08 - 14 November 2023
(Issue 44)
is sponsored by

Readers who encounter problems with the email version of this newsletter can
view the latest web edition here
CONTENTS
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
- FBI director, Virginia officials call for reversal of decision to relocate FBI headquarters in Maryland - Politico, 09 Nov 23
- South Korea plans to launch its 1st military spy satellite on Nov. 30 - ABC News, 05 Nov 23
- Ex-CIA officer accused of drugging and sexually abusing two dozen women pleads guilty in the latest embarrassment for the spy agency - Fortune, 07 Nov 23
- Denmark’s intelligence agencies win a case against a foreign fighter who claims he worked for them - Associated Press, 08 Nov 23
- US lawmakers introduce surveillance reforms intended to curb FBI spying - Reuters, 07 Nov 23
- Explosive Espionage Scandal Rocks Argentina, Threatens Democratic Stability - BNN Network, 09 Nov 23
- Senate Leaders Plan to Prolong NSA Surveillance Using a Must-Pass Bill - Wired, 10 Nov 23
- Ireland: Intelligence service job ‘likely to go to foreigner’ - The Times, 07 Nov 23
- Inaugural Awards Reception Celebrates Excellence in OSINT for National Security - Clearance Jobs, 06 Nov 23
- China to update state secrets law amid increase in spying - Nikei Asia, 08 Nov 23
- DIA Ramps up New Database on Foreign Military Capabilities - Clearance Jobs, 11 Nov 23
- Counterespionage Corner - A collection of recent material on arrests, convictions, expulsions, and more...
- Cyberespionage Collection - Newly identified actors and operations, countermeasures, policy, other...
Section II - FORMERS' FORUM (Legacy Intel Practitioners' Informed Perspectives)
- Multiple conflicts and war fatigue might challenge policy makers, but long-term global security is at stake. — Former Acting CIA Dep. Dir. for Ops and Arkin Group President Jack Devine, In Other News
- Iran-Backed Militias Pressure U.S. Forces | Egypt’s Role in the Future of Gaza | China’s Position on the Israel-Hamas War | Houthi Involvement in Mideast War Complicates Yemen Settlement | Palestinian Politics Key to Post-Hamas Gaza — Former FBI Special Agent and Soufan Group CEO Ali Soufan, Intel Brief
- A Nuclear North Korea Presents Opportunity for Global Leadership in a Complicated World by Former Director of CIA East Asia Operations Joseph Detrani - Cipher Brief, 09 Nov 23
- Israel and the Court of Public Opinion by Former CIA Executive Glen Corn - Cipher Brief, 09 Nov 23
- The Cross-Strait Intelligence Contest Continues Without Quarter by Former CIA Analyst Peter Mattis - Jamestown Foundation, 10 Nov 23
- Active Measures, Reflexive Control, and Useful Idiots interview with AFIO Member and Former CIA Analyst Dr. John Gentry - The Cognitive Crucible Podcast (Information Professionals Association), 07 Nov 23
Section III - MEMBER CONTRIBUTIONS
- Article: The NSA Seems Pretty Stressed About the Threat of Chinese Hackers in US Critical Infrastructure - Wired, 10 Nov 23
- Article: China's 'communist spies' in the dock in Taiwan - BBC, 09 Nov 23
- Article: Espionage case disclosed where young man became civil servant under instruction of foreign spy - Global Times, 08 Nov 23
- Article: Five Eyes Warning Is Clear: Government and Businesses Must Wake Up to China Threat - The Messenger, 07 Nov 23
- Article: Scientist Claims Quantum RSA-2048 Encryption Cracking Breakthrough - Tom's Hardware, 03 Nov 23
- Article: 9/11’s legacy of unintended consequences - Journal of Policing, Intelligence, and Counterterrorism, 01 May 23
- Article: Intelligence warning in the corporate sector: the 2013 In Amenas terrorist attack in retrospect - Journal of Policing, Intelligence, and Counterterrorism, 26 Oct 23
- Article: U.S. intelligence funding of $100 billion questioned - Washington Times, 01 Nov 23
- Article: Cryptographers Solve Decades-Old Privacy Problem - Quanta Magazine, 06 Nov 23
- Article: Something goes boom in the night: the explosion of a Cold War secret - The Space Review, 13 Nov 23
- Article: How Soviet Intelligence Won the Vietnam War - The Times Examiner, 13 Nov 23
Section IV - DEEP DIVES, FILM, HISTORY, POP CULTURE
- A history of intelligence failures from Pearl Harbour to 9/11 to the Israel-Gaza war - ABC Australia, 07 Nov 23
- Surprise Attack: Understanding the Challenges of Intelligence Collection - Foreign Policy Research Institute, 23 Oct 23
- Fireside Chat with DIA Director LTG Berrier - Center for Strategic and International Studies, 01 Nov 23
- Charting China’s Climb as a Leading Global Cyber Power - Insikt Group, 07 Nov 23
- Infographic and Report: Charted: The Number of North Korean Defectors (1998-2023) - Visual Capitalist, 03 Nov 23
- Intelligence in History - A Collection of Recent Content
- A Night At the Museum - SpyCast: The Latest from International Spy Museum Historian Andrew Hammond, PhD. and his guest experts on HUMINT, SIGINT, IMINT, OSINT, and GEOINT
- True Intelligence Matters in Film: Spycraft, Episode 2: Deadly Poisons - Maria Berry (2021)
- Walking Tours: The Spies of Embassy Row and Spies of Georgetown - Washington, DC. (Sundays, Dates/Times Vary)
Section V - Books, Research Requests, Academic Opportunities, Employment, Obituaries
Books — Forthcoming, New Releases, Overlooked
- Ethics of Spying: A Reader for the Intelligence Professional (Volume 3) (Security and Professional Intelligence Education Series, Volume 3) by Jan Goldman
- The Birth of the Soviet Secret Police: Lenin and History's Greatest Heist, 1917-1927 (A New History of the KGB) by Boris Volodarsky
- Intelligence as Democratic Statecraft: Accountability and Governance of Civil-Intelligence Relations Across the Five Eyes Security Community - the United Kingdom, Canada, Australia, and New Zealand by Christian Leuprecht and Hayley McNorton
Research Requests and Academic Opportunities
- Call for Interviews: Author of forthcoming book seeks conversation with intelligence officers who have worked on China during their career
- Call for Information: CIA’s Office of Soviet Analysis (SOVA) 1981-1992
- Call for Information: Al "Albert" Purdum, stationed at Arlington Hall 55, Defense Language School - Albanian 55-56, NSA Linguist, Sr. Cryptologist 57-95
- Call for Information: Octavio Bermudez, State/Commerce Attache Latin America, Crosley Broadcasting - 1922-1942.
- Call for Information: COS Manila in November 1996
- Call for Information: MACV/SOG Sgt Major Charles “Chuck” Remagen
- Call For Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
- Call For Articles: AFIO Journal, The Intelligencer
- Assistant Professor - Intelligence Studies - Embry-Riddle Aeronautical University, Arizona
- Jack Lee, Career CIA Officer and Former AFIO Florida Chapter Officer
Events from Advertisers, Corporate Sponsors, Others
- 15 Nov 23, 1200-1300 (ET) - Virtual - Geospatial Intelligence: Tracking China's Nuclear Program - Johns Hopkins University
- 28 November 2023, 5 - 6pm EST - Washington, DC - IWP hosts IN-PERSON book presentation by Dr. John Gentry on "The Politicization of U.S. Intelligence: Causes and Consequences"
- 28 and 30 Nov 23, 1400-1500 (ET) - Virtual - SPY with Me: Program for Individuals with Dementia and their Care Partners - International Spy Museum
- 14 - 25 April 2024 - Gary Powers' Cold War Espionage Tour of Austria, the Czech Republic, Slovakia & Hungary - Travel Dates: April 14 to 25,2024 - 12 days/10 nights
See the AFIO Calendar of Events for scheduling further in the future.
The Vienna Trilogy by Tom Gilligan (2023)
In the summer of 1947, Europe was in turmoil. Displaced persons were everywhere. The Red Army occupied Poland, Czechoslovakia, parts of German, and other countries. Austria was divided into zones – Russian, American, British, and French. The NKVD secret police followed on the heels of the Red Army, arresting, kidnapping, even killing those who opposed the communists. This is the setting for Tom Gilligan’s trilogy focused on 11-year old David Hale, whose father, a doctor, was deeply involved with medical treatment for refugees, and also was a former intelligence officer during World War II and continued to support American intelligence in post-war Austria. With his mother and sister on vacation in the US that summer, young David became involved in several intelligence support operations. The trilogy – Escape to the West, Nazi’s on the Run, and Stopping the Russian Bear – recount in fascinating detail how David assisted his father, and an American Intelligence agent, in three gripping adventures.
Gilligan, a former CIA DO officer, has written a book appropriate for young readers. The characters are well drawn. The stories are well constructed and gripping. Each of the trilogies is a little more than 100 pages. The author explains the sophisticated words used and espionage terminology and concepts in footnotes, which is a clever tool for young readers to learn vocabulary and understand how HUMINT works. Gilligan also clearly explains the geo-political situation of 1947 in Europe via conversations between David and his father.
The Vienna Trilogy would make an excellent holiday present for young readers ages 10 to 14. On Amazon, $26.99 for all three books in one volume. Each of the books are also available separately.
Reviewed by Peter C. Oleson, Senior Editor, The Intelligencer.
ACKNOWLEDGEMENTS
The WIN editors thank the following contributors of content for this issue:
JK, LR, PO, GR, TG, JG, MA, KB
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
The WIN editors thank the following contributors of content for this issue:
JK, LR, PO, GR, TG, JG, MA, KB
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
DISCLAIMER
Our editors include a wide range of articles and commentary in the Weekly Intelligence Notes to
inform and educate our readers. The views expressed in the articles are purely those of the authors and do not reflect support or endorsement from AFIO. WIN notices about non-AFIO events do not constitute endorsement or recommendation by AFIO.
AFIO does not vet or endorse research inquiries, career announcements, or job offers. We publish reasonable-sounding inquiries and career offerings as a service to our members. We encourage readers to exercise caution and good judgment when responding and to independently verify the source before supplying resumes, career data, or personal information.
TECHNICAL DIFFICULTIES
Readers who encounter problems with links or viewing this newsletter as an email can access
the latest web edition here.
the latest web edition here.
LATEST FROM AFIO
Note: The WIN will not be published on 21 and 28 November
in honor of the Thanksgiving Holiday. Publication will resume
on 5 December 2023. Happy Thanksgiving from the editorial team!
in honor of the Thanksgiving Holiday. Publication will resume
on 5 December 2023. Happy Thanksgiving from the editorial team!
All of us, these days, receive barrages of fund-raising emails and letters. The annoyance factor is one reason AFIO rarely asks members for contributions and runs a lean outfit. Just as we avoid sending more than a single email per week. And only if you opted-in to receive it.
On this occasion of "Giving Tuesday" and as the end-of-year approaches, we make an exception to ask if you will consider making a contribution (U.S. tax-deductible) in the next two weeks, to help us continue our important outreach and educational missions in 2024.
AFIO provides members with special events, meeting opportunities, one-on-one career guidance, publications, and notices few find elsewhere — an effort that requires support far beyond dues. For those reasons we invite you to donate today, Giving Tuesday — a holiday that celebrates generosity and kindness by giving to nonprofit organizations — or before the close of 2023.
You are the ones making the real difference! And our work is made possible through the support of our members, subscribers, and donors — you. Clicking on either image above will take you to our donation page. AFIO appreciates your interest and any support you're able to provide!
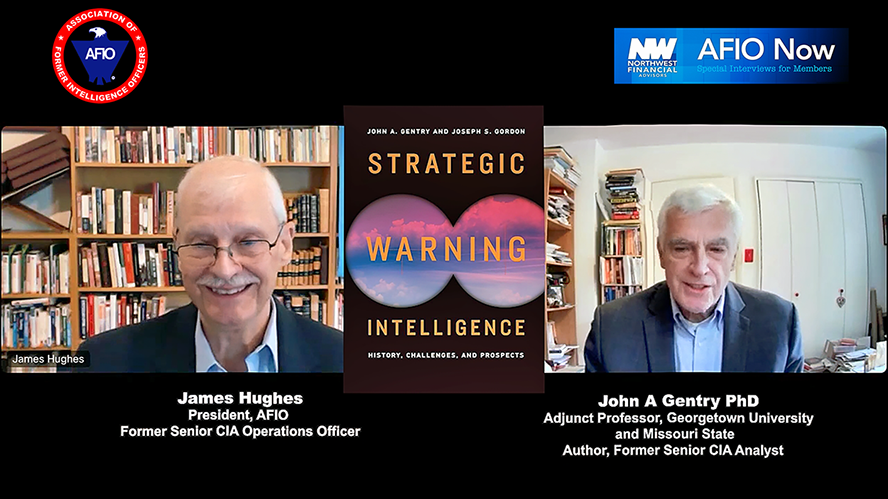
Released exclusively to members 14 November 2023...
Strategic Warning Intelligence and "The Paradox of Warning"
Interview of Thursday, 28 Sep 2023 between Dr John A. Gentry, Former Senior CIA Analyst, Current Adjunct Professor, Georgetown University;
and AFIO President James Hughes, a former senior CIA Operations Officer.
They discuss John's book "Strategic Warning Intelligence: History, Challenges, and Prospects."
The interview runs 37 minutes and includes several Q&As.
Strategic Warning Intelligence: History, Challenges, and Prospects [Georgetown Univ Press, 2019] is available here.
Also see Dr. Gentry's latest book, Neutering the CIA: Why US Intelligence Versus Trump Has Long-Term Consequences (Armin Lear Press, 2023)
Access John Gentry's interview here or click above image.
This, and upcoming AFIO Now videos in 2023, are sponsored by Northwest Financial Advisors.

AFIO National 2024 Board Elections Close End of November
Please Cast Your Vote
Members... cast your ballot here
[Requires log-in]
Elections close Thursday, 30 November 2023 at 11:45 p.m. ET

"AFIO Now" Video Interviews and Podcasts in 2023 are sponsored by
Northwest Financial Advisors
Click here to watch interviews in the AFIO Now series released in 2023.
View interviews from 2020 to 2022 here.
Watch public-release interviews on our YouTube channel or listen to them in podcast form at the links below.
Log into the member-only area for member-only features.
LATEST PODCAST: Part II of Interview with Michael G. Vickers PhD Tuesday, Nov 7, 2023. In this second of a two-part series, former CIA Operations Officer and Undersecretary of Defense for Intelligence Michael Vickers wraps up his discussion of his new memoir, "By All Means Available: Memoirs of a Life in Intelligence, Special Operations, and Strategy." Recorded 29 Jun 2023. Interviewer: Jim Hughes, AFIO President and former CIA Operations Officer.
AFIO Podcast here.
Are you too busy to watch an entire AFIO Now episode on YouTube? Would you rather listen in your car or while accomplishing other tasks? You can download or stream episodes on any of the 8 podcasting platforms that host AFIO Now. Search for 'AFIO Podcast' for a selection of the interviews above (public released ones) on:
Podbean; iTunes; Google; Spotify; Amazon Music; Amazon TuneIn + Alexa; iHeartRadio; Pandora
28 November 2023 (Tuesday), 5 - 6 pm EST - Washington, DC - IWP hosts IN-PERSON book presentation by Dr. John Gentry on "The Politicization of U.S. Intelligence: Causes and Consequences"
 The Institute of World Politics invites you to attend an IN-PERSON book lecture by Dr. John Gentry, Author and Professor at the School of Defense and Strategic Studies, Missouri State University, discussing "The Politicization of U.S. Intelligence: Causes and Consequences."
The Institute of World Politics invites you to attend an IN-PERSON book lecture by Dr. John Gentry, Author and Professor at the School of Defense and Strategic Studies, Missouri State University, discussing "The Politicization of U.S. Intelligence: Causes and Consequences."
"The Politicization of U.S. Intelligence: Causes and Consequences” is a presentation in association with Dr. Gentry's recent book, Neutering the CIA: Why US Intelligence Versus Trump Has Long-Term Consequences (Armin Lear Press, 2023). Beginning in 2016 and continuing into 2021, current and former U.S. intelligence officers engaged in domestic partisan politics to an unprecedented extent. This discussion will describe and assess what happened at various agencies, the causes of the politicization, consequences for the agencies and national decision-making, and prospects for renewed politicization in 2024.
***Copies of Dr. Gentry's book will be made available for purchase at the conclusion of the event and can be signed by the author.*** ***This lecture is sponsored by the IWP IAFIE Alpha Student Chapter***
Location: The Institute of World Politics, 1521 16th St NW, Washington, DC 20036.
Special Walking Tours Announcements
from SpyGuide Tours Inc.
from SpyGuide Tours Inc.
NEW - Saturday 25 November 2023 at 10a.m.: Secret Stories of Arlington National Cemetery. Visit the final resting places of some renowned U.S. Intelligence Officers and hear their stories. Stops also into the Tomb of the Unknown Soldier and the Kennedy gravesites. Book at https://spyher.co
Vintage Espionage travels throughout the U.S.
Visit https://spyher.co to learn more and book all tours.
FROM THE AFIO STORE
Special Gifts for Colleagues, Self, or Others
 RARE. Mint condition. Only three copies available. The CIA Insider’s Dictionary, 744 pages, published 1996. A dictionary of tradecraft, intelligence and counterintelligence terms and phrases. A great gift for students, professionals, and writers of spy fiction and nonfiction, and by those interested in intelligence, counterintelligence, and covert operations or book collectors. Price includes shipping within the continental US. $35 Only 3 copies available. Order one today and get your gift shopping started! Telephone the office at 703-790-0320 or email julie@afio.com to obtain one of these last copies.
RARE. Mint condition. Only three copies available. The CIA Insider’s Dictionary, 744 pages, published 1996. A dictionary of tradecraft, intelligence and counterintelligence terms and phrases. A great gift for students, professionals, and writers of spy fiction and nonfiction, and by those interested in intelligence, counterintelligence, and covert operations or book collectors. Price includes shipping within the continental US. $35 Only 3 copies available. Order one today and get your gift shopping started! Telephone the office at 703-790-0320 or email julie@afio.com to obtain one of these last copies.
 NEW Gray long-sleeved polo shirts with embroidered AFIO logo. Men's sizes only.
NEW Gray long-sleeved polo shirts with embroidered AFIO logo. Men's sizes only. Show your support for AFIO with our new Gray Long-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $60 each including shipping.
Sizes for men, only: Small, Medium, Large, XL, XXL, and XXXL. $60 per shirt. Order this and other store items online here.
 NEW 20 oz ceramic Mug with color glazed logo. Made in America. Check out our new tapered, sleek AFIO coffee mug!! This handsome 20 oz. ceramic mug is made in the USA, has a white matte exterior, sports a beautiful navy-blue interior, and is dishwasher safe. Order yours today! $35 per mug includes shipping to a CONUS address. [includes shipping to U.S. based address, only. For foreign shipments, we will contact you with a quote.] SHIPPING: For shipment to a U.S.-based CONUS address, shipping is included in price. For purchases going to AK, HI, other US territories, Canada, or other foreign countries the shipping fees need to be calculated, so please call our office M-F 8 a.m. to 2 p.m. ET at 703-790-0320 or email afio@afio.com providing following information: 1) your name, 2) mailing address (or addresses where each gift item will be shipped), 3) name of the AFIO store items you wish to purchase, 4) quantity of each, 5) your credit card number and expiration date, 6) amount (except for additional of shipping fees) authorized to charge, and 7) your phone number and email should we have questions. Foreign shipments fees will be calculated and estimates emailed to you, awaiting your approval. Order this and other store items online here.
NEW 20 oz ceramic Mug with color glazed logo. Made in America. Check out our new tapered, sleek AFIO coffee mug!! This handsome 20 oz. ceramic mug is made in the USA, has a white matte exterior, sports a beautiful navy-blue interior, and is dishwasher safe. Order yours today! $35 per mug includes shipping to a CONUS address. [includes shipping to U.S. based address, only. For foreign shipments, we will contact you with a quote.] SHIPPING: For shipment to a U.S.-based CONUS address, shipping is included in price. For purchases going to AK, HI, other US territories, Canada, or other foreign countries the shipping fees need to be calculated, so please call our office M-F 8 a.m. to 2 p.m. ET at 703-790-0320 or email afio@afio.com providing following information: 1) your name, 2) mailing address (or addresses where each gift item will be shipped), 3) name of the AFIO store items you wish to purchase, 4) quantity of each, 5) your credit card number and expiration date, 6) amount (except for additional of shipping fees) authorized to charge, and 7) your phone number and email should we have questions. Foreign shipments fees will be calculated and estimates emailed to you, awaiting your approval. Order this and other store items online here.
 Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
Roy Berkeley's "A Spy's London" - Original U.S. Edition - A Few Unsold Copies Available
In 'this remarkable book' (as intelligence historian and AFIO member Nigel West describes in his Foreword), the reader will be struck by the vibrancy of history made real. Author/AFIO member Roy Berkeley goes behind the facades of ordinary buildings, in the city that West calls 'the espionage capital of the World,' to remind us that the history of intelligence has often been made in such mundane places. With his evocative photographs and compelling observations, The 136 sites are organized into 21 manageable walks. But also a joy to armchair travelers. Among the sites: the modest hotel suite where an eager Red Army colonel poured out his secrets to a team of British and American intelligence officers; the royal residence where one of the most slippery Soviet moles was at home for years; the London home where an MP plotting to appease Hitler was arrested on his front steps in 1940. A few copies are available at only $20 a copy (postage to a U.S.-based address included). Telephone the office at 703-790-0320 or email julie@afio.com to obtain one of these last copies.
Access CIA's In-house Gift Shop
One special benefit of AFIO membership is access to CIA's EAA Store.
After completing the required, quick pre-approval process for all AFIO members described here, you can purchase directly from the EAA online store their unusual logo'd gift items for self or colleagues. EAA on 20 October 2023 released the photo above, which features some of their newest CIA items and other gift suggestions.
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
FBI director, Virginia officials call for reversal of decision to relocate FBI headquarters in Maryland - Politico, 09 Nov 23
Virginia officials and the head of the FBI called on Thursday for the reversal of a decision to relocate the headquarters of America’s top law enforcement agency to suburban Maryland. They allege that the federal agency tasked with overseeing the relocation, the General Services Administration, which oversees federal real estate, failed to address what they said were conflicts of interest in the selection process. In an internal message to FBI employees on Thursday that was obtained by POLITICO, FBI Director Christopher Wray blasted the decision to move the agency to Greenbelt, Md., saying that a three-person panel made up of two GSA officials and one FBI official unanimously recommended a site in Virginia for the new headquarters. But instead, a political appointee at the GSA chose the Greenbelt site, against the panel’s recommendation. (Full article here.)
South Korea plans to launch its 1st military spy satellite on Nov. 30 - ABC News, 05 Nov 23
South Korea said Monday it plans to launch its first domestically built spy satellite at the end of this month to better monitor rival North Korea, which is expanding its arsenal of nuclear weapons. The plan was unveiled days after North Korea failed to follow through on a vow to make a third attempt to launch its own reconnaissance satellite in October, likely because of technical issues. Jeon Ha Gyu, a spokesperson for the South Korean Defense Ministry, told reporters Monday that the country’s first military spy satellite will be launched from California’s Vandenberg Air Force Base on Nov. 30. The satellite will be carried by SpaceX’s Falcon 9 rocket. Under a contract with SpaceX, South Korea plans to launch four more spy satellites by 2025, according to South Korea’s Defense Acquisition Program Administration. (Full article here.)
Ex-CIA officer accused of drugging and sexually abusing two dozen women pleads guilty in the latest embarrassment for the spy agency - Fortune, 07 Nov 23
A former CIA officer accused of drugging and sexually assaulting at least two dozen women during various overseas postings pleaded guilty Tuesday to federal sex abuse charges. Brian Jeffrey Raymond kept nearly 500 videos and photographs he took of naked, unconscious women, including many in which he can be seen opening their eyelids, groping or straddling them, prosecutors say. The images date to 2006 and track much of Raymond’s career, with victims in Mexico, Peru and other countries. (Full article here.)
Denmark’s intelligence agencies win a case against a foreign fighter who claims he worked for them - Associated Press, 08 Nov 23
Denmark’s domestic and foreign intelligence services on Wednesday won a case against a Dane of Syrian origin who claimed he worked for them in Syria in 2013 and 2014 and spied on Danish jihadi fighters. Ahmed Samsam was sentenced to eight years in 2018 in Spain for fighting with the Islamic State group in Syria. He sued Denmark’s two spy agencies in an attempt to have a court order them to admit that he had worked for them, and hoping it would enable him to reopen the case in Spain. The Eastern High Court in Copenhagen said in its ruling that Samsam had not made it likely that he could reopen his case in Spain. He immediately appealed the ruling to Denmark’s top court. (Full article here.)
US lawmakers introduce surveillance reforms intended to curb FBI spying - Reuters, 07 Nov 23
A bipartisan team of U.S. lawmakers has introduced new legislation intended to curb the FBI's sweeping surveillance powers, saying the bill helps close the loopholes that allow officials to seize Americans' data without a warrant. The bill follows more than a decade of debate over post-Sept. 11, 2001, surveillance powers that allow domestic law enforcement to warrantlessly scan the vast mountains of data gathered by America's foreign surveillance apparatus. Reforms in the proposed legislation include putting limits on searches of Americans' communications without judicial authorization and a prohibition of so-called "backdoor" searches which invoke foreign intelligence justifications to spy on Americans. "We're introducing a bill that protects both Americans' security and Americans' liberty," Senator Ron Wyden - a Democrat and a longtime critic of government surveillance - said at a press conference on Tuesday. (Full article here.)
Explosive Espionage Scandal Rocks Argentina, Threatens Democratic Stability - BNN Network, 09 Nov 23
In Argentina, a political espionage scandal has exploded, exposing the entrails of a power apparatus allegedly led by Cristina Kirchner, aimed to corner the Judicial Power. The details of the investigation reveal a plot where several threads of the political underworld and intelligence services intersect. The illegally obtained information was used to influence judicial decisions and affect the independence of judges. This scandal could have significant implications for Argentine democracy as it exposes institutional manipulation and intelligence services’ intervention in the country’s politics. (Full article here.)
Senate Leaders Plan to Prolong NSA Surveillance Using a Must-Pass Bill - Wired, 10 Nov 23
Leaders in the United States Senate have been discussing plans to extend Section 702 of the Foreign Intelligence Surveillance Act (FISA) beyond its December 31 deadline by amending must-pass legislation this month. A senior congressional aide tells WIRED that leadership offices and judiciary sources have both disclosed that discussions are underway about saving the Section 702 program in the short term by attaching an amendment extending it to a bill that is sorely needed to extend federal funding and avert a government shutdown one week from now. The program, last extended in 2018, is due to expire at the end of the year. Without a vote to reauthorize 702, the US government will lose its ability to obtain year-long “certifications” compelling telecommunications companies to wiretap overseas calls, text messages, and emails without being served individual warrants or subpoenas. (Full article here.)
Ireland: Intelligence service job ‘likely to go to foreigner’ - The Times, 07 Nov 23
A foreign national will almost certainly be appointed to lead Ireland’s intelligence service, responsible for safeguarding the state from espionage, as the government faces an unprecedented national security crisis. No senior garda has applied for the role of deputy commissioner responsible for intelligence and policing as they would incur tax bills of about €100,000 upon retirement due to an error in 2014 introducing tax rules on pensions. The competition to fill the vacancy will close on Thursday, having received applications from just a handful of candidates from Northern Ireland and Britain. (Full article here.)
Inaugural Awards Reception Celebrates Excellence in OSINT for National Security - Clearance Jobs, 06 Nov 23
The OSINT Foundation, the premier professional association of Intelligence Community (IC) open-source intelligence (OSINT) professionals, held its inaugural awards reception on November 3rd, in a grand celebration of the remarkable achievements in OSINT. Launched in 2022, the OSINT Foundation is dedicated to promoting OSINT tradecraft, elevating the discipline, and building a strong practitioner community, all for the greater advancement of the national security of the United States. The evening, marked by a spirit of recognition and camaraderie, honored not just individuals but also IC organizations whose tireless efforts have significantly enhanced the United States’ national security. The winners in various categories stood out for their outstanding contributions and dedication. Shawn Porter, 312th Military Intelligence Battalion, U.S. Army was awarded the prestigious LTC Ed Waller IC OSINT Practitioner of the Year, a recognition of his exceptional service to the nation, substantial contributions to the OSINT discipline, and his mentorship of fellow OSINT practitioners. (Full article here.)
China to update state secrets law amid increase in spying - Nikei Asia, 08 Nov 23
China is looking to amend its state secrets law for a second time in 13 years to strengthen the Communist Party's control over the country's work involving state secrets amid an increase in espionage. A draft revision released by the National People's Congress, China's top legislative body, in late October shows potential changes to around two-thirds of the current Law on Guarding State Secrets, with 10 new articles added. Among the additions is an article on "adhering to the leadership of the Communist Party of China in the work of protecting state secrets," which states that the party's central secrecy leadership organ will be in charge of guiding, promoting research, formulating policy and coordinating projects related to the country's secrecy work. The changes were proposed to cope with new challenges facing the country's secrecy work, while introducing experience from protecting secrets in the past decade into law, said Li Zhaozong, head of the National Administration of State Secrets Protection, when presenting the draft during a meeting of the Standing Committee of the National People's Congress in October. (Full article here.)
DIA Ramps up New Database on Foreign Military Capabilities - Clearance Jobs, 11 Nov 23
The Defense Intelligence Agency (DIA) is nearing key milestones for its new Machine-assisted Analytic Rapid-repository System (MARS), which will replace an aging system for processing intelligence on foreign militaries, according to the agency’s leader. MARS is expected achieve an initial operational capability in spring 2024 and a full operational capability in 2025, Army Lt. Gen. Scott Berrier, DIA’s director, said on Nov. 1 at the Washington, D.C.-based Center for Strategic and International Studies (CSIS). MARS will replace the Modernized Integrated Database (MIDB), providing increased automation; more types of information, including intelligence on cyber and space capabilities; and larger volumes of data. While a MIDB record might contain a satellite photo with an Excel spreadsheet that explains what the image is, the cloud-based MARS will provide a “map database infused with lots of different open-source data points that will tell you what’s going on there – information that we can buy, other information that we can steal,” Berrier said. (Full article here.)
Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
- Japanese man's 12-yr prison term over espionage finalized in China - The Mainichi, 11 Nov 23
- Latvian ex-Interior Minister gets 8.5 years for Russian espionage - TVP World, 10 Nov 23
- Swedish Govt Proposes Revoking Residence Permits & Passports to Foreigners Suspected of Espionage & Terrorism - Schengen Visa Info, 09 Nov 23
- Espionage case disclosed where young man became civil servant under instruction of foreign spy - Global Times, 08 Nov 23
- The Fight Against Espionage In Europe Dismantles The Low-Down Spider Of Moroccan Intelligence - Echo Rouk, 05 Nov 23
- NIA files supplementary chargesheet in espionage racket case - The Hindu, 06 Nov 23
- Three Mossad spies were arrested in the border areas of Afghanistan and Iran - Ava Press, 05 Nov 23
- The Evolution of Cyber Espionage in the Arab World Since the Beginning of the Arab Spring - Daraj Media, 13 Nov 23
- Russian spies behind cyber attack on Ukraine power grid in 2022 - researchers - Reuters, 09 Nov 23
- The Rising Dragon of Cyber Espionage - The Final Hop, 09 Nov 23
- Mandiant Unveils Russian Cyber Espionage in Ukraine’s Grid Disruption - Security Online, 09 Nov 23
- Kaspersky Lab Exposes TTPs of Asian Cyber Espionage Groups - Security Online, 09 Nov 23
Section II - FORMERS' FORUM
(Legacy Intel Practitioners' Informed Perspectives)
(Legacy Intel Practitioners' Informed Perspectives)
The Latest Insights from Former CIA Acting Deputy Director for Operations Jack Devine.
 In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
09 Nov | Multiple conflicts and war fatigue might challenge policy makers, but long-term global security is at stake. As Israel enters the next phase of its battle against Hamas, with ground troops entering Gaza and reportedly encircling Gaza City, the dramatic, decades-old regional conflict has recaptured the world’s attention. Israeli Prime Minister Netanyahu has cautioned that the physical war will be long and difficult and has suggested that Israel will manage Gaza’s security indefinitely after the battle’s eventual end. As much as members of the international community might try to pressure Israel into a “humanitarian pause” or “ceasefire” in Gaza, Israel recognizes that every pause presents an opportunity for Hamas terrorists to escape through the Egyptian border, re-equip, or further abuse Israeli hostages. (Full version available to AFIO members in the coming days here.)
Daily Analysis of Security Issues and Geopolitical Trends
 Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
Intel Brief The Soufan Center's flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
14 Nov | Iran-Backed Militias Pressure U.S. Forces in Iraq and Syria
By targeting U.S. forces deployed in Iraq and Syria, Iran-backed militias seek to advance Tehran’s objectives of pressuring American leaders to remove U.S. ground forces from countries near Iran’s borders. That the Iraqi and Syrian militia attacks are directed against U.S. bases and personnel, rather than Israel, indicates not only that the militias might lack the capability to project power into Israel, but also that they are mainly seeking to advance anti-U.S. objectives rather than directly support Hamas’ conflict. The Iran-backed Houthi movement, by contrast, which is another pillar of Iran’s “axis of resistance,” sought to attack Israel, not the United States, as an expression of direct support for Hamas’ battle against the Israel Defense Force.
13 Nov | What is Egypt’s Role in the Future of Gaza?
09 Nov | What is China’s Position on the Israel-Hamas War?
08 Nov | Houthi Involvement in Mideast War Hinders Prospects for a Yemen Settlement
07 Nov | Palestinian Politics Key to Post-Hamas Gaza
A Nuclear North Korea Presents Opportunity for Global Leadership in a Complicated World by Former Director of CIA East Asia Operations Joseph Detrani - Cipher Brief, 09 Nov 23
This is the twentieth anniversary of the Six Party Talks, established in 2003, to resolve the nuclear issue with North Korea. It’s an auspicious time for China, the host of the Talks, to put aside tension with the U.S. and encourage North Korea to return to negotiations. Ideally, the subject of North Korea will be discussed when President Joe Biden meets President Xi Jinping at the Asia-Pacific Economic Cooperation Summit in San Francisco later this month. Russia’s February 2022 invasion of Ukraine – and the ongoing bloody war there – and Hamas’s terrorist attack on Israel on October 7 – and the ongoing war in Gaza – have diverted attention away from North Korea, although North Korea reportedly is providing Russia with artillery shells and rockets for its war in Ukraine and Hamas is reportedly using North Korean F-7 rocket-propelled grenades in its war with Israel. Hamas, a proxy of Iran, receives training, funding, and support from Iran for its terrorist activities. And North Korea continues to have a close relationship with Iran, having provided Tehran with rockets, missiles, and weaponry over the years, in return for needed cash for their nuclear and missile programs.(Full report here.)
Israel and the Court of Public Opinion by Former CIA Executive Glen Corn - Cipher Brief, 09 Nov 23
Years ago, while working on a Counterterrorism operation in an unnamed country, the team I was working with was fortunate enough to disrupt a terrorist plot and capture several extremists who were planning to conduct attacks. In the process, we also collected a wealth of information that was in the possession of this terrorist cell, which in the parlance of the Special Operations and Intelligence Community, is commonly referred to as “Site Exploitation” or “SITEX”, materials that can be exploited for intelligence collection purposes. Among the documents was a manual written by Al-Qa’ida and translated into the local language so that it could be used for training new recruits and Jihadists. Being one of the only officers that spoke the local language, it fell upon me to translate key parts of the document. As I read through the material, I found that the authors had used an interesting analogy to help new recruits understand how they would wage war against their enemies. Recognizing that the terrorist groups were smaller and less well-funded than the governments they were fighting, the authors claimed that the goal of their organization was to conduct small-scale attacks that would annoy and disrupt government operations. (Full report here.)
The Cross-Strait Intelligence Contest Continues Without Quarter by Former CIA Analyst Peter Mattis - Jamestown Foundation, 10 Nov 23
Last week, the Taiwan High Court found retired air force Colonel Liu Sheng-shu (劉聖恕) and five serving military officers guilty of espionage for China. The court sentenced Colonel Liu and two of his co-conspirators to approximately 20 years in prison, marking some of the harshest sentencing for espionage in recent years (Taipei Times, October 26). Liu’s spy ring is one of at least 11 rings Taiwanese authorities have broken up over the last two years. These Chinese spies targeted Taiwan’s military, civilian government, industry, and the overseas communities of Chinese minorities. In some cases they were able to operate for years. Although it is tempting to read these cases as simply more examples of Beijing’s relentless intelligence operations against Taiwan, these cases and the tradecraft employed suggest some positive developments—or the relative absence of dangerous trends—in the cross-strait intelligence contest. The cost in trust of Chinese intelligence operations, the requirements of deterrence, and the potential costs of a cross-strait conflict combine to suggest that a wider international effort to counter Chinese intelligence operations is warranted. (Full report here.)
Active Measures, Reflexive Control, and Useful Idiots interview with AFIO Member and Former CIA Analyst Dr. John Gentry - The Cognitive Crucible Podcast (Information Professionals Association), 07 Nov 23
During this episode, AFIO member and former CIA analyst Dr. John Gentry discusses long-term influence strategies employed by the former Soviet Union, which remain ongoing today. The conversation covers a wide range of related topics including reflexive control, useful idiots, institutions, diaspora, plus more. Research Question: John Gentry suggests that an interested student examine vulnerabilities that attackers identify, what causes them, and how to ameliorate them. For starters, he describes three general categories: ideology, gullibility, and interests (for example: financial). (48 mins) (Listen here.)
Section III - MEMBER CONTRIBUTIONS
Article: The NSA Seems Pretty Stressed About the Threat of Chinese Hackers in US Critical Infrastructure - Wired, 10 Nov 23
The United States National Security Agency is often tight-lipped about its work and intelligence. But at the Cyberwarcon security conference in Washington DC on Thursday, two members of the agency’s Cybersecurity Collaboration Center had a “call to action” for the cybersecurity community: Beware the threat of Chinese government-backed hackers embedding in US critical infrastructure. Alongside its “Five Eyes” intelligence alliance counterparts, the NSA has been warning since May that a Beijing-sponsored group known as Volt Typhoon has been targeting critical infrastructure networks, including power grids, as part of its activity. Officials emphasized on Thursday that network administrators and security teams need to be on the lookout for suspicious activity in which hackers manipulate and misuse legitimate tools rather than malware—an approach known as “living off the land”—to carry out clandestine operations. They added that the Chinese government also develops novel intrusion techniques and malware, thanks to a substantial stockpile of zero-day vulnerabilities that hackers can weaponize and exploit. Beijing collects these bugs through its own research, as well as a law that requires vulnerability disclosure. (Read full report here.)
Article: China's 'communist spies' in the dock in Taiwan - BBC, 09 Nov 23
Taiwan and China have been spying on each other since 1949, when Chinese nationalists set up a separate government in Taipei opposing Mao Zedong's communist China. In the last 10 months, Taiwanese authorities have handed down a steady stream of charges and convictions - proof, they say, that Beijing's espionage strategy has intensified and expanded beyond elite military circles. Retired air force colonel Liu Sheng-shu was sentenced to 20 years in prison in October for running a military spy ring for Beijing. At least 16 people have been accused of spying for China since the start of the year, compared with the 44 espionage cases registered by Taiwan's Ministry of Justice Investigation Bureau between 2013 and 2019. (Read full report here.)
Article: Espionage case disclosed where young man became civil servant under instruction of foreign spy - Global Times, 08 Nov 23
China's national security authorities recently disclosed an espionage case in which a young man became a civil servant under the instruction of a foreign spy, as reported by Shanghai Media Group on Tuesday. The young man surnamed Dong was born in the 1990s. After graduating from university in 2019, Dong started working at a research institute in Shanghai. One evening, on Dong's way to home, he was stopped by a foreigner asking for directions. They later became acquainted. The foreigner, who is actually a spy, turned to Dong for help to do monthly reports on their respective fields of study, and offered to reward him in payments. Later, the foreigner asked Dong to find industry-related content, data, and analysis reports from his workplace. Dong was well aware that internal information was classified, but he couldn't resist the temptation of the payments. As their relationship deepened, under the guidance of the foreign spy, Dong even successfully became a civil servant, leading to more opportunities to access important and core information and data within the organization. Dong was asked to make copies or take photos of these documents at his instruction. (Read full report here.)
Article: Five Eyes Warning Is Clear: Government and Businesses Must Wake Up to China Threat - The Messenger, 07 Nov 23
Which presents the greater espionage threat to Western democracy: the Russia-Ukraine war or the Israel-Hamas conflict? Remarkably, if you ask the West’s five leading intelligence officials, the answer is “neither.” Last month when the Five Eyes — an intelligence alliance of Australia, Canada, New Zealand, the United Kingdom, and the United States — came together for their first-ever public meeting and joint interview, they didn’t focus on Russian imperialism or a conflict that might engulf the Middle East. Instead, they focused on China’s access to and theft of Western intellectual property. On close examination, it is easy to see why the intelligence leaders feel this way. The Five Eyes’ unprecedented joint call for action reflects warning signs that have been flashing “since China first opened its market.” (Read full report here.)
Article: Scientist Claims Quantum RSA-2048 Encryption Cracking Breakthrough - Tom's Hardware, 03 Nov 23
A commercial smartphone or Linux computer can be used to crack RSA-2048 encryption, according to a prominent research scientist. Dr Ed Gerck is preparing a research paper with the details but couldn’t hold off from bragging about his incredible quantum computing achievement (if true) on his LinkedIn profile. Let us be clear: the claims seem spurious, but it should be recognized that the world isn’t ready for an off-the-shelf system that can crack RSA-2048, as major firms, organizations, and governments haven’t yet transitioned to encryption tech that is secured for the post-quantum era. (Read full report here.)
Article: 9/11’s legacy of unintended consequences - Journal of Policing, Intelligence, and Counterterrorism, 01 May 23
Richard Betts once observed that reforms of U.S. intelligence usually produce unintended, negative consequences. The relatively large legislative and administrative reforms that followed the 9/11 terrorist attacks on the United States enhanced American counterterrorism capabilities substantially but confirmed Betts’ observation in new ways. This article discusses unintended negative consequences in five general arenas that developed in various ways over different periods of time, including undesirable effects on analysis, collection, organisational cultures, and the politicisation of intelligence. While some implications are clear, others are less certain and some are still unfolding. (Read full report here.)
Article: Intelligence warning in the corporate sector: the 2013 In Amenas terrorist attack in retrospect - Journal of Policing, Intelligence, and Counterterrorism, 26 Oct 23
The 2013 terrorist attack at the In Amenas, Algeria gas production facility killed 40 innocent people and shook the corporate security industry. Analyzing this event raises important questions about the nature and limitations of intelligence warning for private industry. Corporate security intelligence has been adopted by many companies that desire a ‘decision advantage’, but in this case, it failed to foresee the attack. A seminal report on the attack produced by Statoil (now Equinor) encouraged numerous changes in how companies should protect themselves against severe security threats. One conclusion was that in uncertain and dangerous environments, intelligence cannot be relied upon to reduce uncertainty and provide adequate warning. The Statoil report acknowledges that the joint venture likely would not have gotten the intelligence necessary to warn of an impending attack. The core business is not necessarily focused on the changing threat environment. In this case, even more accurate ‘tactical’ intelligence might not have led to a timely evacuation. Moreover, as the Algerian Army’s failure to prevent the In Amenas attack reveals, corporations’ risk assessments cannot ignore the severe limitations of their host country security institutions. This case study raises some concerns about overvaluing corporate intelligence’s effectiveness in high-risk security environments. (Read full report here.)
Article: U.S. intelligence funding of $100 billion questioned - Washington Times, 01 Nov 23
Annual intelligence spending for civilian and military spy agencies was made public this week and shows that the combined budget for fiscal year 2023 intelligence programs was $99.6 billion. The Pentagon released its figure for what is called the military intelligence program for the 12 months that ended Sept. 30, showing $27.9 billion that is said to be aligned with the Biden administration’s national defense strategy. Director of National Intelligence Avril Haines, in a separate announcement, revealed that the national intelligence program budget for last year was $71.7 billion. Both intelligence budgets were formerly secret, but topline amounts are now made public under a 2019 federal law. (Read full report here.)
Article: Cryptographers Solve Decades-Old Privacy Problem - Quanta Magazine, 06 Nov 23
We all know to be careful about the details we share online, but the information we seek can also be revealing. Search for driving directions, and our location becomes far easier to guess. Check for a password in a trove of compromised data, and we risk leaking it ourselves. These situations fuel a key question in cryptography: How can you pull information from a public database without revealing anything about what you’ve accessed? It’s the equivalent of checking out a book from the library without the librarian knowing which one. Concocting a strategy that solves this problem — known as private information retrieval — is “a very useful building block in a number of privacy-preserving applications,” said David Wu, a cryptographer at the University of Texas, Austin. Since the 1990s, researchers have chipped away at the question, improving strategies for privately accessing databases. One major goal, still impossible with large databases, is the equivalent of a private Google search, where you can sift through a heap of data anonymously without doing any heavy computational lifting. (Read full report here.)
Article: Something goes boom in the night: the explosion of a Cold War secret - The Space Review, 13 Nov 23
In the fall of 1983 American reconnaissance satellites spotted preparations for a space launch at the sprawling Soviet missile and space launch range known as the Baikonur Cosmodrome, then popularly called “Tyuratam.” The satellites photographed activity at what the CIA labeled “Launch Site A1.” A1 was in fact the most famous launch pad at Baikonur, both for the Soviet Union and the rest of the world. When a CIA U-2 spyplane had first flown over Baikonur in the late 1950s, it spotted one primary launch pad, which the National Photographic Interpretation Center, which analyzed overhead imagery of the Soviet Union, soon named Complex A. Later launch complexes were designated B, C, D, and so on. Complex A became famous as the site of the Sputnik launch, and later Yuri Gagarin launched from there as well. But soon Site A1 would be the site of a spectacular accident, one that the Soviet Union sought to keep secret. American satellites would photograph the accident in detail, and information on it would accidentally leak to the Western media. (Read full report here.)
Article: How Soviet Intelligence Won the Vietnam War - The Times Examiner, 13 Nov 23
From October through December 1972, U.S. B-52 bombing and U.S Navy mining of North Vietnamese principal ports brought the North Vietnamese Communists in Hanoi to their knees. This and President Nixon’s Vietnamization of the ground war beginning in 1969 had brought all but 26,000 Americans home and won the war. A peace treaty was signed in Paris on January 27, 1973. It could have been a stronger treaty had Congress not applied financial pressures to limit American actions. However, all that was needed to maintain peace was keeping the South Vietnamese armed forces supplied. But following Nixon’s Watergate scandal and 1974 Congressional elections, Congress so limited funds to support South Vietnam’s defensive capabilities that North Vietnam, bolstered by renewed Soviet financing, launched a massive, heavily equipped invasion of South Vietnam and Cambodia in 1975. The abandonment and the fall of South Vietnam and Cambodia resulted in the deaths of 1,1 million South Vietnamese and 2.4 million Cambodians by murder, starvation, deprivation, and drowning in the South China Sea under the brutal rule of Communist regimes. We had won the war, but Congress gave the victory away with disgraceful consequences. (Read full report here.)
Section IV - DEEP DIVES, FILM, HISTORY, POP CULTURE
A history of intelligence failures from Pearl Harbour to 9/11 to the Israel-Gaza war - ABC Australia, 07 Nov 23
While the war in Gaza shows no signs of abating, a big question remains unanswered: How did Hamas manage to take Israel by surprise with its October 7 attack? Despite Israel's formidable intelligence capabilities, Hamas was able to plan and execute the deadliest attack since the country was founded in 1948. Hamas-led militants killed and kidnapped scores of Israelis, and Israel has retaliated with an ongoing war in the Palestinian territory. But history has shown that surprise attacks aren't always a surprise. Warnings are sometimes missed because of institutional mistakes, a lack of coordination or shortcomings in leadership. They are intelligence failures — and there are multiple examples across the globe where these failures have resulted in disaster. (Full report here.)
Surprise Attack: Understanding the Challenges of Intelligence Collection - Foreign Policy Research Institute, 23 Oct 23
The horrors of Hamas’ terrorist attack against Israel on October 7, 2023 are compounded by the shock that Israel’s vaunted intelligence services were seemingly caught unawares after decades of exceptional performance. In this two-part series, the Overheard podcast addresses the challenges of predicting and preventing surprise attacks from the perspectives of intelligence collection, analysis, and interaction with policy makers. In part one, Carol Rollie Flynn, FPRI President and 30 year veteran of the Central Intelligence Agency (CIA), joins Phil Wasielewski to discuss the challenges of intelligence collection to prevent surprise attacks. (Full report here.)
Fireside Chat with DIA Director LTG Berrier - Center for Strategic and International Studies, 01 Nov 23
Please join CSIS for a fireside chat with Lieutenant General Scott Berrier, Director of the Defense Intelligence Agency (DIA). CSIS’s Kari Bingen, Director of the Aerospace Security Program, and Emily Harding, Director of the Intelligence, National Security, and Technology (INT) Program, will join LTG Berrier to discuss geostrategic challenges and how DIA is posturing to meet them. Topics of conversation will include innovation in the intelligence community, the role of DIA in strategic competition with China, and intelligence sharing with partners and allies. (Watch video here.)
Charting China’s Climb as a Leading Global Cyber Power - Insikt Group, 07 Nov 23
Over the past half-decade, Chinese state-sponsored cyber operations have transformed, emerging as a more mature, stealthy, and coordinated threat than in previous years. This new paradigm is exemplified by the widespread exploitation of zero-day and known vulnerabilities in public-facing security and network appliances. It is coupled with a heightened emphasis on operational security, minimizing evidence of intrusion activity, and impeding adversary tracking tradecraft, including through the use of extensive anonymization networks and "living-off-the-land" techniques. These observed shifts have likely been influenced by both internal factors, such as major restructuring within China's military and changes in domestic vulnerability regulations, and external factors, including public reporting and exposures by Western governments and the cyber threat intelligence community. This evolution of Chinese state-sponsored cyber operations toward greater stealth and operational security has created a more complex and challenging landscape for target organizations, governments, and the cybersecurity community. Chinese cyber-enabled economic espionage activity has evolved from earlier practices characterized by the theft of a very broad range of commercial intellectual property. (Read full report here.)
Charted: The Number of North Korean Defectors (1998-2023) - Visual Capitalist, 03 Nov 23
Why are the number of North Korean defectors decreasing? North Korea, formally known as the Democratic People’s Republic of Korea, is a totalitarian dictatorship with extremely limited freedoms and rights reported for its citizens. Due to the country’s tight controls on borders and information, people that want to leave the country often have to physically escape and are known as defectors. These visuals use data from the South Korea’s Ministry of Reunification to track the number of North Korean defectors who make it to South Korea each year, as well as international reporting to explain the dwindling numbers. (View graphic here.)
Intelligence in History - A Collection of Recent Content
- From Secret Agent to Romanov Impostor: The Michael Goleniewski Story - Heart for History, 09 Nov 23
- Cellars of Secrecy: Vintner Peter Sichel’s Double Life As An OSS & CIA Spy - Spyscape, 08 Nov 23
- The IRD at Home - Tom Griffin on Intelligence History, 08 Nov 23
- How a German Spy Chief Built a Smuggling Network Out of a Mission to Install a Nazi King in Britain - Crime Reads, 07 Nov 23
- PX-1000: Pocket telex with encryption - Crypto Museum, 09 Nov 23
- CIA Top Secret Mission To Wiretap Soviet Underwater Cables - The Spy Network, 06 Nov 23
- Stars Under Cover: 12 Celebrities Who Worked as Spies - Wealth of Geeks, 06 Nov 23
- The Old Man and the CIA, Part 1: American Gestapo - SpyScape, 07 Nov 23
- When Wartime Women Triumphed Under Cover - SpyTalk, 09 Nov 23
The Latest from International Spy Museum Historian Andrew Hammond, PhD.
 Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
07 Nov | “Agent of Betrayal, FBI Spy Robert Hanssen” – with CBS’ Major Garrett and Friends. Andrew leads a SPY Museum panel discussion between four experts on the most damaging mole in FBI history, Robert Hanssen. This program was in collaboration with CBS/Paramount on their new podcast “Agent of Betrayal."
True Intelligence Matters in Film - Spycraft, Episode 2: Deadly Poisons - Maria Berry (2021)
 For some covert missions, the goal is not information, but assassination, and lethal toxins have been deployed by spy agencies to kill perceived foes. Netflix.
For some covert missions, the goal is not information, but assassination, and lethal toxins have been deployed by spy agencies to kill perceived foes. Netflix.
More information about this based-on-true-events production here.
Walking Tours - Washington, DC - Sundays (Dates/Times Vary)
Former intelligence officers guide visitors on two morning and afternoon espionage-themed walking tours: "Spies of Embassy Row" and "Spies of Georgetown." For more information and booking, click here or contact rosanna@spyher.co
Section V - Books, Research Requests, Employment, Obituaries
Books — Forthcoming, Newly Released, Overlooked
 Ethics of Spying: A Reader for the Intelligence Professional (Volume 3) (Security and Professional Intelligence Education Series, Volume 3) –
Ethics of Spying: A Reader for the Intelligence Professional (Volume 3) (Security and Professional Intelligence Education Series, Volume 3) –
by Jan Goldman
(Rowman and Littlefield Publishers, 15 Nov 23)
The first volume introduced readers to ethics in intelligence operations. Published when the U.S. was conducting operations in the post-9/11 era, this book represents the first collection of articles to seriously study ethics for and about intelligence professionals. The second volume established the codes of conduct that professionals in the private and public sectors would employ that could be separate from those of their private lives. Ethics of Spying: A Reader for the Intelligence Professional, Volume 3 combines the best articles from the first two volumes. It’s reorganized into 5 parts, and it contains new articles that expand and explain further the meaning and dichotomy of a working professional in the intelligence community and the national security and civil liberties they are entrusted with safeguarding. New articles include Ethics of Human Intelligence Operations; Tension and Strategy: : Ethics Phobia; Tension and Strategy: Sources and Bypassing Strategies; Just Intelligence Theory; Ethics, Intelligence, and Preemptive and Preventive Actions; Speak No Evil; Using Private Corporations to Conduct Intelligence Activities for National Security Purposes; and Intelligence Research and Scholarship
Order book here.
 The Birth of the Soviet Secret Police: Lenin and History's Greatest Heist, 1917-1927 (A New History of the KGB)
The Birth of the Soviet Secret Police: Lenin and History's Greatest Heist, 1917-1927 (A New History of the KGB)
by Boris Volodarsky
(Frontline Books, 31 May 23)
This book is new in every aspect and not only because neither the official history nor an unofficial history of the KGB, and its many predecessors and successors, exists in any language. In this volume, the author deals with the origins of the KGB from the Tsarist Okhrana (the first Russians secret political police) to the OGPU, Joint State Political Directorate, one of the KGB predecessors between 1923 and 1934. Based on documents from the Russian archives, the author clearly demonstrates that the Cheka and GPU/OPGU were initially created to defend the revolution and not for espionage. The Okhrana operated in both the Russian Empire and abroad against the revolutionaries and most of its operations, presented in this book, are little known. The same is the case with regards to the period after the Cheka was established in December 1917 until ten years later when Trotsky was expelled from the Communist Party and exiled, and Stalin rose to power. For the long period after the Revolution and up to the Second World War (and, indeed, beyond until the death of Stalin) the Cheka’s main weapon was terror to create a general climate of fear in a population. In the book, the work of the Cheka and its successors against the enemies of the revolution is paralleled with British and American operations against the Soviets inside and outside of Russia. For the first time the creation of the Communist International (Comintern) is shown as an alternative Soviet espionage organization for wide-scale foreign propaganda and subversion operations based on the new revelations from the Soviet archives. Here, the early Soviet intelligence operations in several countries are presented and analyzed for the first time, as are raids on the Soviet missions abroad. The Bolshevik smuggling of the Russian imperial treasures is shown based on the latest available archival sources with misinterpretations and sometimes false interpretations in existing literature revised. After the Bolshevik revolution, Mansfield Smith-Cumming, the first chief of SIS, undertook to set up ‘an entirely new Secret Service organization in Russia’. During those first ten years, events would develop as a non-stop struggle between British intelligence, within Russia and abroad, and the Cheka, later GPU/OGPU. Before several show ‘spy trials’ in 1927, British intelligence networks successfully operated in Russia later moving to the Baltic capitals, Finland and Sweden while young Soviet intelligence officers moved to London, Paris, Berlin and Constantinople. Many of those operations, from both sides, are presented in the book for the first time in this ground-breaking study of the dark world of the KGB
Order book here.
 Intelligence as Democratic Statecraft: Accountability and Governance of Civil-Intelligence Relations Across the Five Eyes Security Community - the United Kingdom, Canada, Australia, and New Zealand
Intelligence as Democratic Statecraft: Accountability and Governance of Civil-Intelligence Relations Across the Five Eyes Security Community - the United Kingdom, Canada, Australia, and New Zealand
by Christian Leuprecht and Hayley McNorton
(Oxford University Press, 16 Nov 21)
This book features a comparative study in intelligence accountability and governance across the Five Eyes: the imperative for member countries of the world's most powerful intelligence alliance to reconcile democracy and security through transparent standards, guidelines, legal frameworks, executive directives, and international law. It argues that intelligence accountability is best understood not as an end in itself but as a means that is integral democratic governance. On the one hand, to assure the executive of government and the public that the activities of intelligence agencies are lawful and, if not, to identify breaches in compliance. On the other hand, to raise awareness of and appreciation for the intelligence function, and whether it is being carried out in the most effective, efficient, and innovative way possible to achieve its objective. The analysis shows how the addition of legislative and judicial components to executive and administrative accountability has been shaping evolving institutions, composition, practices, characteristics, and cultures of intelligence oversight and review in the United States, the United Kingdom, Canada, Australia, and New Zealand using a most-similar systems design. Democracies are engaged in an asymmetric struggle against unprincipled adversaries. Technological change is enabling unprecedented social and political disruption. These threat vectors have significantly affected, altered, and expanded the role, powers and capabilities of intelligence organizations. Accountability aims to reassure skeptics that intelligence and security practices are indeed aligned with the rules and values that democracies claim to defend.
Order book here.
Research Requests and Academic Opportunities
Call for Interviews: Alex W. Palmer, a contributing writer at The New York Times Magazine, is working on a book about the history of American intelligence on China. He's looking to speak with any intelligence officers who worked in or on China during their career, from whatever timeframe and in whatever role. He can be reached at alex.palmer@nytimes.com and +1-262-894-7160 on Signal.
Call for Information: Dr. Andrew Hammond and Dr. Mark Stout are seeking interviewees for a journal article on the CIA’s Office of Soviet Analysis (SOVA). The final output will be based on oral history interviews which can be (a) on-the-record (b) off-the-record or (c) utilizing a pseudonym. The data will be used for this project only and thereafter destroyed. Our aim is to understand how people who served in SOVA or who worked alongside SOVA made sense of it: what was it like, what was its culture, what were its strengths and weaknesses, how did it relate to the rest of the CIA and other agencies, is there anything we can learn from SOVA re the new era of Great Power Conflict, etc.? If you served in SOVA during the period 1981 to 1992 and would like to be interviewed, please contact Dr. Andrew Hammond at ahammond@spymuseum.org.
Call for Information: Seeking information on Al "Albert" Purdum, stationed at Arlington Hall 55, Defense Language School - Albanian 55-56, NSA Linguist, Sr. Cryptologist 57-95. Looking for colleagues or friends who knew him, of him. Researching Role of National Security Linguists and Foreign Affairs. Contact cristina.purdum@gmail.com.
Call for Information: Seeking information on Octavio Bermudez, State/Commerce Attache Latin America Crosley Broadcasting- 1922-1942. Sources needed - Passenger list of Hoover's 1928 Good Will Tour, Details/objectives by country, 25 year agreement with Ecuador to build broadcast station in Quito- role in Open Source Enterprise, WWII locating Axis Spies, American Propaganda/Spy Communication Network. 41-46 OCIAA propaganda, embedded code/scripts for broadcast, hand delivered to Crosley, Cincinnati - the only fenced compound, with 24 hr. armed guards, watch tower. Researching Role of Foreign Service Attaches - Development of American Broadcasting Capabilities pre WWII in Latin America. Contact cristina.purdum@gmail.com.
Call for Information: Author drafting a book on the Clinton administration seeks contact with the person who served as COS Manila in November 1996 for the purpose of background research. Members who can identify the COS and/or are in contact with him, please forward this request to the COS or contact the author. Responses may be sent to dpluchinsky@rocketmail.com.
Call for Information: Seeking information on, Sgt Major Charles “Chuck” Remagen, assigned to MACV/SOG in Vietnam 67-68. Seek details about his role as a Sgt Major with MACV “Studies and Observations Group in Vietnam 7/1/67 to 1/21/68. Responses may be sent to magen@hotmail.com.
Call for Sources: Intelligence activities in Grenada and the southern Caribbean between 1979, Operation Urgent Fury, Leonard Barrett
The Washington Post is developing a multi-part audio documentary series (i.e. podcast) chronicling the Grenadian revolution and the US intervention in 1983. They've interviewed nearly 100 people so far, ranging from the heads of state, former Grenadian officials, current and former US officials, veterans, and intelligence officers. They're looking for people who served at the time and may be knowledgeable about intelligence activities in Grenada and the southern Caribbean between 1979 and Operation Urgent Fury. They would also be interested in speaking with anyone who knew Leonard Barrett during the same period. If anyone is interested in participating, please reach out to Washington Post reporter Ted Muldoon via email at ted.muldoon@washpost.com or on Signal at 651-497-5449.
Call For Articles: AFIO Journal, The Intelligencer
AFIO is seeking authors for its section on "When Intelligence Made a Difference" in the semi-annual Intelligencer journal. Topics of interest for which we are seeking authors include:
• The Richard Sorge espionage ring in Tokyo in World War II and
the impact of his intelligence on Stalin and the battle for Moscow.
• How Rommel’s Afrika Korps used SIGINT against the British in
World War II.
• How A.Q. Khan’s nuclear proliferation efforts were uncovered
and stopped.
• The breaking of the Nazi U-boat SHARK encryption system.
• How US intelligence found Usama Bin Laden in Abbottobad, Pakistan.
• How allied SIGINT isolated the Afrika Korps from its logistics chain.
• How US intelligence discovered the Soviet’s high speed Shkval torpedo.
• Intelligence and the rescue of Scott O’Grady.
• Other topics are also welcome.
Interested authors please contact Peter Oleson, senior editor The Intelligencer, at peter.oleson@afio.com
Jobs
Assistant/Associate Professor of Intelligence Studies (Global Security and Intelligence Studies) - Embry-Riddle Aeronautical University - Prescott, Arizona
Embry-Riddle Aeronautical University's Prescott, Arizona campus is accepting applications for a tenure-track assistant or associate-level professor of intelligence studies to teach intelligence courses to students in the Global Security and Intelligence program. The successful candidate will teach students about the intelligence community, strategic intelligence, the intelligence cycle and intelligence analysis, writing, and briefing. Prior experience working in the intelligence community is strongly preferred. We are interested in candidates with teaching acumen in intelligence analysis and writing using structured analytical techniques.
Additional information and application here.
Obituaries
![]() Jack Lee — Career CIA Officer and Former AFIO Florida Chapter Officer
Jack Lee — Career CIA Officer and Former AFIO Florida Chapter Officer
John F. (Jack) Lee, 88, longtime resident of Viera, FL passed away peacefully on Monday, November 6, 2023. Jack was born in Philadelphia, PA. He graduated from La Salle College High School in Philadelphia, served in the United States Army for three years, and graduated from Middlebury College with a degree in Russian studies. He then served honorably for 34 years in the CIA's Directorate of Operations in 5 countries. A committed teacher, he helped train the next generation of case officers after retirement from CIA. He was grateful to have visited all seven continents and was a long-time Vice President of the Satellite Chapter of the Association of Former Intelligence Officers (AFIO). His impact on the lives of those who knew him was profound. His bloodline reaches back to the beginning…his kin signed the American Declaration of Independence. His standard was the highest, and his character was beyond exemplary. His service to America has endured longer than most human beings have been alive.
No nearterm events.
See the AFIO Calendar of Events for scheduling further in the future.
Events from Advertisers, Corporate Sponsors, Others
15 Nov 23, 1200-1300 (ET) - Virtual - Geospatial Intelligence: Tracking China's Nuclear Program - Johns Hopkins University
Join host Michael Ard for a curated conversation with Renny Babiarz, a Chinese nuclear weapons specialist and geospatial intelligence analyst. This talk explores general connections between geopolitics and geospatial disciplines, and then specifically shows how geospatial analysis can lead to important geopolitical developments. One common example of such a connection is the Cuban Missile Crisis, which blossomed into a crisis because CIA imagery analysts discovered ballistic missile bases under construction in Cuba. This led to a dramatic geopolitical confrontation between the U.S. and the Soviet Union. Today, some of the world's most important geopolitical issues remain rooted in our knowledge of developments at specific locations on the earth. For example, recent developments at China's Lop Nur Nuclear Weapons Test Site suggest a dramatically new era of nuclear weapon testing and development is about to begin. This would have profound implications not only for geopolitics, but for life itself on Earth. Renny Babiarz is vice president of analysis and operations for AllSource Analysis, where he manages geospatial intelligence analysis projects on security, economic, and artificial intelligence issues for government, non-government, and private-sector customers. He is also an adjunct faculty member for the Johns Hopkins MS in Geospatial Intelligence program. Babiarz has over 20 years of experience researching China’s political and military systems, including 10 years of experience in the field of GEOINT analysis focusing on Asia and weapons of mass destruction. He has a PhD in political science, specializing in China's nuclear weapons program, from Johns Hopkins University; an MA in Asian studies, specializing in China, from University of Hawaii at Manoa; and certificates in Chinese language and GEOINT analysis. Additionally, Babiarz worked in public service as a GEOINT analyst for the National Geospatial-Intelligence Agency. (More details and registration here.)
28 November 2023, 5 - 6pm EST - Washington, DC - IWP hosts IN-PERSON book presentation by Dr John Gentry on "The Politicization of U.S. Intelligence: Causes and Consequences"
 The Institute of World Politics invites you to attend an IN-PERSON book lecture by Dr. John Gentry, Author and Professor at the School of Defense and Strategic Studies, Missouri State University, discussing "The Politicization of U.S. Intelligence: Causes and Consequences."
The Institute of World Politics invites you to attend an IN-PERSON book lecture by Dr. John Gentry, Author and Professor at the School of Defense and Strategic Studies, Missouri State University, discussing "The Politicization of U.S. Intelligence: Causes and Consequences."
"The Politicization of U.S. Intelligence: Causes and Consequences” is a presentation in association with Dr. Gentry's recent book, Neutering the CIA: Why US Intelligence Versus Trump Has Long-Term Consequences (Armin Lear Press, 2023). Beginning in 2016 and continuing into 2021, current and former U.S. intelligence officers engaged in domestic partisan politics to an unprecedented extent. This discussion will describe and assess what happened at various agencies, the causes of the politicization, consequences for the agencies and national decision-making, and prospects for renewed politicization in 2024.
***Copies of Dr. Gentry's book will be made available for purchase at the conclusion of the event and can be signed by the author.*** ***This lecture is sponsored by the IWP IAFIE Alpha Student Chapter***
Location: The Institute of World Politics, 1521 16th St NW, Washington, DC 20036.
28 and 30 Nov 23, 1400-1500 (ET) - Virtual - SPY with Me: Program for Individuals with Dementia and their Care Partners - International Spy Museum
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. Free but space is limited. To register, please email Shana Oltmans at soltmans@spymuseum.org. Visit www.spymuseum.org.
14 - 25 April 2024 - Gary Powers' Cold War Espionage Tour of Austria, the Czech Republic, Slovakia & Hungary - Travel Dates: April 14 to 25,2024 - 12 days/10 nights
Join author & historian Gary Powers Jr. on this 12-day tour of Cold War and espionage related sites in Austria, the Czech Republic, Slovakia & HungaryThe deadline to enroll is 11/30/23 with a required deposit of $495. Final payment is due 12/30/23.
What's Included: • Round-trip air transportation from Washington, DC; • 10 nights in centrally located, four-star hotels; • Full-time CHA Tour Director; • Valuable insight & informative commentary by Gary Powers Jr.; • On-tour transportation by private motorcoach; • Breakfast & dinner (or lunch) daily; • Sightseeing tours & visits shown in itinerary (subject to change based on availability)
Tour Prices: Full Tour Price: $5,695 per person; Land Tour Price: $4,645 per person (does not include round-trip airfare and airport transfers); Repeat Gary Powers travelers will receive a $200 discount! Price based on double occupancy.
A $600 single room fee will apply for travelers without roommates.
The deadline to enroll is 11/30/23 with a required deposit of $495. Final payment is due 12/30/23.
Questions? Call 1-800-323-4466 or email info@cha-tours.com.
Enroll Online at: www.cha-tours.com/GaryPowers
 NEW Gray long-sleeved polo shirts with embroidered AFIO logo. Men's sizes only.
NEW Gray long-sleeved polo shirts with embroidered AFIO logo. Men's sizes only.
Show your support for AFIO with our new Gray Long-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $60 each including shipping.
Sizes for men, only: Small, Medium, Large, XL, XXL, and XXXL. $60 per shirt. Order this and other store items online here.
 NEW 20 oz ceramic Mug with color glazed logo. Made in America. Check out our new tapered, sleek AFIO coffee mug!! This handsome 20 oz. ceramic mug is made in the USA, has a white matte exterior, sports a beautiful navy-blue interior, and is dishwasher safe. Order yours today! $35 per mug includes shipping to a CONUS address. [includes shipping to U.S. based address, only. For foreign shipments, we will contact you with a quote.] SHIPPING: For shipment to a U.S.-based CONUS address, shipping is included in price. For purchases going to AK, HI, other US territories, Canada, or other foreign countries the shipping fees need to be calculated, so please call our office M-F 8 a.m. to 2 p.m. ET at 703-790-0320 or email afio@afio.com providing following information: 1) your name, 2) mailing address (or addresses where each gift item will be shipped), 3) name of the AFIO store items you wish to purchase, 4) quantity of each, 5) your credit card number and expiration date, 6) amount (except for additional of shipping fees) authorized to charge, and 7) your phone number and email should we have questions. Foreign shipments fees will be calculated and estimates emailed to you, awaiting your approval. Order this and other store items online here.
NEW 20 oz ceramic Mug with color glazed logo. Made in America. Check out our new tapered, sleek AFIO coffee mug!! This handsome 20 oz. ceramic mug is made in the USA, has a white matte exterior, sports a beautiful navy-blue interior, and is dishwasher safe. Order yours today! $35 per mug includes shipping to a CONUS address. [includes shipping to U.S. based address, only. For foreign shipments, we will contact you with a quote.] SHIPPING: For shipment to a U.S.-based CONUS address, shipping is included in price. For purchases going to AK, HI, other US territories, Canada, or other foreign countries the shipping fees need to be calculated, so please call our office M-F 8 a.m. to 2 p.m. ET at 703-790-0320 or email afio@afio.com providing following information: 1) your name, 2) mailing address (or addresses where each gift item will be shipped), 3) name of the AFIO store items you wish to purchase, 4) quantity of each, 5) your credit card number and expiration date, 6) amount (except for additional of shipping fees) authorized to charge, and 7) your phone number and email should we have questions. Foreign shipments fees will be calculated and estimates emailed to you, awaiting your approval. Order this and other store items online here.
 Black short-sleeved polo shirts with Embroidered AFIO logo
Black short-sleeved polo shirts with Embroidered AFIO logo
Show your support for AFIO with our new Black Short-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $50 each including shipping.
Sizes for (M) men, only; Small, Medium, Large, XL, XXL, and XXXL. $50 per shirt.
You may pay by check or credit card. Complete your order online here or mail an order along with payment to: AFIO, 7600 Leesburg Pike, Ste 470 East, Falls Church, VA 22043-2004. Phone orders at 703-790-0320. Questions? Contact Annette at: annettej@afio.com.

PopSocket for cellphones or tablets
Show your support to AFIO while enjoying the convenience offered by our AFIO Logo PopSocket. The PopSocket is most commonly used as a stand and as a grip for your mobile phone or tablet; handy for taking selfies, watching videos, and for texting. The PopSocket looks like a small button or sticker which, when closed, sticks flat to your mobile device. However, its accordion-like design enables it to pop open for use. The benefits of using a PopSocket make it a must-have accessory for your mobile phone or tablet. It also aids in keeping your phone from slipping off your hand during use, falling, or breaking.
Price: $15. Order this and other store items online here.

Duffel Bags - Royal Blue and Black with Full Color AFIO Logo This duffel has it all when it comes to value, style and organization.
600 denier polyester canvas with polyester double contrast; D-shaped zippered entry for easy access. Front pocket with hook and loop closure. End mesh pocket Easy-access end pockets. Four durable, protective feet and built-in bottom board for added strength. Web handles with padded grip. Detachable, adjustable shoulder strap.
Dimensions: 11"h x 19.75"w x 9.75"d; Approx. 2,118 cubic inches
Price: $50. Order this and other store items online here.

Caps - Dark Navy with Navy AFIO Logo
An authentic silhouette with the comfort of an unstructured, adjustable fit. Fabric: 100% cotton. Unstructured. Fabric strap closure with adjustable D-clip. Price: $30. Order this and other store items online here.
| PUBLISHED
IN 2023 Be informed on career opportunities in the U.S. Intelligence Community |
||
 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. AFIO's popular 47-page booklet reaches thousands of high school, college students, university guidance offices, and distributed in classes teaching intelligence, to help those considering careers in the U.S. Intelligence Community. |
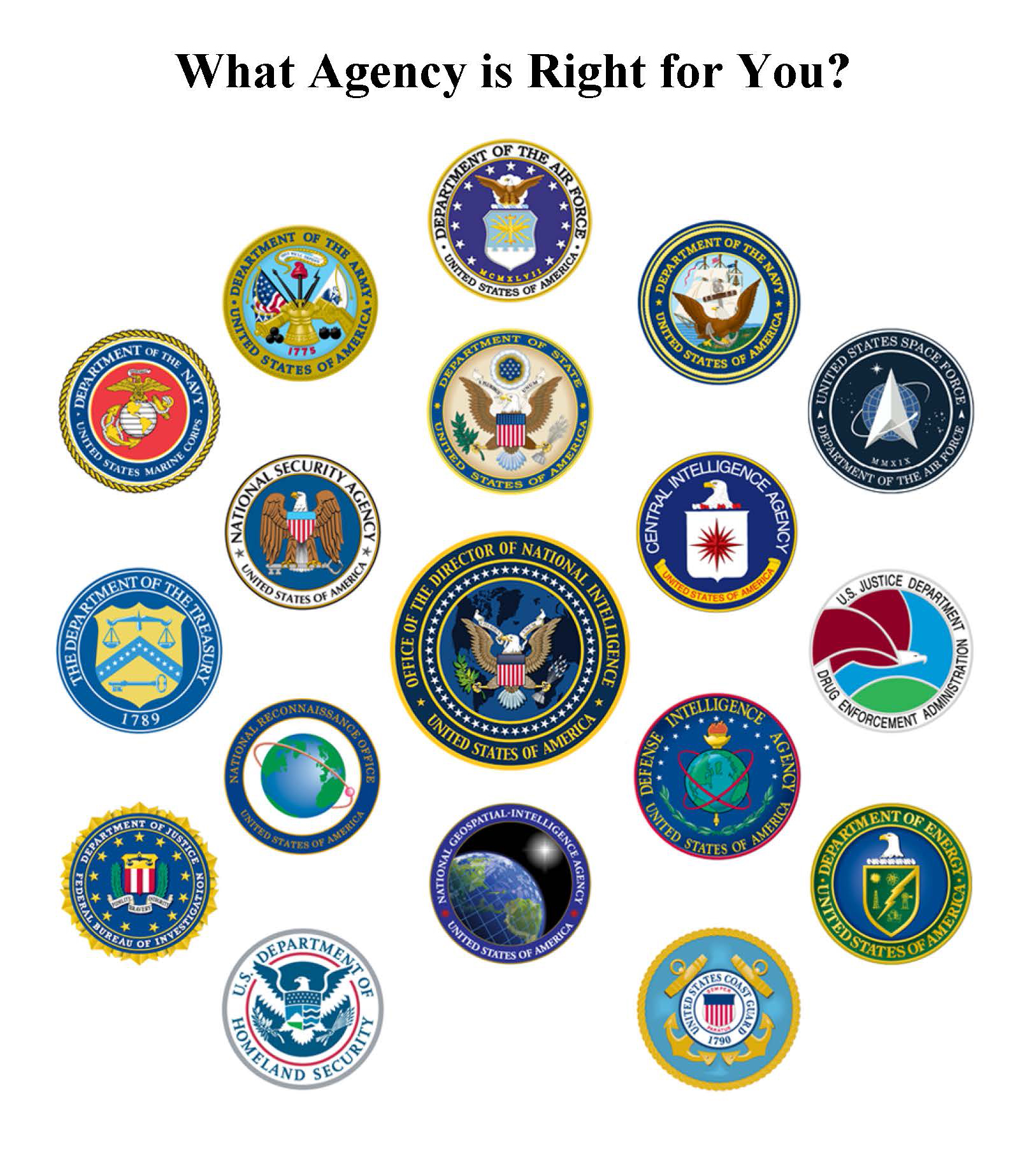 |
| This is the all new fifth edition. The publication is also popular with University Career Guidance Centers, professors and academic departments specializing in national security, and parents assisting children or grandchildren in choosing meaningful, public service careers. This booklet is provided online as a public service from the generosity of AFIO board, volunteer editors/writers, donors, and members. We thank all for their support which makes this educational effort possible. |
||
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |
||
 Guide to the Study of Intelligence...and...When Intelligence Made a Difference
Guide to the Study of Intelligence...and...When Intelligence Made a Difference
"AFIO's Guide to the Study of Intelligence" has sold out in hard-copy.
It is available in digital form in its entirety on the
AFIO website here.
Also available on the website here are the individual articles of AFIO's
history project "When Intelligence Made a Difference" that have been
published to date in The Intelligencer journal.
More articles will be appear in future editions.
Some features of the email version of the WIN do not work for readers who have chosen the Plaintext Edition, some AOL users, and readers who access their email using web mail. You may request to change from Plaintext to HTML format here afio@afio.com. For the best reading experience, the latest web edition can be found here: https://www.afio.com/pages/currentwin.htm
To unsubscribe from the WIN email list, please click the "UNSUBSCRIBE" link at the bottom of the email. If you did not subscribe to the WIN and are not a member, you received this product from a third party in violation of AFIO policy. Please forward to afio@afio.com the entire message that you received and we will remove the sender from our membership and distribution lists.
(c) 1998 thru 2023
AFIO Members Support the AFIO Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for back issues of the WINs, information about AFIO, conference agenda and registrations materials, and membership applications and much more! .
AFIO | 7600 Leesburg Pike, Suite 470 East, Falls Church, VA 22043-2004 | (703) 790-0320 (phone) | (703) 991-1278 (fax) | afio@afio.com