22 - 28 February 2023 — (Issue 09)
is sponsored by

Readers who encounter problems with the email version of this newsletter can
view the latest web edition here
| Visit us on |
CONTENTS
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
- China Protests US Surveillance Plane's Taiwan Strait Flight - Military.com, 27 Feb 23
- NASA keeps an eye on China — from the space above Mars - Mashable, 25 Feb 23
- NSA's National Security Operations Center celebrates 50 years of 24/7 operations in service to the Nation - NSA, 21 Feb 23
- Belgium on High Alert as Russian 'Spy Ship' Detected in North Sea - Marine Link, 22 Feb 23
- Fake Russian diplomats revealed as heart of ‘hive’ spy ring in Australia - Sydney Morning Herald, 23 Feb 23
- A U-2 Pilot Took This Selfie With the Chinese Spy Balloon. It's Astonishing. - Popular Mechanics, 22 Feb 23
- NSA’s “state secrets” defense kills lawsuit challenging Internet surveillance - Arstechnica, 22 Feb 23
- China, Russia targeting Canada's artificial intelligence know-how, CSIS warns - Toronto Sun, 22 Feb 23
- Classified documents show up in odd places, portraying sloppy system beyond Trump, Pence, Biden - USA Today, 23 Feb 23
- China’s secret police actively hunting people on US soil - New York Post, 25 Feb 23
- The stories of Ukrainian citizens who formed espionage cells to help liberate Kherson - NPR, 22 Feb Jan 23
- Dutch intelligence: Many cyberattacks by Russia are not yet public knowledge - The Record, 22 Feb 23
- Cyber Intelligence Coordination Within the Department of Homeland Security - Lawfare, 24 Feb 23
- Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
- Marking One Year of War in Ukraine: State Department Counselor Derek Chollet — Former Acting CIA Director Mike Morell, Intelligence Matters
- "The Espionage News Cycle" - A Conversation with SPY's Aliza Bran — Andrew Hammond, PhD. SpyCast
- History will look back at the Russian invasion of Ukraine -- that took place a year ago today -- and say that this was a defining inflection point in global realignment. — Former Acting CIA Dep. Dir. for Ops and Arkin Group President Jack Devine, In Other News
- Support for Ukraine’s Displaced, Shamima Begum (Balancing Security, Humanitarian Concerns, Accountability), How the Ukraine War Shaped the Global Order, China Bolsters Russian Disinformation on Ukraine, UK Branding Wagner Group as Terrorists? — Former FBI Special Agent and Soufan Group CEO Ali Soufan, Intel Brief
- Chinese Spy Balloon, Russian and Iranian Hackers, Fighting Disinformation, Struggle in Turkey and Syria, Is Social Media Driving Mass Violence?, and more... — WTOP National Security Correspondent JJ Green - Inside the SCIF, Target USA, The Hunt
- Afghan Treachery and Kabul's Collapse, FDR’S Female Secret Agent Wore Two Hats, and A Final Word on Balloongate - Jeff Stein and Colleagues in SpyTalk (Substack)
Section III - MEMBER CONTRIBUTIONS
- Article: Russia covertly mapping key energy infrastructure for sabotage, Dutch report warns - Intel News, 21 Feb 23
- Information Sheet: Best Practices for Securing Your Home Network - NSA, 22 Feb 22
- Online Exhibit: Project AZORIAN - CIA, 24 Feb 23
- Book Recommendation: Terrorist Events Worldwide 2022 - Edward Mickolous, 21 Feb 23
- Exclusive: Lab Leak Most Likely Origin of Covid-19 Pandemic, Energy Department Now Says - Wall Street Journal, 26 Feb 23
- Article: The West’s next challenge: Russian spy ops beyond Ukraine - The Hill, 23 Feb 23
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
- Audio: Is cyberespionage actually signals intelligence? (30 mins) - Between Two Nerds, 21 Feb 23
- Audio: CSIS Documents Reveal a Web of Chinese Influence in Canada (23 mins) - The Decibel, 27 Feb 23
- Audio: An interview with Andrew Boyd, director of the CIA's Centre for Cyber Intelligence (53 mins) - Risky.biz, 23 Feb 23
- OpEd: South Africa’s intelligence agency needs speedy reform - or it must be shut down - The Conversation, 24 Feb 23
- Analysis: The Global Footprint of Chinese Cyber Warfare and Espionage - Modern Diplomacy, 20 Feb 23
- Report: The troubled international situation increases the threat to the security of Sweden - Swedish Security Service, 22 Feb 23
- Report: Director-General's Annual Threat Assessment - Australian Security Intelligence Organization, 21 Feb 23
- Tribute: Remembering the Life and Legacy of CIA Trailblazer Don Cryer - CIA, 21 Feb 23
- OpEd: The new era of counterintelligence must shift focus to the gray zone - The Hill, 23 Feb 23
- Paper: Critical Intelligence Studies - A new framework for analysis - Intelligence and National Security Journal, 21 Feb 23
- Report: Russia’s War in Ukraine - Military and Intelligence Aspects - Congressional Research Service, 13 Feb 23
- Analysis: Sri Lanka’s Intelligence Agencies - Debunking the Pseudo-Nationalist Narrative - Sri Lankan Guardian, 24 Feb 23
- Infographic and Report: Ranked - Biotoxins in Nature, by Lethal Dose - Visual Capitalist, 24 Feb 23
- Intelligence in History - A Collection of Recent Content
- True Intelligence Matters in Film: The Iron Curtain - Director William A. Wellman (1948)
- Intelligence in Pop Culture - Poem - Reflections on Espionage: The Question of Cupcake - John Hollander (1974, 1999)
- Walking Tours: The Spies of Embassy Row and Spies of Georgetown - Washington, DC. (Sundays, Dates/Times Vary)
Section V - Books, Research Requests, Academic Opportunities, Jobs, Obituaries
Books — Forthcoming, New Releases, Overlooked
- Before Bletchley Park: The Codebreakers of the First World War by Paul Gannon
- We Were Never There: Volume 1: CIA U-2 Operations over Europe, USSR, and the Middle East, 1956-1960 by Kevin Wright
- Agent Zigzag: A True Story of Nazi Espionage, Love, and Betrayal by Ben Macintyre
Research Requests and Academic Opportunities
- Academic Opportunity: Critical Thinking for Intelligence Analysis Course (21 Apr 23, 0800-1700 (ET) - The Intelligence and Security Academy - Virtual
- Academic Opportunity: The International Security and Intelligence Programme (9 July - 5 August 2023) - Magdalene College, Cambridge
- Call For Papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
- Search For Stories: of encounters with China's civilian and military intelligence apparatus.
- Search For Information: on CIA gallantry award recipients Bob A. Plan and Arthur J. Porn.
- Search For Information: on CIA operation against Iran in late 1990s and bomb found during President Clinton visit to Philippines in 1996
- Search For Information: on the adverse effects of diversity, equity, and inclusion on intelligence
- Search For Information: on non-OSS, pre-CIA, civilian US intelligence activity
- Call For Papers: Israel Affairs - "The Struggle in the Israeli Security Zone in South Lebanon, 1985-2000" (30 Mar 23 deadline)
- Search for French Intel Officer: who was in touch with journalist William Reymond.
- Search for Colleagues: Tom Lane and Nancy Kenealy sought for collaboration on book.
- Call For Information: Harvard Undergraduate Student and Researcher Seeks Primary source documents, historical records, or points of contact regarding Freedom Company, aka Eastern Construction Company, of the Philippines
- Call For Articles: AFIO Journal, The Intelligencer
- Call For Assistance: Researcher Seeks Copy of 1941 FBI Booklet
- Faculty Opening - Adjunct Faculty, Intelligence Analysis - Krieger School of Arts and Sciences, Johns Hopkins University, Online
- Faculty Opening - Teaching Intelligence Analysis - James Madison University, Harrisonburg, VA
- Intelligence Practice Lead - SOS International, Washington, D.C.
- Supervisory Criminal Investigator (Special Agent-In-Charge) - U.S. Army CID, Nationwide
- Retired Federal Government Employees Wanted - National Security Agency, Fort Meade, MD
- Assistant Professor - Intelligence Studies (Global Security and Intelligence Studies), Embry-Riddle Aeronautical University - Prescott, Arizona
- Teaching Associate - Intelligence and National Security Studies, Coastal Carolina University, Conway, South Carolina
- Assistant Professor - Intelligence and National Security Studies - University of Texas, El Paso
- Jim Lynch, Senior CIA Researcher and Multi-Directorate Leader
- Catherine Kelleher, Former DAS Defense and National Security Leader in Academia and Government
- Barbara Shortley, Career CIA Operations Officer, Trailblazer
- Richard Rentz, CIA Communicator and Honorable Service Award Holder
- 02 Mar 23 (Thursday), 1900 (CT) - Virtual via Zoom - AFIO San Antonio hosts Zbigniew Wojcik, author of "Slaying the Soviet Beast" on Communist Chinese Party infiltration of western technical, educational, and research organizations - San Antonio TX Chapter
- 16 Mar 23 (Thursday), 1130 (MST) - In Person - Colorado Springs David Humpert discussing "1983 The Year of Maximum Danger" - Rocky Mountain CO Chapter
- 13 Apr 23 (Thursday), 1130 (PST) - In Person - San Francisco - CAPT Richard E. Hanson on CIA Operations in Viet Nam - Andre LeGallo Chapter
Events from Advertisers, Corporate Sponsors, Others
- 28 Feb 23, 1400-1500 (ET) SPY with Me: Memory Loss Program – International Spy Museum - Virtual
- 01 Mar 23, 1200 - 1300 (ET) The Ukraine Conflict One Year Later: An Intelligence Perspective - Johns Hopkins University – Virtual
- 02 Mar 23, 1200 (ET) – Virtual Spy Chat with Chris Costa ft. Special Guest: Alan E. Kohler, Jr. – International Spy Museum Program - Virtual
- 03 Mar 23, 1700-2000 (ET) – SPY Community Night: Ward 006 – International Spy Museum Program - In Person - Washington, DC
- 08 Mar 23, 1200 (ET) – The Double Life of Katharine Clark – International Spy Museum Program - Virtual
- 13 Mar 23, 1700 - 1800 (ET) Publishing with Intelligence - Institute of World Politics – Virtual
- 14 Mar 23, 0900 - 0945 (ET) Coffee and Conversation with DIA China Mission Group Chief Doug Wade - INSA – Virtual
- 15 Mar 23, 1200 (ET) – Intro to MASINT with Peter Humphrey – International Spy Museum Program - Virtual
- 18 Mar 23, 1400-1600 (ET) – Book Signing Event with Jonna Mendez – International Spy Museum - In Person – Washington, DC
- 19 - 28 Mar 23 - Gary Powers' 10-Day Cold War Espionage Tour - In-person, Washington DC to Europe and back
- 24 Mar 23, 1200 (ET) – Sidney Reilly: Master Spy with Benny Morris – International Spy Museum Program - Virtual
- 27 Mar 23, 1830 (ET) – Red London with Alma Katsu – International Spy Museum Program - Virtual
- 28 Mar 23, 1400-1500 (ET) – SPY with Me: Memory Loss Program – International Spy Museum Program - Virtual
- 29 Mar 23, 0900-1700 (ET) – How Wars End: A Conference Presented by the Pardee Center for the Study of the Longer-Range Future – Boston University - In Person
- 30 Mar 23, 1400-1500 (ET) – SPY with Me: Memory Loss Program – International Spy Museum Program - Virtual
- 13-14 Jul 23 2023 Intelligence and Security Summit – AFCEA/INSA - In Person - National Harbor, MD
See the AFIO Calendar of Events for scheduling further in the future.
National OSINT Day Proclamation
The membership of the OSINT Foundation, the professional association of U.S. Intelligence Community open-source intelligence (OSINT) practitioners, has voted in favor of establishing an annual day of recognition for the OSINT discipline. In recognition of the contributions made to the national security of the United States by OSINT practitioners and the OSINT discipline, the Foundation has designated February 26th as National OSINT Day. To properly contextualize the long history of the discipline, the date was chosen in commemoration of the formal establishment of the Foreign Broadcast Monitoring Service (FBMS) on February 26, 1941. FBMS was established by President Franklin Delano Roosevelt as part of the Federal Communications Commission (FCC) which became the Foreign Broadcast Intelligence Service in July 1942, and subsequently the Foreign Broadcast Information Service in November of 1946.1 In addition to broadcast media, early OSINT practitioners also exploited print media in support of the war effort via the Interdepartmental Committee for the Acquisition of Foreign Publications (IDC) of the Library of Congress, which was proposed by Major General William “Wild Bill” Donovan, Director of the Office of Strategic Services (OSS) on December 22, 1941.2 The IDC, in partnership with the OSS was instrumental not only in exploiting hardcopy publicly available information, but also helped to restore looted works to affected nations, and greatly expanded the international holdings of the Library of Congress and academic libraries across the nation. Barbara Alexander, President of the OSINT Foundation stated, “In recognition of 82 years of continuous vigilance in defense of the nation, we are honored to proclaim February 26, 2023, as National OSINT Day.”
LATEST FROM AFIO
The AFIO Board of Directors is pleased to announce the following were recently added as Director Emeriti for many years of selfless service on the AFIO National Board:
• Sarah L. BOTSAI, PhD — She was with the National Security Agency and is recognized by NSA and in the National Cryptologic Museum as "...one of the leading Women in American Cryptology." She is a Charter Member, Senior Cryptologic Executive Service; served as Deputy Director, White House Situation Room; Intelligence Community Staff; Cryptologic Advisor, USCINCPAC; Faculty, National War College.
• Martin C. FAGA — Retired in 2006 as president, CEO of MITRE. Before MITRE, he served as Assistant Secretary of the Air Force for Space and served as Director of the National Reconnaissance Office (NRO), reporting to the SECDEF and the Director of CIA for the development, acquisition and operation of all US satellite reconnaissance programs.
• Michael J. ROGERS, The Honorable — He is a former member of Congress, was an officer in the U.S. Army, and served as a FBI Special Agent. He chaired the House Permanent Select Committee on Intelligence (HPSCI) and was a member of the Energy and Commerce panel.
Full bios of the above and of all current board members may be viewed here.
Released exclusively to members 21 February 2023...
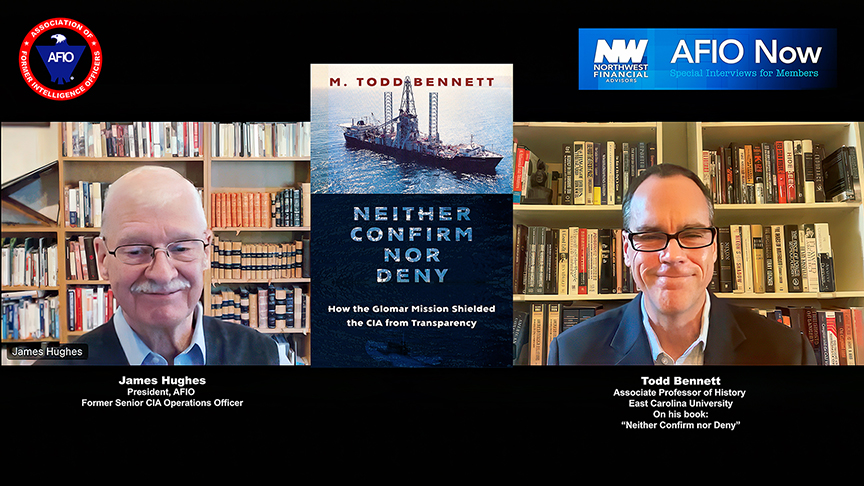
How the Glomar Explorer's Covert Espionage Mission Shielded the CIA from Transparency
Interview of Wednesday, 1 February 2023 of M. Todd Bennett, Federal Historian/Professor/Author. Interviewer - Host: James Hughes, AFIO President, a former CIA Operations Officer.
TOPIC: Todd Bennett and Jim Hughes discuss Bennett's latest book, "Neither Confirm nor Deny: How the Glomar Mission Shielded the CIA from Transparency" which covers billionaire Howard Hughes's 1974 Glomar Explorer, a risky deep-sea mining vessel used to retrieve a sunken Soviet sub.
The secret operation featured underwater espionage, impossible gadgetry, and high-stakes international drama, and employed public deniability -- what became known as "the Glomar response": "We can neither confirm nor deny. . . . "
The interview explores the logistics, media fallout, and geopolitical significance of this deep-sea operation. It helped the CIA ward off oversight during a decade infatuated with expansive openness and disdain for secrecy. And closes with advice for students seeking careers in intelligence.
The interview runs 25 minutes and includes several Q&As.
Purchase a copy of "Neither Confirm nor Deny" here.
Access the Bennett interview here or click above image
The AFIO Now video series in 2023 is sponsored by Northwest Financial Advisors.
NEWLY PUBLISHED
| Be informed on career opportunities in the U.S. Intelligence Community |
 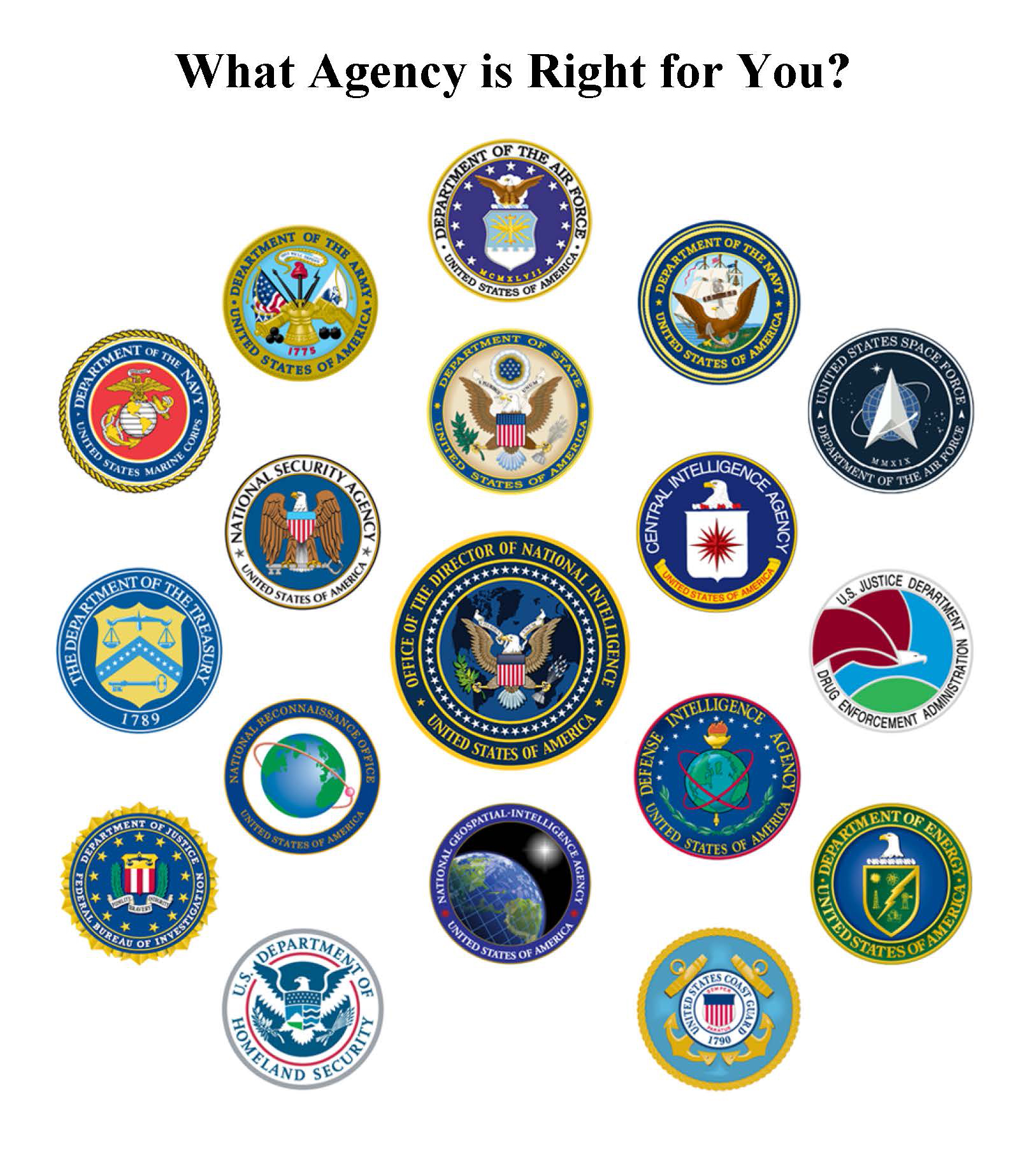 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. This is the all new fifth edition. |
| Careers Booklet (new 2023 Fifth Edition) can be read or downloaded here |

"AFIO Now" Video Interviews and Podcasts in 2023 are sponsored by
Northwest Financial Advisors
Click here to watch interviews in the AFIO Now series released in 2023.
View interviews from 2020 to 2022 here.
Watch public-release interviews on our YouTube channel or listen to them in podcast form at the links below.
Log into the member-only area for member-only features.
Latest podcast episode: Nigel West, Historian and Former MP, on "Spies Who Changed History: Greatest Spies and Agents of the 20th Century" Interview held Sunday, 15 January 2023. Interviewer - Host: James Hughes, AFIO President, a former CIA Operations Officer.
Are you too busy to watch an entire AFIO Now episode on YouTube? Would you rather listen in your car or while accomplishing other tasks? You can download or stream episodes on any of the 8 podcasting platforms that host AFIO Now. Search for 'AFIO Podcast' for a selection of the interviews above (public released ones) on:
Podbean; iTunes; Google; Spotify; Amazon Music; Amazon TuneIn + Alexa; iHeartRadio; Pandora
Social media users, and those who wish to explore, can find or be notified about new
announcements and other material on AFIO's Twitter feed, LinkedIn
page, and YouTube channel. Access them here: LinkedIn, Twitter, and YouTube.
![]()
![]()
![]()
Access CIA's Inhouse Gift Shop
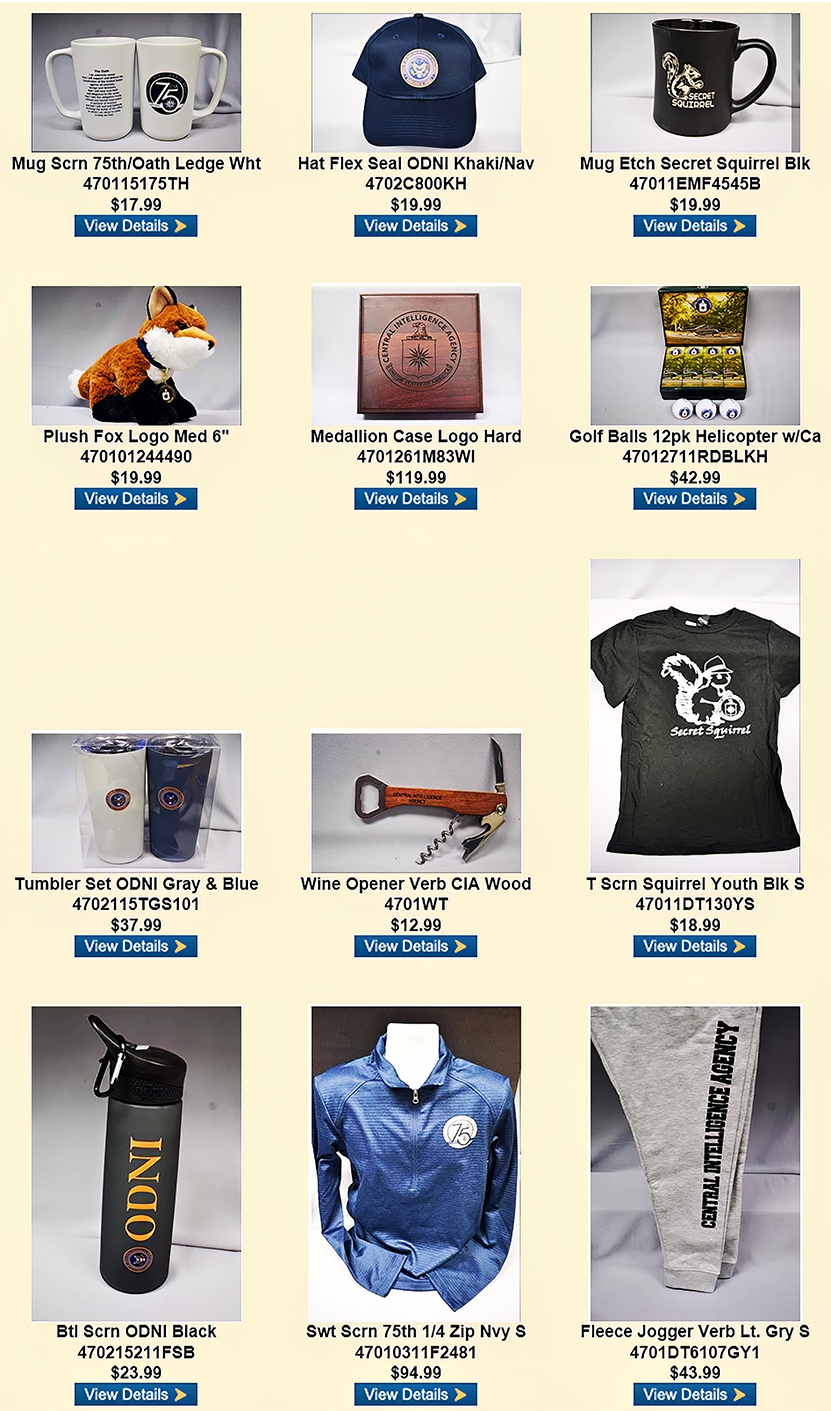
One special benefit of AFIO membership is access to CIA's EAA Store.
After completing the required, quick pre-approval process for all AFIO members, described here, you can purchase directly from the EAA online store their unusual logo'd gift items for self or colleagues. EAA on 10 February 2023 released the photo above, which features some of their newest CIA items and other gift suggestions.
ACKNOWLEDGEMENTS
The WIN editors thank the following contributors of content for this issue:
EB, PO, FR, CP, JH
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
EB, PO, FR, CP, JH
Readers are encouraged to suggest material for any section of the WIN to:
winseditor@afio.com
DISCLAIMER
Our editors include a wide range of articles and commentary in the Weekly Intelligence Notes to
inform and educate our readers. The views expressed in the articles are purely those of the authors and do not reflect support or endorsement from AFIO. WIN notices about non-AFIO events do not constitute endorsement or recommendation by AFIO.
AFIO does not vet or endorse research inquiries, career announcements, or job offers. We publish reasonable-sounding inquiries and career offerings as a service to our members. We encourage readers to exercise caution and good judgment when responding and to independently verify the source before supplying resumes, career data, or personal information.
TECHNICAL DIFFICULTIES
Readers who encounter problems with links or viewing this newsletter as an email can access
the latest web edition here.
the latest web edition here.
Section I - CURRENT INTELLIGENCE NEWS HIGHLIGHTS
China Protests US Surveillance Plane's Taiwan Strait Flight - Military.com, 27 Feb 23
China said it closely monitored the flight of a U.S. surveillance plane through the Taiwan Strait on Monday, accusing the U.S. of having “deliberately disrupted and undermined the regional situation.” Chinese forces organized to keep an eye on the passage of the P-8A Poseidon anti-submarine patrol plane and “all matters were in hand,” the People’s Liberation Army’s Eastern Theater Command said in a social media posting. China regards self-ruled Taiwan as its own territory to be brought under its control by force if necessary, and views the passage of foreign military ships and aircraft through the 160-kilometer (100-mile)-wide strait as deliberate snubs and provocations. While U.S. warships regularly transit the strait, one of the world’s busiest shipping lanes, it is more rare for U.S. military aircraft to do so. (Full article here.)
NASA keeps an eye on China — from the space above Mars - Mashable, 25 Feb 23
While the United States spied on China spying on the United States, watchful eyes didn't stop on Earth — or even the space around it. Over 100 million miles away from the planet, NASA's Mars Reconnaissance Orbiter has had more than a bird's eye view of China's Mars rover, Zhurong. A camera onboard the robotic U.S. spacecraft flying up to 250 miles above the red planet takes pictures of vast swathes of terrain. The instrument is capable of displaying features as small as a kitchen table(Opens in a new tab), according to the U.S. space agency. On Tuesday the Twitter account for the orbiter's High Resolution Imaging Experiment(Opens in a new tab), or Hirise camera, posted three side-by-side images of the Chinese rover from above. They show the land vehicle has not budged in the past five months. The team managing the camera, based at the University of Arizona, said they take pictures of China's rover to "track its progress and monitor the surface for changes." In images taken between Sept. 8, 2022, and Feb. 7, the rover — seen as a dark bluish dot — hasn't changed positions. (Full article here.)
NSA's National Security Operations Center celebrates 50 years of 24/7 operations in service to the Nation - NSA, 21 Feb 23
After being established, NSOC began operations in OPS1 at NSA Washington, spending the next 50 years supporting events such as the end of the Cold War, the Gulf War and Desert Shield/Desert Storm, the 9/11 terrorist attacks, and the national pivot to strategic competition. One such event that illustrates NSOC’s critical role as NSA’s nerve center was during the Iran hostage crisis in 1981. On January 18, 1981, President Carter called NSOC and spoke directly with the SOO to receive status updates about preparations in Tehran. On the morning of the inauguration, President Carter spoke with the SOO multiple times, asking questions about NSA’s collection capabilities and Iranian air traffic control tower procedures. President Carter insisted that the line with NSOC be kept open so he could follow the progress of events in real time — even as he was riding to the Capitol, the link with NSOC was reestablished in the car and an aide maintained contact at the Capitol throughout the inauguration ceremonies. (Full article here.)
Belgium on High Alert as Russian 'Spy Ship' Detected in North Sea - Marine Link, 22 Feb 23
Belgium said it is investigating the presence of a Russian "spy ship" in the North Sea, a day after its neighbor the Netherlands reported that Russia was targeting North Sea infrastructure. The ship was detected in the Belgian North Sea around mid-November last year, Vincent Van Quickenborne, the Justice and North Sea minister, said in a statement headlined "Russian spy ship off our coast in November". While the presence of Russian ships in the North Sea is not forbidden, Belgium said it was monitoring the situation closely, in the context of the war in Ukraine. "We don't know the exact motives of this Russian ship, but let's not be naive," Van Quickenborne said. "Especially if it behaves suspiciously close to our wind farms, undersea gas and data cables and other critical infrastructure." (Full article here.)
Fake Russian diplomats revealed as heart of ‘hive’ spy ring in Australia - Sydney Morning Herald, 23 Feb 23
A highly active “hive” of Russian spies posing as diplomats operated in Australia for more than 18 months before it was dismantled as part of a sweeping and aggressive counter-espionage offensive by ASIO. The Australian intelligence agency spent months tracking the Russian spy ring, which comprised purported embassy and consular staff and operatives using other deep cover identities, before ASIO finally moved to force the ring’s key players out of Australia, according to sources with knowledge of its operation. ASIO director-general Mike Burgess described the spying operation in a major speech he delivered in Canberra on Tuesday, but did not name Russia. Sources confirmed ASIO had uncovered the spy ring operating out of a number of locations, including the Russian embassy in Canberra, while the Morrison government was in power. (Full article here.)
A U-2 Pilot Took This Selfie With the Chinese Spy Balloon. It's Astonishing. - Popular Mechanics, 22 Feb 23
For more than two weeks, rumors swirled that there was a selfie, taken by a U-2 spy plane pilot, that included the now-infamous Chinese spy balloon in the background. The secretive nature of the intelligence community suggested the photo, if it existed, might never see the light of day. Now, a photo has emerged that confirms it’s the real thing. The stunning image sheds light on how dedicated the U.S. government was to keeping tabs on the lighter-than-air intruder—and shooting it down when the time was right. The photo was shared yesterday on a number of social media accounts and appears above. The Twitter account explains that exactly where the photo came from is unknown, but seems to originate with the Dragon Lady Today website, which is devoted to all things U-2. (Full article here.)
NSA’s “state secrets” defense kills lawsuit challenging Internet surveillance - Arstechnica, 22 Feb 23
The US Supreme Court yesterday denied a petition to review a case involving the National Security Agency's surveillance of Internet traffic, leaving in place a lower-court ruling that invoked "state secrets privilege" to dismiss the lawsuit. The NSA surveillance was challenged by the Wikimedia Foundation, the American Civil Liberties Union, and the Knight First Amendment Institute at Columbia University. The Supreme Court's denial of Wikimedia's petition for review (formally known as "certoriari") was confirmed in a long list of decisions released yesterday. "As a final development in our case, Wikimedia Foundation v. NSA, the United States Supreme Court denied our petition asking for a review of the National Security Agency's (NSA) mass surveillance of Internet communications and activities. This denial represents a big hit to both privacy and freedom of expression," the Wikimedia Foundation said yesterday. (Full article here.)
China, Russia targeting Canada's artificial intelligence know-how, CSIS warns - Toronto Sun, 22 Feb 23
Canada’s spy service warns that adversaries will turn to espionage and foreign interference tactics to target the country’s increasingly important artificial-intelligence sector. The Canadian Security Intelligence Service says in a newly released analytical brief that countries including China and Russia can be expected to “pursue Canada’s AI through all available vectors” — from state-sponsored investment to the use of covert operatives. The analysis by the spy agency’s intelligence assessments branch, marked CSIS Eyes Only, was completed in July 2021 but only recently released to The Canadian Press in response to an access-to-information request filed in October of that year. It is the latest signal from the intelligence community that Canada’s technological innovation and resulting economic advancement are vulnerable to foreign forces out to co-opt or pilfer valuable research. (Full article here.)
Classified documents show up in odd places, portraying sloppy system beyond Trump, Pence, Biden - USA Today, 23 Feb 23
Beyond the high-profile cases of classified documents found in the homes of President Joe Biden, former President Donald Trump and former Vice President Mike Pence, federal court records portray a sloppy system for tracking the country's most important secrets. Intelligence agency staffers and contractors were caught in recent years squirreling away enormous troves of documents. One contractor mailed home computer hard drives filled with secrets from Afghanistan to Texas. Stashes of secret documents have been scattered through homes, sheds and cars. Staffers sometimes copied documents onto compact discs or even handwritten notes. It wasn’t always the documents that got workers caught. One path to thousands of pages of classified records was strewn with marijuana leaves. (Full article here.)
China’s secret police actively hunting people on US soil - New York Post, 25 Feb 23
The revelations read like an overwrought spy thriller: secret foreign police stations in Manhattan, shady foreign security thugs hunting American residents in American neighborhoods. But they weren’t fiction: Following stories in The Post, last month The New York Times reported that the FBI raided a non-descript building in Chinatown where the innocent-looking community association on the third floor hid a nefarious surprise — an unauthorized “police service center” linked to the Chinese Communist Party. That secret police station is a terrifying threat to Chinese-Americans, other CCP targets — and American sovereignty itself. The Times speculated that these stations are linked to what the CCP calls “Operation Fox Hunt”: an allegedly anti-corruption campaign that more often veers into intimidation, harassment and, at times, even coerced rendition of United States residents. (Full article here.)
The stories of Ukrainian citizens who formed espionage cells to help liberate Kherson - NPR, 22 Feb Jan 23
The southern port city of Kherson was the first major Ukrainian city occupied by Russian forces. With deep historical ties to Russia, it was not expected to be a center of resistance, but an army of citizen spies defied Moscow's expectations and helped Ukrainian forces liberate the city last November. NPR's Joanna Kakissis has the story of Kherson and its citizens turned partisans. Let's start with the day of the invasion, February 24, 2022. Tetiana Horobstova, a retired physics teacher, remembers it again as a beautiful day in Russia. She remembers making breakfast and watching from her balcony as the sun rose, turning the sky pink and illuminating green fields bursting with the winter harvest. "And then I heard the explosions. And then I saw the explosions - one near the airport, then a second, the third at a gas station. It seemed to turn everything red."..." (Full article here.)
Dutch intelligence: Many cyberattacks by Russia are not yet public knowledge - The Record, 22 Feb 23
Many of Russia’s cyber operations against Ukraine and NATO members during the past year have not yet become public knowledge, according to a joint report published this week by two Dutch intelligence services. Although dozens of private sector reports have detailed Russian ops during the war in Ukraine, experts have questioned whether the cybersecurity industry has visibility into the full extent of that activity. The joint report from the Dutch General Intelligence and Security Service (AIVD), alongside its Military Intelligence and Security Service (MIVD), cites two reasons why “many of these attempts have not yet become public knowledge.” The fact that “the pace of Russian cyber operations is fast” is a big factor, the report said. And the nature of many targeted institutions — such as military and diplomatic agencies — leads to secrecy about their vulnerabilities. “Before and during the war, Russian intelligence and security services engaged in widespread digital espionage, sabotage and influencing against Ukraine and NATO allies,” says the report, which describes the full-blown invasion of Ukraine a year ago this week as “a turning point in history.” (Full article here.)
Public-Public Partnerships: Cyber Intelligence Coordination Within the Department of Homeland Security - Lawfare, 24 Feb 23
The Department of Homeland Security is an expansive agency, responsible for counterterrorism, protection of critical infrastructure, cybersecurity, and much more. Because of its broad set of responsibilities, many experts and lawmakers claim that the agency is too widespread, too decentralized, and too unwieldy and that it needs to be dismantled. Fully deconstructing the department would be quite the task and is perhaps unrealistic. However, it is worth finding efficiencies across several of the department’s responsibilities—specifically in the cyber domain—to improve the safety and security of the American public. The Department of Homeland Security has three components with significant cyber missions—the Cybersecurity and Infrastructure Agency (CISA), Immigration and Customs Enforcement/Homeland Security Investigations (ICE/HSI), and the U.S. Secret Service (USSS). (Some might include the U.S. Coast Guard in this list, but due to its attachment to the Department of Defense, I am excluding it from this discussion.) These three agencies have overlapping and adjacent missions and authorities in the cyber domain but often do not collaborate on specific cases or incidents—especially in their field offices. The Department of Homeland Security should do more to harness its collective power and showcase how a unified department can operate and succeed. The department should seize this opportunity and create a new paradigm: strategic cyber intelligence hubs. (Full article here.)
Counterespionage Corner - Recent Arrests, Convictions, Expulsions, and more...
- Australia to deport Kazakh-born Irish woman for allegedly spying for Russia - Intel News, 26 Feb 23
- Chinese spy who visited key Delhi ‘installations’ held during Nepal return - Times of India, 24 Feb 23
- Ex-Army colonel who spied for China sentenced to 7.5 years in prison - Focus Taiwan, 24 Feb 23
- DRDO Official Arrested on Espionage Charges, Sent to 4-day Police Custody - News18, 25 Feb 23
- Polish authorities charge Russian with spying for Moscow - Associated Press, 23 Feb 23
- Danish former minister charged with revealing state secrets - Associated Press, 21 Feb 23
- Delhi NIA court convicts one terrorist in espionage case - Law Beat, 27 Feb 23
- Lithuanian citizen once again arrested in espionage case - Delfi, 27 Feb 23
- Former FBI National Security Branch Agent Gets Prison For Leaking Info To Armenian Mob - Patch, 27 Feb 23
Section II - REGULARLY FEATURED PODCASTS, BROADCASTS, NEWSLETTERS
The Latest National Security Topic Interview by Former Acting D/CIA Mike Morell
 Intelligence Matters: A CBS News national security podcast hosted by former CIA Acting Director and CBS News national security contributor Michael Morell.
Intelligence Matters: A CBS News national security podcast hosted by former CIA Acting Director and CBS News national security contributor Michael Morell.
21 Feb | Marking One Year of War in Ukraine: State Department Counselor Derek Chollet
In this episode of Intelligence Matters, host Michael Morell speaks with State Department Counselor Derek Chollet about the state of the war in Ukraine as it enters its second year. Morell and Chollet discuss the implications of a deepening relationship between Russia and Iran as well as Russia and China, which the U.S. recently warned against providing material aid to Moscow. Chollet also provides new insights into the newly tense relationship between Washington and Beijing, following the shootdown of a Chinese surveillance balloon. He outlines the Biden administration's approach to managing Iran's nuclear ambitions after the earlier collapse of nuclear talks.
Past episodes:
14 Feb | Chinese Spy Balloon Fallout: Military Expert John Culver
07 Feb| Inside Global Diplomacy: RT. Honourable Baroness Catherine Ashton
31 Jan | China Expert Dennis Wilder on U.S. Policy Towards Beijing
More about Intelligence Matters by Michael Morell here.
The Latest from International Spy Museum Historian Andrew Hammond, PhD.
 Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
Spycast is the official podcast of the International Spy Museum and hosts interviews with intelligence experts on matters of HUMINT, SIGINT, IMINT, OSINT, and GEOINT. Spycast is hosted by historian Andrew Hammond, PhD.
21 Feb | "The Espionage News Cycle" - A Conversation with SPY's Aliza Bran Aliza Bran joins Andrew to discuss her role as Media Relations Manager at the International Spy Museum. Aliza is a D.C. native and graduate of Washington University in St. Louis.
Past episodes:
14 Feb | From the Vault: "The Birth of American Propaganda" - A Conversation with John Hamilton
07 Feb | How Artificial Intelligence is Changing the Spy Game
31 Jan | The Lion and the Fox - Civil War Spy vs. Spy
The Latest Insights from Former CIA Acting Deputy Director for Operations Jack Devine.
 In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
In Other News The proprietary analytic newsletter crafted for The Arkin Group's private clients by former CIA Acting Deputy Director for Operations Jack Devine.
23 Feb | History will look back at the Russian invasion of Ukraine -- that took place a year ago today -- and say that this was a defining inflection point in global realignment. What is most striking is how very disruptive the invasion has been and how the downstream effects have prompted strategic pivots from nearly all parties. A flailing NATO was reinvigorated and a resonant counter narrative to the global rise in autocracy began to crystallize in the zeitgeist. What’s more the undergirding tenants of economic cooperation stood strong with countries and private corporations largely complying at their own initiative to the international sanctions regime. Europe weened itself from Russian energy incurring a cost no one expected it to bear and prompted an accelerated shift to clean energies, concurrently depriving Russia of its biggest leverage with Europe. Supply chain disruptions from Covid were exacerbated, catalyzing an enduring effort to diversity supply chains away from China. China’s role as an essential partner for Russia is undeniable but Russia’s role for China is less that of a strategic partner and more that of a useful pawn who can distract Western attention away from the South China Sea and China’s own regional expansion ambitions. Still China’s support for Russia will remain circumscribed by the importance of its trade relationships with the West. Perhaps most stark is this diminishment of Russia’s strategic agency as an energy exporter and viable strategic threat to Europe;: if Russia cannot win against Ukraine, then it doesn’t hold a chance against Europe. This reality has prompted a heightened risk of domestic political trouble within Russia coming from its Far Right flank. (Full version available to AFIO members in the coming days here.)
10 Feb | Keeping Russia at bay one year into the war will require unrelenting political and physical will.
Daily Analysis of Security Issues and Geopolitical Trends
 Intel Brief The Soufan Center’s flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
Intel Brief The Soufan Center’s flagship, daily analytical product focused on complex security issues and geopolitical trends that may shape regional or international affairs. The Soufan Center was founded by former FBI Special Agent and Soufan Group CEO Ali Soufan.
28 Feb | One Year After Russia’s Invasion, Will Support for Ukraine’s Displaced Continue?
Russia’s full-scale invasion of Ukraine has provoked what many experts consider the most significant displacement of people in Europe since the Second World War. The United Nations High Commissioner for Refugees (UNHCR) recorded over eight million Ukrainian refugees across Europe – representing about 20 percent of the country’s pre-war population – and nearly five million have applied for temporary protection. Women and children comprise 90 percent of those who have fled the country, according to UNHCR. (Full brief here.)
27 Feb | Shamima Begum and the Difficulty of Balancing Security, Humanitarian Concerns, and Accountability
24 Feb | How Has the War in Ukraine Shaped the Current Global Order?
23 Feb | China Aids and Abets Russian Disinformation Efforts in the Ukraine Conflict
22 Feb | Will the United Kingdom Proscribe the Wagner Group as a Terrorist Entity?
Analysis of Global Security Events with WTOP National Security Correspondent JJ Green
 Inside the SCIF - 17 Feb - Chinese Spy Balloon, Russian and Iranian Hackers
Inside the SCIF - 17 Feb - Chinese Spy Balloon, Russian and Iranian Hackers
 Target USA Podcast - 23 Feb - The Struggle in Turkey and Syria After Devastating Earthquakes.
Target USA Podcast - 23 Feb - The Struggle in Turkey and Syria After Devastating Earthquakes.
The Hunt Broadcast - 15 Feb - Is social media driving an increase in mass violence?
The Latest Insights from Jeff Stein and Colleagues in SpyTalk (Substack)
27 Feb | Afghan Treachery and Kabul's Collapse - Jeff Stein
The war may be over but the autopsies continue. The latest report from the Special Inspector General for Afghanistan Reconstruction, established in 2012 to monitor U.S. spending and war progress, is yet another withering examination of the last months of the U.S. and NATO-backed regime of Ashraf Ghani. There is plenty of blame to go around to explain the quick and utter collapse of the Afghan National Defense and Security Forces, or ANDSF, a summary of the report says. But the details are still stunning. (Full article here.)
23 Feb | FDR’S Female Secret Agent Wore Two Hats - Derek Leebaert
Much remains unknown about Franklin Roosevelt’s long presidency, which began ninety years ago next month, because historians have always spotlighted the titanic leader himself, while shedding comparatively little light on some of his closest associates. One of them was Frances Perkins, FDR’s secretary of labor, one of only four people who served at the top echelon of FDR’s administrations from beginning to end. (The others were Harold Ickes, secretary of the interior; Henry Wallace, who led the biggest government department, agriculture, to become vice president in 1941; and Harry Hopkins, FDR’s de facto secretary of public welfare and then his diplomatic alter ego during the war.) (Full article here.)
21 Feb | A Final Word on Balloongate - Matt Brazil
In 1976, I spent the summer in Taiwan studying Chinese, living with the family of an officer in Taiwan’s defense forces. The colonel commanded a political warfare battalion on Quemoy, one of the Nationalist-held island redoubts just 10 kilometers from mainland China. His principal weapon: balloons. Their payload: anti-communist propaganda leaflets. (Full article here.)
18 Feb | Return to the Wilderness of Mirrors - Jeff Stein
08 Feb | Mole Reversal - Jeff Stein
04 Feb | Frenemies: US-Israel Spy Strains Emerge Over Iran - Jonathan Broder
To support SpyTalk, subscribe here.
Section III - MEMBER CONTRIBUTIONS
Russia covertly mapping key energy infrastructure for sabotage, Dutch report warns - Intel News, 21 Feb 23
The Russian intelligence services are “covertly mapping” the energy infrastructure of the North Sea, in preparation for acts of disruption and sabotage, according to a new report form the Dutch government. The 32-page report was published this week, ahead of the one-year anniversary of the 2022 Russian invasion of Ukraine. It was authored collaboratively by the two main intelligence agencies of the Netherlands, the General Intelligence and Security Service (AIVD) and the Military Intelligence and Security Service (MIVD). The report notes that Russian spy ships, drones, satellites and human agents are engaged in an unprecedented effort to chart the energy and other “vital marine infrastructure” of the North Sea. The purpose of this effort is to understand how the energy and other key infrastructure works in the North Sea. The term North Sea refers to the maritime region that lies between France, Belgium, the Netherlands, Germany, Denmark, Norway and the United Kingdom. It hosts key energy infrastructure, including oil, natural gas, wind and wave power installations, which supply energy to much of northern Europe. (Full article here.)
Information Sheet: Best Practices for Securing Your Home Network - NSA, 22 Feb 22
Executive summary: Don't be a victim! Malicious cyber actors may leverage your home network to gain access to personal, private, and confidential information. Help protect yourself, your family, and your work by practicing cybersecurity-aware behaviors, observing some basic configuration guidelines, and implementing the following mitigations on your home network, including: upgrade and update all equipment and software regularly, including routing devices; exercise secure habits by backing up your data and disconnecting devices when connections are not needed; limit administration to the internal network only. Recommendations for device security: Electronic computing devices, including computers, laptops, printers, mobile phones, tablets, security cameras, home appliances, cars, and other “Internet of Things” (IoT) devices must all be secured to reduce the risk of compromise. Most home entertainment and utility devices, such as home monitoring systems, baby monitors, IoT devices, smart devices, Blu-rayTM players, streaming video players, and video game consoles, are capable of accessing the Internet, recording audio, and/or capturing video. Implementing security measures can ensure these devices don’t become the weak link in your home protection... (Full article here.)
Online Exhibit: Project AZORIAN - CIA, 24 Feb 23
Imagine standing atop the Empire State Building with an 8-foot-wide grappling hook on a 1-inch-diameter steel rope. Your task is to lower the hook to the street below, snag a compact car full of gold, and lift the car back to the top of the building. On top of that, the job has to be done without anyone noticing. That, essentially, describes what the CIA did in Project AZORIAN, a highly secret six-year effort to retrieve a sunken Soviet submarine from the Pacific Ocean floor during the Cold War. The story began in 1968 when K-129, a Soviet Golf II-class submarine carrying three SS-N-4 nuclear-armed ballistic missiles, sailed from the naval base at Petropavlovsk on Russia’s Kamchatka Peninsula to take up its peacetime patrol station in the Pacific Ocean northeast of Hawaii. Soon after leaving port, the submarine and its entire crew were lost. (Full article here.)
Book Recommendation: Terrorist Events Worldwide 2022 - Edward Mickolous, 21 Feb 23
This is the 21st in a series of chronologies of international and domestic terrorist attacks and global, regional, and individual government and private responses. The author, Edward Mickolus, wrote the first doctoral dissertation on international terrorism while earning an M.A., M.Phil, and Ph.D. from Yale University. He then served in analytical, operational, management, and staff positions in the Central Intelligence Agency for 33 years, where he was CIA's first full-time analyst on international terrorism; analyzed African political, economic, social, military, and leadership issues; wrote political-psychological assessments of world leaders; and managed collection, counterintelligence, and covert action programs against terrorists, drug traffickers, weapons proliferators, and hostile espionage services. He founded Vinyard Software, Inc., (vinyardsoftware.com) whose International Terrorism Data Center provides the best publicly-available data on terrorists and events around the world. Visit his website at EdwardMickolus.com. (More information and order here.)
Exclusive: Lab Leak Most Likely Origin of Covid-19 Pandemic, Energy Department Now Says - Wall Street Journal, 26 Feb 23
The U.S. Energy Department has concluded that the Covid pandemic most likely arose from a laboratory leak, according to a classified intelligence report recently provided to the White House and key members of Congress. The shift by the Energy Department, which previously was undecided on how the virus emerged, is noted in an update to a 2021 document by Director of National Intelligence Avril Haines’s office. The new report highlights how different parts of the intelligence community have arrived at disparate judgments about the pandemic’s origin. The Energy Department now joins the Federal Bureau of Investigation in saying the virus likely spread via a mishap at a Chinese laboratory. Four other agencies, along with a national intelligence panel, still judge that it was likely the result of a natural transmission, and two are undecided. The Energy Department’s conclusion is the result of new intelligence and is significant because the agency has considerable scientific expertise and oversees a network of U.S. national laboratories, some of which conduct advanced biological research. The Energy Department made its judgment with “low confidence,” according to people who have read the classified report. (Full article here.) (Note: May require a one time free registration or sit behind a pay wall.)
Article: The West’s next challenge: Russian spy ops beyond Ukraine - The Hill, 23 Feb 23
After one year of war in Ukraine, the West’s exposure and the arrest of Russia’s spies are having an effect on the Kremlin’s ability to conduct espionage and covert operations. This counterintelligence campaign should not let up as Russia’s military, economic and political weakness will likely lead to an increase in its security and intelligence activities, not a decrease. Russia’s security services will need to demonstrate their value and utility in the wake of their failure in Ukraine, and these activities will remain one of the few tools with which Russia can effectively signal or escalate. From the outset of the war, the United States and Europe expelled nearly 600 Russian “diplomats” or suspected intelligence officers from across the continent. This materially degraded the country’s ability to conduct traditional espionage and sharply limits its ability to carry out “active measures” and other forms of “hybrid war.” This increased awareness of, and efforts to counter, Russia’s intelligence activities also marks a notable break with the pre-Ukraine efforts. Prior to the war, European counterintelligence activities were notably weaker and less coordinated. The West must, however, avoid becoming complacent in this effort as Russia is likely to increasingly turn to covert operations as the war progresses and as Russia’s material position weakens. (Full article here.)
Section IV - DEEPER DIVES, FILM, HISTORY, POP CULTURE
Audio: Is cyberespionage actually signals intelligence? (30 mins) - Between Two Nerds, 21 Feb 23
In this edition of Between Two Nerds Tom Uren and The Grugq look at the differences and similarities between signals intelligence and cyber operations. Why did Five Eyes Sigint organisations end up ‘owning’ cyber operations and does that make sense, or should there be a separate cyber intelligence organisation? In this podcast Grugq reads quotes about the mid 1990s struggle between NSA and CIA over ownership of cyber. Quotes are from the PhD dissertation “Penetrate, Exploit, Disrupt, Destroy: The Rise of Computer Network Operations as a Major Military Innovation” by Craig Wiener. (Listen here.)
Audio: CSIS Documents Reveal a Web of Chinese Influence in Canada (23 mins) - The Decibel, 27 Feb 23
Documents from Canada’s spy agency CSIS – viewed by The Globe and Mail – show how China was influencing Canada’s 2021 federal election by promoting candidates favourable to the regime, how it warned “friendly” Canadians about investigations and targeted Canadians with tactics like cyberattacks, bribery and sexual seduction. These documents highlight a troubling web of China’s interference in Canadian political, financial and academic institutions. Robert Fife, The Globe’s Ottawa bureau chief, explains why these documents matter and what we can learn about how China is trying to influence Canadian affairs. (Listen here.)
Audio: An interview with Andrew Boyd, director of the CIA's Centre for Cyber Intelligence (53 mins) - Risky.biz, 23 Feb 23
In this interview the director of the CIA’s Center for Cyber Intelligence (CCI) sits down with Risky Business podcast host Patrick Gray to talk about: What CCI actually does; The CIA’s role in cyber intel and operations; What lessons have been learned from Russia’s cyber campaigns targeting Ukraine; Why a cyber conflict with China will be very, very different; His views on the ransomware threat; Much, much more... (Listen here.)
OpEd: South Africa’s intelligence agency needs speedy reform - or it must be shut down - The Conversation, 24 Feb 23
South Africa’s civilian intelligence service, the State Security Agency, is a broken institution. It is meant to provide intelligence to forewarn the country about national security threats. Powerful individuals aligned to former president Jacob Zuma, presumably at his behest, repurposed the institution to help him maintain his grip on power. It was one of many institutions that were repurposed for improper personal or political gain during his tenure (May 2009 to February 2018): a process that has become known as state capture. His successor, President Cyril Ramaphosa, promised in 2022 to reform the agency so it would serve its original mission. He committed to returning it to the pre-2009 era of having separate domestic and foreign branches, each led by its own director-general. This decision is a major positive development. The Zuma administration merged the two branches and abused the centralised model to protect the president from criticism. Dismantling this architecture of abuse is happening too slowly, however, with no transitional plan having been announced publicly. Such a plan should include appointing interim heads for the domestic and foreign branches, rather than relying on people in acting positions. The government’s underestimation of the time needed to restructure the intelligence agency could have potentially serious, even dangerous, consequences. (Full report here.)
Analysis: The Global Footprint of Chinese Cyber Warfare and Espionage - Modern Diplomacy, 20 Feb 23
Turning the pages of history concerning the gradual progress of humankind, right from the ancient to the modern world, a common connecting link can be found. It is called War. But what makes this fact more interesting is the perpetually changing nature of war. It is an expression of numerous variables of history and their complex combination in which war plays a major role that cannot be undermined. Theoretically, the epistemological framework of wars has been categorised into five generations. The present-day modern world is witnessing 5th-generation warfare. It relies heavily on the weaponisation of cyberspace and the magnanimous data generated by various States. Every imaginable fact that can be noted, quantified and stored digitally can be considered potential data. This all-encompassing and pervasive nature makes data a crucial asset of a state. This asset, if compromised due to a lack of security, can cause severe damage. Cyberwarfare, in this regard, is a phenomenon that uses this cyberspace which is primarily a realm of data, by states and non-states actors to spy or block access to critical data stored online. This is followed by demanding a ransom from the victim for access to data, often compromising the confidentiality, privacy and security of individuals and states. (Full report here.)
Report: The troubled international situation increases the threat to the security of Sweden - Swedish Security Service, 22 Feb 23
Russia poses a serious threat to the security of Sweden, and Russia's actions, along with those of other authoritarian states such as China and Iran, have become increasingly offensive. Recent developments with the increased spread of conspiracy theories and anti-government rhetoric have increased the scope of the threat associated with subversion as well as the attack threat. The deteriorated international situation has had a direct effect on Sweden, as the external threat also affects Sweden’s domestic security. Current global developments are difficult to assess; each threat adds to the overall threat, and changes occur quickly. This has been described in the Swedish Security Service’s 2022–2023 situational assessment report. "The actions of Russia and other authoritarian states have become increasingly offensive, and security-threatening activities are ongoing. In addition, because of current international developments, extremism is growing, the attack threat has increased, and the scope of the threat associated with subversive activities has widened. Seen as a whole, the situation has accelerated the threat to Sweden," says Charlotte von Essen, Head of the Swedish Security Service. (Full report here.)
Report: Director-General's Annual Threat Assessment - Australian Security Intelligence Organization, 21 Feb 2023
Welcome to ASIO and the Ben Chifley Building. Excellencies, elected representatives, Inspector-General, agency heads, Secretaries, Military Chiefs, Commissioners, ladies and gentlemen. Sadly, there are some notable absences here tonight. In the last year, ASIO lost a number of current and past employees, including three former Directors-General: Alan Wrigley, John Moten and David Irvine. Alan, John, David and those others I cannot name publicly, I honour your service to ASIO and your contribution to Australia’s national security. A journalist once approached David Irvine to ask for a comment. His answer was classic David: “My boy, being a top spook is not compatible with being a media tart.” Wise words worth reflecting on – some of you might be thinking: perhaps not often enough in my case! David was right of course; intelligence chiefs need to be very careful about what they reveal publicly – and I’ll return to that later. But it’s also true that more agency heads are making public appearances to explain threats, both here and overseas to explain the threat. (Full report here.)
Tribute: Remembering the Life and Legacy of CIA Trailblazer Don Cryer - CIA, 21 Feb 23
Nearly five years ago, CIA lost one of its greatest champions of diversity and inclusion, Donald R. Cryer. He was a CIA Trailblazer—an individual whose leadership, achievements, and dedication to mission had a significant and lasting impact on the Agency’s history—and a lifelong Washingtonian. Don passed away at the age of 75. Don enjoyed a long, successful Agency career with more than 40 years of service to the country. He joined the Agency in 1962 as a GS-3 name-trace clerk, worked his way up within the Directorate of Operations to become one of the Intelligence Community’s leading experts in the field of information management, and retired as a Special Assistant to then-CIA Director George Tenet. As adept as he was at the technical side of intelligence work, Don understood the crucial role that diversity and inclusion play in mission success long before the Agency articulated this goal. Don was a strong advocate for eliminating institutional barriers to the advancement of women and minorities within the Agency. He served as a mentor to numerous officers over the years and led by example. In doing so, Don inspired other officers to do their best. (Full report here.)
OpEd: The new era of counterintelligence must shift focus to the gray zone - The Hill, 23 Feb 23
Strategic competition in the current global context is a post-counterterrorism-era paradigm shift that demands more aggressive offensive U.S. counterintelligence activities. Rethinking counterintelligence and counterterrorism for great power competition is both necessary and urgent. In other words, though terrorism is still a significant U.S. national security priority, large-scale counterterrorism wars are a phenomenon of the decade’s past. The essential first priority for achieving a competitive advantage in this new era of strategic competition is understanding the nature of competition in the gray zone. Gray zone activities play out in a sort of shadowy netherworld that falls below the threshold of a shooting war. They are amorphous campaigns for influence that combine non-military means and surrogates to destabilize and circumvent the strengths of a target state. These malign activities can include assassinations, kidnappings and disinformation operations, alongside traditional espionage activities, but with far more aggressive use of proxies: Think of Russia’s “little green men” overseas. But here in the U.S., the threats manifest in more sophisticated ways, like when U.S. private investigators are hired, unwittingly, by intelligence officers of hostile states. In the case of Iran, for example, U.S. private investigators were unknowingly providing intelligence to foreign agents for the purpose of kidnapping an Iranian American journalist living in New York. (Full report here.)
Paper: Critical Intelligence Studies - A new framework for analysis - Intelligence and National Security Journal, 21 Feb 23
As the purpose of the study of intelligence is, in part, to aid the practice of intelligence, scholarship must reflect that practice. This article sets out a theoretical framework for Critical Intelligence Studies that will increase the real-world applicability of the study of intelligence as currently represented by Intelligence Studies. Critical Security Studies’ recognition of the broadening and widening of the concept of security, and the ensuing recognition that intelligence work is not only done by state intelligence agencies or for the security of states, provides an opportunity to push forward the study of intelligence into a position where a well-developed, and theoretically sound, Critical Intelligence Studies can be meaningfully said to exist. (Full report here.)
Report: Russia’s War in Ukraine - Military and Intelligence Aspects - Congressional Research Service, 13 Feb 23
Russia’s renewed invasion of neighboring Ukraine in February 2022 marked the start of Europe’s deadliest armed conflict in decades. After a steady buildup of military forces along Ukraine’s borders since 2021, Russia invaded Ukraine on February 24, 2022, with Russian ground forces attacking from multiple directions. Initially, Russian forces made gains along all lines of advance. However, Russian forces ran into effective and likely unexpected levels of Ukrainian resistance from the invasion’s outset. In addition, many analysts and officials assess that, during this first stage of the war, the Russian military performed poorly overall and was hindered by specific tactical choices, poor logistics, ineffective communications, and command-and-control issues. The Ukrainian Armed Forces (UAF), while at a quantitative and qualitative disadvantage in personnel, equipment, and resources, have proven more resilient and adaptive than Russia expected. Over the course of the first several weeks of the war, Russian President Vladimir Putin and the Russian military had to adjust to various setbacks and other developments on the ground. With many of its advances stalled, Russian defense officials announced in late March 2022 that Russian military operations would focus on eastern Ukraine, including the regions of Donetsk and Luhansk (collectively known as the Donbas, where Russian-led separatists have been fighting since 2014) and that Russia would withdraw its forces around Kyiv and Chernihiv in the north. Russia subsequently gained additional territory in the Donetsk and Luhansk regions and held territory in other regions, including Kharkiv in the northeast and Zaporizhia and Kherson in the south. (Full report here.)
Analysis: Sri Lanka’s Intelligence Agencies - Debunking the Pseudo-Nationalist Narrative - Sri Lankan Guardian, 24 Feb 23
Nationalism and patriotism have the potential to unite a nation and instill a sense of shared identity, but their abuse by those who do not understand the importance of national interests can jeopardize a country’s long-term well-being. Unfortunately, in Sri Lanka, these concepts have been widely misused for political purposes, making it rare to find genuine nationalists and patriots. Instead, the country is plagued by pseudo-nationalists and fake patriots who exploit public sentiment and national interests for their own personal gain, posing a threat to the country’s future prosperity. Pseudo-nationalists and fake patriots are individuals who use nationalist rhetoric for their own political gain, without any real understanding of what it means to act in the best interests of the nation. These individuals are often more interested in promoting their own personal agendas than in advancing the greater good of their country. One of the key dangers posed by these individuals is that they are often willing to play politics with everything, including national security and foreign policy. They may take positions that are popular with their base or that score political points, but that ultimately weaken the country’s position on the world stage. For example, they may oppose important trade agreements or alliances that are critical to the country’s economic or military strength, simply because they do not want to be seen as “weak” or as ceding control to other nations. (Full report here.)
Infographic and Report: Ranked - Biotoxins in Nature, by Lethal Dose - Visual Capitalist, 24 Feb 23
Intelligence officers who have worked the CBRN issue are familiar with biotoxins, harmful substances that come from living organisms. They can take many forms, from the venom of a snake or spider to the neurotoxins produced by certain types of algae or microbes. In the infographic above, we look at some common biotoxins in the natural world and rank them based on how deadly they are to an average 70 kg (154 lb) human being. (Access visual tool and full report here.)
Intelligence in History - A Collection of Recent Content
- Video - Spy cameras: The Soviet Union's Disguised Button Camera - Spycamerasaurus, 26 Feb 23
- Article - NSB implicated in 1980 Lin I-hsiung family murders - Taipei Times, 25 Feb 23
- Article - When Switzerland was the location of choice for Chinese espionage - Swiss Info, 21 Feb 23
- Article - The Legendary U.S. Surveillance Plane That Flew For Over 50 Years - Slash Gear, 24 Feb 23
- Audio - An Activist Escaping Panama with Kimberly Muse (97 mins) - Spycraft 101, 20 Feb 23
- Video - Adolf Hitler - Secret Agent (12 mins) - War Stories with Mark Felton, 23 Feb 23
True Intelligence Matters in Film - The Iron Curtain - Director William A. Wellman (1948)
 Soviet soldier turned bureaucrat Igor Gouzenko is assigned to his first overseas posting in 1943 to Ottawa, Canada, as a cipher clerk for the military attaché, their offices in a secret wing of the Soviet embassy. Igor is not to tell anyone what he does for a living, he given a cover story which he is to recite even when questioned by his own people. He and his wife Anna Gouzenko are supposed to be cordial to their Canadian neighbors and associates, but not fraternize or befriend them, as they are still considered the enemy, despite both countries being on the same side in the war. Igor follows his instructions to a T, but it is more difficult for Anna, who does not have the distraction of work during the day, and who can see that their neighbors are not their enemies but good people much like themselves. Over the next few years, Igor sees that what is happening around him and the work in which he is involved will not result in a world in which he wants to raise his newborn son, Andrezj. As such, the Gouzenkos decide not to return to the Soviet Union. Besides defecting, Igor wants to expose what he is privy to, namely that there is a secret Soviet spy ring operating in Canada, which is comprised of people in authority, such as Canadian military personnel and elected officials. The spy ring's biggest project is to provide the Soviet government with secrets concerning the atomic bomb. Igor being able to get the necessary papers out of the embassy will be difficult enough, especially as he, Anna and Andrezj have been notified that the posting has concluded and that they are scheduled to return to the Soviet Union, but proving his claim to someone in authority in Canada who will listen before the Soviets discover what he is doing is a whole different matter.
Soviet soldier turned bureaucrat Igor Gouzenko is assigned to his first overseas posting in 1943 to Ottawa, Canada, as a cipher clerk for the military attaché, their offices in a secret wing of the Soviet embassy. Igor is not to tell anyone what he does for a living, he given a cover story which he is to recite even when questioned by his own people. He and his wife Anna Gouzenko are supposed to be cordial to their Canadian neighbors and associates, but not fraternize or befriend them, as they are still considered the enemy, despite both countries being on the same side in the war. Igor follows his instructions to a T, but it is more difficult for Anna, who does not have the distraction of work during the day, and who can see that their neighbors are not their enemies but good people much like themselves. Over the next few years, Igor sees that what is happening around him and the work in which he is involved will not result in a world in which he wants to raise his newborn son, Andrezj. As such, the Gouzenkos decide not to return to the Soviet Union. Besides defecting, Igor wants to expose what he is privy to, namely that there is a secret Soviet spy ring operating in Canada, which is comprised of people in authority, such as Canadian military personnel and elected officials. The spy ring's biggest project is to provide the Soviet government with secrets concerning the atomic bomb. Igor being able to get the necessary papers out of the embassy will be difficult enough, especially as he, Anna and Andrezj have been notified that the posting has concluded and that they are scheduled to return to the Soviet Union, but proving his claim to someone in authority in Canada who will listen before the Soviets discover what he is doing is a whole different matter.
More on this based-on-true-events production here.
Intelligence in Pop Culture - Poem - Reflections on Espionage: The Question of Cupcake - John Hollander (1974, 1999)
 This book-length poem by one of the major poets of our era is structured as a series of messages transmitted by a master spy to the director of spy operations and to a number of his fellow spies. The spy speaks of his own alienation and sense of purposelessness as a secret agent―a metaphor for a human existence committed to ordering, deciphering, and making sense of a world of random signs. First published in 1974, the book is now reprinted (1999) with a substantial introduction by the author that elaborates on the genesis of the poem, the literary figures who inspired some of the characters, the poem’s reception, and other matters. (Read the original 1974 version for free here.)
This book-length poem by one of the major poets of our era is structured as a series of messages transmitted by a master spy to the director of spy operations and to a number of his fellow spies. The spy speaks of his own alienation and sense of purposelessness as a secret agent―a metaphor for a human existence committed to ordering, deciphering, and making sense of a world of random signs. First published in 1974, the book is now reprinted (1999) with a substantial introduction by the author that elaborates on the genesis of the poem, the literary figures who inspired some of the characters, the poem’s reception, and other matters. (Read the original 1974 version for free here.)
Walking Tours - Washington, DC - Sundays (Dates/Times Vary)
Former intelligence officers guide visitors on two morning and afternoon espionage-themed walking tours: "Spies of Embassy Row" and "Spies of Georgetown." For more information and booking, click here or contact rosanna@spyher.co
Section V - Books, Research Requests, Jobs, Obituaries
Books — Forthcoming, Newly Released, Overlooked
 Before Bletchley Park: The Codebreakers of the First World War
Before Bletchley Park: The Codebreakers of the First World War
by Paul Gannon
(The History Press, 01 Sep 21)
The story of Bletchley Park’s codebreaking operations in the Second World War is now well known, but its counterparts in the First World War—Room 40 and MI1(b)—remain in the shadows, despite their involvement in and influence on most of the major events of that war. From the First Battle of the Marne, the shelling of Scarborough, the battles of Jutland and the Somme in 1916, to the battles on the Western Front in 1918, the German naval mutiny and the Zimmermann Telegram, this cast of characters—several of them as eccentric as anyone from Bletchley Park in the Second World War—secretly guided the outcome of the "Great War" from the confines of a few smoke-filled rooms. Using hundreds of intercepted and decrypted German military, naval, and diplomatic messages, bestselling author Paul Gannon reveals the fascinating story of British codebreaking operations. By drawing on many newly discovered archival documents that challenge misleading stories about Room 40 and MI1(b), he reveals a sophisticated machine in operation.
Order book here.
 We Were Never There: Volume 1: CIA U-2 Operations over Europe, USSR, and the Middle East, 1956-1960
We Were Never There: Volume 1: CIA U-2 Operations over Europe, USSR, and the Middle East, 1956-1960
by Kevin Wright
(Helion and Company, 30 Sep 21)
Devised by Kelly Johnson and initially operated by the CIA, the U-2 is the world’s most famous ‘spyplane.’ It flew at unprecedented altitudes and carried the most sophisticated sensors available, all in the greatest secrecy. Operating from remote locations and without markings, they often took-off before first light. Ostensibly operated by civilians flying meteorological research missions, their bold overflights took them far across Eastern Europe, the USSR, Middle and Far East. However, many details of the aircraft’s operational history remain vague and a considerable amount is still classified. Continuing national political sensitivities have meant that much about these early operations has still not been fully revealed even more than 60 years later. This book utilizes a large number of recently declassified documents to explore the remaining hidden details. It provides in-depth examinations of some missions not previously fully described and include more about Norway’s role in U-2 operations, and a breakdown of British U-2 overflights of the Middle East using recently released files from the British Ministry of Defence. It examines some of the U-2’s extensive efforts to collect intelligence on Soviet ballistic missile test launches and space program, on ‘Fast Move’ staging operations and lots more from these missions up to May 1960. Chapters explore some of the ground-breaking technology employed by the U-2 to photograph and eavesdrop on Soviet nuclear, military and industrial activities. These include revealing secrets of the Fili heavy bomber production plant, just five miles from the Kremlin. Overflights of the ‘Arzamas-16' closed nuclear city, Vozrozhdeniya biological warfare center in the Aral Sea and the mystery that was Mozhaysk. Over 90 photographs, maps and illustrations provide details of the aircraft, the cameras and electronic defensive and eavesdropping systems. The specialized nuclear fallout sampling role is explored and the ‘weather packs’ installed to substantiate the wafer-thin false cover story of the U-2’s role as a ‘meteorological research’ aircraft. Maps, most never been seen before, record the detailed routes flown by U-2 pilots deep into denied airspace to reveal the secrets of Soviet military, nuclear, scientific and industrial sites.
Order book here.
 Agent Zigzag: A True Story of Nazi Espionage, Love, and Betrayal
Agent Zigzag: A True Story of Nazi Espionage, Love, and Betrayal
by Ben Macintyre
(Crown, 04 Sep 07)
Eddie Chapman was a charming criminal, a con man, and a philanderer. He was also one of the most remarkable double agents Britain has ever produced. Inside the traitor was a man of loyalty; inside the villain was a hero. The problem for Chapman, his spymasters, and his lovers was to know where one persona ended and the other began. In 1941, after training as a German spy in occupied France, Chapman was parachuted into Britain with a revolver, a wireless, and a cyanide pill, with orders from the Abwehr to blow up an airplane factory. Instead, he contacted MI5, the British Secret Service. For the next four years, Chapman worked as a double agent, a lone British spy at the heart of the German Secret Service who at one time volunteered to assassinate Hitler for his countrymen. Crisscrossing Europe under different names, all the while weaving plans, spreading disinformation, and, miraculously, keeping his stories straight under intense interrogation, he even managed to gain some profit and seduce beautiful women along the way. The Nazis feted Chapman as a hero and awarded him the Iron Cross. In Britain, he was pardoned for his crimes, becoming the only wartime agent to be thus rewarded. Both countries provided for the mother of his child and his mistress. Sixty years after the end of the war, and ten years after Chapman’s death, MI5 has now declassified all of Chapman’s files, releasing more than 1,800 pages of top secret material and allowing the full story of Agent Zigzag to be told for the first time. A gripping story of loyalty, love, and treachery, Agent Zigzag offers a unique glimpse into the psychology of espionage, with its thin and shifting line between fidelity and betrayal.
Order book here.
Research Requests and Academic Opportunites
Academic Opportunity: Critical Thinking for Intelligence Analysis Course - 21 Apr 23, 0800-1700 (ET) - Virtual
This course will help Intelligence Analysts improve their critical thinking skills. It begins by reviewing the basic characteristics of quality intelligence analysis (and the challenges to producing it) and the methodology for building an analytic argument. The course continues with a discussion of the mental traits and habits that inhibit critical thinking and objectivity. Finally, the course discusses several types of structured techniques designed to inject critical thinking and analytic rigor into intelligence production. $600 fee. (More information and registration here.)
Academic Opportunity: The International Security and Intelligence Programme - 9 July to 5 August 2023 - Magdalene College, Cambridge
Chaired by Sir Richard Dearlove the former Chief of the British Secret Intelligence Service, the Cambridge Security Initiative (CSi) launched the ISI Programme in 2016. The purpose of this unique programme is to provide an opportunity for participants to meet and work with leading academics and practitioners from the intelligence and security communities in the historic setting of one of the world’s foremost universities. The Programme is run in partnership with the Department of War Studies at Kings College, London. (More information and registration here.)
Call for papers: Intelligence and Post-War Reconstruction - International Journal of Intelligence and Counterintelligence
History shows that without planning for post-war reconstruction, apparent victory in war can lead to long-term defeat. On the other hand, wise post-war planning can lead to friendly, peaceful, and profitable relations between victor and vanquished. For political, socio-economic and security-related planning, intelligence plays a crucial role in estimating capabilities, securing infrastructure, locating persons of interest, and rebuilding. In honor of the 75th anniversary of the European Recovery Program (Marshall Plan) after the Second World War, the editors are particularly interested in papers dealing with intelligence concerning post-war reconstruction initiatives and planning connected to historical and recent conflicts. Both case studies and theoretical and methodological approaches are welcome. The studies may include, but do not have to be focused on, the following questions and issues:
- The role of diplomatic and military intelligence during the conflict as preparation for post-war reconstruction, from the conceptual to the practical.
- What intelligence needs to be collected to secure and boost reconstruction?
- What contacts, networks, and infrastructure are necessary for intelligence to be effective?
- Who has been or should be approached and/or recruited for reconstruction efforts based on intelligence?
- When has intelligent post-war planning (or its opposite) been historically evident?
- How should intelligence interact with formerly warring parties and international organizations to empower practical reconstruction efforts?
- What intelligence collection challenges have services encountered in working for post-war peace?
- How did intelligence factor in the European Recovery Program?
- What was George C. Marshall’s position on the role of intelligence in general or concrete examples related to “his” plan?
01 Nov 23 deadline. More information and submission instructions here.
Search for stories: Matt Brazil, an AFIO member in the San Francisco Chapter and co-author of Chinese Communist Espionage, An Intelligence Primer (Naval Inst. Press, 2019) is writing a second work on Beijing's worldwide espionage and influence offensive. As part of that effort, he seeks interesting stories of encounters with China's civilian and military intelligence apparatus. If you are interested in telling your story or you know someone who would be, Matt can be reached via matthew.brazil@gmail.com or his website www.mattbrazil.net.
Search for information: Author and AFIO member Toby Harnden is researching recipients of CIA gallantry awards (DCI's OPA is assisting). Harnden is eager to speak to anyone with memories of, information about, or pointers toward Bob A. Plan and Arthur J. Porn. Plan was born in Croatia in 1920 and served with the OSS in Yugoslavia 1944-45. He became a CIA contractor, working as a career agent and translator, and was based in Greece in the 1950s and Mexico in the 1960s. He was parented by EUR Division when he came out of retirement to enter Tehran in 1980. Porn, born in 1930, was a WH case officer from 1958 who was based in Argentina, Honduras and Bolivia in the 1960s and 1970s. He was honored for an act of bravery in Bolivia in 1970. Please contact tobyharnden@gmail.com or 202-213-3775.
Search for information: Searching for information on a CIA "intelligence operation" carried out during the Clinton administration in 1997 or 1999 aimed at Iran and/or its MOIS in response to Iran's involvement in the 1996 Khobar Towers bombings. Clinton's counterterrorism chief Richard Clarke made a brief reference to this operation on p. 129 of his book Against All Enemies; George Tenet made a possible reference to this operation on p. 124 of his book At the Center of the Storm; and Bruce Riedel posted a reference to it here in his article "The Iran Primer: The Clinton Administration." He called it "Operation Sapphire" - not to be confused with Operation Sapphire aimed at Kazakhstan. Also, searching for information on a bomb found on a bridge in Manila, Philippines around November 23, 1996 when President Clinton was in the city. Contact: dpluchinsky@rocketmail.com.
Search for information: Dr John Gentry of Georgetown University seeks information on what ways, to what extent, at what agencies, and with what implications/consequences are DEI (diversity, equity, inclusion) policies damaging the IC and DOD. Request examples and assessments that link senior-level policies, and middle managers' interpretations of them, to specific organizational and personal actions and then to actual consequences in sufficient volume and detail to be able to make a coherent argument. Anonymity assured. Contact: jag411@georgetown.edu.
Search for information An AFIO member who is researching "a State Department officer who seems to have functioned as a pre-CIA intelligence officer without having joined the OSS" would welcome leads on persons or books specializing "in 'pre-CIA' 'CIA history'." Anyone with pertinent information can contact info@whittakerchambers.org.
Call For Papers: The Struggle in the Israeli Security Zone in South Lebanon, 1985-2000, Israel Affairs
In June 1985, the Israel Defense Forces (IDF) de jure completed its withdrawal from Lebanon to the Israeli borders. De facto, Israel left in its hands a strip of land, about 15 kilometers from its border, in which its ally, the South Lebanon Army (SLA), operated. This strip of land came to be known as the Israeli Security Zone. The idea was that the SLA would be almost independent, while the IDF would intervene only when necessary in the battle against Palestinian and Shiite groups and supervise the SLA. Soon, however, the IDF became more involved, building military posts within the Security Zone, reinforcing itself, and encountering new challenges. In May 2000, Israel pulled its forces back to its borders and the SLA collapsed, along with the Security Zone. The 15 years of fighting in the Security Zone were rarely mentioned within Israeli society, let alone in the academic sphere. Only in recent years has the Israeli public become aware of this period after many soldiers who served in the Security Zone began sharing their memories through books and social media. The campaign to raise awareness of the period successfully ended when in March 2021, Israel officially recognized this period as one of warfare. This special issue aims to interdisciplinarily bridge the gap in the academic discourse regarding the war in the Security Zone. The editors are interested in articles dealing with various topics concerning the 1985-2000 war in the Security Zone. 30 March 2023 deadline. For more information, including submission instructions and suggested topics, click here.
Search for French Intelligence Officer: Gary Schaut of Sudbury, Canada is in search of a French intelligence agent who was still active around 1997 in France, and who had provided information in that year to a French journalist named “William Reymond." Anyone with pertinent information can contact Schaut at gbschaut@sympatico.ca.
Search for Colleagues: Dennis Pluchinsky seeks contact with Tom Lane and Nancy Kenealy, "who worked with Cindy, Gina, and Jeff" in the mid-1990s on al-Qaeda. Pluchinsky is in contact with all three of these other colleagues and would like to establish contact with Lane and Kenealy regarding his work on a four-volume book series on anti-American terrorism overseas ("see Amazon for more details" about the books). Please contact Pluchinsky at dpluchinsky@rocketmail.com.
Call For Information: Harvard student seeks primary source documents, historical records, or points of contact regarding Freedom Company, aka Eastern Construction Company, of the Philippines
Ryan Santos, a senior at Harvard, is writing his history thesis titled “The outsourcing of freedom”: Filipino operatives in the origins of the American war in Indochina, 1954-1967. The focus of the research project is on the Freedom Company of the Philippines (later became the Eastern Construction Company in 1958), a dynamic private enterprise funded by the US to send Filipino paramilitary specialists - who were successful in suppressing their own local communist insurgency in the Huks - to assist in counterinsurgency and nation-building operations in Vietnam, Laos, and Indonesia. Ryan hopes to use his research on the Freedom Company of the Philippines and the Eastern Construction Company to underscore the diversity of geopolitical agents involved in American foreign policy during the Cold War, the development of US-Philippine relations, and the origins of American involvement in Indochina. If this project is of any interest or if there are any primary source documents, historical records, or points of contact that would be helpful, please contact him at ryansantos@college.harvard.edu.
Call For Articles: AFIO Journal, The Intelligencer
For the past four years, AFIO has included in The Intelligencer a series of articles on “when intelligence made a difference.” Written by scholars, intelligence practitioners, students, and others, they cover events from ancient times to the modern world and in many countries. AFIO is soliciting articles for future issues. Most articles run between 2,000 and 3,000 words, although some are longer or shorter. If you have an idea for an article that fits the theme, email senior editor Peter Oleson at peter.oleson@afio.com.
Call For Assistance: Researcher Seeks Copy of 1941 FBI Booklet
An AFIO member who is conducting research on the beginnings of industrial security programs before WWII is in search of a copy of a 55-page FBI booklet, dated December 1941, titled "Suggestions for Protection of Industrial Facilities." Digital copies or photocopies are acceptable. Please contact winseditor@afio.com with any information.
Jobs
Faculty Opening - Adjunct Faculty, Intelligence Analysis - Krieger School of Arts and Sciences, Advanced Academic Programs, Johns Hopkins University, Online
The Advanced Academic Programs (AAP) division seeks non-tenure track adjunct faculty to teach several courses within the MS in Intelligence Analysis program. The course(s) will be taught fully online beginning in Summer 2023 and beyond. Candidates with online course development and teaching experience and those with experience teaching and engaging students from diverse backgrounds are of particular interest. Full details and online application instructions can be found here.
Faculty Opening - Teaching Intelligence Analysis - James Madison University - Harrisonburg, Virginia
The Faculty of the Intelligence Analysis (IA) Program at James Madison University (JMU) are searching for a dynamic new colleague to join us in the ongoing co-creation of an exceptional educational experience to prepare the next generation of analysts. Our program is in its 16th year, and our graduates regularly secure positions as analysts in the public and private sectors, including the Intelligence Community, military and law enforcement organizations, defense contractors, and major consulting firms. Our vision is a versatile, multidisciplinary undergraduate education that simultaneously emphasizes methodology, technology, and communication, with a specialization in intelligence analysis. We especially seek a new colleague who can strengthen our longstanding distinctive focus on developing good reasoning and/or our more recent focus on research design and analytic production.
We would welcome a potential new colleague from any academic discipline (to include the humanities, social sciences, and natural sciences) and/or any professional background (to include former intelligence, military, homeland security, law enforcement, and other security and analytic professionals) that enables them to speak with credibility about the process of doing analysis. The desire to engage both traditional academics and professional analysts is extremely important to us. We also value both teaching excellence as well as one-on-one professional mentoring. We especially seek candidates who are able to “bridge the gap” and to engage students whose struggles are different from their own, and who can help them flourish in their future personal and professional lives. The position requires either a Ph.D. in a relevant academic field by hiring date (for a tenure-track appointment) or a minimum of a Bachelor’s Degree (Master’s Preferred) with substantial, demonstrated experience as an analyst (for appointment on a Renewable Term Contract). Our normal teaching load is three courses per semester.
Application materials should include 1) a detailed cover letter that tells the story of how the candidate’s expertise and experience fit our aspirations, values, and teaching needs, 2) curriculum vitae/resume, 3) a “statement of inclusive excellence” that highlights (amongst other things) how the applicant has successfully helped colleagues from different backgrounds and perspectives to flourish in their work, and 4) contact information for at least three references.
The search will remain open until the position is filled. Salary commensurate with experience. Questions can be directed to the Chair of the search committee, Dr. Noel Hendrickson, at hendrinx@jmu.edu. Employment is contingent upon the successful completion of a criminal background check.
Additional details and further online application instructions can be found here.
Intelligence Practice Lead - SOS International, Washington, D.C.
The Intelligence Practice Lead, Americas, alongside the Consulting and Solutions Practice Director, Americas, is responsible for developing the Intelligence business within the regional security consulting team. The Intelligence Practice Lead will oversee the development, positioning, sales and the effective coordination and delivery of all intelligence consulting and solutions, including Intelligence Managed Services, in the US and Canada region. In this role the individual will oversee the provision of support to International SOS’s US and Canada regional distribution channels to drive customer satisfaction and profitable growth across relevant business lines, in the technical domain of Intelligence. The individual will help to translate International SOS’s Security value proposition into clear priorities and actions, in support of the business lines’ commercial road maps. In addition, the role will be responsible for: driving day-to-day delivery of Intelligence consulting deliverables (including capability assessment, planning, training etc); establishing a cadre of analyst external consultants; educating key internal stakeholders and clients; leading/contributing to the expansion of intelligence methodologies and deliverables; along with their cadre of external consultants.
Additional information and application here.
Supervisory Criminal Investigator (Special Agent-In-Charge) - U.S. Army CID, Nationwide
Serves as the Criminal Investigation Division (CID) Field Office Special Agent-In-Charge (SAC) and is the principle law enforcement expert and advisor responsible for all investigations and operations conducted by CID offices within their area of responsibility (AOR). Directly supervises multiple Supervisory Criminal Investigators, full-performance level GS-13 and GS-14 criminal investigators, and support personnel in co-located and satellite offices.
Additional information and application here.
Retired Federal Government Employees Wanted - National Security Agency - Fort Meade, Maryland
The National Security Agency (NSA) may occasionally need skilled civilian retirees to augment the existing work force on high priority projects or programs. In order to fill these temporary positions quickly, we need to know who may be interested and available to return to work with us on a short notice basis as well as their skills. Retirees provide expertise and corporate knowledge to temporarily support mission requirements, manpower shortfalls, and/or mentor the next generation of Agency employees. Salary Range: $86,335 - $170,800.
Additional information and application here.
Assistant/Associate Professor of Intelligence Studies (Global Security and Intelligence Studies) - Embry-Riddle Aeronautical University - Prescott, Arizona
Embry-Riddle Aeronautical University's Prescott, Arizona campus is accepting applications for a tenure-track assistant or associate-level professor of intelligence studies to teach intelligence courses to students in the Global Security and Intelligence program. The successful candidate will teach students about the intelligence community, strategic intelligence, the intelligence cycle and intelligence analysis, writing, and briefing. Prior experience working in the intelligence community is strongly preferred. We are interested in candidates with teaching acumen in intelligence analysis and writing using structured analytical techniques.
Additional information and application here.
Teaching Associate - Intelligence and National Security Studies - Coastal Carolina University, South Carolina
The Department of Intelligence and Security Studies ( ISS ) at Coastal Carolina University is accepting applications for a pool of Teaching Associates (part-time adjunct faculty) to teach introductory and undergraduate elective course offerings for the program beginning in August 2022. While the ad is open to any specialization within the field of study, courses in the areas of homeland security, law enforcement intelligence, counter-narcotics, and cybersecurity are of particular interest. Course offerings can be in a face-to-face or synchronous online modality. To be considered, candidates must have a masters or doctoral degree in a relevant subject area. Prior professional experience in the profession, as well as prior teaching experience are preferred.
Additional information and application here.
Assistant Professor of Intelligence and National Security Studies - University of Texas, El Paso
The Department of Criminal Justice is seeking to fill one full-time tenure-track position beginning Fall 2023 at the Assistant Professor level. Responsibilities include conducting and publishing scholarly research, seeking extramural funding, teaching face-to-face and online courses, and service to the department, university, and profession. Applicants must have a Ph.D. in a closely related field in Intelligence and/or Security Studies from an accredited university (e.g., criminal justice, political science, public policy, security studies). ABD applicants will be considered if doctorate will be in hand by Fall 2023. Active research agenda and published scholarly journal articles are required to apply. Applicants with only a J.D., Psy.D., or Ed.D. will not be considered. All research/teaching areas of intelligence/national security studies will be considered, but preference will be given to candidates who have demonstrated teaching and/or research areas in at least one of these areas: Homeland Security, Intelligence Analysis, or Terrorism/Counter-Terrorism.
Additional information and application here.
Obituaries
![]() Jim Lynch — Senior CIA Researcher and Multi-Directorate Leader
Jim Lynch — Senior CIA Researcher and Multi-Directorate Leader
James "Jim" Philip Lynch, 84, passed away peacefully on February 17, 2023, at Inova Fair Oaks Hospital in Fairfax, VA. Born in Woonsocket, Rhode Island, Jim graduated the University of Rhode Island, Kingston with a B.S in Agriculture, after which he went on to earn an M.S. and Ph.D in Botany/Plant Pathology at the University of Maryland, College Park. Upon the completion of his graduate studies at the University of Maryland, Jim was hired as a research scientist by the CIA, the start of a career that spanned 32 years. Jim was one of a handful of officers to have ever served in a senior command function in all four directorates of the CIA.
![]() Catherine Kelleher — Former DAS Defense and National Security Leader in Academia and Government
Catherine Kelleher — Former DAS Defense and National Security Leader in Academia and Government
Dr. Catherine McArdle Kelleher, 84, passed away on February 15, 2023, at Necitas, her assisted living care facility in Silver Spring, MD. Dr. Kelleher taught, wrote, and advised policymakers in the areas of international security and American defense policy for the past 50 years. Decorated for her public service by both the American and German governments, she taught and wrote extensively on conventional and nuclear arms control as well as German, Russian, and European security issues. Dr. Kelleher held multiple academic appointments, including at the Universities of Michigan, Denver, and Maryland, as well the National Academies of Sciences, the Brookings Institution, the Aspen Institute, and the Naval War College. She also served as a deputy assistant secretary of defense for Russia, Ukraine, and Eurasia; the Secretary of Defense's representative to NATO; and on the National Security Council. Educated at Mt. Holyoke College, the Free University of Berlin, and MIT, Dr. Kelleher founded the Center for International and Security Studies at Maryland (CISSM) and was the first president of Women in International Security (WIIS). She served as vice chair of the Committee on International Security and Arms Control of the National Academies of Sciences for 15 years, directing annual policy dialogues with China, Russia, and India.
![]() Barbara Shortley — Career CIA Operations Officer, Trailblazer
Barbara Shortley — Career CIA Operations Officer, Trailblazer
Barbara Mary Shortley, 97, of Rehoboth Beach, DE passed away on February 19, 2023. Born in Pittsburgh, PA, Ms. Shortley attended Georgetown Visitation High School followed by Trinity College and the Catholic University of America earning a B.A. in Economics and Political Science. She had a trailblazing career with the Central Intelligence Agency serving as an operations officer conducting clandestine operations across the globe including wartime service in Vietnam and a multi-year assignment to Paris, France. After her retirement from the CIA, she followed her love of foreign travel by opening a travel agency in Washington, DC, leading tours to a variety of international destinations.
![]() Richard Rentz — CIA Communicator and Honorable Service Award Holder
Richard Rentz — CIA Communicator and Honorable Service Award Holder
Richard John Rentz, of Ormond Beach, passed on Sunday, February 19, 2023, at the age of 91. Born in Royal Oak, Michigan, he graduated from St. Mary's High School in 1950. He enlisted in the United States Navy, where he served from 1953 to 1956 in the Asian theater as a Radio Operator onboard the U.S.S. Ernest G. Small, earning the National Defense Service Medal and the China Service Medal. After his honorable discharge, Richard embarked upon a career with the Central Intelligence Agency as a Communications Officer. His work led him to various postings around the world, to include Cyprus, Germany, Taiwan, Turkey, Philippines, India, and Australia. He finished out his career in Virginia and retired in 1991 after 34 years of faithful service, whereupon he was recognized with the CIA Honorable Service award.
Section VI - Events
02 Mar 23 (Thursday), 1900 (CT) - Virtual via Zoom - AFIO San Antonio hosts Zbigniew Wojcik, author of "Slaying the Soviet Beast" on Communist Chinese Party infiltration of western technical, educational, and research organizations. Dr. Wojcik is a Polish scholar who was able to get to the U.S. as a visiting professor. He was not able to bring his family to the United States while the communist were in power, but now has his family with him. Wojcik gave the CIA important information about the communist government's weakness. That story is outlined in his book "Slaying the Soviet Beast." He has first hand experience with Chinese Communists infiltration of US educational organizations. We will forward meeting links several days prior to the actual meeting. Questions to John Franklin, Chapter President, at satxafio@gmail.com.
16 Mar 23 (Thursday), 1130 (MST) - In Person - Colorado Springs - The AFIO Rocky Mountain Chapter hosts Dave Humpert, discussing "1983 The Year of Maximum Danger." ABSTRACT: "During my first years in Washington, I think many of us in the administration took it for granted that the Russians, like ourselves, considered it unthinkable that the United States would launch a first strike against them. But the more experience I had with the Soviet leaders and other heads of state who knew them, the more I began to realize that many Soviet officials feared us not only as adversaries but as potential aggressors who might hurl nuclear weapons at them in a first strike." President Ronald Reagan - "The American intelligence misconception was not to fully realize the nature of Soviet fears and the implication of those fears….Understanding other people's misconceptions is a long-standing problem in intelligence analysis."
BIO: During his varied career as a USAF Soviet/Russian military and political specialist, Dave relied on his knowledge of Russian political and military history and its culture with two degrees in Russian Area Studies. His Russian language ability was invaluable as an interpreter, translator, and source-language analyst in a variety of challenging assignments for the USAF and the operational intelligence community. In 2002, Dave retired from the USAF and began a career in DIA as the Senior Analyst for Political-Military Strategic (Russia) issues with the J2 Directorate, NORAD/USNORTHCOM. He performed additional intelligence duties for CIA, NSA and Department of State until his final retirement in 2016. This is an in-person event. For event location and other information, contact Steve Pease at steve13507@gmail.com.
13 Apr 23 (Thursday), 1130 (PST) - In Person - San Francisco - The AFIO Andre LeGallo Chapter hosts Richard E. Hanson on CIA Operations in Viet Nam. No-host cocktail. Location: Basque Cultural Center, 599 Railroad Avenue, South San Francisco, CA. Please contact Mariko Kawaguchi, Board Secretary at afiosf@aol.com for questions. Students: please e-mail your school ID to get sponsored. Register here.
See the AFIO Calendar of Events for scheduling further in the future.
Events from Advertisers, Corporate Sponsors, Others
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. To register, please email Shana Oltmans at soltmans@spymuseum.org. Free but space is limited. More about event here.
Join host Michael Ard for a discussion with former CIA Operations Officer James Acuna as they discuss, "The Ukraine Conflict One Year Later: An Intelligence Perspective." James Acuna has nearly three decades of experience in intelligence operations in both the public and private sector, including nearly 20 years as an Operations Officer with the Central Intelligence Agency. Based in Tallinn, Acuna is founder of Frontier Vectors, a US and European based security and business consultancy service for Eastern European start-ups and American VCs. Reserve a spot here.
Attend this online discussion of the latest intelligence, national security, and terrorism issues in the news. Spy Museum Executive Director Chris Costa, a former intelligence officer of 34 years, will be joined by Alan E. Kohler, Jr., FBI Assistant Director, Counterintelligence Division. Kohler was named assistant director of the FBI's Counterintelligence Division in April 2020. Kohler had most recently served as the special agent in charge of the Washington Field Office's Counterintelligence Division. He joined the FBI as a special agent in 1996 and worked counterintelligence matters at the Washington Field Office. He also served on the Evidence Response Team and took part in the FBI's response to the 9/11 attack on the Pentagon. In 2003, he transferred to the Counterintelligence Division to manage Russian counterintelligence investigations and was promoted to unit chief in 2004. In 2006, Kohler transferred to the New York Field Office to supervise a counterintelligence squad and then later a squad working cyber national security and criminal matters. He served as an assistant legal attaché in London beginning in 2012, acting as the FBI's liaison with British intelligence and law enforcement agencies. Kohler moved to the Norfolk Field Office in Virginia in 2016 as the assistant special agent in charge of the counterintelligence, counterterrorism, intelligence, and crisis management programs. He returned to FBI Headquarters in 2017 as the chief of the Eurasian Section, which manages the Bureau's operations countering Russian intelligence threats. In 2018, he was promoted to deputy assistant director in the Counterintelligence Division and managed multiple portfolios. He was promoted to the special agent in charge of the Counterintelligence Division at the Washington Field Office in 2019. He is a recipient of the Attorney General's Award for Exceptional Service, the FBI Director's Award for Outstanding Counterintelligence Investigation, and the Exceptional Achievement Medal from the Director of National Intelligence. Program is free of charge but requires advanced registration. Explore or Register here: www.spymuseum.org.
The International Spy Museum is lifting our veil of secrecy exclusively for our neighbors in DC's Ward 6. This is a chance to explore the Museum's exhibits, meet former spies, and test your spy skills through tradecraft demonstrations. Community organizations will also be briefing you on some of their latest activities—this is intel you can use whether you are a spy or just want to understand your zone of operations better! Ward 6 operatives of all ages are invited to attend! This event is ONLY for Ward 6 residents. Click here to see if you live in Ward 6. Guests 17 and under MUST be with an adult (18+) at all times. Program is free of charge but requires advanced registration. Explore or Register here: www.spymuseum.org.
She was the first female accredited correspondent during World War II. After secret meetings with its author, she smuggled The New Class, an anti-Communist manifesto out of Yugoslavia, where it went on to sell more than three million copies and be translated into more than 60 languages. Isn't it time you knew her story? Katharine Clark was the first female military accredited correspondent during World War II. Staying on as a foreign correspondent behind the Iron Curtain after the War, she risked her life to expose the truth about the realities of Communism to the world. Join author Katharine Gregorio to discover a trailblazer and an intense and too little-known Cold War story. Gregorio dug into the real life of her great aunt to write The Double Life of Katharine Clark: The Untold Story of the Fearless Journalist Who Risked Her Life for Truth and Justice. Support for this program has been provided by a generous grant from the Pritzker Military Foundation, on behalf of the Pritzker Military Museum & Library. Explore or Register here: www.spymuseum.org.
13 Mar 23, 1700 - 1800 (ET) – Publishing with Intelligence - Institute of World Politics – Virtual
This information-filled seminar will discuss getting your article or manuscript to be published by an academic journal or obtaining a contract for a book. The forum will provide a book proposal template used by some major book publishers and how proposed articles make it through a double-blind review process for an academic publication. A question and answer period will dominate the forum, and attendees are encouraged to bring any proposed manuscripts they seek to publish. About the Speaker: Dr. Jan Goldman is Professor of Intelligence and Security Studies at The Citadel. His research areas focus on ethics and intelligence operations, secrecy, intelligence analysis, psychological operations, intelligence in civil society, and intelligence education. He has over 25 years experience working in the U.S. intelligence community. He taught for many years at the National Intelligence University (formally known as the National Defense Intelligence College) and the FBI Academy at Quantico, Virginia. He is the organizer for several international academic and professional intelligence conferences held at Johns Hopkins University, Georgetown University, and Oxford University. He is currently the editor-in-chief of the highly respected International Journal of Intelligence and Counterintelligence; the founding editor for professional textbooks – Security Professionals Intelligence Education Series (S.P.I.E.S. at Rowman and Littlefield Publishers); a member of several academic, research and publishing advisory boards; co-founder of the non-profit International Intelligence Ethics Association; and the founding editor of the International Journal of Intelligence Ethics. He is the author or editor of numerous publications to include, as a co-author, Intelligence and Information Policy for National Security: Key Terms and Concepts (Rowman and Littlefield, 2017). His two-volume The Central Intelligence Agency: An Encyclopedia of Covert Operations, Intelligence Gathering, and Spies (ABC-CLIO, 2016) honored as Editors’ Top Community College Resources award and the Best Reference Title award of 2016; and War on Terror Encyclopedia: From the Rise of Al Qaeda to 9/11 and Beyond (ABC-CLIO, 2015). Dr. Goldman is an internationally recognized expert on ethics and intelligence, and the only intelligence analyst to be awarded “current and warning intelligence expert” at the Defense Intelligence Agency. Free registration here.
Join intelligence community colleagues online for a Coffee and Conversation with Doug Wade, Chief, China Mission Group, Defense Intelligence Agency (DIA). In this 45-minute discussion with Larry Hanauer, INSA Vice President for Policy, Mr. Wade will discuss China's military capabilities, technology innovation, space and cyber strategies, and political/economic influence on countries around the world. He will also discuss the value of open source intelligence in understanding China, prospects for conflict in the Taiwan Straits and elsewhere in the Pacific, and lessons from the Russia-Ukraine war that could be applied to a conflict with China. Free registration here.
Birds do it, bees do it -- even educated slugs do it! But you can't do it…that is smell certain chemicals, feel an earthquake before it hits, or sense changes in the atmosphere. That's why spy agencies have invented super sensors to collect invisible intelligence -- chemical traces, nuclear particles, vibrations, and wave-lengths – that can be used to identify and track targets. Join us for an introduction to the too little-known field of Measurement and Signature Intelligence (MASINT) from Peter Humphrey. Humphrey is an all-source analyst: a researcher and writer with some 50 publications in the fields of intelligence, international affairs, and geophysics. Explore or Register here: www.spymuseum.org.
From the spymaster and inspiration for the movie Argo, discover the "real-life spy thriller" of the brilliant but under-supported CIA operatives who developed breakthrough spy tactics that helped turn the tide of the Cold War. Antonio Mendez and his future wife Jonna were CIA operatives working to spy on Moscow in the late 1970s, at one of the most dangerous moments in the Cold War. Soviets kept files on all foreigners, studied their patterns, and tapped their phones. Intelligence work was effectively impossible. The Soviet threat loomed larger than ever. The Moscow Rules tells the story of the intelligence breakthroughs that turned the odds in America's favor. Jonna Mendez is a former Chief of Disguise with over twenty-five years of experience as a CIA officer working in Moscow and other sensitive areas. Explore or Register here: www.spymuseum.org.
19 - 28 Mar 23 - Washington DC to Europe and back - Gary Powers' 10-Day Cold War Espionage Tour
Join author and historian Gary Powers Jr. on this unforgettable 10-day tour of Cold War and Espionage related sites throughout Germany and the Czech Republic
Day 1: Departure from the USA; Day 2: Arrival Berlin; Day 3: Berlin - Potsdam - Berlin; Day 4: Berlin; Day 5: Berlin – Leipzig – Dresden; Day 6: Dresden – Prague – Pilsen; Day 7: Pilsen – Míšov – Pilsen; Day 8: Pilsen – Rozvadov – Nuremberg – Stuttgart; Day 9: Stuttgart – Sinsheim – Speyer – Frankfurt; Day 10: Departure for the USA.
Included Visits: Berlin Wall Memorial • Checkpoint Charlie Museum • German Spy Museum • Military History Museum Gatow • Glienicke Bridge • Hohenschönhausen Memorial • Berlin Stasi Museum • Allied Museum on Clay Allee • Museum in Der Runde Ecke • Leipzig Forum of Contemporary History Museum • Dresden's Military History Museum • Bautzner Strasse Dresden Memorial • KGB Museum • Prague Museum of Communism • Vitkov Hill Nuclear Bunker • Pilsner Urquell Brewery • Atom Museum • Iron Curtain Museum • Nuremberg Trials Memorial • Stuttgart Cold War Bunker • Sinsheim Technik Museum • Speyer Museum of Technology.
Tour Name: Gary Powers' Cold War Espionage Tour - view tour; Group Name: Garypowers.Com Tours; Departure City: Washington, DC; Tour Departure Date: March 19, 2023; Tour Return Date: 28 Mar 23.
Tour Price: $3,950.00 (deduct $950 for land only tour) per person, assumes 2-person registration.
For full description of the activities and accommodations on each of those dates and locations, explore full information about the tour here or Call 1.800.323.4466.
To enroll now for this 2023 once in a lifetime tour, do so here.
ALSO See: "Enemy Territory: The Story of American CIA U-2 Pilot Francis Gary Powers" - A Graphic Novel by Francis Gary Powers Jr. and Walter Pfenninger.
Join International Spy Museum Historian and Curator Dr. Andrew Hammond in conversation with historian Benny Morris, author of Sidney Reilly: Master Spy, about one of the most colorful and best-known spies of the twentieth century. Emerging from humble beginnings in southern Russia, Reilly was an inventive, multilingual businessman and conman who became a virtuoso of espionage. He spent World War I in the United States, brokering major arms deals for tsarist Russia, and then joined the ranks of MI6, Britain's foreign intelligence service. He tried to overthrow the Bolshevik regime in Moscow before eventually being lured back to Russia and executed. The Spy Museum is proud to exhibit the only object in existence that illustrates the connection between Reilly and R.H. Bruce Lockhart, co-conspirator of the plot. Join the historians as they sift through the reality and the myth of Reilly's life to paint a fascinating portrait of one of the most intriguing figures from the golden age of spies. Program is free of charge but requires advanced registration. Explore or Register here: www.spymuseum.org.
Alma Katsu is the award-winning author of seven novels; Red London, her latest is a follow-up to the successful Red Widow where she unveiled Lyndsey Duncan, a CIA intelligence officer nicknamed "the human lie detector." Katsu knows what she is writing about. She had a thirty-five-year career as a senior intelligence analyst for several US agencies, including the CIA and NSA, where she advised policymakers and military commanders on issues of national security. Her newest book is a nuanced, race-against-the-clock story that invokes today's headlines. International Spy Museum Director of Adult Education Amanda Ohlke and Katsu will discuss how Lyndsey reflects the reality of women working in intelligence and how the thriller's plot reflects both current affairs and famous notes from the past—like well-placed moles at the CIA. Explore or Register here: www.spymuseum.org.
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. To register, please email Shana Oltmans at soltmans@spymuseum.org. Free but space is limited. Register below. Explore or Register here: www.spymuseum.org.
Wednesday, 29 Mar 23, 0900-1700 (ET) – Boston, MA – How Wars End: A Conference Presented by the Pardee Center for the Study of the Longer-Range Future – Boston University - In Person
The event will feature five expert panels:How wars end from a historical perspective (Moderator: Prof. Erik Goldstein), How intelligence supports diplomats in ending wars (Moderator: Prof. Joseph Wippl), How the Afghanistan War ended (Moderator: Prof. John Woodward), How the Iraq War ended (Moderator: Prof. Shamiran Mako), How current crises will end (Moderator: Ambassador Mark Storella). The full list of panelists will be announced in the coming weeks. This conference is convened by Prof. John Woodward, Prof. Cathal J. Nolan, and Prof. Erik Goldstein in their capacity as Pardee Center Faculty Research Fellows. This event is free and open to the public. Register here.
SPY with Me is an interactive virtual program for individuals living with dementia and their care partners. Join SPY as we use music and artifacts to explore some of our favorite spy stories. Programs last one hour and are held virtually through Zoom. Every month the same program is offered on two different dates. To register, please email Shana Oltmans at soltmans@spymuseum.org. Free but space is limited. Register below. Explore or Register here: www.spymuseum.org
"The Nation's Premier Intel and National Security Event" - Save the date for the 10th Annual AFCEA/INSA Intelligence and National Security Summit! The powerful, two-day program, at the Gaylord National Resort, will feature five blockbuster plenaries, six engaging breakout sessions, and a jam-packed exhibit hall full of the latest IC technology innovations. Top leaders will discuss State of the Community, Military Intelligence Priorities, Strategic Intelligence, and Cybersecurity Challenges. Breakout sessions with senior leaders, technology experts, and thought leaders will examine some of the most pressing issues facing the community. Plus, powerful networking opportunities designed to foster partnerships and relationship building. Stay tuned! Registration to open in early March. Check for updates here.
Gifts for Friends, Colleagues, Self
 Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Now available: Black short-sleeved polo shirts with Embroidered AFIO logo
Show your support for AFIO with our new Black Short-sleeve Polo Shirts. Shirts are shrink and wrinkle resistant of fine cotton with a soft, "well-worn, comfy" yet substantial feel. They feature a detailed embroidered AFIO seal. Get a shirt for yourself and consider as gifts for colleagues, family, and friends. Only $50 each including shipping.
Sizes for (M) men, only; Small, Medium, Large, XL, XXL, and XXXL. $50 per shirt.
You may pay by check or credit card. Complete your order online here or mail an order along with payment to: AFIO, 7600 Leesburg Pike, Ste 470 East, Falls Church, VA 22043-2004. Phone orders at 703-790-0320. Questions? Contact Annette at: annettej@afio.com.

PopSocket for cellphones or tablets
Show your support to AFIO while enjoying the convenience offered by our AFIO Logo PopSocket. The PopSocket is most commonly used as a stand and as a grip for your mobile phone or tablet; handy for taking selfies, watching videos, and for texting. The PopSocket looks like a small button or sticker which, when closed, sticks flat to your mobile device. However, its accordion-like design enables it to pop open for use. The benefits of using a PopSocket make it a must-have accessory for your mobile phone or tablet. It also aids in keeping your phone from slipping off your hand during use, falling, or breaking.
Price: $15. Order this and other store items online here.

Caps - Dark Navy with Navy AFIO Logo
An authentic silhouette with the comfort of an unstructured, adjustable fit. Fabric: 100% cotton. Unstructured. Fabric strap closure with adjustable D-clip. Price: $30. Order this and other store items online here.

Duffel Bags - Royal Blue and Black with Full Color AFIO Logo This duffel has it all when it comes to value, style and organization.
600 denier polyester canvas with polyester double contrast; D-shaped zippered entry for easy access. Front pocket with hook and loop closure. End mesh pocket Easy-access end pockets. Four durable, protective feet and built-in bottom board for added strength. Web handles with padded grip. Detachable, adjustable shoulder strap.
Dimensions: 11"h x 19.75"w x 9.75"d; Approx. 2,118 cubic inches
Price: $50. Order this and other store items online here.
AFIO Mug with color glazed seal.
Made in the U.S.A., dishwasher-safe.
$35 includes shipping.
Sip your morning joe in style or use it to stash pens, cards, paperclips, or candy.
Order this and other store items online here.
JUST PUBLISHED
FOR 2023
| Be informed on career opportunities in the U.S. Intelligence Community | ||
 |
Intelligence as a Career - with updated listings of colleges teaching intelligence courses, and Q&As on needed foreign languages, as well as the courses, grades, extracurricular activities, and behavioral characteristics and life experiences sought by modern U.S. intelligence agencies. AFIO's popular 47-page booklet reaches thousands of high school, college students, university guidance offices, and distributed in classes teaching intelligence, to help those considering careers in the U.S. Intelligence Community. |
 |
| This is the all new fifth edition. The publication is also popular with University Career Guidance Centers, professors and academic departments specializing in national security, and parents assisting children or grandchildren in choosing meaningful, public service careers. This booklet is provided online as a public service from the generosity of AFIO board, volunteer editors/writers, donors, and members. We thank all for their support which makes this educational effort possible. |
||
| Careers Booklet (new 2023 Fifth Edition) can be read online here |
||
| or downloaded as a PDF here | ||
| Careers webpage | ||
 Guide to the Study of Intelligence...and...When Intelligence Made a Difference
Guide to the Study of Intelligence...and...When Intelligence Made a Difference
"AFIO's Guide to the Study of Intelligence" has sold out in hard-copy.
It is available in digital form in its entirety on the
AFIO website here.
Also available on the website here are the individual articles of AFIO's
history project "When Intelligence Made a Difference" that have been
published to date in The Intelligencer journal.
More articles will be appear in future editions.
Some features of the email version of the WIN do not work for readers who have chosen the Plaintext Edition, some users of AOL, and readers who access their email using web mail. You may request to change from Plaintext to HTML format here afio@afio.com. For the best reading experience, the latest web edition can be found here: https://www.afio.com/pages/currentwin.htm
To unsubscribe from the WIN email list, please click the "UNSUBSCRIBE" link at the bottom of the email. If you did not subscribe to the WIN and are not a member, you received this product from a third party in violation of AFIO policy. Please forward to afio@afio.com the entire message that you received and we will remove the sender from our membership and distribution lists.
(c) 1998 thru 2022
AFIO Members Support the AFIO Mission - sponsor new members! CHECK THE AFIO WEBSITE at www.afio.com for back issues of the WINs, information about AFIO, conference agenda and registrations materials, and membership applications and much more! .
AFIO | 7600 Leesburg Pike, Suite 470 East, Falls Church, VA 22043-2004 | (703) 790-0320 (phone) | (703) 991-1278 (fax) | afio@afio.com