993-1995, where he had supervisory authority over thousands of CIA employees involved in sensitive missions throughout the world. In addition, he served as Chief of the Latin American Division from 1992-1993 and was the principal manager of the CIA’s sensitive projects in Latin America. Between 1990 and 1992, Mr. Devine headed the CIA’s Counternarcotics Center, which was responsible for coordinating and building close cooperation between all major U.S. and foreign law enforcement agencies in tracking worldwide narcotics and crime organizations. From 1985-1987, Mr. Devine headed the CIA’s Afghan Task Force, which successfully countered Soviet aggression in the region. In 1987, he was awarded the CIA’s Meritorious Officer Award for this accomplishment. Mr. Devine’s international experience with the U.S. government included postings to Latin America and Europe. During his more than 30 years with the CIA, Mr. Devine was involved in organizing, planning and executing countless sensitive projects in virtually all areas of intelligence, including analysis, operations, technology and management. He is the recipient of the Agency’s Distinguished Intelligence Medal and several meritorious awards. He is a recognized expert in Intelligence matters and has written Op-Ed articles for The Washington Post, The Wall Street Journal, The Financial Times, Foreign Affairs Magazine, The World Policy Journal, Politico and The Atlantic Monthly. He has also made guest appearances on National Press Club, CNN, CBS, NBC, MSNBC, Fox News, CSPAN, Bloomberg News as well as the History and Discovery channels, PBS, NPR and ABC Radio.
Program is free of charge but requires advanced registration here.
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. To register, please email Shana Oltmans at soltmans@spymuseum.org. Free but space is limited. Visit www.spymuseum.org.
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. To register, please email Shana Oltmans at soltmans@spymuseum.org. Free but space is limited. Visit www.spymuseum.org.
Gifts for Friends, Colleagues, Self
 Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Show your support for AFIO with our new Black Short-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $50 each including shipping.
Sizes for (M) men, only; Small, Medium, Large, XL, XXL, and XXXL. $50 per shirt.
You may pay by check or credit card. Complete your order online here or mail an order along with payment to: AFIO, 7600 Leesburg Pike, Ste 470 East, Falls Church, VA 22043-2004. Phone orders at 703-790-0320. Questions? Contact Annette at: annettej@afio.com.

PopSocket for cellphones or tablets
Show your support to AFIO while enjoying the convenience offered by our AFIO Logo PopSocket. The PopSocket is most commonly used as a stand and as a grip for your mobile phone or tablet; handy for taking selfies, watching videos, and for texting. The PopSocket looks like a small button or sticker which, when closed, sticks flat to your mobile device. However, its accordion-like design enables it to pop open for use. The benefits of using a PopSocket make it a must-have accessory for your mobile phone or tablet. It also aids in keeping your phone from slipping off your hand during use, falling, or breaking.
Price: $15. Order this and other store items online here.

Duffel Bags - Royal Blue and Black with Full Color AFIO Logo This duffel has it all when it comes to value, style and organization.
600 denier polyester canvas with polyester double contrast; D-shaped zippered entry for easy access. Front pocket with hook and loop closure. End mesh pocket Easy-access end pockets. Four durable, protective feet and built-in bottom board for added strength. Web handles with padded grip. Detachable, adjustable shoulder strap.
Dimensions: 11"h x 19.75"w x 9.75"d; Approx. 2,118 cubic inches
Price: $50. Order this and other store items online here.
AFIO Mug with color glazed seal.
Made in the U.S.A., dishwasher-safe.
$35 includes shipping.
Sip your morning joe in style or use it to stash pens, cards, paperclips, or candy.
Order this and other store items online here.

Caps - Dark Navy with Navy AFIO Logo
An authentic silhouette with the comfort of an unstructured, adjustable fit. Fabric: 100% cotton. Unstructured. Fabric strap closure with adjustable D-clip. Price: $30. Order this and other store items online here.
| PUBLISHED
IN 2023 Be informed on career opportunities in the U.S. Intelligence Community |
||
 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. AFIO's popular 47-page booklet reaches thousands of high school, college students, university guidance offices, and distributed in classes teaching intelligence, to help those considering careers in the U.S. Intelligence Community. |
 |
| This is the all new fifth edition. The publication is also popular with University Career Guidance Centers, professors and academic departments specializing in national security, and parents assisting children or grandchildren in choosing meaningful, public service careers. This booklet is provided online as a public service from the generosity of AFIO board, volunteer editors/writers, donors, and members. We thank all for their support which makes this educational effort possible. |
||
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |
||
 Guide to the Study of Intelligence...and...When Intelligence Made a Difference
Guide to the Study of Intelligence...and...When Intelligence Made a Difference
"AFIO's Guide to the Study of Intelligence" has sold out in hard-copy.
It is available in digital form in its entirety on the
AFIO website here.
Also available on the website here are the individual articles of AFIO's
history project "When Intelligence Made a Difference" that have been
published to date in The Intelligencer journal.
More articles will be appear in future editions.
Some features of the email version of the WIN do not work for readers who have chosen the Plaintext Edition, some AOL users, and readers who access their email using web mail. You may request to change from Plaintext to HTML format here afio@afio.com. For the best reading experience, the latest web edition can be found here: https://www.afio.com/pages/currentwin.htm
To unsubscribe from the WIN email list, please click the "UNSUBSCRIBE" link at the bottom of the email. If you did not subscribe to the WIN and are not a member, you received this product from a third party in violation of AFIO policy. Please forward to afio@afio.com the entire message that you received and we will remove the sender from our membership and distribution lists.
(c) 1998 thru 2023
AFIO Members Support the AFIO Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for back issues of the WINs, information about AFIO, conference agenda and registrations materials, and membership applications and much more! .
AFIO | 7600 Leesburg Pike, Suite 470 East, Falls Church, VA 22043-2004 | (703) 790-0320 (phone) | (703) 991-1278 (fax) | afio@afio.com