18 - 24 October 2023
(Issue 41)
is sponsored by

Readers who encounter problems with the email version of this newsletter can
view the latest web edition here
CONTENTS
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
- U.K. Navy ends tradition of Chinese laundrymen on warships over spying fears - The Telegraph, 23 Oct 23
- Ex-NSA employee admits trying to sell top-secret information to Russia - Axios, 23 Oct 23
- CIA has spent tens of millions on Ukrainian intelligence agencies - RT citing Washington Post, 23 Oct 23
- CIA Issued Warnings About Potential Escalated Hamas Attacks On Israel Days Before Strike - Forbes, 13 Oct 23
- Visiting professor used PhD students to gather intelligence for China, Asio boss alleges - The Guardian, 18 Oct 23
- Russian ship suspected of espionage spotted off Dutch coast - NL Times, 20 Oct 23
- How Israel underestimated Hamas’s intelligence capabilities – an expert reviews the evidence - The Conversation, 18 Oct 23
- Brazil police arrest two intel agents for alleged illegal surveillance - Reuters, 20 Oct 23
- Counterespionage Corner - A collection of recent material on arrests, convictions, expulsions, and more...
- Cyberespionage Collection - Newly identified actors and operations, countermeasures, policy, other...
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
- “The Intelligence Legacy of the Yom Kippur War” – with Uri Bar-Joseph — Andrew Hammond, PhD. SpyCast
- Hamas and Israel are now engaged in both a physical and information war. — Former Acting CIA Dep. Dir. for Ops and Arkin Group President Jack Devine, In Other News
- What Follows Hamas in Gaza? | Iran’s Role in Crisis Widens Rift with the West | Xi and Putin Meet Against Backdrop of Middle East Conflict | Iranian Proxies Threaten to Escalate Conflict | Humanitarian Crisis in Gaza | Hard Questions Ahead for Ukraine and Allies — Former FBI Special Agent and Soufan Group CEO Ali Soufan, Intel Brief
- Israel vs. Hamas | How did Hamas plot the invasion of Israel? | The fallout of the Israel-Hamas conflict — WTOP National Security Correspondent JJ Green - Inside the SCIF, Target USA, The Hunt
- The Spies of Hamas | Israel Conflict Challenges U.S. Intelligence - Jeff Stein and Colleagues in SpyTalk
Section III - MEMBER CONTRIBUTIONS
- Article: How the CIA’s top-ranking woman beat the agency’s men at their own game - Washington Post, 21 Oct 23
- Article: How Hamas Caught U.S. and Israeli Intelligence Unaware - Wall Street Journal, 19 Oct 23
- Article: The CIA dropped the ball here': Hacker hijacked the CIA's secure contact link for Russian informants due to Twitter flaw - The Daily Mail, 19 Oct 23
- Article: Spy vs. spy: How Israelis tried to stop Russia’s information war in Africa - Washington Post, 21 Oct 23
- Article: Allied Spy Chiefs Warn of Chinese Espionage Targeting Tech Firms - New York Times, 18 Oct 23
- Article: The Clever Cameras Used by the East German Stasi to Spy on Citizens - Petapixel, 16 Oct 23
- Article: Behind a Senator’s Indictments, a Foreign Spy Service Works Washington - New York Times, 13 Oct 23
- Article: Behind a Senator’s Indictments, a Foreign Spy Service Works Washington - New York Times, 13 Oct 23
- Article: A surprising number of celebrities have worked as spies - Washington Post, 22 Oct 23
- Article: Ukrainian spies with deep ties to CIA wage shadow war against Russia - Washington Post, 22 Oct 23
Section IV - DEEPER DIVES, OPINION, ANALYSIS, FILM, HISTORY, POP CULTURE
- Building Trust to Enhance Elicitation - International Journal of Intelligence and Counterintelligence, 17 Oct 2023
- State Department cipher machines and communications security in the early Cold War, 1944–1965 - Intelligence and National Security, 17 Oct 23
- Hoover Institution: FBI Director Wray and 'Five Eyes' counterparts discuss threats in first joint appearance (67 mins) - PBS, 17 Oct 23
- What we know about Beijing’s spies - The Spectator, 18 Oct 23
- Even War Has Rules, So Why No Rules for Espionage? - Homeland Security Newswire, 21 Oct 23
- How Israel’s Spies Failed—and Why Escalation Could Be Catastrophic - Foreign Policy, 19 Oct 23
- Curbing the threats to encryption - Australian Strategic Policy Institute, 23 Oct 23
- How the Chinese Communist Party Uses Cyber Espionage to Undermine the American Economy - Center for Strategic and International Studies, 19 Oct 23
- Spoils of war failures: FSB general who botched Russia's war preparations owns millions of dollars worth of real estate - The Insider, 12 Oct 23
- Infographic and Report: Visualized: Which Countries are Dominating Space
- Intelligence in History - A Collection of Recent Content
- True Intelligence Matters in Film: The Impossible Spy - Jim Goddard (1987)
- Walking Tours: The Spies of Embassy Row and Spies of Georgetown - Washington, DC. (Sundays, Dates/Times Vary)
Section V - Books, Research Requests, Academic Opportunities, Employment, Obituaries
Books — Forthcoming, New Releases, Overlooked
- The Sisterhood: The Secret History of Women at the CIA by Liza Mundy
- Marianne Is Watching: Intelligence, Counterintelligence, and the Origins of the French Surveillance State by Deborah Bauer
- Soldiers, Spies, and Statesmen: Egypt's Road to Revolt by Hazem Kandil
Research Requests and Academic Opportunities
- Call for Information: COS Manila in November 1996
- Call for Information: MACV/SOG Sgt Major Charles “Chuck” Remagen
- Call For Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
- Call For Articles: AFIO Journal, The Intelligencer
- Adjunct Faculty - MS in Intelligence Analysis - Johns Hopkins University, Maryland
- Assistant Professor - Intelligence Studies - Embry-Riddle Aeronautical University, Arizona
- Bob Martin, Decorated Military Detailee to the IC
- Marty Faga, Former NRO Director, President of MITRE, and AFIO Vice Chairman
- 26 October 2023, 7:30 pm - In-Person Pasadena, CA - AFIO Los Angeles hosts AFIO National Board Member Everette Jordan, former Deputy Assistant of the Treasury for IC Integration and National Intelligence Manager for Economic Security and Threat Finance for the DNI.
- 27 October 2023 (Friday), 3 p.m. - Naples, FL - The new Southwest FL (Naples, Fort Myers) AFIO Chapter Business and Speaker Meeting
- 9 November 2023 (Thursday), 11:00 a.m. PST - Las Vegas, NV - Las Vegas Chapter Meeting features Amir Eden, Friends of The Israeli Defense Forces (IDF), Director of Nevada, and Colorado Chapters, discussing situation in Mideast
- 9 November 2023 (Thursday), 11:30 a.m. PST - San Francisco, CA - AFIO San Francisco Chapter meeting features Ricky Deutsch on "Spies in the Sky: HEXAGON -- A History of the Last Film-Based Satellite"
- 11 November 2023 (Saturday), 11:30 a.m. - Indialantic, FL - The AFIO Florida Satellite Chapter hears from Col Susie Dabrowski USAF (Ret) on "High-Impact Operations."
Events from Advertisers, Corporate Sponsors, Others
- 26 Oct 23, 1200-1300 (ET) - Virtual - Inside Intelligence presents the Foundations of American Intelligence - Johns Hopkins University
- 1 November 2023, 1200 - 1300 (ET) - Virtual - Leadership Analysis: Understanding an Intelligence Discipline - Johns Hopkins University
- 8 November 2023, 6 - 8pm EST - Williamsburg, VA - Veterans Day Book Talk with Brian Morra '78 on "Cold War History to Today's Russian Invasion of Ukraine"
- 14 - 25 April 2024 - Gary Powers' Cold War Espionage Tour of Austria, the Czech Republic, Slovakia & Hungary - Travel Dates: April 14 to 25,2024 - 12 days/10 nights
See the AFIO Calendar of Events for scheduling further in the future.
ACKNOWLEDGEMENTS
The WIN editors thank the following contributors of content for this issue:
GR, PO, LR, FR, JK, CP, EB, JD, MA
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
The WIN editors thank the following contributors of content for this issue:
GR, PO, LR, FR, JK, CP, EB, JD, MA
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
DISCLAIMER
Our editors include a wide range of articles and commentary in the Weekly Intelligence Notes to
inform and educate our readers. The views expressed in the articles are purely those of the authors and do not reflect support or endorsement from AFIO. WIN notices about non-AFIO events do not constitute endorsement or recommendation by AFIO.
AFIO does not vet or endorse research inquiries, career announcements, or job offers. We publish reasonable-sounding inquiries and career offerings as a service to our members. We encourage readers to exercise caution and good judgment when responding and to independently verify the source before supplying resumes, career data, or personal information.
TECHNICAL DIFFICULTIES
Readers who encounter problems with links or viewing this newsletter as an email can access
the latest web edition here.
the latest web edition here.
Access CIA's Inhouse Gift Shop
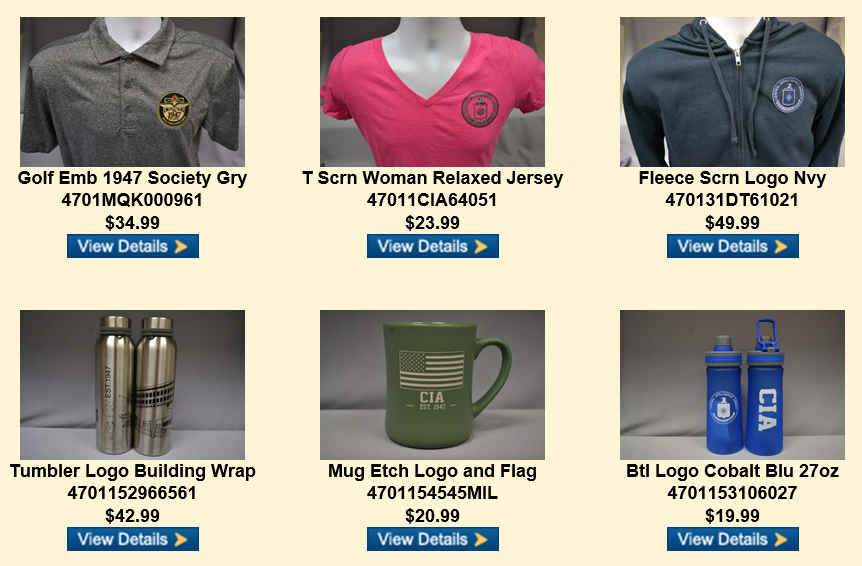
One special benefit of AFIO membership is access to CIA's EAA Store.
After completing the required, quick pre-approval process for all AFIO members described here, you can purchase directly from the EAA online store their unusual logo'd gift items for self or colleagues. EAA on 17 October 2023 released the photo above, which features some of their newest CIA items and other gift suggestions.
FROM THE AFIO STORE
 Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
In 'this remarkable book' (as intelligence historian and AFIO member Nigel West describes in his Foreword), the reader will be struck by the vibrancy of history made real. Author/AFIO member Roy Berkeley goes behind the facades of ordinary buildings, in the city that West calls 'the espionage capital of the World,' to remind us that the history of intelligence has often been made in such mundane places. With his evocative photographs and compelling observations, The 136 sites are organized into 21 manageable walks. But also a joy to armchair travelers. Among the sites: the modest hotel suite where an eager Red Army colonel poured out his secrets to a team of British and American intelligence officers; the royal residence where one of the most slippery Soviet moles was at home for years; the London home where an MP plotting to appease Hitler was arrested on his front steps in 1940.
A few copies are available at only $20 a copy (postage to a U.S.-based address included). Telephone the office at 703-790-0320 or email julie@afio.com to obtain one of these last copies.
 Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Clearance Sale on Long-Sleeved Polo Shirts with AFIO Logo
Superior quality and shrink resistant; features a detailed embroidered AFIO seal. The shirt color is royal blue.
The sale price is $25 and includes shipping.
Available in men's sizes only: small, medium, large, extra-large, XXL, and XXXL.
Due to limited quantities, please contact the AFIO National Office for availability of size and to provide payment information.
You may telephone the office at 703-790-0320 or email annettej@afio.com
LATEST FROM AFIO
Released exclusively to members 17 October 2023...
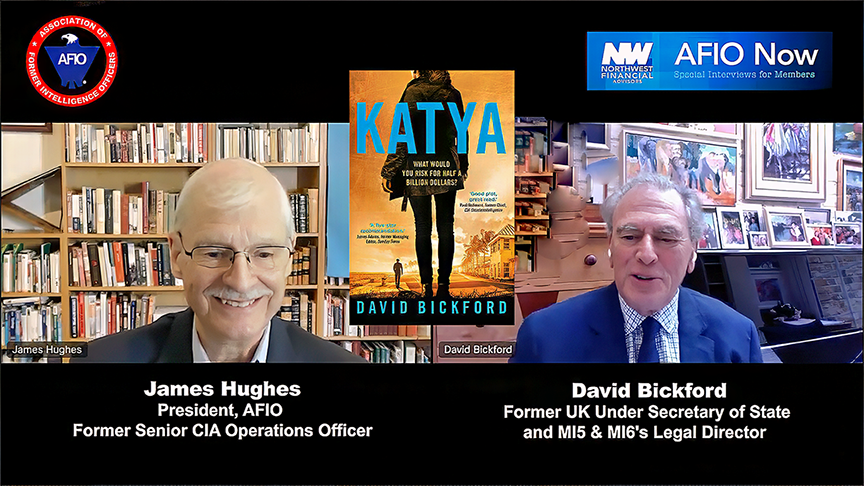
What Would You Risk for Half a Billion Dollars?
David Bickford, Former UK Under Secretary of State & MI5 & MI6 Legal Director
on his novel "Katya"
Interview of Thursday, 20 July 2023 between David Bickford, Former UK Under Secretary of State & MI5 & MI6 Legal Director, on his novel Katya, and AFIO President James Hughes, a former senior CIA Operations Officer.
They discuss the plot, the use of Katya - an urchin living on the streets of Russia - and Bickford's professional insights on full display as his protagonist faces difficulties all spies are familiar with...and some they aren't. Katya finds herself in a race against time, navigating a treacherous landscape of deception, money laundering, prostitution, and terrorism. The outcome remains uncertain as she battles Cartwright's schemes and confronts her own demons. With her team at her side, Katya must rely on her training and experience to survive and succeed in her mission to retrieve Gadaifi’s stolen fortune. Bickford also closes with advice to those considering a career in the intelligence services.
The interview runs 11 minutes and includes several Q&As.
“Katya combines just enough professionally informed realism with great plot and character development to hold a former intelligence officer’s attention - a great read as only the Brits can do it.”
-- Paul Redmond - Chief, CIA Counterintelligence, Retired; AFIO Member.
"Bickford is a legend from the world of espionage and counter-espionage." -- James Adams, Advisor National Security Agency
David Bickford's books can be found here and can be purchased in the U.S. here
AFIO Chairman Stewart Baker's review of Katya is here
Access the David Bickford interview here or click above image.
This, and upcoming AFIO Now videos in 2023, are sponsored by Northwest Financial Advisors.

AFIO National 2024 Board Elections Have Opened
Members... cast your ballot here
[Requires log-in to ensure valid and current membership]
Elections close Thursday, 30 November 2023 at 11:45 p.m. ET
“From IWP with Love”: An Evening of Espionage - Institute of World Politics
26 October 2023, 6 - 10 pm - Washington, DC
 Join IWP supporters, alumni, and friends for a special Black Tie celebration of The Institute of World Politics! Includes tour of the International Spy Museum.
Join IWP supporters, alumni, and friends for a special Black Tie celebration of The Institute of World Politics! Includes tour of the International Spy Museum.
6:00 PM VIP Exhibit Tours; 6:45 PM General Reception and Dinner Buffet; 7:30 PM Remarks; 8:00 PM Dancing
Exhibits open until 10:00 PM
Options for Attendance:
• You may choose to become a member of the IWP Chancellor's Council (annual donation of $1000 or more) and receive complimentary tickets to all of the Chancellor's Council events, which will take place from October 25-26.
• You may choose to purchase tickets.
• You may choose to become a sponsor.
If you would like to become a sponsor, or if you have questions about becoming a Chancellor's Council member, please email Ariane Sweeney at asweeney@iwp.edu.
Dress: Black Tie or Military Dress Equivalent Optional
Event location: International Spy Museum, 700 L'Enfant Plaza SW, Washington, DC 20024
Accommodations: IWP has a room block at the St. Regis for October 24-27, 2023. Deluxe King rooms are $445 per night, and Premier Deluxe King rooms are $465 per night. Book a room online or call 1-888-627-8087. Because these rooms are limited, we encourage you to book early if you plan to attend.
To explore this upcoming event or to purchase a ticket and view sponsorship opportunities, please click here.

"AFIO Now" Video Interviews and Podcasts in 2023 are sponsored by
Northwest Financial Advisors
Click here to watch interviews in the AFIO Now series released in 2023.
View interviews from 2020 to 2022 here.
Watch public-release interviews on our YouTube channel or listen to them in podcast form at the links below.
Log into the member-only area for member-only features.
LATEST PODCAST: Interview of I.S. Berry. In this episode, former CIA Operations Officer, lawyer, and novelist I.S. Berry discusses her latest novel, "The Peacock and the Sparrow", a spy thriller that takes place against the backdrop of the Arab Spring. Recorded 5 July 2023. Interviewer: Jim Hughes, AFIO President and former CIA Operations Officer.
AFIO Podcast here.
Are you too busy to watch an entire AFIO Now episode on YouTube? Would you rather listen in your car or while accomplishing other tasks? You can download or stream episodes on any of the 8 podcasting platforms that host AFIO Now. Search for 'AFIO Podcast' for a selection of the interviews above (public released ones) on:
Podbean; iTunes; Google; Spotify; Amazon Music; Amazon TuneIn + Alexa; iHeartRadio; Pandora
Special Walking Tours Announcements
from SpyGuide Tours Inc.
from SpyGuide Tours Inc.
Saturday 21 October 2023. Last chance this year to attend "The January 6th Experience" walking tour from the White House to the Capitol, with Spyher host, misinformation expert, and former intelligence analyst. Book at https://spyher.co and use Promo Code J6E2023 for $20 off. $5 of each sale will be donated to the Capitol Police Memorial Fund.
The Spies of Wall Street, available daily. Book at https://spyher.co and embark on a riveting journey through lower Manhattan, where every corner reveals secrets stepped in espionage and intrigue. Traverse the annals of history, from the clandestine operations of George Washington's intelligence network during the Revolutionary War to the audacious actions of Soviet sleeper agents, perfectly hidden within New York's glitterati.
Visit https://spyher.co to learn more and book all tours.

Spies, Lies & Nukes - Third Conference - Santa Fe, NM
Plan Your Fall Attendance NOW to capture the lower rates
Special Rate Available for AFIO Members Here
10-12 November 2023 - Sante Fe, NM - Spies, Lies & Nukes Conference
We will meet Nov 10-12 at the beautiful La Fonda Resort in Santa Fe, NM. We have added an additional day to this year's conference and EVERYONE is a VIP and invited to attend the VIP reception on Friday evening.
Hear about intriguing, provocative, and sometimes shocking conversations on cyberattacks, covert actions, nuclear scams, how real spies are recruited, and daring operations that changed history from legendary and highly decorated CIA officers who lived in the "wilderness of mirrors" for years.
Speakers for this conference include a former deep cover illegal KGB agent, a former CIA Deputy Director, former CIA Intelligence and Special Ops Officers, a former Assistant Secretary of Defense and others.
See bios of these amazing speakers, conference schedule & topics: www.SpiesLiesNukes.com Tickets include breakfasts and lunches, a VIP reception on Friday evening and all speaker presentations and panels.
La Fonda is holding specially priced rooms for our guests until OCTOBER 10 only. Please purchase your tickets and reserve your rooms while they are still available. This historic and elegant venue provides an intimate meeting space that allows for interactions and discussions, but space is limited.
This third, enhanced running of Spies, Lies & Nukes. Join Valerie Plame and some of her legendary, highly decorated, and experienced CIA colleagues as they pull back the curtain on the real life "wilderness of mirrors" that is international espionage.
Hear from and engage with the best of CIA's spies to better understand today's world: from emergent threats, to never-before-told spy operations, black market nuclear scams, how to recruit a spy, the growth of domestic terrorism, how social media is used in espionage, and keeping your employees and your company safe from foreign spies.
Topics: "Soul Catcher: The Metaphysics of Recruiting a Spy" with Jim Lawler, Former Senior CIA Ops Officer
"Delusion and Illusion in Moscow" with Jonna Mendez in conversation with Valerie Plame, Former Covert CIA Ops Officer
"CIA in the Movies" - Panel;
"China: An Emerging Threat" with Mary Beth Long, Former Assistant Secretary of Defense for International Security Affairs
"Inside Putin's Head" with Rolf Mowatt-Larssen, Former Senior CIA Intelligence Officer
"Clarity in Crisis: Leadership Lessons from the CIA" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"Disinformation Distortions: AI, Deep Fakes, and Everything You Always Wanted to Know About Social Media and Espionage" with Alma Katsu, Former Senior CIA and NSA Analyst
"Morality and Ethics in the CIA" with Doug London, Former Senior Officer in the CIA's Clandestine Service
Michael Morell in conversation with Valerie Plame, Former Covert CIA Ops Officer
"Eliminating Players on the Intelligence Battlefield: Havana Syndrome" with Marc Polymeropoulos, Former Senior CIA Ops Officer
"The End of the Global Nuclear Order" with Valerie Plame, Former Covert CIA Ops Officer
Program also includes: Former Senior CIA Deputy Director; Michael J. Morell
FEE: Regular Sale purchase window: Jun 16 - Nov 2, $1300; Late Sale purchase window: Nov 3 - Nov 10, $1450. Special AFIO rate here.
Ticket price does not include accommodations. More about accommodations here
Tickets include breakfasts, lunches, VIP reception and all speaker presentations and activities.
Conference location: Conference Location: La Fonda On the Plaza, 100 E. San Francisco Street, Santa Fe, NM 87501
More information or to register here
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
U.K. Navy ends tradition of Chinese laundrymen on warships over spying fears - The Telegraph, 23 Oct 23
The Navy is ditching its century-old tradition of having Chinese servants on warships amid fears they could be spying. Hundreds of Chinese laundrymen have worked on British ships since the 1930s with most from Hong Kong but will now be replaced by Nepalese Gurkhas. The Sun reported that the Ministry of Defence had made the decision over fears Beijing could obtain secret information by threatening the loved ones of laundrymen. The paper said that three Chinese nationals were barred from joining HMS Queen Elizabeth, the Navy’s flagship aircraft carrier, on her strike group voyage to the contested South China Sea. A fourth Chinese laundryman was dismissed this month after 39 years of washing and pressing sailors’ uniforms and officers’ white tablecloths because his family lives in Hong Kong. The tradition began as a local custom early in the last century and was formalised through contracts with various Hong Kong companies. (Full article here.)
Ex-NSA employee admits trying to sell top-secret information to Russia - Axios, 23 Oct 23
A former National Security Agency employee admitted trying to sell classified national security information to Russia, according to a plea deal Monday. Jareh Sebastian Dalke, 31, of Colorado Springs, pleaded guilty to six counts of attempting to transmit classified National Defense Information to a person he believed to be a Russian agent, but who was actually an undercover FBI employee. The Army veteran admitted that from August to September 2022, "in order to demonstrate both his 'legitimate access and willingness to share,' he used an encrypted email account to transmit excerpts" of three top-secret documents to the undercover employee, per a Department of Justice statement. Dalke was last year paid $16,499 in cryptocurrency for excerpts of National Defense Information (NDI) documents that he shared before offering to sell for $85,000 the rest of the information that was classified as "Top Secret//Sensitive Compartmented Information," according to the plea agreement. (Full article here.)
CIA has spent tens of millions on Ukrainian intelligence agencies - RT citing Washington Post, 23 Oct 23
The CIA has spent “tens of millions” of dollars on transforming Kiev’s Soviet-style spy services into “potent allies against Moscow,” The Washington Post reported on Monday, citing multiple sources in the US and Ukrainian intelligence communities. The US foreign intelligence service has been heavily involved in Ukrainian affairs since at least 2015, according to the report. The agency maintains a “significant presence” in Kiev amid the conflict with Russia. “The agency has provided Ukraine with advanced surveillance systems, trained recruits at sites in Ukraine as well as the United States, built new headquarters for departments in Ukraine’s military intelligence agency,” the report reads. The CIA has been aiding Ukraine’s SBU domestic intelligence service, as well as its military counterpart, the GUR. (Full article here.)
CIA Issued Warnings About Potential Escalated Hamas Attacks On Israel Days Before Strike - Forbes, 13 Oct 23
The Canadian Security Intelligence Service (CSIS) has warned Inuit leaders that foreign adversaries could gain a foothold in Canada by offering to fill infrastructure gaps in the North. But Natan Obed, president of the Inuit Tapiriit Kanatami (ITK) — the nonprofit organization that represents more than 65,000 Inuit across Inuit Nunangat and the rest of Canada — said the spy agency's inability to share classified intelligence with the region's decision-makers leaves them in the dark about the risks. "We are making decisions every day that are currently not as informed as they could be about threats and considerations," Obed recently told CBC News. "The partners that we choose are sometimes not the partners that we hope to have." (Full article here.)
Visiting professor used PhD students to gather intelligence for China, Asio boss alleges - The Guardian, 18 Oct 23
The spy agency Asio says it has disrupted a plot by China’s intelligence services to “infiltrate a prestigious Australian research institution” with officials forcing an academic to leave the country before any harm was done. The Asio chief, Mike Burgess, provided broad details of the alleged plot while also accusing China of engaging in “the most sustained, scaled and sophisticated theft of intellectual property and expertise in human history”. “It is unprecedented and unacceptable,” Burgess said during a press conference in California on Wednesday alongside counterparts from the US, the UK, Canada and New Zealand. The MI5 director general, Ken McCallum, with the FBI’s director, Christopher Wray, in July. US and UK spy chiefs warn Middle East crisis could raise domestic terror threat. Burgess acknowledged that “all nations spy” and “all nations seek strategic advantage” but he said China’s behaviour went “well beyond traditional espionage” and became “a ruthless business model aimed at seizing commercial advantage”. (Full article here.)
Russian ship suspected of espionage spotted off Dutch coast - NL Times, 20 Oct 23
A Russian research ship believed to be used for espionage was sailing along the Dutch coast on Wednesday. This was reported by the investigative journalistic platform Pointer (KRO-NCRV) on Friday. The Yevgeny Gorigledzhan vessel switched off its AIS transmitter shortly after entering the North Sea. The Yevgeny Gorigledzhan is a Russian Navy oceanographic vessel officially designed for bottom surveys and underwater work. However, according to Pointer, the vessel was likely part of a secret Russian military program established during the Cold War called GUGI. (Full article here.)
How Israel underestimated Hamas’s intelligence capabilities – an expert reviews the evidence - The Conversation, 18 Oct 23
Israel has a cutting-edge security technology industry and was (and still should be) considered to be the leading nation for national security. The controversial electronic intelligence platform Pegasus was developed in Israel, and the border between Israel and Gaza was considered – before the October 7 attack – to be a leading example of using sensors and machine learning to reduce the need for human guards while not reducing the strength of the security. But when Hamas fighters descended on the Supernova music festival on October 7, they had used drones to disable Israeli communication towers and remote-controlled machine guns. They also used unexpected tactics to breach the border. These included flooding the Iron Dome air defences with rockets, arriving on hang-gliders and demolishing the border with bulldozers (a likely echo of Israel’s use of bulldozers in occupied territories). (Full article here.)
Brazil police arrest two intel agents for alleged illegal surveillance - Reuters, 20 Oct 23
Brazil's federal police on Friday arrested two intelligence officials from the country's spy agency Abin for allegedly using phone hacking tools without judicial approval. Police said in a statement they had also carried out 25 search and seizure warrants in five states as part of the probe being led by the country's Supreme Court. Brazilian newspapers O Globo and Folha de S.Paulo reported that Abin officials allegedly bought the spying software FirstMile from Israeli firm Cognyte (CGNT.O) and used it to invade targets' phones and geolocate them. (Full article here.)
Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
- MI5 are closing down Iran and China spy networks, says Tom Tugendhat - Great Britain News, 19 Oct 23
- Gujarat ATS nabs spy relaying military intel to Pakistan; Anand resident involved in cyber espionage - Lokmat Times, 20 Oct 23
- China says it uncovered another spying case in US - GDN, 22 Oct 23
- China formally arrests Japanese man for alleged espionage - Nikkei Asia, 19 Oct 23
- American Journalist Detained in Russia Faces Alleged Espionage Charges - Arise News, 19 Oct 23
- Former NSA Director: AI is ‘double-edged sword’ for cybersecurity - The Hill, 17 Oct 23
- The Hidden Perils of Cyber Espionage: PEAPOD and Void Rabisu - Crypto Mode, 18 Oct 23
- Persistent Espionage Campaign Targets APAC Governments - Infosecurity Magazine, 17 Oct 23
- War crimes tribunal says September cyberattack was act of espionage - The Record, 20 Oct 23
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
The Latest from International Spy Museum Historian Andrew Hammond, PhD.
 Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
17 Oct | “The Intelligence Legacy of the Yom Kippur War” – with Uri Bar-Joseph Uri Bar-Joseph joins Andrew Hammond to discuss the intelligence failure of the Yom Kippur War. Uri is an author and professor emeritus at Haifa University.
The Latest Insights from Former CIA Acting Deputy Director for Operations Jack Devine.
 In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
19 Oct | Hamas and Israel are now engaged in both a physical and information war. The catastrophic aftermath of Hamas’s attack on Israel continues, resulting in extensive loss of civilian lives and exceedingly complicated political calculations. Hamas and Israel are now engaged in both a physical and information war, as demonstrated by the response to this week’s al-Ahli hospital explosion in Gaza where multiple social and traditional media mistakenly blamed an Israeli airstrike for the destruction. (Full version available to AFIO members in the coming days here.)
Daily Analysis of Security Issues and Geopolitical Trends
 Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
24 Oct | What Follows Hamas in Gaza?
On October 20, Israeli Minister of Defense Yoav Gallant outlined Israel’s plan for the removal of Hamas from power in the Gaza Strip and for the security and governance of the territory in the immediate aftermath. The third phase of Israel’s plan, according to Gallant - presumably to be enacted after Hamas is ousted from control - is to create a new “security regime” for Gaza. However, neither he nor any other Israeli officials have specified what entities or bodies might ultimately assume control of the area. All Israeli leaders have stated clearly that Israel does not intend to resume an occupation of the territory. Israel ceded control of the Gaza Strip to the Palestinian Authority in 2005, opting to wall the territory off with tight border controls and other defensive security measures. However, the United Nations still considers the territory as Israel-occupied from an international legal point of view. Tel Aviv is responsible for providing utilities to Gaza's residents and controls the borders in and out of the area. Israeli leaders undoubtedly calculate that governing Gaza directly after uprooting Hamas would subject Israel to unending insurgency and unrest, taking Israeli forces and resources away from the other fronts, including the northern border with Lebanon. There, the Israel Defense Forces (IDF) face off with the well-armed Iranian ally, Lebanese Hezbollah. Since the crisis began, Israeli leaders have reportedly stated that the Gaza Strip should ultimately become the “responsibility” of the Arab states, without specifying precisely what a longer-term role of the Arab world in Gaza would look like in practice. Presumably, if an Israeli-Palestinian political solution were reached in which a Palestinian state is formed, the Gaza Strip would become a part of that new state.
23 Oct | Iran’s Role in Mideast Crisis Widens Rift with the West
20 Oct | Xi and Putin Meet Against the Backdrop of Conflict in the Middle East
19 Oct | Hand on the Trigger: Iranian Proxies Threaten to Escalate the Conflict with Israel
18 Oct | Approaching the Abyss: The Humanitarian Crisis in the Gaza Strip
17 Oct | No End in Sight, Hard Questions Ahead for Ukraine and Allies
Analysis of Global Security Events with WTOP National Security Correspondent JJ Green
 Inside the SCIF - 19 Oct - Israel vs. Hamas
Inside the SCIF - 19 Oct - Israel vs. Hamas
 Target USA Podcast - 18 Oct - How did Hamas plot the invasion of Israel?
Target USA Podcast - 18 Oct - How did Hamas plot the invasion of Israel?
The Hunt Broadcast - 18 Oct - The fallout of the Israel-Hamas conflict
The Latest Insights from Jeff Stein and Colleagues in SpyTalk
 21 Oct | The Spies of Hamas - Jeff Stein
21 Oct | The Spies of Hamas - Jeff Stein
There was a time many years ago that I’d drive past a soccer stadium in South Vietnam looking for a chalk scratch on the wall. Horizontal meant that my net of spies had reports for me. Posing as farmers, rice peddlers and the like, my spies eyeballed and engaged communist soldiers and units and reported back the essentials: names, numbers, weapons, uniforms, morale and so forth. This was old-timey military espionage for sure, a legacy of the OSS and its allied spy services in World War Two, who depended on agents in the French underground and elsewhere to track and subvert the Nazis. By the end of the century, though, advances in technology had eclipsed much of battlefield HUMINT, as human-based spying efforts are called. In the wars in Iraq and Afghanistan, U.S. field commanders increasingly came to favor electronic intercepts and “overhead”—eavesdropping spy planes, satellites and eventually drones—to locate the enemy and suss out its plans. HUMINT was just too hard, too time-consuming and too unreliable against the likes of Al Qaeda, ISIS and the Taliban. Better to just trace the insurgents’ cell phone calls. (Full article here.)
19 Oct | Israel Conflict Challenges U.S. Intelligence - Jonathan Broder
Veteran former CIA analysts well remember the hours and days they spent urgently scrambling to determine exactly who carried out the Sept. 11, 2001 attacks. Like their CIA brothers and sisters assessing the horrific events in Israel and Gaza today, they knew broadly who was responsible, but needed to come up with unequivocal proof of who did it. Nothing short of the political map of the Middle East, and the U.S. role in the region, was at stake. Today’s Hamas-Israel conflict poses similar existential questions. “It’s really daunting,” former CIA analyst Gail Helt says, describing the atmosphere inside the analysis directorate when major events like the 9/11 attack and this month’s surprise Hamas invasion of Israel, followed by the troubling strike on a Gaza hospital, erupt. (Full article here.)
Section III - MEMBER CONTRIBUTIONS
Article: How the CIA’s top-ranking woman beat the agency’s men at their own game - Washington Post, 21 Oct 23
In the early history of the CIA, marked by towering male figures like Allen Dulles, William Colby and William “Wild Bill” Donovan, few careers proved more remarkable — and unlikely — than that of a Southern blue blood named Eloise Randolph Page. Page anticipated the launch of Sputnik when just about everyone else was taken by surprise. She was the top female officer in the CIA’s clandestine service in the 1960s and 70s and the first woman to head a major overseas station. She was physically tiny but larger-than-life, reactionary but visionary, snobby but able to overcome patriarchal provincialism to wield unheard-of influence, at a time when the agency’s sexist culture ensured most women’s career tracks were limited to secretarial and clerk roles. Born in 1920, Page began her intelligence career during World War II as a secretary at the Office of Strategic Services, the CIA’s precursor. She was assigned to Donovan, the OSS chief, who liked to recruit from highborn families and must have been delighted that “Eloise,” as everybody called her, came from not only one such family, but two. The Randolphs and the Pages were two of Virginia’s oldest White families, with roots that went back to the origins of the commonwealth, and to slavery. “She was a classy woman,” as one female officer put it, “who belonged somewhere on a plantation.” (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: How Hamas Caught U.S. and Israeli Intelligence Unaware - Wall Street Journal, 19 Oct 23
Hamas’s attack on Israel should be a wake-up call to U.S. intelligence services. That a terrorist attack of this magnitude—with seismic implications for global security—came as a surprise to many in Washington shows that we need to reassess our own operations sharply to ensure that America has a comprehensive threat picture that can provide early warnings and prevent national-security tragedies. The Israelis will no doubt examine this lapse thoroughly. Several possible reasons come to mind for why Israel and its allies, including the U.S., failed to report on the exact nature, timing and scale of the attack. Disinformation could have played a role in diluting Israeli intelligence. Hamas has years of experience with Israel’s intelligence methods and strategic priorities, giving the terrorists the know-how to feed Israeli operatives false information. Over the past two years, Israel had seemingly developed a working relationship with Hamas on issues like humanitarian-aid deliveries and work permits for Gaza residents. That would have given Hamas operatives opportunities to communicate regularly with Israelis and perhaps gain the Israelis’ trust by sharing accurate information on other threats from Gaza—lending credibility to Hamas’s deceptions about its own plans. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: The CIA dropped the ball here': Hacker hijacked the CIA's secure contact link for Russian informants due to Twitter flaw - The Daily Mail, 19 Oct 23
An American hacker was able to use a glitch on the CIA's X account (formerly known as Twitter) to direct potential informants to his own Telegram channel. The link on the CIA's Twitter channel offers informants ways to covertly contact the agency - and large amounts of the text is in Russian, to enable people within the country to contact the CIA. Kevin McSheehan, 37, said that he noticed that the Telegram link on the X page could be hijacked, and redirected it to his own channel to prevent hostile nations exploiting the link. McSheehan, who describes himself as a 'pro-CIA patriot' told the BBC, 'My immediate thought was panic. 'I saw that the official Telegram link they were sharing could be hijacked - and my biggest fear was that a country like Russia, China, or North Korea could easily intercept Western intelligence. 'The CIA really dropped the ball here.' (Read full report here.)
Article: Spy vs. spy: How Israelis tried to stop Russia’s information war in Africa - Washington Post, 21 Oct 23
When Israeli businessmen Royi Burstien and Lior Chorev touched down in the busy capital of the West African nation of Burkina Faso, they had an urgent message for the country’s embattled ruler. The Israelis — one a veteran political operative and the other a former army intelligence officer — had been hired with the mission of keeping the government of President Roch Marc Kaboré in power. Their company, Percepto International, was a pioneer in what’s known as the disinformation-for-hire business. They were skilled in deceptive tricks of social media, reeling people into an online world comprised of fake journalists, news outlets and everyday citizens whose posts were intended to bolster support for Kaboré’s government and undercut its critics. But as Percepto began to survey the online landscape across Burkina Faso and the surrounding French-speaking Sahel region of Africa in 2021, they quickly saw that the local political adversaries and Islamic extremists they had been hired to combat were not Kaboré’s biggest adversary. The real threat, they concluded, came from Russia, which was running what appeared to be a wide-ranging disinformation campaign aimed at destabilizing Burkina Faso and other democratically-elected governments on its borders. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: Allied Spy Chiefs Warn of Chinese Espionage Targeting Tech Firms - New York Times, 18 Oct 23
The United States and its allies vowed this week to do more to counter Chinese theft of technology, warning at an unusual gathering of intelligence leaders that Beijing’s espionage is increasingly trained not on the hulking federal buildings of Washington but the shiny office complexes of Silicon Valley. The intelligence chiefs sought to engage private industry in combating what one official called an “unprecedented threat” on Tuesday as they discussed how to better protect new technologies and help Western countries keep their edge over China. The choice of meeting venue — Stanford University, in Silicon Valley — was strategic. While Washington is often considered the key espionage battleground in the United States, F.B.I. officials estimate that more than half of Chinese espionage focused on stealing American technology takes place in the Bay Area. It was the first time the heads of the F.B.I. and Britain’s MI5 and their counterparts from Australia, Canada and New Zealand had gathered for a public discussion of intelligence threats. It was, in effect, a summit of the spy hunters, the counterintelligence agencies whose job it is to detect and stop efforts by China to steal allied secrets. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: The Clever Cameras Used by the East German Stasi to Spy on Citizens - Petapixel, 16 Oct 23
East Germany, or the German Democratic Republic (GDR), was one of the most tightly-controlled police states in recent memory from 1949 to 1990 that would spy on its own citizens throughout using all sorts of fascinating imaging equipment. The Ministry for State Security, better known as the Stasi by its German acronym, was a fierce and shadowy secret police intent on keeping the Socialist Unity Party (SED) in power as a one-party communist state during the Cold War. In January 1990, only two months after the fall of the Berlin Wall, protesters stormed Stasi headquarters in East Berlin in an attempt to stop its agents from destroying documents and force both East and West Germany to make them fully accessible to citizens upon reunification. Ever since, the building has been a museum chronicling and documenting just how the GDR became such a police state and how the Stasi enforced the party line. To this day, citizens can make appointments to come in and see files kept on them, learning everything about why they were under suspicion — and who informed on them. (Read full report here.)
Article: Behind a Senator’s Indictments, a Foreign Spy Service Works Washington - New York Times, 13 Oct 23
“What else can the love of my life do for you?” asked Nadine Arslanian, the girlfriend of Senator Robert Menendez. She posed the question at a cozy dinner at a steakhouse in May 2019 attended by Gen. Ahmed Helmy, Egypt’s top spy in Washington. The discussion was revealed in a federal indictment on Thursday. As General Helmy would come to find out, even if Ms. Arslanian and her soon-to-be husband were not always able to deliver what Egypt wanted, they at least seemed to try very hard. The indictment charged Mr. Menendez, Democrat of New Jersey, and his now wife with conspiring to act as agents of the Egyptian government. The document, in addition to another indictment made public last month, paint an unseemly picture of how the couple advanced Egyptian interests on numerous fronts. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: Wi-Fi that Can Read Through Walls - Tech Briefs, 28 Sep 23
Researchers in UC Santa Barbara Professor Yasamin Mostofi’s lab have proposed a new foundation that can enable high-quality imaging of still objects with only Wi-Fi signals. Their method uses the Geometrical Theory of Diffraction and the corresponding Keller cones to trace edges of the objects. The technique — which appeared in the Proceedings of the 2023 IEEE National Conference on Radar (RadarConf) — has also enabled, for the first time, imaging, or reading, the English alphabet through walls with Wi-Fi, a task once deemed too difficult for Wi-Fi due to the complex details of the letters. “Imaging still scenery with Wi-Fi is considerably challenging due to the lack of motion,” said Mostofi. “We have then taken a completely different approach to tackle this challenging problem by focusing on tracing the edges of the objects instead.” This innovation builds on previous work in the Mostofi Lab, which since 2009 has pioneered sensing with everyday radio frequency signals such as WiFi for several different applications, including crowd analytics, person identification, smart health, and smart spaces. (Read full report here.)
Article: A surprising number of celebrities have worked as spies - Washington Post, 22 Oct 23
During World War II, Josephine Baker regularly attended parties at embassies and consulates in occupied France, where she would flirt with high-ranking Nazi officials. Because of her celebrity as a dancer, actor and singer, the German men would swoon over her — and sometimes begin to divulge military secrets after being plied with alcohol. Baker would later jot down notes and hide them where she hoped no one would find them: in her underwear. In her 1977 autobiography “Josephine,” she wrote how those secrets were “snugly in place, secured by a safety pin,” so they could be carried past checkpoints and delivered to the French Resistance. The American-born performer was one of surprisingly large number of celebrities involved in espionage during the 20th century, including escape artist Harry Houdini, baseball catcher Moe Berg, movie actress Marlene Dietrich, spy novelist Ian Fleming, chef Julia Child and Hollywood heartthrob Cary Grant. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Article: Ukrainian spies with deep ties to CIA wage shadow war against Russia - Washington Post, 23 Oct 23
The cluttered car carrying a mother and her 12-year-old daughter seemed barely worth the attention of Russian security officials as it approached a border checkpoint. But the least conspicuous piece of luggage — a crate for a cat — was part of an elaborate, lethal plot. Ukrainian operatives had installed a hidden compartment in the pet carrier, according to security officials with knowledge of the operation, and used it to conceal components of a bomb. Four weeks later, the device detonated just outside Moscow in an SUV being driven by the daughter of a Russian nationalist who had urged his country to “kill, kill, kill” Ukrainians, an explosion signaling that the heart of Russia would not be spared the carnage of war. The operation was orchestrated by Ukraine’s domestic security service, the SBU, according to officials who provided details, including the use of the pet crate, that have not been previously disclosed. The August 2022 attack is part of a raging shadow war in which Ukraine’s spy services have also twice bombed the bridge connecting Russia to occupied Crimea, piloted drones into the roof of the Kremlin and blown holes in the hulls of Russian naval vessels in the Black Sea. (Read full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Section IV - DEEPER DIVES, OPINION, ANALYSIS, FILM, HISTORY, POP CULTURE
Building Trust to Enhance Elicitation - International Journal of Intelligence and Counterintelligence, 17 Oct 2023
Drawing on the scientific literature on trust and the experiences of distinguished interviewers, two primary trust-building tactics with potential application in investigative and intelligence interviewing were identified and assessed for their efficacy in this context. Trust-building tactics that demonstrate trustworthiness and demonstrate a willingness to trust portray the interviewer as reliable and dependable (i.e., perceptions of cognitive trust) as well as convey goodwill and warmth (i.e., perceptions of affective trust) were viewed as likely to increase a source’s willingness to disclose critical information. Across three experiments, both tactics were found to be influential in engaging the reciprocity principle in a manner that elicited the sources’ cooperation and enhanced information yield. However, perceptions of cognitive trust were found to function as a direct encouragement to reveal information. In contrast, perceptions of affective trust first facilitated a willingness to cooperate that had the potential for subsequently manifesting as an instrumental form of cooperation. Intelligence has been called “the second oldest profession.” There is a certain irony, then, when intelligence officers routinely ask a recruited source to “trust me,” as such a request means trust me with your safety, trust me to protect your family, even trust me with your life. Nonetheless, accomplished interviewers view the challenge of earning a source’s trust to be of vital importance to eliciting intelligence information. Across the spectrum of human intelligence—from agent handling to interrogation—case studies of successful operators highlight the fact that time and effort in building trust can facilitate intelligence elicitation. This article builds on the theoretical literature on trust and the experiences of distinguished interviewers to describe the role of trust building in mitigating resistance. Central to the discussion are two trust-building tactics—demonstrating trustworthiness and demonstrating a willingness to trust—that can be leveraged to encourage cooperation in an operational context. The next step was to evaluate the efficacy of these proposed trust-building tactics via three experiments and explore the application of these tactics in investigative and intelligence elicitation contexts. (Full report here.)
State Department cipher machines and communications security in the early Cold War, 1944–1965 - Intelligence and National Security, 17 Oct 23
From 1944 the State Department attempted to improve its communications security by creating a Division of Cryptography and mechanising the encryption process. This article assesses the effectiveness of these reforms and shows that State’s new cipher equipment had cryptographic vulnerabilities. Moreover, the department was unable to maintain physical security at the Moscow embassy and through espionage and technical surveillance the KGB broke the ciphers and read American communications. The paper concludes by analysing the impact of this security failure, including the claim that intercepted messages influenced Stalin’s decision to approve the North Korean invasion of South Korea in 1950. It has been well established that in the first four decades of the 20th century the State Department struggled to keep its correspondence secret. David Kahn and Christopher Andrew have shown that the department had weak codes and feeble physical and personnel security. Communications security appeared not to be a priority for the department; Daniel Larsen recently examined cultural attitudes towards secrecy and diplomacy in the State Department during the Wilson administration and found that at the start of the First World War State exhibited ‘virtually no concern for the quality of its codes or the confidentiality of its communications’. The United States was in effect conducting open diplomacy, with other great powers like Russia, France and Britain able to read American diplomatic telegrams. Even in the inter-war period, State Department cryptography was small scale and inert. The head of the Division of Communications and Records was responsible for creating and maintaining all of State’s cryptographic systems, and codes and ciphers were updated or replaced very infrequently. What has not been studied is whether State Department communications security noticeably improved with the coming of the Cold War. This lack of attention is probably due to the difficulty of accessing sources since many of the relevant documents of the State Department and the National Security Agency (NSA) are still classified, making research on the post-1945 period challenging. However, some of the secrecy was lifted in 2015 when the NSA released over 50,000 pages of official documents formerly held by the American cryptologist William Friedman.Footnote4 There remain gaps in the historical record but with this material it is possible for the first time to trace the development of State Department communications security in the early Cold War. So drawing on the Friedman archive, as well as other sources, this article will assess how effectively the State Department protected its communications between 1944 and 1965. It will show that the department made a concerted effort to break with the past and improve security by creating a Division of Cryptography and bringing into service a series of electro-mechanical cipher machines. The article will then evaluate the vulnerabilities of the new cipher equipment and examine the threat to their physical security from Soviet espionage and technical surveillance. The paper will conclude by discussing whether failings in State Department security benefitted the Soviet Union and affected Soviet decision-making towards Korea in 1950. (Full report here.)
Hoover Institution: FBI Director Wray and 'Five Eyes' counterparts discuss threats in first joint appearance (67 mins) - PBS, 17 Oct 23
Former National Security Advisor Condoleeza Rice moderates a discussion on current espionage threats from China and other actors in the first-ever public appearance of representatives of all Five Eyes partners in a public forum. (Watch here.)
What we know about Beijing’s spies - The Spectator, 18 Oct 23
Two years ago, Richard Moore, head of MI6, said that China was now the organisation’s ‘single greatest priority’. Parliamentarians and the British public have been starkly reminded of this by last week’s news that a parliamentary researcher had been arrested on suspicion of spying for China. On this episode, we won’t be commenting on the ins and outs of that case, but talking more generally about Chinese espionage. What forms does it take, what are its goals and how successful are the Chinese secret services at achieving those? I’m joined by a brilliant and knowledgeable guest. Nigel Inkster is the former director of operations and intelligence for MI6. He has served in Beijing and Hong Kong, and is now the senior adviser on cyber security and China at the think tank IISS. (Full report here.)
Even War Has Rules, So Why No Rules for Espionage? - Homeland Security Newswire, 21 Oct 23
There are even rules for war, which is why it makes little sense that there are none for espionage during times of peace. That was the central issue explored by Asaf Lubin, faculty affiliate at Berkman Klein Center for Internet & Society, during a talk at Harvard Law School about his forthcoming book The International Law of Intelligence: The World of Spycraft and the Law of Nations. “Cicero said that in times of war, the law falls silent,” said Lubin, who is an associate professor of law at Indiana University’s Maurer School of Law in Bloomington. “But war has been regulated. You might be unhappy with the international humanitarian law, the laws of war for good reasons, and yet at least there’s a framework for war. The idea that we cannot fathom regulation of a particular field doesn’t hold true in this day and age.” Organized by the Harvard International Law Journal and the Harvard National Security & Law Association, Lubin’s talk explored the contemporary legal framework that governs peacetime intelligence operations and the ways in which espionage remains in “a legal penumbra,” in the words of legal scholar Simon Chesterman. (Full report here.)
How Israel’s Spies Failed—and Why Escalation Could Be Catastrophic - Foreign Policy, 19 Oct 23
The trauma that Israel suffered on Oct. 7 is both unprecedented and unthinkable by any Israeli historical measure. Never before has Israel experienced such a calamity in its 75-year history. Even Hamas never expected such operational success. Indeed, actors across the region, notably Hezbollah and Iran, were stunned by the success of the Hamas offensive. (Full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Curbing the threats to encryption - Australian Strategic Policy Institute, 23 Oct 23
Government efforts to access private communications are nothing new. In decades past, such attempts at prying were often justified on national-security grounds. Today, however, policymakers point to child safety and disinformation as reasons to limit privacy protections. Established democracies are often leading this charge, inadvertently paving the way for the world’s autocrats. But people around the world aren’t taking these policies lying down. They speak out, using events like Global Encryption Day to highlight the importance of privacy and security not just for their own lives but for their communities and societies. And as vociferous opposition continues to stymie government efforts to expand surveillance powers, it’s become clear that public pressure works. Encryption, which scrambles digital data so that it can be read only by someone with the means to decode it, has become ubiquitous because it keeps information confidential and secure while authenticating the identity of the person with whom one is communicating. Today, billions of people use encryption to send digital messages and emails, transfer money, load websites and protect their data. The gold standard in security is end-to-end encryption (E2EE), since only the participants have access to the data—not even the service provider can decipher it. (Full report here.)
How the Chinese Communist Party Uses Cyber Espionage to Undermine the American Economy - Center for Strategic and International Studies, 19 Oct 23
The United States is locked in a long-term competition with the Chinese Communist Party (CCP). Even though that competition need not turn to conflict, it will almost certainly continue to see a network of operatives linked to the CCP wage a systematic cyber espionage campaign designed to gain an intelligence advantage and steal intellectual property. Put simply, China is trying to cheat its way to the top of key industries in the 21st century. Their quest to achieve dominance in artificial intelligence and machine learning (AI/ML) is unlikely to be any different. Let’s start with the facts. According to the Dyadic Cyber Incident and Campaign Dataset (DCID), the People’s Republic of China is the world’s most egregious actor in terms of cyber espionage targeting private firms and linked to stealing intellectual property. Since 2000, China has been associated with 90 cyber espionage campaigns, 30% more than Russia. The actual number is likely higher and each instance sees multiple businesses targeted that overlap priority industries specified in the CCP’s “Made in China 2025” plan. In other words, hackers work for communist technocrats in modern China. And, as seen in numerous cases these cyber operations work alongside clandestine human intelligence networks to steal trade secrets from U.S. firms. These multifaceted campaigns have the potential to offset any advantages artificial intelligence brings to cyber defenses, a reality on display in the recent discovery of malware in U.S. critical infrastructure. (Full report here.)
The Rise of the New Spycraft Regimes - Foreign Policy, 21 Oct 23
The world of global espionage has traditionally been dominated by the big powers—Russia, China, the United States, France, and Britain. But a series of recent revelations are a reminder that the intelligence services of middle powers—particularly those of the so-called global south—are not only active in the West, but also likely expanding the scope and ambition of their activities. The ramifications of these activities could rival any major power spy scandal. The states are smaller, but the stakes are not. (Full report here.) (NOTE: This material may require a one time free subscription or sit behind a paywall.)
Visualized: Which Countries are Dominating Space - Visual Capitalist, 08 Jul 22
Believe it or not, there is a lot of stuff in space. In fact, our atmosphere is filled with more than 11,000 objects that have been launched since the foray into space began. The Space Race started during the Cold War, and early on the Soviet Union dominated when it came to the amount of devices and objects launched into our atmosphere. But a few years ago, the U.S. took back that title with Elon Musk’s SpaceX helping lead the charge. This visual, using data from Our World in Data, breaks down the amount of objects launched into space by country over time. here.)
Intelligence in History - A Collection of Recent Content
- The Strange Case of a Nazi Who Became an Israeli Hitman - Haaretz, 11 Oct 23
- World’s Biggest Espionage? Russia Celebrates 110th Anniversary Of ‘Agent’ Who Played A Key Role In Stealing Nuke Tech - Eurasian Times, 18 Oct 23
- On This Day — Richard Sorge “The spy who changed the world” is arrested in Tokyo (October 18, 1941) - Intel Today, 18 Oct 23
True Intelligence Matters in Film - The Impossible Spy - Jim Goddard (1987)
 The true story of an Israeli civilian who was recruited into Israel's Secret Intelligence Agency to become a spy in Damascus, where he spent years infiltrating the Syrian political establishment. Israel's national hero, Eli Cohen, successfully entered the upper echelons of the Syrian government as a double-agent. The secrets he obtained became crucial in Israel's victory in the 1967 Six Day War.
The true story of an Israeli civilian who was recruited into Israel's Secret Intelligence Agency to become a spy in Damascus, where he spent years infiltrating the Syrian political establishment. Israel's national hero, Eli Cohen, successfully entered the upper echelons of the Syrian government as a double-agent. The secrets he obtained became crucial in Israel's victory in the 1967 Six Day War.
More information about this based-on-true-events production here.
Walking Tours - Washington, DC - Sundays (Dates/Times Vary)
Former intelligence officers guide visitors on two morning and afternoon espionage-themed walking tours: "Spies of Embassy Row" and "Spies of Georgetown." For more information and booking, click here or contact rosanna@spyher.co
Section V - Books, Research Requests, Employment, Obituaries
Books — Forthcoming, Newly Released, Overlooked
 The Sisterhood: The Secret History of Women at the CIA
The Sisterhood: The Secret History of Women at the CIA
by Liza Mundy
(Crown, 17 Oct 23)
Created in the aftermath of World War II, the Central Intelligence Agency relied on women even as it attempted to channel their talents and keep them down. Women sent cables, made dead drops, and maintained the agency’s secrets. Despite discrimination—even because of it—women who started as clerks, secretaries, or unpaid spouses rose to become some of the CIA’s shrewdest operatives. They were unlikely spies—and that’s exactly what made them perfect for the role. Because women were seen as unimportant, pioneering female intelligence officers moved unnoticed around Bonn, Geneva, and Moscow, stealing secrets from under the noses of their KGB adversaries. Back at headquarters, women built the CIA’s critical archives—first by hand, then by computer. And they noticed things that the men at the top didn’t see. As the CIA faced an identity crisis after the Cold War, it was a close-knit network of female analysts who spotted the rising threat of al-Qaeda—though their warnings were repeatedly brushed aside. After the 9/11 attacks, more women joined the agency as a new job, targeter, came to prominence. They showed that data analysis would be crucial to the post-9/11 national security landscape—an effort that culminated spectacularly in the CIA’s successful effort to track down bin Laden in his Pakistani compound. Propelled by the same meticulous reporting and vivid storytelling that infused Code Girls, The Sisterhood offers a riveting new perspective on history, revealing how women at the CIA ushered in the modern intelligence age, and how their silencing made the world more dangerous.
Order book here.
 Marianne Is Watching: Intelligence, Counterintelligence, and the Origins of the French Surveillance State
Marianne Is Watching: Intelligence, Counterintelligence, and the Origins of the French Surveillance State
by Deborah Bauer
(University of Nebraska Press, 01 Dec 21)
Professional intelligence became a permanent feature of the French state as a result of the army’s June 8, 1871, reorganization following France’s defeat in the Franco-Prussian War. Intelligence practices developed at the end of the nineteenth century without direction or oversight from elected officials, and yet the information gathered had a profound influence on the French population and on pre–World War I Europe more broadly. In Marianne Is Watching Deborah Bauer examines the history of French espionage and counterespionage services in the era of their professionalization, arguing that the expansion of surveillance practices reflects a change in understandings of how best to protect the nation. By leading readers through the processes and outcomes of professionalizing intelligence in three parts—covering the creation of permanent intelligence organizations within the state; the practice of intelligence; and the place of intelligence in the public sphere—Bauer fuses traditional state-focused history with social and cultural analysis to provide a modern understanding of intelligence and its role in both state formation and cultural change. With this first English-language book-length treatment of the history of French intelligence services in the era of their inception, Bauer provides a penetrating study not just of the security establishment in pre–World War I France but of the diverse social climate it nurtured and on which it fed.
Order book here.
 Soldiers, Spies, and Statesmen: Egypt's Road to Revolt
Soldiers, Spies, and Statesmen: Egypt's Road to Revolt
by Hazem Kandil
(Verso, 13 Nov 12)
Revolutions are difficult to understand and almost impossible to predict. Egypt’s 2011 revolt was no exception. The military’s abandonment of Mubarak—a turning point for the revolt—confounded many observers, who assumed that the leader and the generals stood or fell together. The officers, it was thought, ruled from behind the scenes and simply swapped the figures in the spotlight to preserve the status quo. In a challenge to this conventional view, Hazem Kandil presents the revolution as the latest episode in an ongoing power struggle between the three components of Egypt’s authoritarian regime: the military, the security services, and the political apparatus. A detailed study of the interactions within this invidious triangle over six decades of war, conspiracy, and sociopolitical transformation, Soldiers, Spies, and Statesmen is the first systematic analysis of how Egypt metamorphosed from a military into a police state—and what that means for the future of its revolution.
Order book here.
Research Requests and Academic Opportunities
Call for Information: Author drafting a book on the Clinton administration seeks contact with the person who served as COS Manila in November 1996 for the purpose of background research. Members who can identify the COS and/or are in contact with him, please forward this request to the COS or contact the author. Responses may be sent to dpluchinsky@rocketmail.com.
Call for Information: Seeking information on, Sgt Major Charles “Chuck” Remagen, assigned to MACV/SOG in Vietnam 67-68. Seek details about his role as a Sgt Major with MACV “Studies and Observations Group in Vietnam 7/1/67 to 1/21/68. Responses may be sent to magen@hotmail.com.
Call for Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
The Washington Post is developing a multi-part audio documentary series (i.e. podcast) chronicling the Grenadian revolution and the US intervention in 1983. They've interviewed nearly 100 people so far, ranging from the heads of state, former Grenadian officials, current and former US officials, veterans, and intelligence officers. They're looking for people who served at the time and may be knowledgeable about intelligence activities in Grenada and the southern Caribbean between 1979 and Operation Urgent Fury. They would also be interested in speaking with anyone who knew Leonard Barrett during the same period. If anyone is interested in participating, please reach out to Washington Post reporter Ted Muldoon via email at ted.muldoon@washpost.com or on Signal at 651-497-5449.
Call For Articles: AFIO Journal, The Intelligencer
AFIO is seeking authors for its section on "When Intelligence Made a Difference" in the semi-annual Intelligencer journal. Topics of interest for which we are seeking authors include:
• The Richard Sorge espionage ring in Tokyo in World War II and
the impact of his intelligence on Stalin and the battle for Moscow.
• How Rommel’s Afrika Korps used SIGINT against the British in
World War II.
• How A.Q. Khan’s nuclear proliferation efforts were uncovered
and stopped.
• The breaking of the Nazi U-boat SHARK encryption system.
• How US intelligence found Usama Bin Laden in Abbottobad, Pakistan.
• How allied SIGINT isolated the Afrika Korps from its logistics chain.
• How US intelligence discovered the Soviet’s high speed Shkval torpedo.
• Intelligence and the rescue of Scott O’Grady.
• Other topics are also welcome.
Interested authors please contact Peter Oleson, senior editor The Intelligencer, at peter.oleson@afio.com
Jobs
Adjunct Faculty - MS in Intelligence Analysis - Johns Hopkins University - Maryland
The Advanced Academic Programs (AAP) division of the Krieger School of Arts and Sciences seeks non-tenure-track adjunct faculty to teach 473.665 Human Intelligence Operations within the MS in Intelligence Analysis program. The course will be taught fully online/asynchronously beginning Spring 2024. Candidates with online course development and teaching experience and those with experience teaching and engaging students from diverse backgrounds are of particular interest.
Additional information on qualifications and application instructions here.
Assistant/Associate Professor of Intelligence Studies (Global Security and Intelligence Studies) - Embry-Riddle Aeronautical University - Prescott, Arizona
Embry-Riddle Aeronautical University's Prescott, Arizona campus is accepting applications for a tenure-track assistant or associate-level professor of intelligence studies to teach intelligence courses to students in the Global Security and Intelligence program. The successful candidate will teach students about the intelligence community, strategic intelligence, the intelligence cycle and intelligence analysis, writing, and briefing. Prior experience working in the intelligence community is strongly preferred. We are interested in candidates with teaching acumen in intelligence analysis and writing using structured analytical techniques.
Additional information and application here.
Obituaries
![]() Bob Martin — Decorated Military Detailee to the IC
Bob Martin — Decorated Military Detailee to the IC
Lt Colonel Robert F. Martin (Bob), 78, of Virginia Beach, died peacefully at home on April 20, 2023 after a lengthy illness. He was born in Arizona. Bob's early years were spent moving 26 times from base to base with his military family, to wherever his father was stationed at the time, including time spent in Australia, North Carolina, New York and Hawaii. After graduating high school he enlisted in the United States Army where he served our country for 20 years, including two tours of duty in Vietnam as a pilot. Bob's distinguished career of military, and government service included Infantry, Armor, Cavalry, Aviation and Special Operations units. He spent his last five years of active duty as the Army's Counterterrorist Staff Officer with a two year detail to a national level intelligence agency conducting operations in Latin America, Africa and the Middle East. His dedicated service was recognized through many medals and awards, including six awards for valor and thirty three awards for service to the United States and foreign governments. Among them were the Legion of Merit, National Defense Service Medal, Republic of Vietnam Campaign Medal, Vietnamese Service Medal, Vietnamese Cross of Gallantry, Air Medal, Army Commendation Medal, Distinguished Flying Cross, Republic of Vietnam Gallantry Cross Unit Citation. He valued education, and was an avid reader. He had a vast knowledge of military history. He graduated from Embry-Riddle Aeronautical University with a degree in Aviation Management. He then graduated from the US Army Command and General Staff College and received his MBA from Indiana University.
![]() Marty Faga —Former NRO Director, President of MITRE, and AFIO Vice Chairman
Marty Faga —Former NRO Director, President of MITRE, and AFIO Vice Chairman
Martin C. Faga of Falls Church, VA passed away on Oct. 19, 2023 due to heart failure, surrounded by his loving family. He was 82 years old. Marty was born and raised in Bethlehem, PA. He received Bachelor’s and Master’s degrees in Electrical Engineering from Lehigh University and received a commission as a Second Lieutenant in the United States Air Force. He spent six years as a Research and Development officer in the Air Force, after which he worked for the CIA for several years. In 1976, he joined the staff of the House Permanent Select Committee on Intelligence, rising to become the Staff Director. In 1989, he was appointed by President George H.W. Bush as Assistant Secretary of the Air Force and Director of the National Reconnaissance Office; he served in that role until 1993. During this time, he led the NRO through the First Gulf War and the de-classification of the existence of the NRO. Following retirement from government service in 1993, he joined MITRE Corporation as a Vice President, rising to be the President and CEO. He retired from MITRE in 2006. He remained on MITRE’s Board of Directors, and served on numerous other boards and commissions. After many years of service to AFIO on its board, including as Vice Chairman, he was appointed Vice Chairman Emeritus.
26 October 2023, 7:30 pm - Pasadena, CA - AFIO Los Angeles hosts AFIO National Board Member Everette Jordan, former Deputy Assistant of the Treasury for IC Integration and National Intelligence Manager for Economic Security and Threat Finance for the DNI. The chapter has an upcoming event with AFIO Board Member Everette Jordan on Oct. 26th. This will be a meet and greet event and will take place out in Pasadena at 7.30 PM at the El Cholo Cafe, 300 E Colorado Blvd Suite 214, Pasadena, CA 91101. Everette Jordan had an impressive 45-year career in service to the Departments of Defense, The Treasury, and the Army. Part of his service included leadership and staff assignments with IC partners and Capitol Hill. His more recent leadership roles were as the Deputy Assistant of the Treasury for IC Integration and National Intelligence Manager for Economic Security and Threat Finance for the DNI.
Please mark your calendar if you are able to attend. Look forward to you seeing you!
Questions to Vincent Autiero, Chapter President, AFIO-Los Angeles Chapter, 5651 W Manchester Ave, Los Angeles, CA 90045
27 October 2023 (Friday), 3 p.m. - Naples, FL - The new Southwest FL (Naples, Fort Myers) AFIO Chapter Business and Speaker Meeting
This AFIO Southwest Florida business and speaker meeting takes place at the Hawthorn Suites which is located at 3557 Pine RIdge Road in Naples, FL. Attendees are urged to be on time as there will be a number of presentations.
The meeting runs approximately 2 hours.
The business portion of the meeting kicks off from 3pm to 3:30 pm.
That will be followed by two outstanding speakers who will discuss terrorist activities/countermeasures/intelligence relating to air travel. One speaker will discuss the technical area of "which wire to cut."
Photos or recordings are not allowed.
Location: Hawthorn Suites Meeting Room, 3557 Pine Ridge Road, Naples FL 34109
Registration or Questions to Hugo Harmatz at lawyur@aol.com.
9 November 2023 (Thursday), 11:00 a.m. PST - Las Vegas, NV - Las Vegas Chapter Meeting features Amir Eden, Friends of The Israeli Defense Forces (IDF), Director of Nevada, and Colorado Chapters, discussing situation in Mideast. The AFIO Las Vegas Chapter meeting features Amir Eden, Friends of The Israeli Defense Forces (IDF), Director of Nevada, and Colorado Chapters. Given current world events we are fortunate to have this special speaker lined up that I’m sure you will enjoy. The event will be held at Charlie’s Lakeside Bar and Restaurant, 8603 W Sahara Ave, Las Vegas, NV 89117.
Qs and RSVPs to Linda Cohn at 702-239-1370 or by email if you have any questions. Early RSVPs are also appreciated. See you in November.
9 November 2023 (Thursday), 11:30 a.m. PST, - San Francisco, CA - AFIO San Francisco Chapter meeting features Ricky Deutsch on "Spies in the Sky: HEXAGON -- A History of the Last Film-Based Satellite."
Location: Basque Cultural Center, 599 Railroad Avenue, South San Francisco. Time: 11:30am no host cocktails; 12 noon (Pacific) meeting start
RSVP here at Event Registration Link. Pre-registration required.
Questions to Mariko Kawaguchi, PO Box 117578, Burlingame, CA 94011, afiosf@aol.com
11 November 2023 (Saturday), 11:30 a.m. EDT, - Indiatlantic, FL - The AFIO Florida Satellite Chapter hears from Col Susie Dabrowski USAF (Ret) on "High-Impact Operations."
Colonel Susie Dabrowski served over 26 years in the U.S. Air Force. Her career included positions in space and nuclear high-impact operations. She served in Pacific and European theaters and five Joint Commands. Upon retirement, she served as a Program Manager in the defense industry. She is currently the Vice President, Southeast Region, Space Force Association.
Location: Doubletree Hotel, Rt A1A, Indialantic, Florida. The sit-down lunch cost is $35.00 per person
RSVPs or Qs to Larry Sanford, President or call 978-502-3328.
See the AFIO Calendar of Events for scheduling further in the future.
Events from Advertisers, Corporate Sponsors, Others
26 Oct 23, 1200-1300 (ET), - Inside Intelligence presents the Foundations of American Intelligence - Virtual - Johns Hopkins University
Join host Michael Ard for a conversation with Mark Stout, former director of the MA in Global Security Studies, on the Foundations of American Intelligence. Mark Stout has taught in Advanced Academic Programs since 2007. From 2013 to 2021 he was the director of the Master of Arts in Global Security Studies and he directed the post-Baccalaureate Certificate in Intelligence from 2014 to 2019. Stout previously worked for thirteen years as an intelligence analyst, first with the State Department’s Bureau of Intelligence and Research and later with the CIA. Stout also worked on the Army Staff in the Pentagon and at the Institute for Defense Analyses. In addition, from 2010 to 2013 Stout was the historian at the International Spy Museum in Washington, DC. Stout is a series co-editor of Georgetown University Press’ Studies in Intelligence History book series. He is a contributing editor at War on the Rocks and he was the founding president of the North American Society for Intelligence History from 2016-2019. He is the co-author or co-editor of several books and has published articles in The Journal of Strategic Studies, Intelligence and National Security, Studies in Intelligence, and Studies in Conflict and Terrorism. He has a book on American intelligence in World War I under contract to the University Press of Kansas. Stout has degrees from Stanford and Harvard Universities and a PhD in history from the University of Leeds in the United Kingdom. His research interests include American intelligence history and military thought. Details and free registration here.
01 Nov 23, 1200-1300 (ET), - Leadership Analysis: Understanding an Intelligence Discipline - Virtual - Johns Hopkins University
Join Michael Ard for a curated conversation with Deborah Wituski on "Leadership Analysis: Understanding an Intelligence Discipline." Wituski is the vice president for Resilience and Risk Foresight at Google and is responsible for the global program that informs business decisions with trusted resilience and risk analysis to protect Google's people, property, and ideas. Prior to Google, Wituski served in the U.S. government for 20 years. Starting as a leadership analyst in Iraq for the Central Intelligence Agency, Wituski went on to work on Middle East and counterterrorism issues and held senior positions, including chief of staff to the director, CIA. Wituski earned a Bachelor of Arts and a Master of Arts in political science from West Virginia University and a PhD in political science from Ohio State University. Details and free registration here.
8 November 2023, 6 - 8pm EST - Williamsburg, VA - Veterans Day Book Talk with Brian Morra '78 on "Cold War History to Today's Russian Invasion of Ukraine" 
Please join us for a Veterans Day event with W&M alumni Brian J. Morra ’78, who will be discussing his book "The Able Archers." The talk will focus on Brian’s writing process, the history of the Cold War period depicted in the book, and connections that can be drawn to the present-day Russian invasion of Ukraine.
Brian is a former U.S. intelligence officer and a retired senior aerospace executive. Learn more about him. A reception and book signing will follow the talk, and the library’s Special Collections Research Center will have select military collections on display. The W&M Bookstore will be there selling copies of his book. This event is produced in partnership with W&M Libraries, W&M Military and Veteran Affairs, and Association of 1775. Location: Swem Library, Read and Relax, 400 Landrum Dr, Williamsburg, VA 23185Map this location
Free food. Registration/RSVP Required Please register to be guaranteed a seat!
Register for this Event here.
14 - 25 April 2024 - Gary Powers' Cold War Espionage Tour of Austria, the Czech Republic, Slovakia & Hungary - Travel Dates: April 14 to 25,2024 - 12 days/10 nights
Join author & historian Gary Powers Jr. on this 12-day tour of Cold War and espionage related sites in Austria, the Czech Republic, Slovakia & HungaryThe deadline to enroll is 11/30/23 with a required deposit of $495. Final payment is due 12/30/23.
What's Included: • Round-trip air transportation from Washington, DC; • 10 nights in centrally located, four-star hotels; • Full-time CHA Tour Director; • Valuable insight & informative commentary by Gary Powers Jr.; • On-tour transportation by private motorcoach; • Breakfast & dinner (or lunch) daily; • Sightseeing tours & visits shown in itinerary (subject to change based on availability)
Tour Prices: Full Tour Price: $5,695 per person; Land Tour Price: $4,645 per person (does not include round-trip airfare and airport transfers); Repeat Gary Powers travelers will receive a $200 discount! Price based on double occupancy.
A $600 single room fee will apply for travelers without roommates.
The deadline to enroll is 11/30/23 with a required deposit of $495. Final payment is due 12/30/23.
Questions? Call 1-800-323-4466 or email info@cha-tours.com.
Enroll Online at: www.cha-tours.com/GaryPowers
Gifts for Friends, Colleagues, Self
 Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Show your support for AFIO with our new Black Short-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $50 each including shipping.
Sizes for (M) men, only; Small, Medium, Large, XL, XXL, and XXXL. $50 per shirt.
You may pay by check or credit card. Complete your order online here or mail an order along with payment to: AFIO, 7600 Leesburg Pike, Ste 470 East, Falls Church, VA 22043-2004. Phone orders at 703-790-0320. Questions? Contact Annette at: annettej@afio.com.

PopSocket for cellphones or tablets
Show your support to AFIO while enjoying the convenience offered by our AFIO Logo PopSocket. The PopSocket is most commonly used as a stand and as a grip for your mobile phone or tablet; handy for taking selfies, watching videos, and for texting. The PopSocket looks like a small button or sticker which, when closed, sticks flat to your mobile device. However, its accordion-like design enables it to pop open for use. The benefits of using a PopSocket make it a must-have accessory for your mobile phone or tablet. It also aids in keeping your phone from slipping off your hand during use, falling, or breaking.
Price: $15. Order this and other store items online here.

Duffel Bags - Royal Blue and Black with Full Color AFIO Logo This duffel has it all when it comes to value, style and organization.
600 denier polyester canvas with polyester double contrast; D-shaped zippered entry for easy access. Front pocket with hook and loop closure. End mesh pocket Easy-access end pockets. Four durable, protective feet and built-in bottom board for added strength. Web handles with padded grip. Detachable, adjustable shoulder strap.
Dimensions: 11"h x 19.75"w x 9.75"d; Approx. 2,118 cubic inches
Price: $50. Order this and other store items online here.

Caps - Dark Navy with Navy AFIO Logo
An authentic silhouette with the comfort of an unstructured, adjustable fit. Fabric: 100% cotton. Unstructured. Fabric strap closure with adjustable D-clip. Price: $30. Order this and other store items online here.
| PUBLISHED
IN 2023 Be informed on career opportunities in the U.S. Intelligence Community |
||
 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. AFIO's popular 47-page booklet reaches thousands of high school, college students, university guidance offices, and distributed in classes teaching intelligence, to help those considering careers in the U.S. Intelligence Community. |
 |
| This is the all new fifth edition. The publication is also popular with University Career Guidance Centers, professors and academic departments specializing in national security, and parents assisting children or grandchildren in choosing meaningful, public service careers. This booklet is provided online as a public service from the generosity of AFIO board, volunteer editors/writers, donors, and members. We thank all for their support which makes this educational effort possible. |
||
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |
||
 Guide to the Study of Intelligence...and...When Intelligence Made a Difference
Guide to the Study of Intelligence...and...When Intelligence Made a Difference
"AFIO's Guide to the Study of Intelligence" has sold out in hard-copy.
It is available in digital form in its entirety on the
AFIO website here.
Also available on the website here are the individual articles of AFIO's
history project "When Intelligence Made a Difference" that have been
published to date in The Intelligencer journal.
More articles will be appear in future editions.
Some features of the email version of the WIN do not work for readers who have chosen the Plaintext Edition, some AOL users, and readers who access their email using web mail. You may request to change from Plaintext to HTML format here afio@afio.com. For the best reading experience, the latest web edition can be found here: https://www.afio.com/pages/currentwin.htm
To unsubscribe from the WIN email list, please click the "UNSUBSCRIBE" link at the bottom of the email. If you did not subscribe to the WIN and are not a member, you received this product from a third party in violation of AFIO policy. Please forward to afio@afio.com the entire message that you received and we will remove the sender from our membership and distribution lists.
(c) 1998 thru 2023
AFIO Members Support the AFIO Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for back issues of the WINs, information about AFIO, conference agenda and registrations materials, and membership applications and much more! .
AFIO | 7600 Leesburg Pike, Suite 470 East, Falls Church, VA 22043-2004 | (703) 790-0320 (phone) | (703) 991-1278 (fax) | afio@afio.com